Information Security Controls are the bread and butter of audit professionals, the bane of developers, and the playground of security professionals. From a business perspective, they provide a means for enabling business resiliency by protecting and reducing the risk associated with the threat landscape. Insofar as the concept of defense in depth is embraced, it’s impact is reduced to mere banding about when we consider ever-present security breaches. If your strategy of control design is based on effectiveness, you do not have true defense in depth, you have a single thread of defense. We learned from our analysis of a reference architecture that businesses and their information systems have multiple attack vectors, therefore, controls modeled from multiple perspectives. This is what yields a truly defense-in-depth environment along with resiliency of controls and continuous compliance. Five steps can get you there.
Step 1: Foundational Controls
A primary outcome of implementing a best-in-class information security program is maintaining the state of due care and due diligence. These states are maintained when what is considered as basic controls are present in a system. A rational method of control organization can be found in NIST 800-53 v41 where controls are situationally categorized as: common, system-specific, and hybrid. Common controls provide a state of inheritance as they protect the various subsystems of an information system. Enterprise user directories providing authentication and authorization are examples of a common control in that they enable access to multiple systems across a SOA architecture. System-specific controls reside with service-specific systems, examples are database or web server controls. Hybrid is a blend of common and system-specific such as an antivirus (AV) management solution where the AV solution is specific to protecting against malware yet providing common protection to specified clients. The modes of inheritance through common and hybrid controls enables efficient control design resulting in reduced control sprawl, operational cost, and technology complexity.
Implementation of foundational controls provides the first tier of defense, with further effectiveness maximized through environmental application.
Step 2: Environment
Environmental controls are a superset of systems views of physical, logical, and virtual contained within a chassis (appliance) or across interoperable information systems, enabling scaling of foundational controls. Routers and next generation firewalls can provide boundary protection physically, logically, and virtually as a common control. Platforms (for example, Microsoft Windows) can provide inheritance of controls to virtual tiers through hardening of the physical and logical tiers. Likewise, virtual tiers can support a lattice-based model of security, enabling varied access based on interaction between associated objects and subjects.
Implementation of environmental controls provides the second tier of defense, with further effectiveness maximized through functional application.
Step 3: Functional Controls
The premise of defense is depth is “manage risk with diverse defensive strategies, so that if one layer of defense turns out to be inadequate, another layer will hopefully prevent full breach.”2 Foundational controls are less effective when designed non-functionally, meaning while operational, if compromised other controls will fail in a domino effect. Functional controls in contrast are designed to withstand compromise should another control fail. Controls are made functional by designing toward the expectation of compromise, failure and control reaction.
Control reaction is preventative, detective and corrective.3 Preventative controls prevent breach or exploitation, whereas detective controls provide alerts based on characteristics, patterns, and other indicators of compromise. Corrective controls provide automated remediation of threat execution or block active threat continuation. Ordering your foundational controls based on reaction enables control resiliency, ensuring offensive protection to a failed control along with further tuning through tiered situational application.
Step 4: Situational
Situational controls, Priority and Use Case, contain characteristics enabling agile threat modeling design and integration and are based on three modes of operation, as shown in the table below:
| Situational | |||
| Priority | Use Case | ||
| Mode | Operation | Mode | Operation |
| Primary | Permits authorized actions, blocks unauthorized actions | Who (you are) | Authorized human or non-human user |
| Secondary | When primary fails, may block, correct, and alert unauthorized actions | Where (you are) | Internal to the infrastructure or external in an untrusted environment |
| Tertiary | When secondary fails, alerts and block unauthorized actions | What (you have) | Company-owned device (full form factor) Company-owned device (small factor) Personal device |
This view-based application of controls ensures adequate coverage for a variety of user types, access circumstances, and scaling to accommodate varied technology and enable adaptive defense without manual intervention. The strength of these controls are further enhanced when information flow is considered, as information is the end-goal of attackers.
Step 5: Threat Flow
Threat flow is based on ingress and ingress activity. This is where mechanisms and solutions are categorized based on their ability to protect ingress or egress flow of information in combination or autonomously. For example, a DDoS control configured to meter traffic volume is an ingress control to prevent and alert against DDoS attacks. In contrast, an edge router configured to send alerts to a SIEM that is alerting to exceeded traffic thresholds is an egress control.
Controls Modeled on Value
We are now at the core of control design complexity with a need to quantify and qualify the schemes by which controls may be designed. Use of a value ladder enables a tiered yet interactive view of all options organized based on value, as seen in the Figure 1 below.
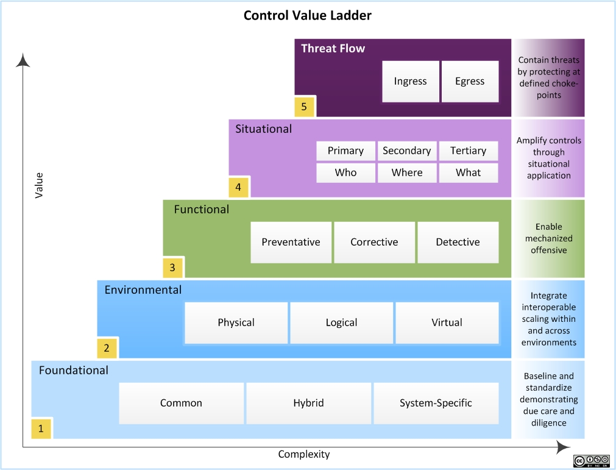
Figure 1: Control value ladder for measuring defense and depth and control complexity.
Integration of the complete control tier and its components provides a meshed control architecture that demonstrates true defense in depth.
Sanity Check
If you’re an Information Security leader, consider how you’d arranged your control ladder. After building your control ladder, how does it align to your exist roadmap and does it support gap remediation?
If you’re part of the technical staff, if your leadership presented you with a value ladder, what technical solutions, mechanism and configuration specifications align to each rung?
In part 5, we will discuss strategies for implementing.


