In previous blogs, we’ve debated the pros and cons of cryptocurrency, but like it or not, they’re a real part of our economy now. That means they’re part of our illicit economy, too. F5 Labs has been tracking crypto-mining malware that hijacks a computer’s resources in order to create cryptocurrency, but there’s a more obvious threat to anyone holding cryptocurrency like Bitcoin or Ethereum. Cryptocurrency can be straight-up stolen from our computers, just like payment card numbers or credentials.
This summer, we released our first annual Application Protection Report which, among other things, took a deep look at data breaches across the US. In 2017, we examined a decade of the most severe breaches. Now seemed like an appropriate time for us to look closely at cryptocurrency breaches.
As the title of this piece implies, we’re closing in on a billion dollars’ worth of cryptocurrency stolen in 2018—and the year isn’t even over yet. It’s pretty simple math, starting with the top five: CoinCheck at $520 million,1 followed by BitGrail at $195 million,2 then Zaif for $60 million,3 and CoinRail at $40 million,4 and finally Bancor for $23.5 million.5 That totals $838.5 million dollars. And those are just the major incidents this year. It’s completely believable that we could hit a billion dollars in the next month or two.
One of the biggest problems with cryptocurrency is that it’s not as heavily regulated as the traditional financial industry. Therefore, we don’t see as many mandatory stringent technical and administrative protection measures in place. Security is lax, and there are more fly-by-night operators.6 Worst of all, it is very difficult to reverse cryptocurrency transactions. If you get ripped off, there not much you can do to undo the fraud, and there’s no deposit insurance to make you whole. Some cryptocurrency exchanges have covered the loss for some customers. However, once the losses reach the tens of millions, exchanges often close their doors and you’re left holding an empty (virtual) bag.
Seven Years of Cryptocurrency Thefts
We looked through the last seven years of major cryptocurrency thefts for this analysis, which totaled 73 cases.7 At the beginning of these incidents (2011), Bitcoin had parity with the US dollar, with a single coin averaging about a buck. Today that same coin is worth over $6,000. Do we see a six-thousand-fold growth in crypto theft? Well, as Figure 1 shows, it’s actually closer to double that at a nearly twelve-thousand-fold increase.
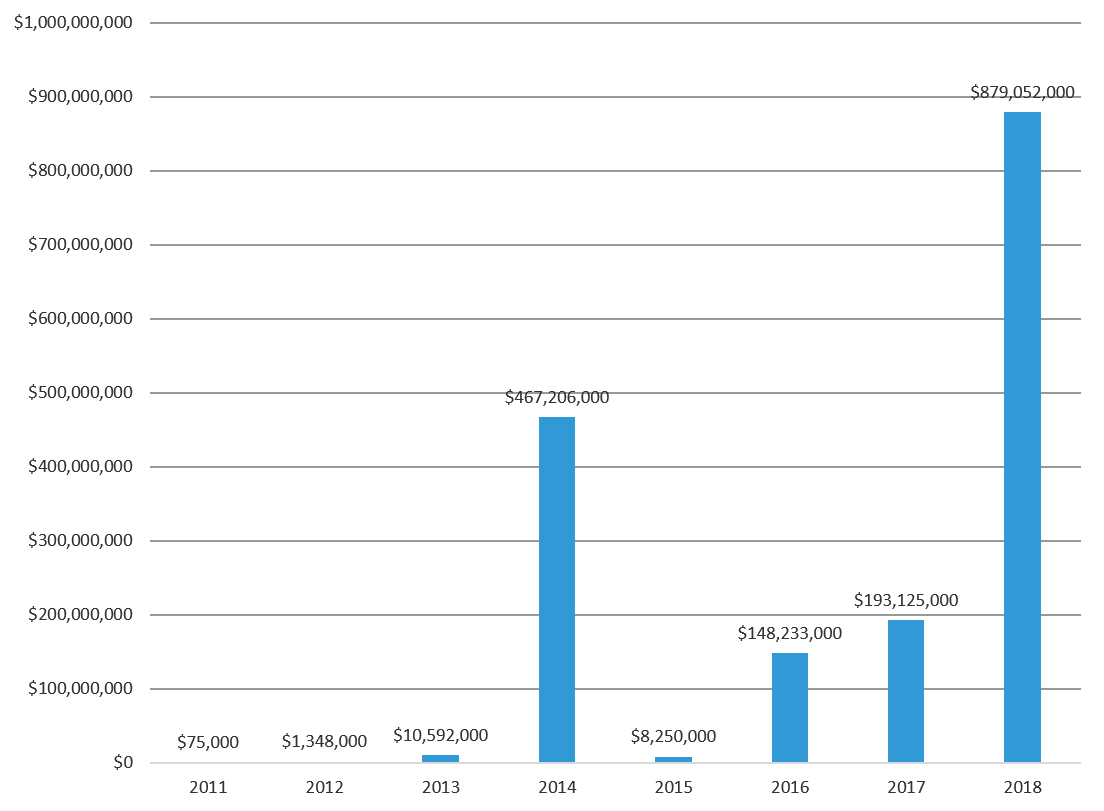
Figure 1: Dollars lost to cryptocurrency thefts over the last seven years
Over the past seven years of cryptocurrency data thefts, we found the average take on an incident was around $31 million. Figure 2 shows the pure number of cryptocurrency theft incidents.
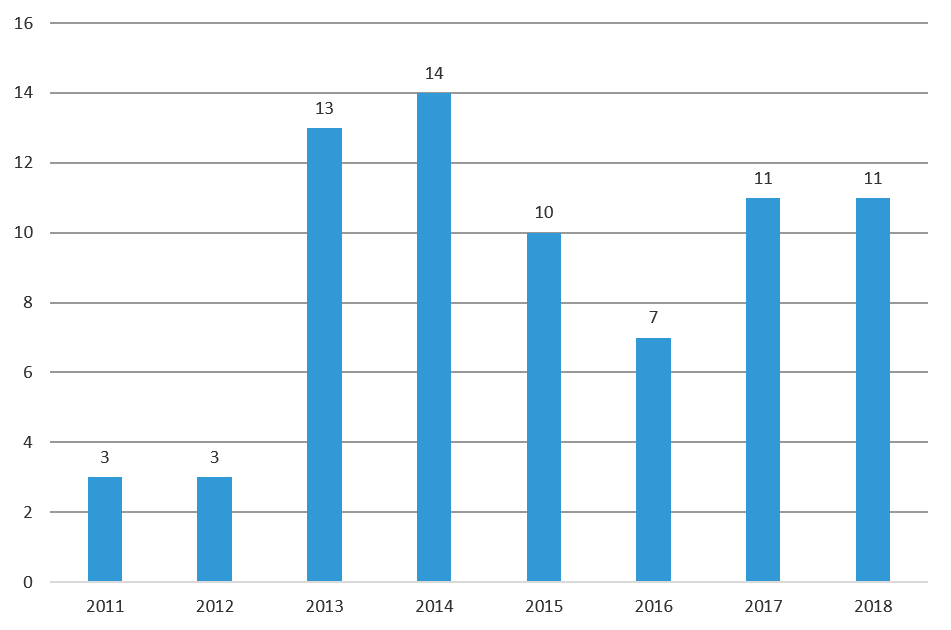
Figure 2: Cryptocurrency incidents over the past seven years
Overall, the dollar losses are mounting, but the number of incidents has stayed pretty much the same, averaging 9 per year. During the uptick that occurred around 2013, the average jumped from three incidents per annum in previous years to 11 afterwards. What happened in 2013? Well, it was the Year of Bitcoin,8 per Forbes Magazine, denoting the serious financial investment being put towards cryptocurrencies. It seems to have piqued criminal attention, as well.
What is Going Wrong?
Like most security professionals, we at F5 Labs are most interested in how the attackers are getting in so we can design the appropriate defenses. We read through all these cases and, where we could, we attributed the incidents to an inciting cause, as shown in Figure 3.
| Cause | % incidents |
| Unknown | 43.84% |
| Application vulnerability | 26.03% |
| Access credential theft | 8.22% |
| Phishing | 6.85% |
| Hacked box | 4.11% |
| Insider | 4.11% |
| DNS hijack | 2.74% |
| Third party | 2.74% |
| Accident | 1.37% |
Figure 3: Causes of cryptocurrency theft by incidence percentage
It’s worthwhile to compare these statistics to general data breaches, as we did in the 2018 Application Protection Report. In comparing the incident numbers, the first thing that jumped out to us was the high rate of insiders. For cryptocurrency thefts, the incidence rate is more than double, at 4.1% versus the average of 2%. That much highly liquid value sitting around is a tempting target for thieves, inside and out of an organization. That’s why traditional financial institutions worldwide have strict personnel management practices such as background checks, separation of duties, and system change auditing.
We also see double the amount of undisclosed causes, which is a known problem in the cryptocurrency industry. Some cryptocurrency thefts have been attributed to exchange owners faking a hack and taking off with the money.9
We also saw a significantly higher number of DNS hijacking attacks. They do happen to traditional banks,10 but they are relatively rare in comparison to other types of attacks. In the cryptocurrency world, DNS attacks seem to be a larger problem.
One statistic that didn’t vary was breaches attributed to web application vulnerabilities. Web apps are complicated and provide an easy way to get to the goods. We’ll dive deeper into that in the next section.
Lastly, access credential theft and phishing actually saw lower numbers than traditional cyber-crime. This could be due to the stronger reliance on multi-factor authentication in the smaller and newer cryptocurrency industry. A smaller, newly formed organization focused on technology would be able to roll out multi-factor authentication a lot faster than a venerable, large bank.
If you look at the causes by dollar loss, as shown in Figure 4, you’ll see the proportions don’t shift much.
| Cause | Loss ($M) |
| Unknown | $1,266.87 |
| Application vulnerability | $304.71 |
| Hacked box | $67.69 |
| Phishing | $47.43 |
| Insider | $13.00 |
| Access credential theft | $7.50 |
| DNS hijack | $0.41 |
| Third party | 0.23 |
Figure 4: Causes of cryptocurrency theft by dollar loss
Who is Getting Hacked?
There are many different technological services in the cryptocurrency industry, all of which are targets for cyber-criminals. The most commonly hit technical services are cryptocurrency exchanges (63% of incidents). These exchanges are the digital equivalent of currency exchanges, except instead of exchanging dollars for euros or yuan, they are for exchanging cryptocurrency, like selling Bitcoin to buy Ethereum. Customers come to exchanges to buy or sell their various currencies, which makes these sites a nexus of high value transactions.
Cryptocurrency uses storage mechanisms called wallets, and there are two kinds. A “hot wallet” is Internet-connected and is used to store the cryptocurrency you would use for day-to-day transactions. Think of a hot wallet like the real-world wallet in your pocket or purse holding the cash for your morning latte. Hot wallets can run on cryptocurrency exchanges for easy trading, but they also can run as client software on your computer or mobile device. Because of this, hot wallets are more likely stolen (pickpocketed?) by cyber-criminals. To reduce the risk, cryptocurrency technology also leverages “cold wallets” that, as you can guess, are not connected online. The best cold wallets are air-gapped systems, such as a USB stick with a strong password. Within cryptocurrency exchanges, cold wallets exist as separate, strongly-encrypted databases requiring a wallet owner to unlock it with a private key.
This distinction is significant because the wallets running on cryptocurrency exchanges are the primary target for attackers. Both hot wallets and cold wallets have been hit. As shown in Figure 5, of the known attacked technologies, hot wallets within exchanges are ripped off three times as much as cold wallets.
| Technology | Incidents |
| Hot Wallet | 20 |
| Cold Wallet | 6 |
| Authentication | 2 |
| Both Hot & Cold Wallet | 1 |
| Shopping cart | 1 |
| Webservers | 1 |
Figure 5: Attacked technology within exchange thefts
Wallet software for clients that is outside of an exchange can also be attacked. Those represent about one seventh of the cryptocurrency thefts.
Another cryptocurrency technology is the mining service. Instead of using your own hardware to mine or forge coins, you rent someone else’s. There are a handful of incidents over the years where these mining services were hacked and the cryptocurrency stolen.
Figure 6 shows how the types of affected organizations broke down by incidents:
| Service hacked | Incidents |
| Exchanges | 63.0% |
| Wallets | 15.1% |
| Mining service | 4.1% |
| Miscellaneous | 17.8% |
Figure 6: Incidents involving different types of cryptocurrency services
Broken down into more detail, Figure 7 shows dollar loss totals:
| Type | Impact ($M) |
| Transaction services | $0.01 |
| Payment service provider | $1.80 |
| Online market | $2.60 |
| Cryptocurrency algorithm | $7.00 |
| Platforms | $7.70 |
| Wallets | $7.99 |
| Ethereum clients | $20.25 |
| Mining Services | $60.00 |
| Management software | $91.70 |
| Exchanges | $1,508.83 |
Figure 7: Dollar loss involving different types of cryptocurrency services
No matter how you slice it, cryptocurrency exchanges are like banks with lots of easy-to-grab money flowing through, so that’s where criminals will strike first.
Where Are We Going?
At the end of the day, we need to remember that all of these things are applications running on the Internet. Applications are complex conglomerations of interacting services (/content/f5-labs-v2/en/labs/articles/cisotociso/apps-are-like-onions--they-have-layers.html) in a variety of environments glued together with APIs, authentication credentials, and networks. This means they have an extensive attack surface and therefore need extensive security testing and protection.
Governments around the world are now starting to regulate the cryptocurrency industry,11 and some have already begun defining cybersecurity measures. Korea Regulation 5.5.7 (Regulation on Supervision of Electronic Finance) is being looked at as one of the leaders12 in that it treats cryptocurrency exchange cybersecurity measures the way a financial institution would. Hopefully, we’ll start to see other governments follow South Korea’s lead so we can turn the tide on this skyrocketing trend. In the meantime, brace yourselves to see cryptocurrency theft break the billion-dollar mark by the end of 2018.


