True to form, the hacktivist group Anonymous continues to make DDoS tools available to even the most unsophisticated user. In February 2016, the group published its latest YouTube video containing detailed examples of uses for various DDoS tools. The video description contains a link to a zip file containing these tools.

Figure 1: Screenshot from the Anonymous DDOS Tools 2016 video on YouTube
2016 Tools Bundle
A substantial number of DDoS tools (20, in fact) are included in this bundle. All of them are easy to use, and have nice GUI menus. It’s not necessary to have any understanding of how the attacks work in order to operate the tools. This makes them very appealing to laypersons with little understanding of computer networking.

Figure 2: Screenshot from the video of multiple attack tools in use at once
Most of the tools offer similar DDoS attack types—primarily HTTP, TCP, and UDP floods—but there is some interesting differentiation. For example, some tools offer more Layer 7 attack granularity, while giving the attacker control of the attacked URL folders and parameters as well as supporting POST floods. Other tools such as Anonymous Ping Attack and Pringle DDoS focus on a single attack type: ICMP flood.

Figure 3: Screenshot of Pringle DDoS, a simple ICMP flooder
If an attacker wants to launch a powerful Low and Slow DDoS attack, surprisingly, he or she will find only a single tool in this bundle. That is the well-known Slowloris.pl Perl tool, which is not authored by Anonymous at all. R.U.D.Y and other slow POST tools are noticeably missing from this bundle.
Another group of tools provides some evasions, such as support for sending requests with different user agent and referrer headers. For example, UnKnown DoSer, a Layer 7 flooder, even supports randomization of URL, User-Agent, and the Content-Length values in order to bypass hard-coded attack signatures.
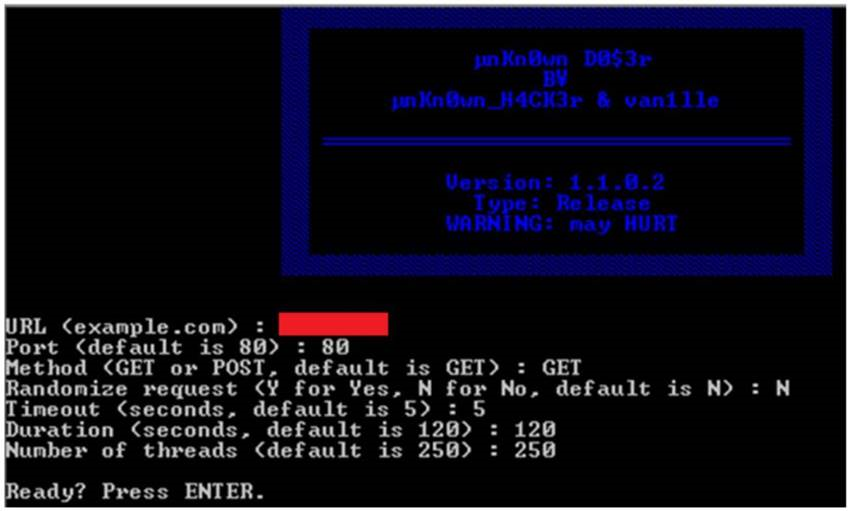
Figure 4: Screenshot of UnKnown DoSer, a Layer 7 flooder with request randomization capabilty
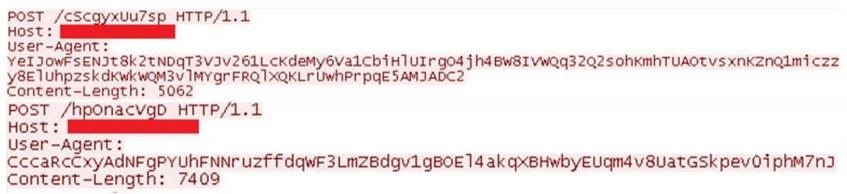
Figure 5: Screenshot of UnKnown DoSer attack traffic, demonstrating fields randomization
Can’t Get Enough of LOIC
Tools based on Low Orbit Ion Cannon (LOIC), an open source network stress testing and DOS attack application written in C#, are prominent in this bundle: LOIC, JavaLOIC, LOIC-IFC, LOIC-SD and NewLOIC. LOIC was notoriously known as the main attack delivery tool used in several Anonymous operations such as Operation Payback, Project Chanology, and more. Being JAVA based, JavaLOIC is a cross-platform tool with a built-in proxy feature that enables an attacker to hide his or her own IP address.
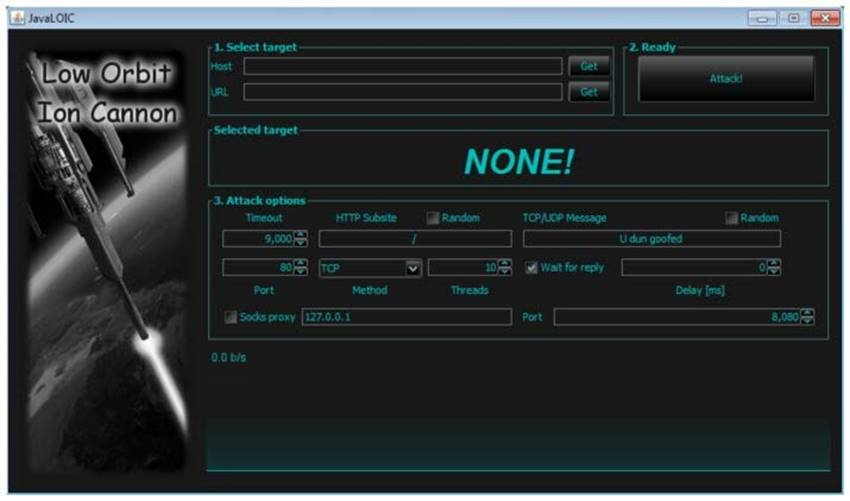
Figure 6: Screenshot of LOIC attack tool
Some Anonymous sub-groups localize and re-brand the LOIC tool. For example, LOIC-SD was first published by a Brazilian hacker group called Script Defenders and is mainly designed to overcome a language barrier by translating LOIC's user interface into Portuguese.
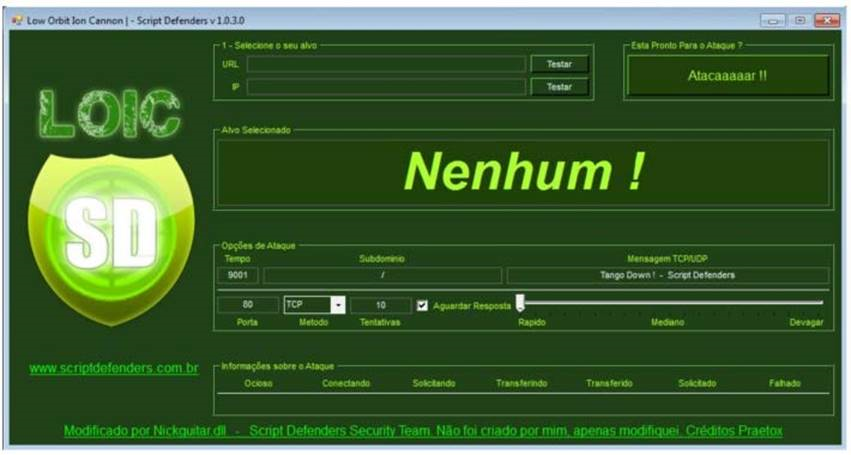
Figure 7: Script Defenders’ variant of LOIC
The Indonesia Fighter Cyber hacking group created LOIC-IFC. It differs only in the default TCP/UDP flood message saying, "Merdeka atau Mati" which means "Freedom or Death" in Malay. From a technical perspective, it provides additional ability to append random characters to the attacked URL in case of HTTP flood, and to the packet payload in case of TCP/UDP.

Figure 8: Indonesia Fighter Cyber’s variant of LOIC
Another LOIC-modified tool included in this bundle is NewLOIC, which, despite its name, offers no new functionality, only a new GUI design.
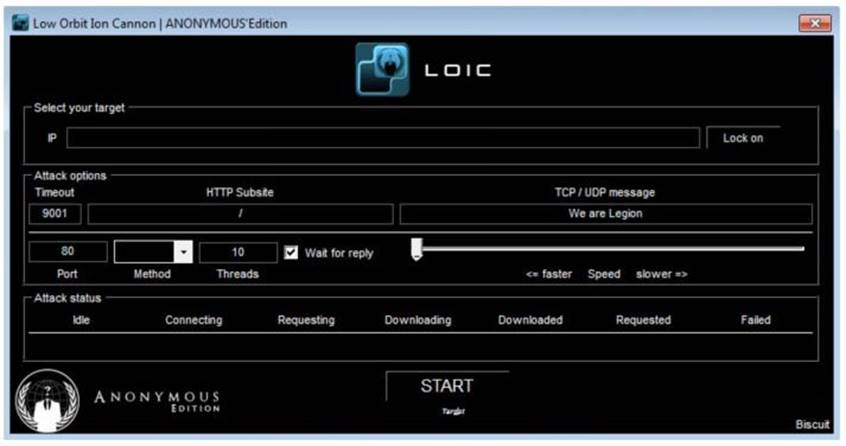
Figure 9: NewLOIC offers no new functionality, only a new GUI
Anonymous still considers LOIC and its various versions to be meaningful tools in its DDoS arsenal. In fact, a quarter of the tools included in this bundle are LOIC-based tools, despite the risk they pose to the attacker of exposing his or her IP address.
DDoS Tools Features Comparison
The following table compares various aspects of all 20 tools in the bundle.

Figure 10: Tool comparison
What’s Missing
Some of the DDoS tools known to be used by Anonymous aren’t included in the published bundle. R.U.D.Y, keep-dead.php, TORsHammer, THC-SSL-DOS, #Refref, and AnonStress are just some of the known tools that don't appear here. Attack tools that use proxies to protect the identity of their users also seem to be missing in this bundle, which makes potential Anonymous new recruits vulnerable to detection and prosecution.
Even so, Anonymous continues to strengthen its presence. By regularly publishing a variety of simple-to-use tools, the group makes DDoS attacks more accessible and easy to perpetrate, with the obvious goal of recruiting more users to support its hacktivist operations. Although not a single tool in the bundle is new, the group continues to terrorize the world with every successful DDoS operation.


