SECTION 1
Nearly 90% of all Internet traffic is encrypted—and we’re quickly moving toward an Internet where that will be true of nearly every piece of data in transit. Although this is great for privacy and confidentiality, it creates a serious blind spot for security.
of malware installed through phishing is hiding in encryption.
ENCRYPTED MALWARE: THE HIDDEN THREAT
By taking advantage of encryption, attackers can bypass most inspection devices to deliver malware inside the network. In addition, encrypted data exfiltration bypasses security tools without scrutiny. F5 Labs threat research shows that 71% of malware uses encryption to hide when it communicates back to command and control locations. Additionally, 57% of malware sites and 95% of phishing sites were accessed just one time, complicating incident response investigations.
Cybercriminals know that organizations have trouble decrypting and inspecting traffic—and they use that to their advantage. Using malware such as spyware, ransomware, and rootkits, as well as exploits, attackers compromise users, networks, and applications to steal personal data.
In 2018, 28% of all data breaches involved some form of malware according to the Verizon 2019 Data Breach Investigations Report. In addition to being used by criminal organizations for financial gain, malware is increasingly employed by state-sponsored entities to disrupt other countries and commit espionage.
Gaining better visibility into encrypted traffic is one of the most important steps you can take to protect your applications and your business.
This problem isn’t new. Over the years, the cyber security industry has designed many tools to detect or block malware and malicious traffic. Organizations deploy technologies such as next-generation firewalls to watch user behavior, sandboxes to find zero-day exploits, intrusion protection systems to block malicious payloads, data loss prevention scanners to prevent data exfiltration, and web gateway services to secure inbound and outbound traffic.
These solutions evolved over the years to become adept at preventing malware from infecting users’ systems and compromising corporate networks or applications. However, they weren't designed for encryption/decryption at scale, so they can't examine what's inside the encrypted traffic. The rise of encrypted data created an opportunity for attackers—and a headache for network administrators. Making matters worse, many inspection devices can’t keep pace with the rapidly changing encryption landscape, such as requirements for Perfect Forward Secrecy (PFS) in TLS 1.3, resulting in blind spots or performance degradation. If you want to keep your apps, your data, and your organization protected against malware, you can’t afford to be blind to encryption.
Bad actors leverage encryption to evade detection, and phishing is one of the more popular attack scenarios.
HOW PHISHING AND MALWARE EVADE DETECTION
Encrypted malware is one of the most serious threats to the enterprise, and can lead to financial losses, reputation damage, service disruption, and data breaches. Compounding the problem is the fact that any time your users access an infected website or click on a malicious attachment in a phishing email, they can pick up a nasty piece of malware.
Malware loves encryption that allows it slip through your traffic undetected, and phishing is one of the more popular attack scenarios. Free and low-cost HTTPS certificate providers make it easier for attackers to infiltrate malware and exfiltrate stolen assets. In the 2019 Application Protection Report, F5 Labs found that phishing was responsible for 21% of breaches. Learn how that happens using phishing malware in this short video.
DEFENDING AGAINST ENCRYPTED THREATS
If you want to keep your apps, your data, and your organization protected against malware, you can’t afford to be blind to encryption. Gaining better visibility into encrypted traffic is one of the most important steps you can take today. The question remains, what’s the best way to do that without degrading application performance? Read the article to help answer that question.
IS TLS 1.3 THE SOLUTION?
Big Changes to Consider
SECTION 2
Not long ago, the Secure Sockets Layer (SSL), or Transport Layer Security (TLS), was used almost exclusively by government agencies and large financial institutions. Today, TLS 1.3 is used by organizations of all kinds to protect their data transmitted through countless sites and applications.
. . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . .
Almost 86% of all page loads over the web are now encrypted with HTTPS.
THE RISE OF TLS 1.3
The adoption of SSL/TLS has been sped up by regulatory standards such as PCI DSS, HIPAA, and the EU’s General Data Protection Regulation (GDPR), which require that transmitted data be encrypted. Moreover, organizations have been spurred to adopt SSL/TLS by Google search results policy, which gives preferential treatment to sites that encrypt.
However, the rise of SSL/TLS isn’t all good news. Attackers are increasingly hiding insidious attacks within encrypted traffic—which means that the security protocol itself has become a threat vector. Regaining visibility into that encrypted traffic is one of the most important steps you can take to protect your apps, your data, and your business.
WHAT IS TLS 1.3?
When a web client (Internet browser) connects to a secure website, the data is encrypted. But, how does all that happen? What type of encryption is used, and how does the Internet browser know what type of encryption the web server wants to use? This is all determined by what is known as a TLS Cipher Suite. See how it all works in this video.
THE TLS 1.3 HANDSHAKE
The handshake process between client and server has changed dramatically with the new TLS 1.3 protocol. The new process is much more efficient and allows encrypted application data to flow much faster than in previous versions. In this video, we outline the TLS 1.3 handshake and all the cool new features it has.
The TLS 1.3 Handshake >
UPGRADING TO TLS 1.3
Encryption standards are constantly evolving, so it’s crucial to stay up to date with current best practices. The newest version of the TLS protocol (version 1.3) was recently approved by the Internet Engineering Task Force (IETF). There are several key changes in this protocol, such as a requirement to use ciphers that support Perfect Forward Secrecy (PFS), and the introduction of a zero round-trip time handshake for session resumption. In this video, we outline many of the important features of this new protocol.
Upgrading to TLS 1.3 >
TLS ADOPTION IN THE ENTERPRISE
TLS 1.3 has been approved by the IETF and contains major improvements in the areas of security, performance, and privacy. The performance boost TLS 1.3 offers is a welcome upgrade, but there are some security challenges with PFS which makes decryption and inspection increasingly difficult.
However, PFS also removes the ability to perform passive inspection and makes it tougher to spot malicious traffic and defend against attacks hidden in that encrypted traffic. To learn more about organizations' strategies, policies and approaches to TLS 1.3 deployments, read the TLS 1.3 Adoption in the Enterprise report.
of IT practitioners said their top concern about encryption was their ability to monitor application security.
INSPECTING ENCRYPTED PACKETS
Know Your Options
SECTION 3
The growth of SSL/TLS traffic has forced organizations to find solutions that enable their network and their applications to respond to the increased demands of widespread encryption.
. . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . .
DOING NOTHING IS A RECIPE FOR DISASTER
Many organizations are not equipped to detect malware hidden in encrypted traffic using their existing security stack. However, as attackers increasingly conceal their malicious code in traffic that security devices can’t see, the do-nothing option is a recipe for disaster. It also wastes money spent on inspection tools, and the effort spent maintaining them. On the surface, it seems there are several options—but only one of them is truly effective.
01 | Decrypt Everything?
Before user privacy became a popular topic, many organizations terminated SSL/TLS at their ingress point and let everything flow freely in cleartext within their data centers.
Now that GDPR and other regulations are in effect, and privacy is in the news due to high-profile breaches and abuses, this is no longer a viable option. Depending on the types of data you collect and its corresponding jurisdiction, you may be subject to various privacy laws and regulations.
02 | Set up a Decryption Zone
Some security teams set up a decryption zone (air gap), where they decrypt inbound and/or outbound traffic before passing it through a daisy chain of security inspection tools and then re-encrypting it.
This solution at least uncovers hidden malware, but it creates routing complexity and makes it harder to change the architecture. Also, catastrophic outages can occur when in-line security devices fail.
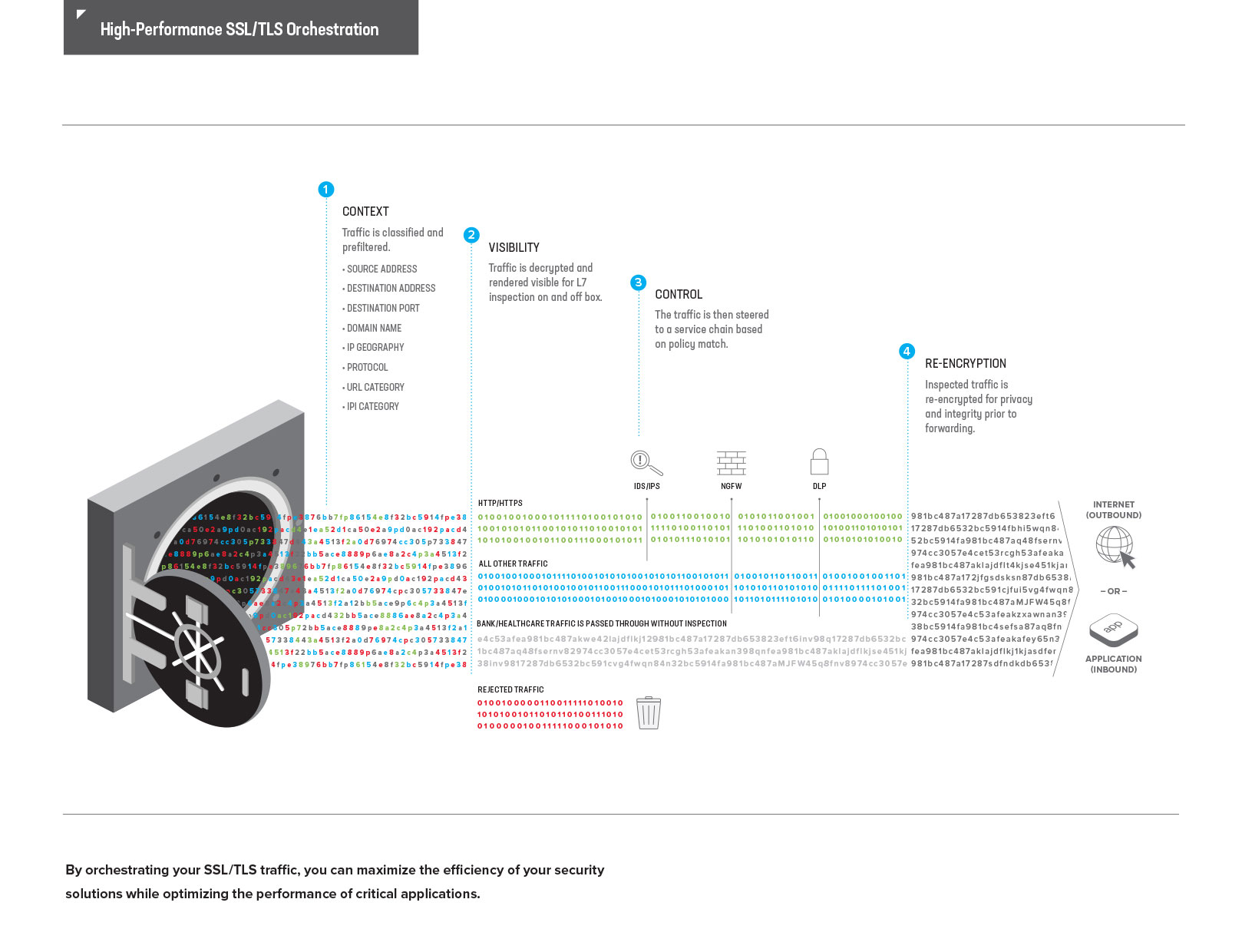
03 | Orchestration
Orchestration is the most effective choice. By applying policy-based decryption and traffic steering to both your inbound and outbound traffic, you can conduct your orchestration of security devices like a maestro.
A high-performing SSL/TLS orchestration solution improves visibility and protects your apps while increasing the security, efficiency, and resilience of your security stack. There is only one SSL decrypt and re-encrypt operation, so automatically you’ve removed the latency of the daisy-chain approach.
This process is so critical that the NSA published an advisory titled “Managing Risk from Transport Layer Security Inspection.” The advisory says that to minimize risk, breaking and inspecting TLS traffic should only be conducted once within the enterprise network. The advisory also strongly recommends against redundant TLSI, where a client-server traffic flow is decrypted, inspected, and re-encrypted by one forward proxy and is then forwarded to a second forward proxy for more of the same.
SEE ENCRYPTED THREATS WITH SSL VISIBILITY
Security inspection tools are increasingly blind to SSL/TLS traffic. While some security solutions include native decryption capabilities, performing decryption and encryption at scale aren’t their core purpose or focus. Without that, encrypted traffic must go through the static daisy chain of a repetitive decrypt/inspect/re-encrypt process across the entire security stack.
This process consumes precious time and resources, adds latency, and disrupts user experience. Plus, it can easily lead to over-subscription—meaning increased costs for oversized security services.
F5 SSL Orchestrator, with its full proxy architecture and dynamic service chaining, presents a true paradigm shift in the way you can deal with malware in your environment. Protect against encrypted threats with SSL visibility.
READY TO STOP ENCRYPTED MALWARE?
Because SSL Orchestrator functions as a full proxy for both SSL/TLS and HTTP, it can make intelligent decisions to steer inbound and outbound traffic to service chains within the security stack, no matter how complicated your inbound and outbound encryption requirements are.
See how SSL Orchestrator provides visibility into encrypted inbound application traffic—including how it dynamically chains security services and applies context-based traffic steering.
The Benefits of Orchestration
Moving Beyond Visibility
SECTION 4
We’ve established that better visibility into encrypted traffic is key to securing your data. An SSL/TLS orchestration solution provides cost-effective decryption and encryption of inbound and outbound traffic—mitigating risk with a flexible policy-based approach.
. . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . .
F5’s SSL Orchestrator provides high-performance decryption of inbound and outbound SSL/TLS traffic, enabling security inspection to expose threats, stop attacks, and reduce business risk.
01 | Visibility Into Encrypted Traffic
With a robust SSL/TLS solution, you get decryption and re-encryption, as well as strong cipher support (including TLS 1.3), all of which allows you to see what’s going on in your encrypted traffic.
02 | Optimal Flexibility
A solution with a full-proxy architecture gives you more control over, and more flexibility with, the different security inspection devices, network topologies, and supported ciphers in your infrastructure. It also lets you monitor and load balance your security devices to ensure that they’re functioning at peak efficiency. You can even skip a device entirely in case of failure, which adds resiliency to your network.
03 | Efficient and Dynamic Service Chaining
This is where the real magic is. F5 SSL Orchestrator can dynamically assign, chain together, and re-use security services. This means you can drive different types of traffic through different sets of security devices, and reuse those devices in different chains—or not use them at all for traffic that does not need inspection. This makes it easy to categorize traffic so you can intelligently route it to, or around, inspection devices based on a number of different factors, including the role of specific users. You can dynamically assign, chain together, and reuse security services on the fly.
With dynamic service chaining, you can scale your SSL/ TLS solution and maximize the usage of your current security devices by letting them concentrate on the areas where they can best protect your organization. In addition, you can add or remove security services without experiencing downtime.
04 | Better Performance
There’s only one decrypt/re-encrypt process rather than several; and it’s carried out by a high-performance orchestration device built for just that purpose.
05 | Centralized Management
By selecting an SSL/TLS solution that provides centralized management, you can simplify the process of choosing and updating the cipher suites that help secure network connections using SSL/TLS. This drives better performance of your traffic inspection security tools, while allowing greater flexibility in managing the ciphers you use in end-to-end encryption. When necessary, the solution can support secure key storage outlined in Federal Information Processing Standards (FIPS).
SSL Orchestrator has a full-proxy architecture, which gives you more control and more flexibility over different protocols and ciphers.
INTEGRATE AND ORCHESTRATE WITH YOUR CURRENT INFRASTRUCTURE
SSL Orchestrator fits easily into your existing architecture by integrating with leading security partners. This solution creates an ecosystem that strengthens security, increases scale and availability, and lowers operational costs. SSL Orchestrator supports multiple deployment modes, easily integrating into complex architectures to centralize decryption for both inbound and outbound traffic.
SSL Orchestrator has a full-proxy architecture, which gives you more control and more flexibility over different protocols and ciphers. And it can load balance, monitor, and potentially skip failed devices. The architecture allows you to not only scale, but also intelligently maximize the correct usage of your existing security investment.
SEE HOW SSL ORCHESTRATOR WORKS WITH YOUR CURRENT INFRASTRUCTURE
Designed to easily integrate with existing and changing architectures, and to centrally manage the SSL/TLS decrypt/encrypt function, F5 SSL Orchestrator delivers the latest SSL/TLS protocol versions and encryption ciphers across your entire security infrastructure.
SSL visibility is only the start. Organizations need better control over their security investments, and that’s where the benefits of SSL Orchestrator really shine.
VISIBILITY IS ESSENTIAL—BUT SSL ORCHESTRATOR OFFERS MORE
Adding F5 SSL Orchestrator to your environment ensures encrypted traffic can be decrypted, inspected by security controls, then re-encrypted. As a result, you can maximize your investments in security inspection technologies—preventing inbound and outbound threats including exploitation, callback, and data exfiltration—which also enhances your cyber-resilience strategy. Read the article to learn more about the benefits managing the flow of all encrypted traffic across your entire security chain.
CUSTOMER STORY:
MEDICAL DATA VISION COMPANY
“We handle clinical data, so security is a backbone of our business systems and we have to focus intensely on maintaining it. The threat of targeted cyberattacks is an ever-growing one that forces us to always stay a step ahead.”
Yukihiro Watanabe
Senior Manager, Sakura DB Division Chief, Medical Data Vision Co., Ltd.
The increase in SSL/TLS traffic shows that organizations are more focused on safeguarding customer data and meeting compliance mandates related to encryption, like GDPR.
It’s essential to move beyond visibility and orchestrate the inspection of encrypted traffic, to allow your security inspection devices to protect your apps, users, and networks. With a robust SSL/TLS orchestration solution, you’ll enjoy better visibility, increased performance, and more flexibility—so you can stop worrying about hidden malware and application exploits and focus on developing and supporting new apps to drive your business.
SPEAK TO AN F5 SECURITY EXPERT
Got a security question, issue, or something else you’d like to discuss?
We’d love to hear from you!