F5 Labs, in conjunction with our partner Baffin Bay Networks, researches global attack traffic region to region to gain a deeper understanding of the cyber threat landscape. Aside from attack campaigns targeting the entire Internet (IPv4 address space), the attack landscape varies regionally in terms of sources, targets, and attack types. In addition, targeted ports expose regional differences in IT norms when it comes to the way non-standard ports are used for HTTP and SSH.
In this latest data collection, we looked at malicious traffic over the same 90-day period—August 1, 2019 through October 31, 2019—in the United States, Canada, Latin America, Europe, Russia, Asia, Australia, and Europe. The attack landscape in Europe was different from the rest of the regions in that it had the most in-region IP addresses sending malicious traffic.
- The number one and two sources of attack traffic targeting European systems came from IP addresses assigned to France and Italy, which launched a combined 20% of all malicious traffic to the region.
- As a whole, Europe saw the most regional attack traffic, with 50% of the top 20 source traffic countries originating in Europe. Along with that, 64% of the normalized attack traffic was in-region, making it difficult for organizations to filter malicious traffic.
- The top IP address launching attacks against systems in Europe was assigned to an IP in Switzerland. Europe was the only region targeted by malicious traffic that originated in Switzerland. This same IP address was not seen attacking other regions in the same period, however, it was seen conducting abusive port scans and attempting credential stuffing attacks.
- Rounding out the top 10 IP addresses were those assigned to Moldova, France, the Netherlands, and the U.S. These 10 IP addresses launched RFB/VNCTop Attacking IP Addresses The top six IP addresses attacking systems in Europe from August 1, 2019 through October 31, 2019 were all assigned to in-region systems (Switzerland, Moldova, or France) and were either engaged in credential stuffing or multi-port scanning, activity that is typically attributed to looking for vulnerabilities. Sixty-nine percent of the IP addresses on the top 50 attacking IP addresses list were engaging in the same multi-port scanning behavior, many of which were Dutch, French, Russian, and Moldovan.1 Similar to the top source traffic countries list, most of the top attacking IP addresses come from within Europe, with the exception of South Korean IP addresses where there were 8 in the 50 top attacking IP list. For a complete list of attacks by IP address, see section Attacks Types of Top Attacking IP Addresses. port 5900 attacks (hitting all regions of the world).
- Europe saw many application services and remote access ports and services targeted by malicious traffic from August 1 through October 31, 2019. Some of the top attacked ports include SSH 22, alternate SSH port 2222, along with port 22222 and port 22223.
- The top ports targeted in Europe followed similar patterns to the rest of the world with VNC port 5900 (being attacked in regions all over the world) as the top attacked port. SMB port 445 followed, along with Telnet port 23, SSH port 22, and HTTP port 80.
For the purposes of this research series, Europe comprises all of the countries that geographically fall within what is commonly referred to as “Europe,” except for Russia. We cover Russia in a separate Regional Threat Perspectives report, so we do not reference any attack traffic targeting Russian systems specifically in this report. Parts of Russia, however, are considered to be geographically within Europe and are included in this analysis for in-region attacks. In addition, Turkey is considered part of the Middle East, so we do not reference any attack traffic targeting Turkey in this report. For more information on either the Russian or Turkish threat landscapes, please refer to the Regional Threat Perspectives, Fall 2019: Russia and Regional Threat Perspectives, Fall 2019: Middle East (/content/f5-labs-v2/en/labs/articles/threat-intelligence/regional-threat-perspectives--fall-2019--middle-east.html).
Top Source Traffic Countries
Before we look at the “top source traffic countries,” it’s important to clarify that we’re talking about the geographical source of IP addresses in this section. The “top source traffic countries” does not mean that the country itself, individuals, or organizations based in that country were responsible for the malicious traffic. The attack traffic could be coming through a proxy server or compromised system or IoT device with IP addresses assigned in a particular country. For expediency, we refer to these as top source traffic countries.
IP addresses assigned to France launched the most malicious traffic against systems in Europe from August 1, 2019 through October 31, 2019. The top 10 source traffic countries during this period were:
France
Italy
Russia
U.S.
Switzerland
Republic of Moldova
Netherlands
South Korea
Turkey
China
All of the top 10 were also the top malicious source traffic countries globally.
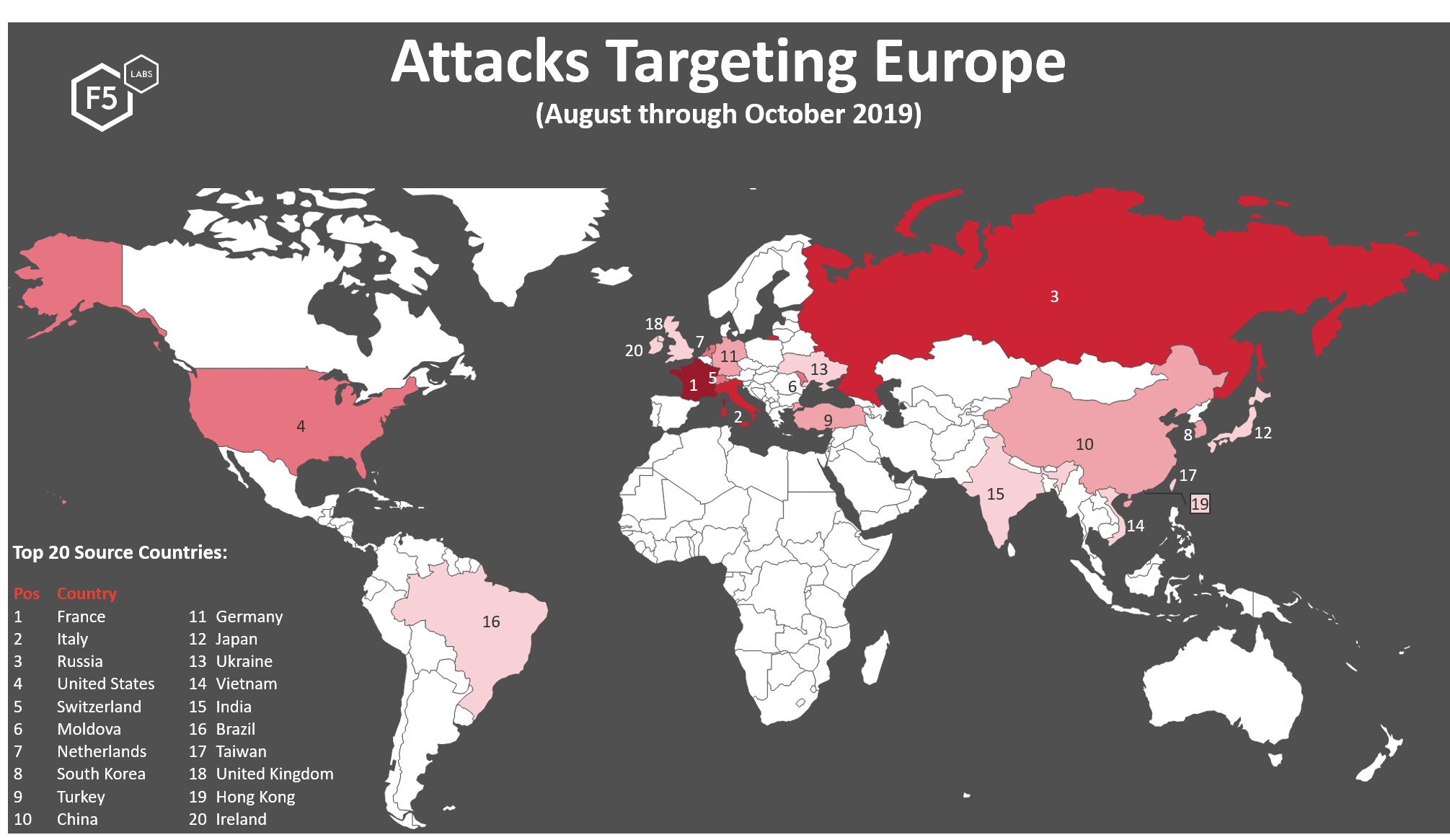
Figure 1. Top 20 source traffic countries launching attack traffic against targets in Europe, August 1, 2019 through October 31, 2019
Fifty percent of the top source traffic countries were in-region and account for 64% of all attack traffic directed towards European systems. This kind of traffic can be more difficult for enterprises to filter since typically businesses want to remain accessible to customers within their region. Thirty-nine out of 50 of the top attacking IP addresses also came from within Europe. IP addresses assigned to France headed the top attacking source countries list, accounting for 11% of the total malicious traffic directed in region. This is closely followed by IP addresses assigned in Italy, in second position. IP addresses assigned in Italy account for 9.9% of all attack traffic directed towards European systems. Both France and Italy were on the list for the top source traffic countries lists globally. IP addresses assigned in both of these countries were seen conducting aggressive port scanning and participating in the RFB/VNC port 5900 port scanning and credential stuffing, targeting all regions all over the world.
Europe also received a considerable amount of traffic from IP addresses assigned in Ireland (position 20) and in Ukraine (position 13). Europe is one of three regions to receive malicious traffic from Ireland, the other two being Canada and the U.S. Regarding Ukraine, malicious traffic attributed to IP addresses assigned in Ukraine only targeted three regions: Russia, Europe, and the Middle East. Other than two IP addresses assigned in Ireland that together launched a normalized 92,000 attacks, no other IP addresses in Ukraine or Ireland were in the top attacking IP address list, discussed later. This indicates that attacks coming from IP addresses in those countries were more distributed; that is, they were launched from many IP addresses but had a low number of attacks per address. This type of activity is deliberate and takes more resources (systems and manpower) to pull off, and therefore is typically attributed to more sophisticated threat actors.
Europe is the only region to receive malicious traffic attributed to source IP addresses assigned in Switzerland (position 5). This accounts for 8.5% of all malicious traffic we could see during the August through October time frame. A majority of that malicious traffic was sent by one IP address, appearing at the top of the attacking IP addresses list. This shows a very concentrated effort using one IP address to conduct credential stuffing and aggressive multi-port scanning.
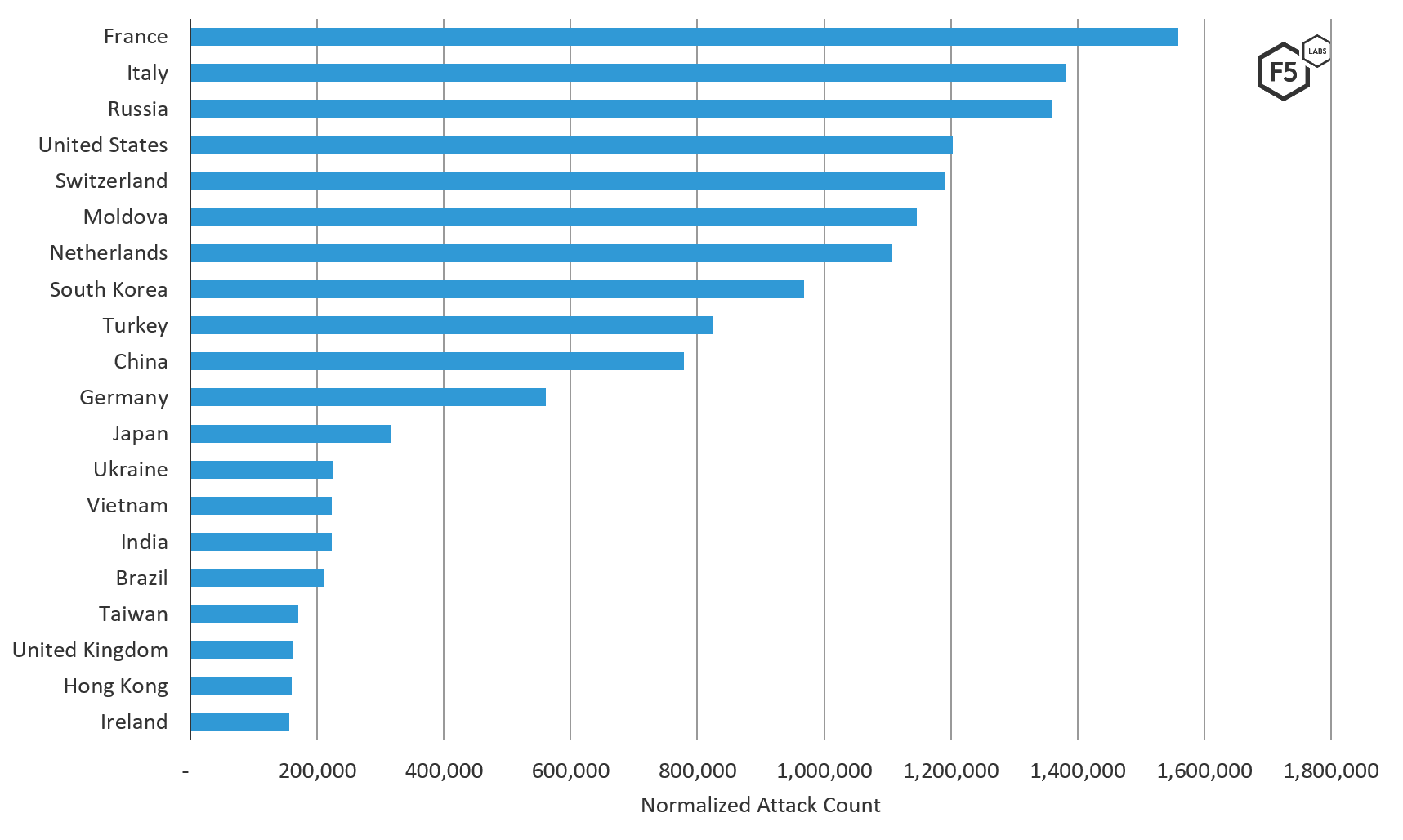
Figure 2. Top 20 source traffic countries (on a normalized scale) of attacks targeting European systems, August – October 2019
Top Attacking Organizations (ASNs)
M247 Ltd, an Internet provider from Switzerland, launched the most attack traffic against systems in Europe. M247 Ltd launched 2.24% more traffic than OVH SAS (a French company) in second position, and 5.22% more attack traffic than RM Engineering (from Moldova) in third position. GTECH S.p.A. in third position has two IP addresses in the top attacking IP addresses list. Garanti Bilisim Teknolojisi ve Ticaret T.A.S. in fourth position, and Amazon.com Inc. in fifth position did not have any IP addresses on the 50 top attacking IP address list, which indicates the attack traffic was more evenly distributed across malicious systems.
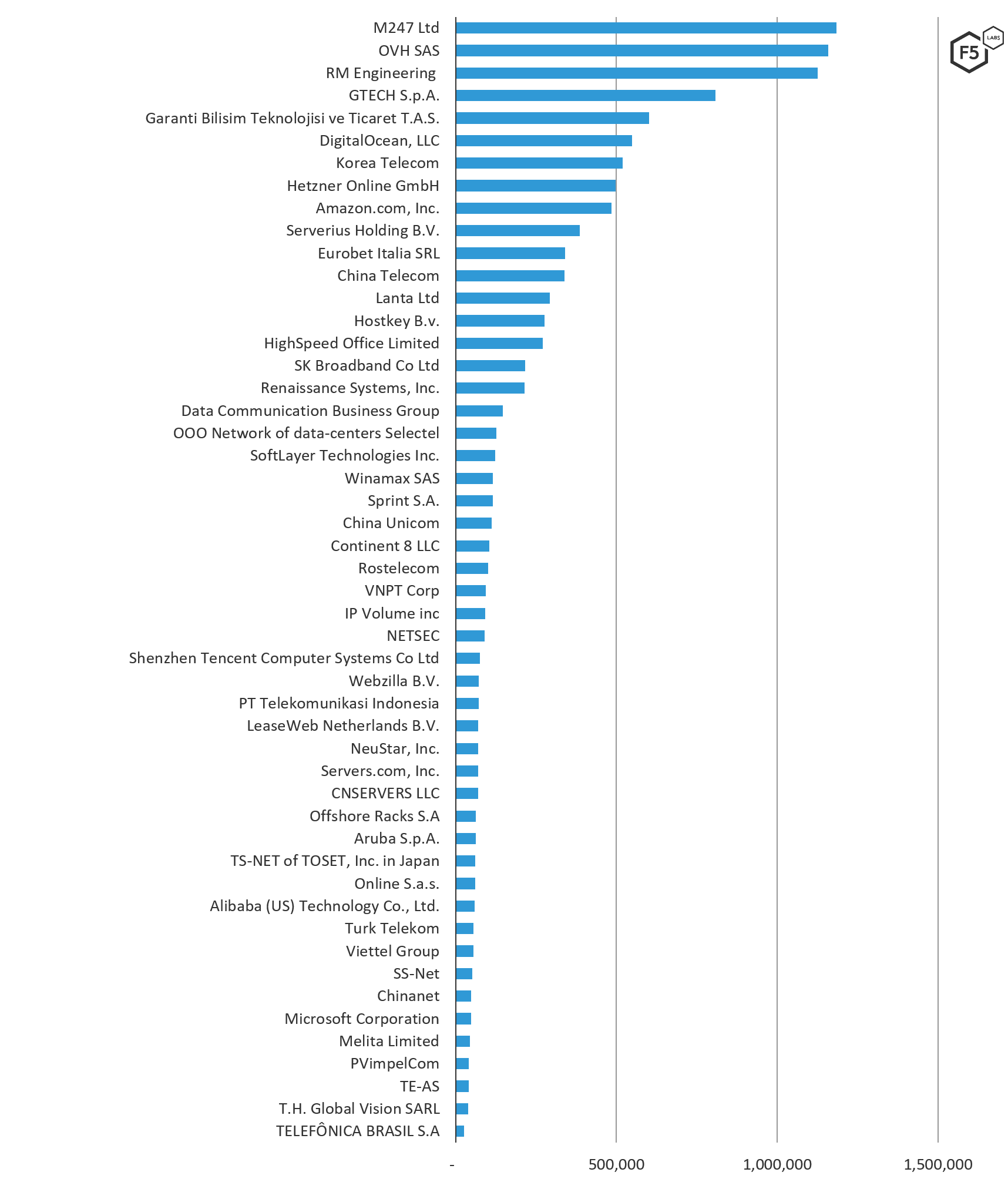
Figure 3. Source ASNs of attacks targeting European systems August – October 2019
The following table lists ASNs and their associated organizations (note that some have multiple ASNs).
| AS Organization | ASN | Normalized Count |
| M247 Ltd | 9009 | 1,185,038.2 |
| OVH SAS | 16276 | 1,159,075.5 |
| RM Engineering LLC | 49877 | 1,126,301.1 |
| GTECH S.p.A. | 35574 | 807,395.5 |
| Garanti Bilisim Teknolojisi ve Ticaret T.A.S. | 12903 | 600,722.8 |
| Amazon.com, Inc. | 16509 | 484,105.1 |
| Digital Ocean | 14061 | 548,931.6 |
| Korea Telecom | 4766 | 518,621.8 |
| Hetzner Online GmbH | 24940 | 496,927.7 |
| Serverius Holding B.V. | 50673 | 386,674.0 |
| Eurobet Italia SRL | 200944 | 341,188.7 |
| China Telecom | 4134 | 338,179.9 |
| LANTA Ltd | 41268 | 292,091.4 |
| Hostkey B.v. | 57043 | 277,040.9 |
| HighSpeed Office Limited | 39326 | 270,382.0 |
| SK Broadband Co Ltd | 9318 | 216,307.9 |
| Renaissance Systems, Inc. | 16897 | 213,634.7 |
| Data Communication Business Group | 3462 | 147,467.8 |
| Selectel | 49505 | 127,132.0 |
| SoftLayer Technologies Inc. | 36351 | 122,465.6 |
| Rostelecom | 12389 | 101,752.2 |
| Winamax SAS | 197014 | 116,259.4 |
| sprint S.A. | 197226 | 115,649.7 |
| CHINA UNICOM | 4837 | 111,169.0 |
| Continent 8 LLC | 14537 | 104,327.7 |
| VNPT Corp | 45899 | 93,137.6 |
| IP Volume inc | 202425 | 92,607.8 |
| NETSEC | 45753 | 90,725.5 |
| Turk Telekom | 47331 | 55,371.1 |
| PT Telekomunikasi Indonesia | 7713 | 71,709.9 |
| Shenzhen Tencent Computer Systems Co Lt | 45090 | 75,921.7 |
| Webzilla B.V. | 35415 | 72,624.9 |
| LeaseWeb Netherlands B.V. | 60781 | 70,187.1 |
| NeuStar, Inc. | 19905 | 69,545.7 |
| Servers.com, Inc. | 7979 | 69,238.9 |
| CNSERVERS LLC | 40065 | 69,217.1 |
| Aruba S.p.A. | 31034 | 62,850.6 |
| Offshore Racks S.A | 52469 | 63,245.9 |
| TS-NET of TOSET, Inc. in Japan | 55902 | 61,289.3 |
| Online S.a.s. | 12876 | 60,936.9 |
| Alibaba (US) Technology Co., Ltd. | 45102 | 59,523.7 |
| VimpelCom | 8402 | 41,593.6 |
| Viettel Group | 7552 | 55,056.7 |
| SS-Net | 204428 | 50,920.3 |
| Chinanet | 23650 | 48,777.3 |
| Microsoft Corporation | 8075 | 47,932.0 |
| Melita Limited | 200805 | 45,333.2 |
| TELEFÔNICA BRASIL S.A | 27699 | 25,558.3 |
| TE-AS | 8452 | 40,710.3 |
| T.H. Global Vision SARL | 59989 | 39,162.0 |
Table 1. ASNs and their associated organizations (some have multiple ASNs)
ASNs Attacking the Middle East Compared to Other Regions
Figure 4 shows the number of attacks by ASN directed towards European systems compared to other regions of the world. The key difference between attack traffic launched from networks targeting Europe versus the rest of the world is the volume of attacks launched from AS organizations from within the region. In terms of the top attacking ASNs around the world, Europe fell in the middle of the pack, not receiving the most attack traffic or the least amount of malicious traffic from OVH SAS, RM Engineering, or DigitalOcean. European systems also saw attack traffic from 5 unique AS organizations and a small percentage of traffic from PVimpelCom, an ASN that only targeted Europe and Russia. Based on that data it could be inferred that this ASN may have been looking more towards targeting Eastern Europe.
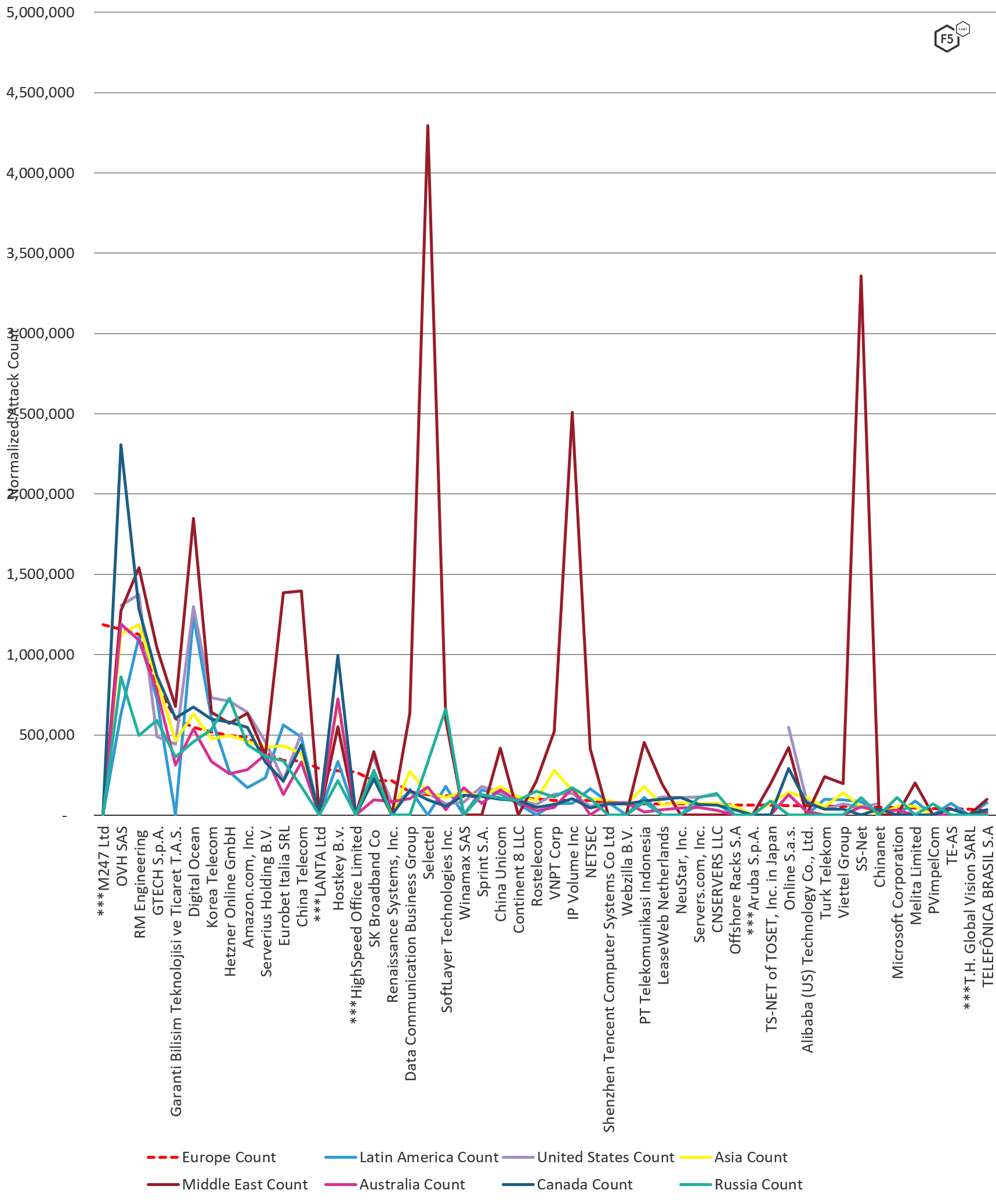
Figure 4. Count of attacks by ASN targeting European systems in comparison to other geographic locations
Top Attacking IP Addresses
The top six IP addresses attacking systems in Europe from August 1, 2019 through October 31, 2019 were all assigned to in-region systems (Switzerland, Moldova, or France) and were either engaged in credential stuffing or multi-port scanning, activity that is typically attributed to looking for vulnerabilities. Sixty-nine percent of the IP addresses on the top 50 attacking IP addresses list were engaging in the same multi-port scanning behavior, many of which were Dutch, French, Russian, and Moldovan.2 Similar to the top source traffic countries list, most of the top attacking IP addresses come from within Europe, with the exception of South Korean IP addresses where there were 8 in the 50 top attacking IP list. For a complete list of attacks by IP address, see section Attacks Types of Top Attacking IP Addresses.
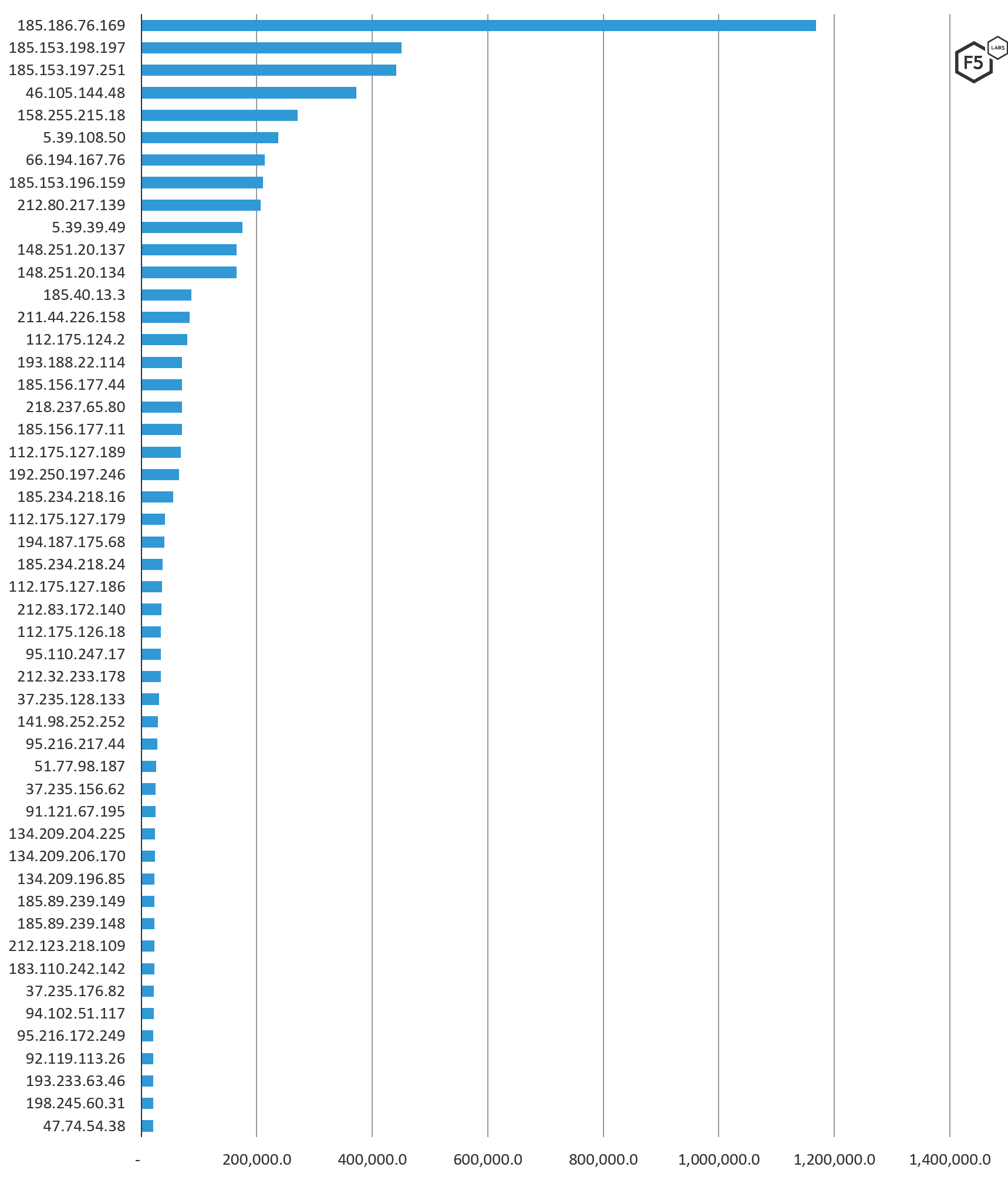
Figure 5. Top 50 IP addresses attacking European targets, August 1 – October 31, 2019
IP Addresses Attacking Europe Compared to Other Regions
The following chart shows the volume of attack traffic European systems received per IP address in comparison to other regions of the world. Attack traffic destined for European systems had some overlap with the rest of the world, with many IP addresses seen in Europe also seen in 6 or 7 other regions of the world. There is an exception of a handful of IP addresses launching global attacks against RFB/VNC port 5900 (see the next section). Although geographically in the same region, the European and the Russian threat landscapes saw little overlap in terms of specific IP addresses sending malicious traffic. Eighteen percent of the top attacking IP addresses sending malicious traffic to Europe were unique to Europe, while 16% of that top 50 were seen sending malicious attack traffic to all other regions in the world.
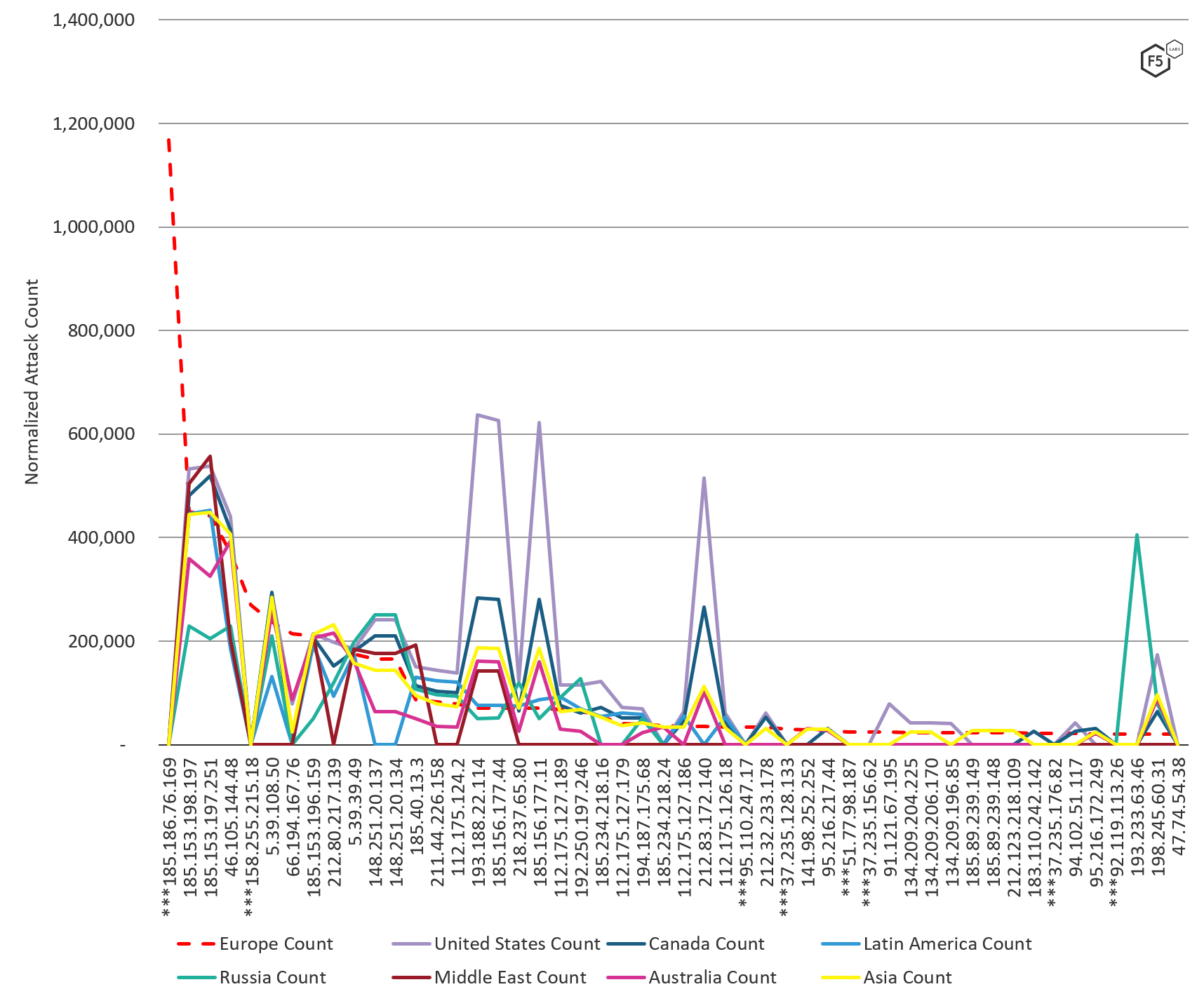
Figure 6. Top 50 IP addresses attacking European systems in comparison to other geo regions, August – October 2019
Attacks Types of Top Attacking IP Addresses
Of the top 50 IP addresses attacking systems in Europe, most IP addresses were assigned in the Netherlands and South Korea (both at 16% of the top attacking IP addresses). These IP addresses, along with the remainder coming from nations all over the world (and all fairly distributed), launched scans against multiple ports (69%), conducted credential stuffing activity (30%), and attempted to drop malware (1%). Many of the IP addresses conducting abusive port scanning and credential stuffing specifically targeted Remote Frame Buffer (RFB)/VNC port 5900 with brute force and credential stuffing attacks.
The IP addresses in Moldova assigned to RM Engineering, as well as those assigned to OVH SAS in France, launched brute force and credential stuffing attacks against Remote Frame Buffer (RFB)/VNC port 5900, globally. All regions of the world were hit with these same attacks from the following IP addresses:
- 185.153.197.251
- 185.153.198.197
- 46.105.144.48
- 193.188.22.114
- 185.156.177.44
- 185.153.196.159
- 5.39.39.49
- 185.40.13.3
These port 5900 attacks were new activity we noticed earlier in the summer that continued through October 31, 2019. We have opened up a public threat hunting investigation on Twitter to uncover what is going on with these attacks and will be looking to share our findings and ask questions soon. Join the conversation on Twitter.
Eighteen percent of the IP addresses seen sending malicious traffic to Europe exclusively targeted this region. The following list is in descending order starting with top attacking IP addresses.
| Source IP Address | AS Organization | Country | Normalized Count | Attack Type |
| 185.186.76.169 | M247 Ltd | Switzerland | 1,168,709.10 | Credential stuffing, multi-port scanning |
| 185.153.198.197 | RM Engineering LLC | Republic of Moldova | 450,566.80 | Credential stuffing, multi-port scanning |
| 185.153.197.251 | RM Engineering LLC | Republic of Moldova | 441,552.30 | Credential stuffing, multi-port scanning |
| 46.105.144.48 | OVH SAS | France | 371,867.70 | Credential stuffing, multi-port scanning |
| 158.255.215.18 | HighSpeed Office Limited | France | 270,381.70 | |
| 5.39.108.50 | OVH SAS | France | 237,506.70 | Credential stuffing, multi-port scanning |
| 66.194.167.76 | Renaissance Systems, Inc. | United States | 213,634.70 | Port scanning (ports: 5900) |
| 185.153.196.159 | RM Engineering LLC | Republic of Moldova | 210,472.40 | Credential stuffing, multi-port scanning |
| 212.80.217.139 | Serverius Holding B.V. | Netherlands | 206,862.40 | Credential stuffing, multi-port scanning |
| 5.39.39.49 | OVH SAS | France | 175,302.50 | Credential stuffing, multi-port scanning |
| 148.251.20.137 | Hetzner Online GmbH | Germany | 165,284.20 | Port scanning (ports: 22, 80, 25, 443) |
| 148.251.20.134 | Hetzner Online GmbH | Germany | 165,167.40 | Port scanning (ports: 80, 443, 25, 22) |
| 185.40.13.3 | GTECH S.p.A. | Italy | 86,495.10 | Port scanning (many ports: 51 unique ports) |
| 211.44.226.158 | SK Broadband Co Ltd | South Korea | 83,242.00 | Port scanning (many ports: 48 unique ports) |
| 112.175.124.2 | Korea Telecom | South Korea | 79,308.30 | Port scanning (many ports: 61 unique ports) |
| 193.188.22.114 | Hostkey B.v. | Russia | 70,512.20 | Credential stuffing, multi-port scanning |
| 185.156.177.44 | Hostkey B.v. | Russia | 70,473.80 | Credential stuffing, multi-port scanning |
| 218.237.65.80 | SK Broadband Co Ltd | South Korea | 70,434.90 | Port scanning (ports: 443, 80, 53, 22) |
| 185.156.177.11 | Hostkey B.v. | Russia | 70,070.20 | Credential stuffing, multi-port scanning |
| 112.175.127.189 | Korea Telecom | South Korea | 68,294.20 | Port scanning (many ports: 48 unique ports) |
| 192.250.197.246 | CNSERVERS LLC | United States | 65,053.10 | Credential stuffing, multi-port scanning |
| 185.234.218.16 | sprint S.A. | Ireland | 54,806.80 | Credential stuffing, multi-port scanning |
| 112.175.127.179 | Korea Telecom | South Korea | 41,407.80 | Port scanning (many ports: 48 unique ports) |
| 194.187.175.68 | GTECH S.p.A. | Italy | 39,907.90 | Port scanning (many ports: 45 unique ports) |
| 185.234.218.24 | sprint S.A. | Ireland | 37,264.40 | Credential stuffing, multi-port scanning |
| 112.175.127.186 | Korea Telecom | South Korea | 35,507.10 | Port scanning (many ports: 46 unique ports) |
| 212.83.172.140 | Online S.a.s. | France | 35,258.80 | Credential stuffing, multi-port scanning |
| 112.175.126.18 | Korea Telecom | South Korea | 34,228.10 | Port scanning (many ports: 42 unique ports) |
| 95.110.247.17 | Aruba S.p.A. | Italy | 33,917.60 | Credential stuffing, multi-port scanning |
| 212.32.233.178 | LeaseWeb Netherlands B.V. | Netherlands | 33,676.30 | Port scanning (ports: 80, 25, 443) |
| 37.235.128.133 | LANTA Ltd | Russia | 30,269.30 | Port scanning (ports: 1433, 445) |
| 141.98.252.252 | 31173 Services AB | United Kingdom | 28,259.80 | Port scanning (ports: 3306) |
| 95.216.217.44 | Hetzner Online GmbH | Finland | 27,323.30 | Credential stuffing, multi-port scanning |
| 51.77.98.187 | OVH SAS | United Kingdom | 25,160.50 | Port scanning (ports: 445, 1433) |
| 37.235.156.62 | LANTA Ltd | Russia | 24,571.30 | Malware Uploads, Multi Port Scanninng |
| 91.121.67.195 | OVH SAS | France | 24,349.90 | Credential stuffing, multi-port scanning |
| 134.209.204.225 | DigitalOcean, LLC | Netherlands | 23,743.30 | Port scanning (ports: 80, 443, 22, 445, 53) |
| 134.209.206.170 | DigitalOcean, LLC | Netherlands | 23,730.50 | Port scanning (many ports: 6 unique ports) |
| 134.209.196.85 | DigitalOcean, LLC | Netherlands | 22,913.10 | Port scanning (many ports: 7 unique ports) |
| 185.89.239.149 | Melita Limited | Malta | 22,665.80 | Port scanning (ports: 443, 80, 53, 22) |
| 185.89.239.148 | Melita Limited | Malta | 22,658.10 | Port scanning (ports: 80, 443, 22, 53) |
| 212.123.218.109 | COLT Technology Services Group Limited | Netherlands | 22,647.40 | Port scanning (ports: 80, 443, 22, 53) |
| 183.110.242.142 | Korea Telecom | South Korea | 22,162.80 | Port scanning (many ports: 7 unique ports) |
| 37.235.176.82 | LANTA Ltd | Russia | 22,033.20 | Port scanning (ports: 445, 1433) |
| 94.102.51.117 | IP Volume inc | Netherlands | 21,392.20 | Credential stuffing, multi-port scanning |
| 95.216.172.249 | Hetzner Online GmbH | Finland | 20,962.10 | Credential stuffing, multi-port scanning |
| 92.119.113.26 | TORAT Private Enterprise | Netherlands | 20,863.80 | Port scanning (many ports: 15 unique ports) |
| 193.233.63.46 | Smart Telecom S.A.R.L | Argentina | 20,766.00 | Port scanning (many ports: 59 unique ports) |
| 198.245.60.31 | OVH SAS | Canada | 20,372.40 | Credential stuffing, multi-port scanning |
| 47.74.54.38 | Alibaba (US) Technology Co., Ltd. | Japan | 20,065.30 | No data available |
Top Targeted Ports
VNC 5900 was the top attacked port in Europe and in all regions globally from August 1, 2019 through October 31, 2019. This activity is not typical, hence the investigative threat hunting we are doing on Twitter mentioned previously. SMB port 445 is in second position for services and ports attacked in Europe, followed closely in third place by Telnet port 23, and SSH port 22 in fourth. These ports are commonly targeted because exploiting a vulnerability on any of these ports can give a malicious actor access to the entire system.
What stands out the most in top attacked ports in Europe is the targeting of SSH and alternate SSH. It is a regional difference from other parts of the world that port 22222 is also used for SSH in Europe. Europe is the only region where port 22222 and 22223 were also both attacked in an attempt to exploit alternate ports and usages of SSH.
In addition to some of the most commonly targeted ports, the number of non-standard HTTP ports (8443, and 8080, and 8088) and other application ports like Microsoft SMB port 445, and Microsoft CRM port 5555 makes it clear that attackers were targeting applications in Europe.
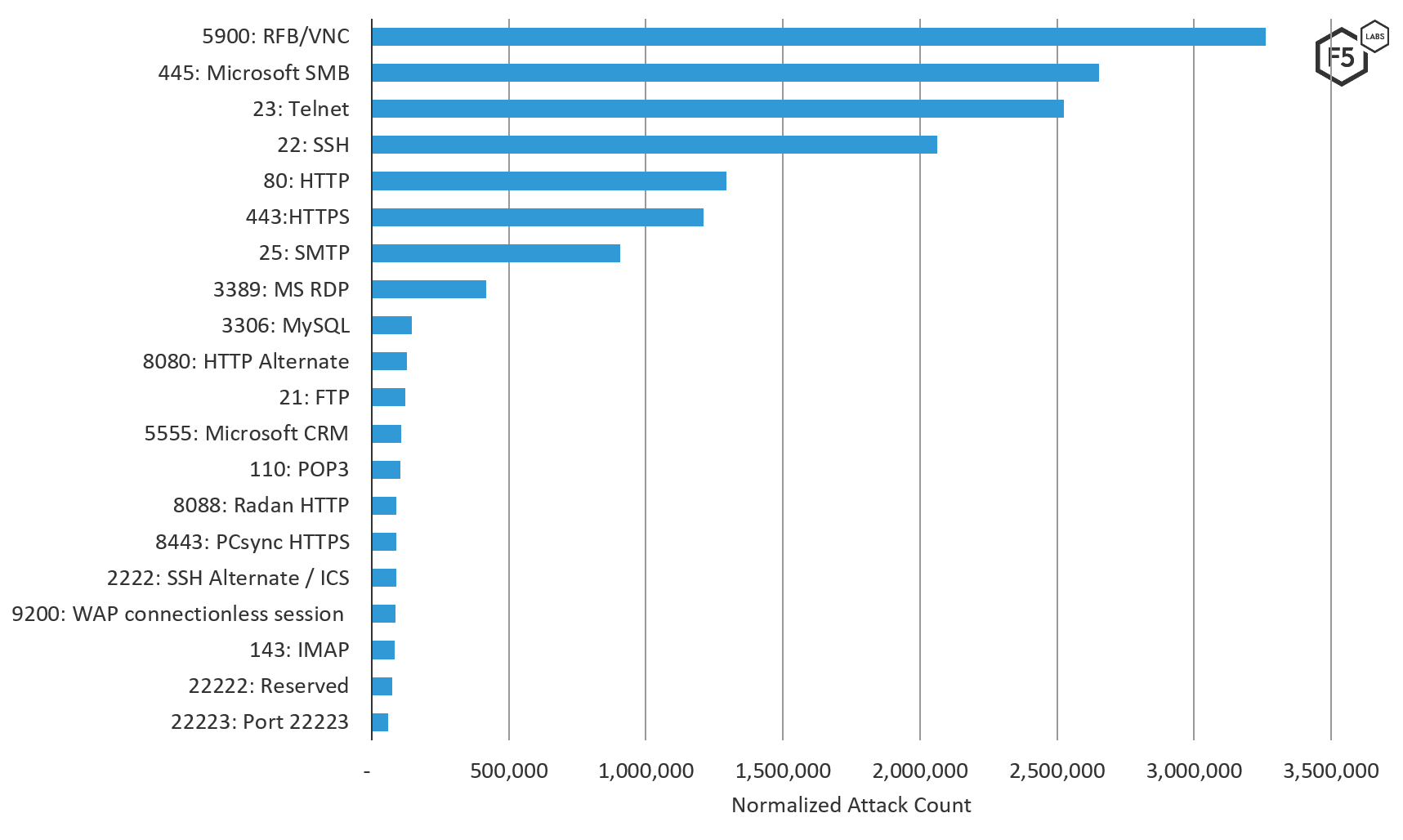
Figure 7. Top 20 ports attacked in Europe, August – October 2019
Conclusion
In general, the best approach a security team can take as defenders in this modern threat landscape is one of “assume breach.” This is not a FUD (fear, uncertainty, and doubt) position, this is a realistic position backed up by the volume of attack traffic that all systems touching the Internet receive, the likelihood of existing vulnerabilities, and the amount of compromised credentials available to attackers. When you take an “assume breach” defensive position, you are collecting attack traffic and monitoring your logs. You can use this high-level attack data to compare against the attack traffic directly hitting your own network. This will help you rule out run-of-the-mill attack traffic, or help you determine whether or not you are being targeted, in which case, investigating the attack sources and patterns is a worthwhile activity.
Additionally, locking down any of the top targeted ports that do not absolutely require unfettered internet access should be completed as soon as possible.
And because default vendor credentials are commonly left in place, and the volume of breached credentials in 2017 (see F5 Labs report Lessons Learned from a Decade of Data Breaches) was enough to determine that many usernames and passwords are now considered “public,” all organizations should have credential stuffing protection in place. Particularly for any system with remote authentication, and especially administrative remote access.
Security Controls
To mitigate the types of attacks discussed here, we recommend the following security controls (/content/f5-labs-v2/en/archive-pages/education/what-are-security-controls.html) be put in place:
Recommendations
- Use firewalls to restrict all unnecessary access to commonly attacked ports that must be exposed publicly on the Internet.
- Never expose internal databases publicly, and restrict access to internal data on a need-to-know basis.
- Prioritize risk mitigation for commonly attacked ports that require external access (like HTTP and SSH) for vulnerability management.
- Protect applications accessible over SSH using brute force restrictions.
- Disable all vendor default credentials (commonly used in SSH brute force attacks) on all systems before deploying them publicly.
- Implement geo IP blocking of commonly attacking countries that your organization does not have a need to communicate with.


