Introduction
Just as we continually analyze the threat landscape, we also look to broaden and improve our telemetry to provide the best possible insights from our datasets. With this, in this article we are excited to share analysis drawn from the F5 Honeynet. This network of sensors deployed across the globe, includes many honeypots running multiple enterprise applications and is one of the components that powers F5 Threat Campaigns signatures. This allows us to drill further down into our threat data deeper than ever before. As we adjust to this new dataset, our Sensor Intel Series will see some changes to how we report on our key findings and statistics. But, as always, underpinning everything we report on is the real attacks we are detecting each month.
This month, we dive into a new scanning campaign focused around the WordPress CVE-2018-14028 vulnerability, but departing from traditional webshell deployment attacks which we would normally expect to see with this vulnerability, the malicious actor is attempting to utilize existing, and potentially long-forgotten, webshells.
Azure-Hosted Scanning Cluster Launches WordPress Webshell Discovery Campaign
By grouping vulnerability exploit attempts into sessions, we have been able to normalize the statistics that we report on when analyzing attacks. Some attacks require multiple steps or employ brute forcing techniques against unknown infrastructure in order to maximize exploitation success. This can heavily skew our results, so we have changed the way we count these in our analysis.
In March 2026, F5 sensors recorded 1,897 session-grouped exploitation attempts (2,821 raw events) targeting CVE-2018-14028, an unrestricted file upload vulnerability in WordPress. This CVE was entirely absent from the previous month's top 10 exploited vulnerabilities, making its sudden appearance a notable shift in the threat landscape.
The most striking characteristic of this campaign is its infrastructure. Of the top 30 source IPs responsible for CVE-2018-14028 exploitation attempts, 29 operate from Microsoft Azure address space, spanning multiple global regions. The top sources include:
| Source IP | Events | Address Range |
|---|---|---|
74.235.238.88 |
313 | Microsoft (74.235.x.x) |
20.151.201.236 |
251 | Azure (20.x.x.x) |
4.204.246.56 |
225 | Azure (4.x.x.x) |
20.63.96.180 |
150 | Azure |
20.63.100.156 |
132 | Azure |
20.104.124.39 |
128 | Azure |
20.48.232.178 |
125 | Azure |
20.151.11.236 |
124 | Azure |
Table 1: Top 8 Malicious IP addresses linked to webshell scanning campaign
This near-total concentration within a single cloud provider's address space strongly suggests a single operator provisioning cloud instances at scale for coordinated scanning, rather than independent actors coincidentally choosing the same platform.
The scanning was indiscriminate. These WordPress-specific URL paths were sprayed across all application types observed by our sensors, including enterprise collaboration platforms, remote access gateways, IT service management interfaces, virtualization management consoles, and web application servers. The attackers made no effort to fingerprint target applications before sending WordPress-specific requests, confirming fully automated mass scanning.
URL Patterns Reveal Webshell Hunting
The requested paths tell a clear story. Rather than attempting the initial file upload exploit, the campaign is scanning for previously planted PHP webshells in predictable WordPress directories:
| Path | Events |
|---|---|
/uploads/2021/02/index.php |
143 |
/wp-content/upgrade/about.php |
107 |
/wp-content/uploads/admin.php |
107 |
/wp-content/uploads/index.php |
101 |
/wp-content/upgrade/index.php |
50 |
Table 2: Scanned potential webshell paths
The filenames are generic (index.php, about.php, admin.php), suggesting the operators are looking for webshells deployed by a specific toolkit that uses standardized naming conventions. The date-stamped path /uploads/2021/02/ follows WordPress's media upload directory structure, indicating the scanners are searching for webshells planted during a specific earlier campaign, potentially dating back to early 2021.
Multipurpose Scanning Infrastructure
Cross-referencing the top Azure scanning IPs against all honeynet activity reveals that CVE-2018-14028 probing is just one component of a much larger scanning operation:
| IP | CVE-2018-14028 | CVE-2017-12932 | Generic Scanning |
|---|---|---|---|
20.63.96.180 |
150 | 101 | 42,789 |
20.48.232.178 |
125 | 302 | 37,171 |
20.151.11.236 |
124 | 156 | 27,367 |
20.104.124.39 |
128 | 151 | 21,871 |
20.220.232.101 |
97 | 151 | 17,059 |
Table 3: Threat actor related activity
Each of these IPs generates tens of thousands of non-CVE-tagged events, meaning the WordPress webshell scanning represents a small fraction of their total activity. These are general-purpose scanning nodes running broad reconnaissance toolkits. The co-occurrence of CVE-2017-12932 (a PHP deserialization vulnerability) alongside CVE-2018-14028 from the same IPs suggests the toolkit bundles multiple PHP and WordPress exploit checks together.
Vulnerability Context
CVE-2018-14028: WordPress Unrestricted File Upload
- CVE ID: CVE-2018-14028
- Affected Product: WordPress 4.9.7
- Vulnerability Type: CWE-434 (Unrestricted Upload of File with Dangerous Type)
- Published: August 10, 2018
How the Vulnerability Works
CVE-2018-14028: The Mechanics
CVE-2018-14028 exploits a flaw in WordPress 4.9.7's plugin upload functionality. Under normal operation, WordPress administrators can upload plugins as ZIP files through the admin dashboard. The vulnerability exists because WordPress does not verify that the uploaded file is actually a ZIP archive before processing it.
Here is how the attack chain works:
- Authentication required: The attacker must first obtain valid WordPress administrator credentials (through credential stuffing, phishing, brute force, or other means).
- Direct PHP upload: Instead of uploading a legitimate plugin ZIP file, the attacker uploads a raw PHP file (a webshell) through the plugin upload mechanism. WordPress accepts the file without validating its type.
- Failed extraction, persistent file: WordPress attempts to extract the "plugin" as if it were a ZIP archive. The extraction fails because the file is not a ZIP, but critically, the uploaded PHP file is not cleaned up. It remains on disk in a predictable location within the wp-content/uploads/ or wp-content/upgrade/ directory.
- Remote code execution: The attacker can then directly access the uploaded PHP file via its predictable URL path (e.g., https://target.com/wp-content/uploads/admin.php), achieving remote code execution on the web server.
The impact is severe: full remote code execution in the context of the web server process. An attacker with a functioning webshell can execute arbitrary commands, exfiltrate data, pivot to internal networks, or use the compromised server as infrastructure for further attacks.
What we're observing in March 2026 is not the initial exploitation (step 2), but step 4: the attackers are scanning the internet for PHP files that were previously uploaded via this mechanism, checking whether webshells are still accessible at the predictable paths where CVE-2018-14028 deposits them.
Threat Assessment
This activity represents a sustained, cloud-hosted webshell discovery campaign with a clear operational model:
- Infrastructure: The operator provisions scanning nodes exclusively within Microsoft Azure, leveraging the cloud provider's global presence to distribute scanning across multiple regions. The use of a legitimate cloud platform provides several advantages: high bandwidth, clean IP reputation (relative to known bulletproof hosting), and the ability to rapidly scale up or tear down instances.
- Objective: The scanning is focused on discovering previously planted webshells rather than performing initial exploitation. This implies one of three scenarios:
- The operator planted webshells in a prior campaign and is now "harvesting" them
- The operator is attempting to discover and hijack webshells planted by other threat actors
- The operator is conducting broad reconnaissance to identify compromised WordPress installations for subsequent exploitation
- Scale: The campaign is one component of a larger scanning operation. The same Azure infrastructure conducts broad, multi-protocol scanning across the internet, with WordPress webshell probing representing a specialized module within a general-purpose scanning toolkit.
MITRE ATT&CK Mapping
| Technique | ID | Description |
|---|---|---|
| Active Scanning: Vulnerability Scanning | T1595.002 | Mass scanning for WordPress webshell artifacts across the internet |
| Exploit Public-Facing Application | T1190 | Targeting WordPress file upload vulnerability for initial access |
| Server Software Component: Web Shell | T1505.003 | Scanning for previously planted PHP webshells in WordPress directories |
| Acquire Infrastructure: Virtual Private Server | T1583.003 | Provisioning Azure cloud instances across multiple global regions |
| Resource Development: Develop Capabilities | T1587 | Coordinated multi-node scanning toolkit with bundled PHP/WordPress checks |
Table 4: Azure threat actor MITRE ATT&CK map
Trend Context: A Clear Escalation Pattern
Historical comparison reveals a deliberate scaling of this campaign over the first quarter of 2026.
CVE-2018-14028 exploitation was already occurring from Azure infrastructure, but at lower volume and with broader geographic distribution. The scanning nodes were spread across at least 10 countries:
| IP | Country | Events |
|---|---|---|
172.190.142.176 |
US | 269 |
20.189.202.45 |
JP | 64 |
52.231.66.246 |
KR | 51 |
20.5.72.178 |
AU | 45 |
4.206.20.144 |
CA | 45 |
20.219.0.101 |
IN | 42 |
20.78.169.245 |
JP | 42 |
20.205.3.49 |
HK | 39 |
Table 5: Source geographical distribution
Additional Azure IPs were observed in Ireland, Singapore, France, and Norway. The top source generated only 269 events, and the overall volume was modest.
By March, the campaign scaled significantly. The top source IP (74.235.238.88) alone produced 313 events, exceeding the previous period's top source. Overall volume increased to 1,897 session-grouped attacks, and the campaign entered the top 10 exploited CVEs for the first time.
This progression, from distributed low-volume testing across many Azure regions to concentrated higher-volume scanning, is consistent with an operator who established and validated their scanning infrastructure in January–February and then scaled up operations in March.
Top CVEs for March 2026
| # | CVE ID | Description | CVSS | Attacks | Raw Events |
|---|---|---|---|---|---|
| 1 | CVE-2024-4577 | PHP CGI on Windows Argument Injection | 9.8 | 16,271 (+2,065) | 29,285 (+3,728) |
| 2 | CVE-2017-9841 | PHPUnit eval-stdin Remote Code Execution | 9.8 | 12,480 (+1,197) | 421,639 (+48,014) |
| 3 | CVE-2018-20062 | ThinkPHP Remote Code Execution in NoneCms | 9.8 | 11,356 (+1,298) | 23,457 (+2,961) |
| 4 | CVE-2025-55182 | React Server Components Pre-Auth RCE | 10 | 4,290 (+2,038) | 32,832 (+23,568) |
| 5 | CVE-2021-34523 | Microsoft Exchange Server Privilege Escalation | 9 | 2,512 (+143) | 6,192 (+2,777) |
| 6 | CVE-2022-41082 | Microsoft Exchange Server Remote Code Execution | 8 | 2,376 (+77) | 2,550 (+106) |
| 7 ↑1 | CVE-2021-26855 | Microsoft Exchange Server SSRF ProxyLogon RCE | 9.1 | 2,093 (+104) | 2,607 (+139) |
| 8 ↓1 | CVE-2025-55184 | React Server Components Pre-Auth DoS | 7.5 | 2,090 (-140) | 11,081 (+2,972) |
| 9 | CVE-2018-14028 | WordPress Plugin Upload ZIP Verification Bypass | 7.2 | 1,897 (+809) | 2,821 (+875) |
| 10 NEW | CVE-2020-15505 | MobileIron Core Remote Code Execution | 9.8 | 1,410 | 2,735 |
Table 6: Top 10 CVEs for March 2026
Trending CVEs for March
CVE-2025-55182
Climbing to position 4 with a near-doubling of activity from 2,252 to 4,290 attacks (a 90.5% increase), this CVSS 10.0 vulnerability demands immediate attention. CVE-2025-55182 is a pre-authentication remote code execution flaw in React Server Components, allowing unauthenticated attackers to achieve full system compromise. With only three months of observed activity and an accelerating exploitation curve, this vulnerability appears to be gaining traction among threat actors targeting modern JavaScript-based application stacks.
CVE-2020-15505
New to the Top 10 this month, CVE-2020-15505 enters at position 10 with 1,410 attacks. This is a critical (CVSS 9.8) remote code execution vulnerability in MobileIron Core, a widely deployed mobile device management platform. Its appearance is notable because the vulnerability is nearly six years old, suggesting threat actors are cycling back to target unpatched MDM infrastructure, which often holds privileged access to enterprise mobile fleets and sensitive configuration data.
CVE-2017-16894
Dropping out of the Top 10 after holding position 2 last month, CVE-2017-16894 recorded zero exploitation activity in March, a complete and sudden cessation. This abrupt disappearance from a high-ranking position is unusual and may indicate that a specific campaign or botnet leveraging this vulnerability has been disrupted or has shifted tactics. Defenders who deprioritized this CVE should remain cautious, as such gaps can be temporary before activity resumes.
CVE-2024-4577
Holding the top position for a second consecutive month, CVE-2024-4577 recorded 16,271 attacks, up from 14,206 in February. This PHP CGI argument injection vulnerability on Windows (CVSS 9.8) allows remote attackers to execute arbitrary code by exploiting how PHP processes CGI arguments. Its steady escalation from 8,102 attacks in December to over 16,000 in March confirms it as the most actively targeted vulnerability in our dataset, and defenders running PHP in CGI mode on Windows should treat patching as an emergency priority.
CVE-2018-14028
Surging 74% from 1,088 to 1,897 attacks, CVE-2018-14028 climbed into position 9 with the largest percentage increase among returning entries. This vulnerability targets a WordPress plugin that fails to properly verify uploaded ZIP files, enabling attackers to bypass upload restrictions and deploy malicious code. The sharp increase suggests renewed automated scanning campaigns targeting WordPress installations, reinforcing the need for defenders to audit plugin inventories and enforce strict upload validation controls.
Long Term Targeting Trends
Top CVEs
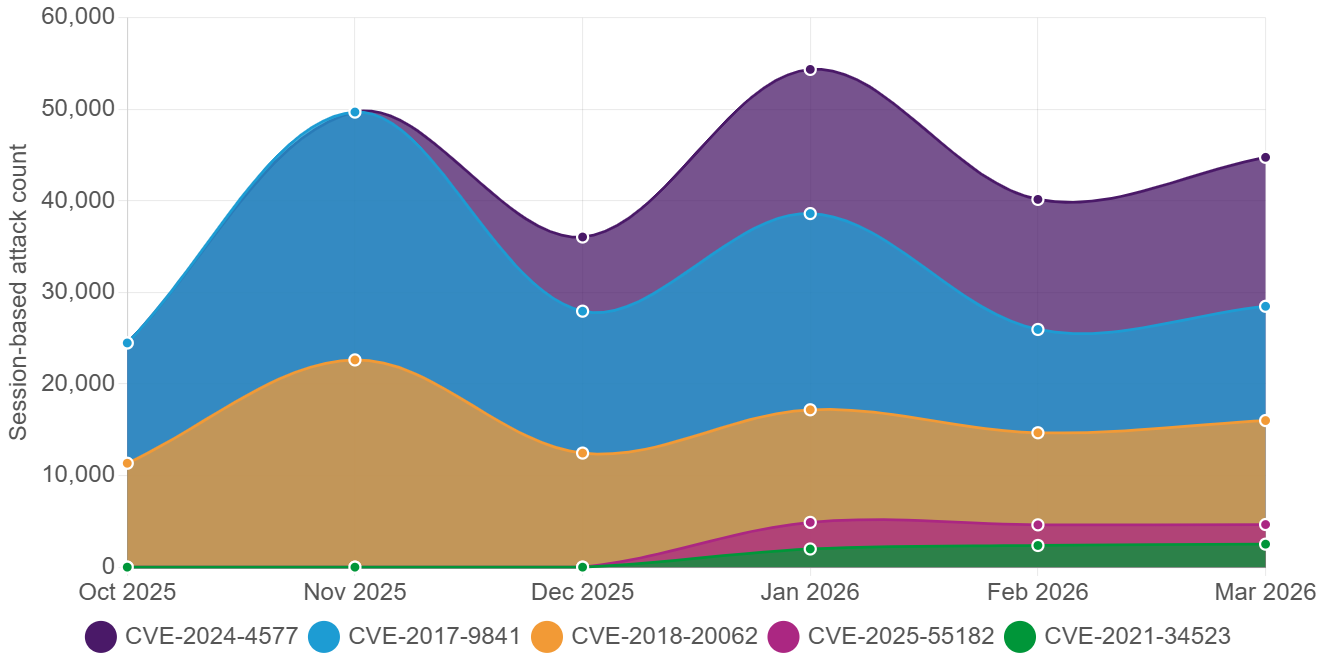
Figure 1: Six-month stacked graph of the top 5 CVEs.
CVE-2024-4577 continues its upward climb, reaching 16,271 exploitation attempts in March, the highest single-month total for any CVE in the dataset. It has now overtaken CVE-2017-9841 as the most targeted vulnerability, despite only appearing in the data four months ago. CVE-2017-9841 remains persistently exploited across all six months, totaling 100,907 attempts, though its March figure of 12,480 is well below its November peak of 27,075. CVE-2021-34523, targeting Microsoft Exchange, has shown steady month-over-month growth since its January emergence, reaching 2,512 in March. CVE-2025-55182, a critical CVSS 10.0 React Server Components flaw, has maintained consistent exploitation around 2,100 to 2,900 attempts per month since January, indicating sustained attacker interest in this newer vulnerability.
Attack Types Over Time
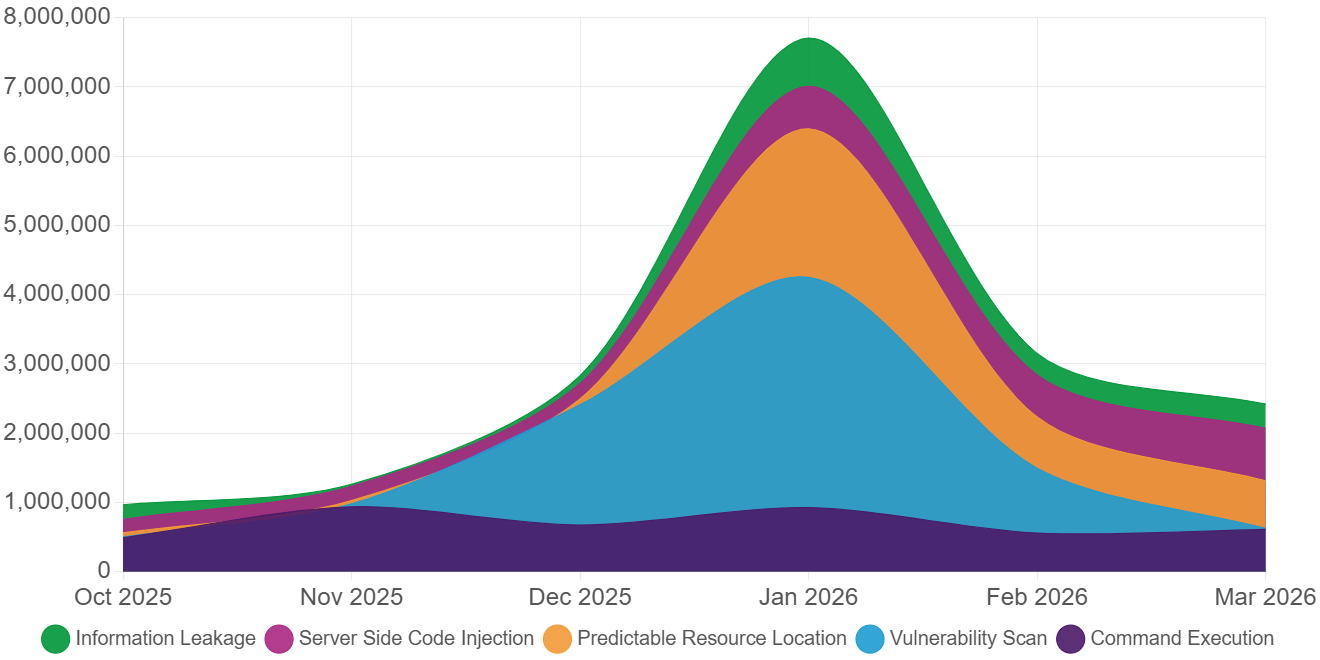
Figure 2: Evolution of attack types over 6 months
The most dramatic shift in March 2026 is the near-total collapse of Vulnerability Scan activity, plummeting from 937,771 in February to just 16,620, a 98.2% decrease. This extraordinary drop may indicate a change in scanning. Server Side Code Injection rose to 758,681 from 608,877, a 24.6% increase that positions it as the second-highest category for the month. Command Execution also climbed to 608,880 (up 9.6%), while Predictable Resource Location dipped slightly by 7.3% to 685,078. Trojan, Backdoor, and Spyware detections increased 33.9% to 79,573, and Cross Site Scripting rose 23.5% to 81,806. Defenders should note the shift toward active exploitation categories like code injection and command execution, which represent more immediate compromise risk than passive scanning.
The United States remains the top source of attack traffic in March 2026 at 4,835,985 events, a 56.4% increase over February's 3,091,452. Germany saw the most aggressive growth, surging 114.2% from 1,662,237 to 3,560,239, solidifying its position as the second-largest source. Canada experienced the most extreme proportional jump, skyrocketing 394.1% from 143,807 to 710,596, suggesting the activation of new attack infrastructure in Canadian IP space. Singapore more than doubled its output to 1,303,632 (up 105.5%), while France showed a more modest 8.7% increase to 943,888. The broad increases across all five top source countries align with the overall 66.5% rise in attack volume and suggest a geographically distributed expansion of malicious activity rather than a single-region campaign.
Top Target Destinations
Canada
Canadian sensors receive a consistent mix of web application exploitation and brute-force login attempts. The attack profile here is notable for a relatively elevated share of directory traversal and file inclusion techniques compared to other monitored regions.
United States
Sensors in the United States continue to absorb the highest volume of attack traffic across our honeynet, consistent with its position as the most targeted destination over the past year. The attack profile is broad, spanning credential brute-forcing, remote code execution attempts, and web application exploitation, reflecting the diverse internet-facing footprint adversaries associate with U.S. infrastructure.
United Kingdom
Our honeynet sensors in the United Kingdom face a diverse attack mix weighted toward web application exploitation and remote code execution. A distinguishing characteristic is the frequency of server-side request forgery and injection attempts targeting web-facing endpoints.
South Korea
Attack traffic hitting South Korean sensors is heavily oriented toward remote code execution and exploitation of management interfaces. The profile here uniquely features a higher prevalence of attempts to abuse administrative and API endpoints compared to other monitored locations.
Singapore
Sensors in Singapore capture a concentrated stream of exploitation attempts focused on web services and remote access protocols. This location is notable for a disproportionate volume of traffic originating from nearby regional sources, indicating localized threat actor interest in Southeast Asian infrastructure.
Conclusion
- A coordinated webshell discovery campaign targeting CVE-2018-14028 entered the top 10 exploited vulnerabilities in March 2026 with 1,897 session-grouped attacks, after being absent from the previous month's rankings.
- 29 of the top 30 source IPs operate from Microsoft Azure address space, strongly suggesting a single operator provisioning cloud infrastructure at scale for coordinated scanning.
- The attackers are not exploiting the vulnerability directly. They are scanning for PHP webshells previously planted via CVE-2018-14028 in predictable WordPress directories, including date-stamped paths suggesting a campaign from early 2021.
- The campaign escalated from a smaller operation in January–February 2026 into a significantly larger effort in March, indicating deliberate scaling of scanning infrastructure.
- These are multipurpose scanning nodes. Each top Azure IP generates tens of thousands of total events, with WordPress webshell probing representing one module in a broader scanning toolkit.
- Despite being nearly eight years old and not listed on CISA KEV, CVE-2018-14028 remains actively targeted. Organizations running WordPress should audit upload directories for unexpected PHP files immediately.
Recommendations
Immediate Actions
- Audit WordPress upload directories now. Inspect wp-content/uploads/, wp-content/upgrade/, and all date-stamped upload subdirectories (especially /uploads/2021/02/) for unexpected PHP files. Legitimate WordPress uploads in these directories are media files (images, documents, videos), not PHP scripts. Any PHP file in these locations should be treated as a confirmed indicator of compromise and investigated immediately.
- Block PHP execution in upload directories. Configure your web server to prevent PHP execution within WordPress upload and upgrade directories.
- Update WordPress. CVE-2018-14028 affects WordPress 4.9.7, released in July 2018. Any installation still running this version has critical security gaps far beyond this single vulnerability. Update to the latest WordPress release immediately.
Ongoing Defensive Measures
- Strengthen WordPress admin authentication. Since CVE-2018-14028 requires authenticated access, enforce strong passwords and multi-factor authentication on all WordPress admin accounts. Audit for unauthorized admin accounts and remove any that cannot be attributed to legitimate users.
- Deploy file integrity monitoring. Implement monitoring on WordPress installations to detect unauthorized file additions to upload, upgrade, and plugin directories. This provides defense against both this specific vulnerability and broader webshell deployment techniques.
- Monitor for Azure-sourced scanning. The identified Azure IP ranges (20.x.x.x, 4.204.x.x, 52.x.x.x, 40.x.x.x, 74.235.x.x, 172.190.x.x) are generating significant scanning volume. While blocking entire Azure ranges is impractical for most organizations, enhanced logging and rate-limiting for requests targeting WordPress upload paths from cloud provider address space can provide early warning of compromise attempts.
- Review web application firewall rules. Ensure WAF rules are configured to detect and block requests for PHP files in WordPress upload directories. The specific paths observed in this campaign (/wp-content/uploads/*.php, /wp-content/upgrade/*.php, /uploads/YYYY/MM/*.php) can be used as detection signatures.


