F5 Labs, in conjunction with our partner Baffin Bay Networks, research global attack traffic region to region to gain a deeper understanding of the cyber threat landscape. Aside from attack campaigns targeting the entire Internet (IPv4 address space), the attack landscape varied regionally in terms of sources, targets, and attack types. In addition, targeted ports exposed regional differences in IT norms when it comes to the way non-standard ports are used for HTTP and SSH.
In this latest data collection, we looked at malicious traffic over the same 90-day period—August 1, 2019 through October 31, 2019—in the United States (U.S.), Canada, Australia, Europe, Russia, Asia, Latin America, and the Middle East. Australian systems were probed for vulnerabilities on the ports most commonly used by applications, but these attacks were outweighed by a global campaign targeting VNC port 5900.
- IP addresses assigned in Europe were the primary source of attacks targeting systems in Australia in the fall of 2019. Specifically, IP addresses assigned to OVH SAS in France launched the most malicious traffic to the region.
- The top five IP addresses launching attacks against systems in Australia were engaged in a global campaign targeting RFB/VNC port 5900 that began in June 2019. Because of this large global campaign, VNC port 5900 was the top targeted port in Australia during this period.
- The RFB/VNC port 5900 attacks brought a new threat actor network onto the scene: RM Engineering LLC out of Moldova.
- Attackers launched reconnaissance scans against Internet facing applications in Australia, looking for vulnerabilities in commonly used services (VNC, HTTP, HTTPS, SMB, RDP, MySQL). They also conducted credential stuffing attacks against SSH and Telnet remote access.
Top Source Traffic Countries
Before we look at the “top source traffic countries,” it’s important to clarify that we’re talking about the geographical source of IP addresses in this section. The “top source traffic” countries” does not mean that the country itself, individuals, or organizations based in that country were responsible for the malicious traffic. The attack traffic could be coming through a proxy server or compromised system or IoT device with IP addresses assigned in a particular country. For expediency, we refer to these as “top source traffic countries.”
IP addresses assigned to France launched the most malicious traffic against systems in Australia from August 1, 2019, through October 31, 2019. The top 10 source traffic countries during this period were:
- France
- Moldova
- Russia
- Italy
- Netherlands
- China
- United States
- South Korea
- Turkey
- Germany
All of the top 10, with the exception of Venezuela and Costa Rica, were also the top malicious source traffic countries globally. The top 5 source traffic countries, all within the European continent, is a threat profile only shared with Asia during this period. All other global regions had either the US, Canada or an Asian country in their top 5 source traffic countries list.
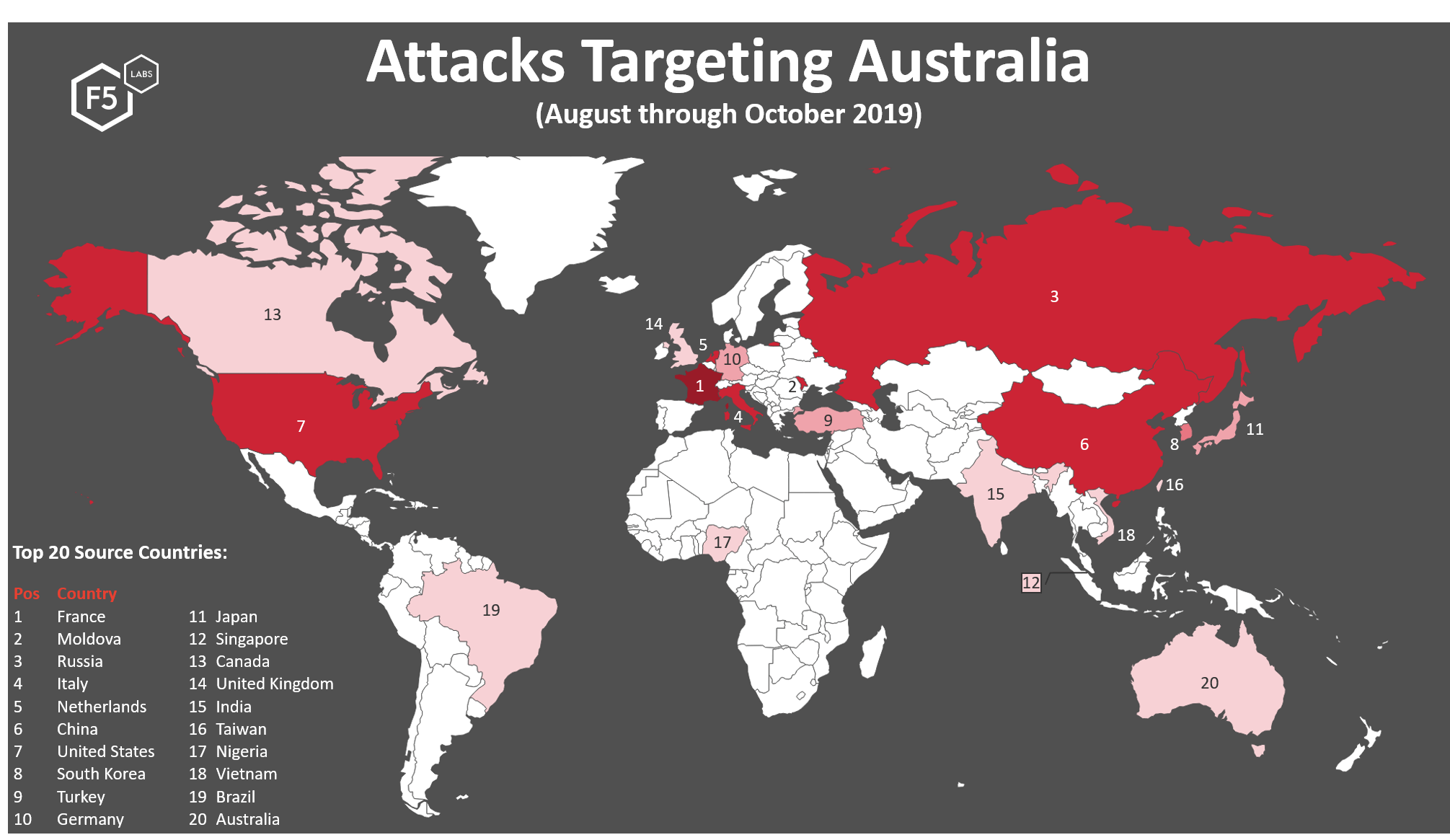
Figure 1. Top 20 source traffic countries launching attack traffic against targets in the Australia, August 1, 2019 through October 31, 2019
IP addresses assigned in France launched the most attack traffic against systems in Australia, followed by IP addresses assigned in Moldova, Russia, Italy and the Netherlands. Traffic from IP addresses assigned in these five countries account for over a half (55%) of malicious traffic seen targeting Australian systems during this time period. IP addresses assigned in Russia (in third position) followed the traffic seen from Moldovan and French IP addresses. Much of this traffic was seen participating in RFB/VNC port 5900 port scanning and credential stuffing (seen all over the world).
Australia received attack traffic originating from two countries that were not seen attacking other regions of the world. These countries were Nigeria, in the 17th position, and Australia itself in the 20th position. Attacks sourced from these countries accounted for 2.2% of all malicious traffic directed towards Australia during this period. This is notable since in other regions of the world (including the US and Europe) in region malicious traffic tops the list and poses a bigger threat. This kind of traffic can be more difficult for enterprises to filter since typically businesses want everyone in their country to be able to access them. Even though in country traffic accounts for a relatively small portion of all malicious traffic, there were two Australian IP addresses appearing in the top 50 attacking IP addresses in position 36, and position 43. These two IP addresses account for 57.66% of all malicious traffic originating from Australian IP addresses.
Australia is one of three regions of the world where Singapore appears in the top 20 source traffic countries. IP addresses assigned in Singapore focused on Asia, Australia, and Canada. There were no IP addresses assigned in Singapore appearing in the top attacking IP list. Notably, though, although not in the top 20 source traffic countries, systems in Australia received over 32,000 attacks from one IP in Romania. No other IP addresses in Romania show up in the top attacking IP address list, discussed later. This indicates that attacks coming from IP addresses in Romania and Singapore (and probably many other countries!) were more distributed; that is, they were launched from lots of IP addresses with low numbers of attacks per address. This type of activity is deliberate and takes more resources (systems and manpower) to pull off, and therefore is typically attributed to more sophisticated threat actors intentionally disguising their activities.
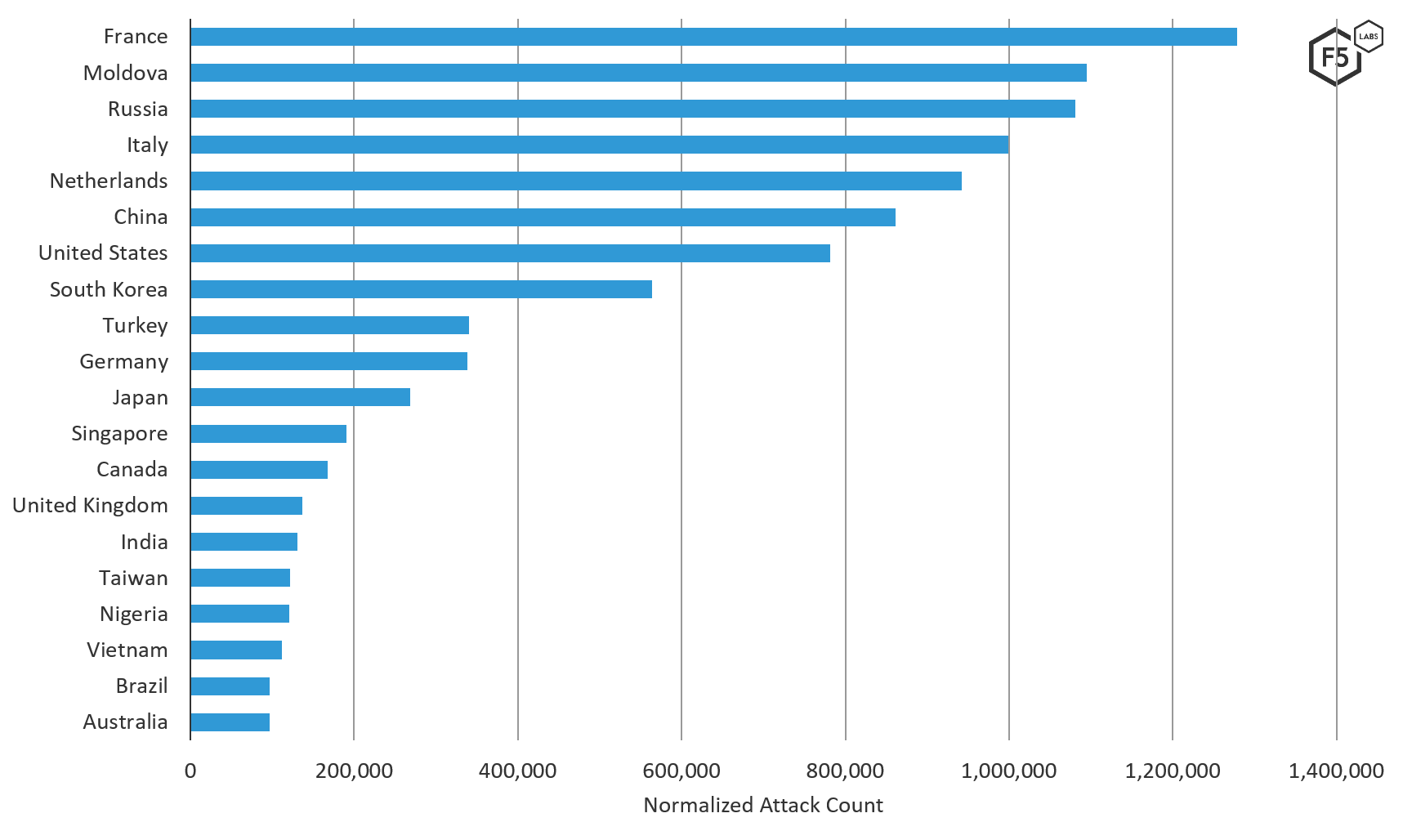
Figure 2. Top 20 source traffic countries (on a normalized scale) of attacks targeting systems in Australia, August through October 2019.
Top Attacking Organizations (ASNs)
Systems in OVH SAS, a hosting provider offering dedicated servers and cloud solutions across datacenters all over the world, were the largest source of attack traffic targeting Australian systems this fall. All regions of the world received attacks from systems in OVH SAS during this time period, as well as previous periods (see F5 Labs Regional Threat Perspectives). OVH SAS is consistently a top network source of attack traffic globally. OVH SAS was also the top source network of attacks towards Russian and Canadian systems, the number two network source of attacks against systems in Europe and Asia, and number three network source of attacks against systems in the U.S. during this time period. Although OVH SAS offers hosting services from locations all over the world, 90% of the attack traffic towards Australian systems came from hosts with IP addresses in France, the other 10% from OVH SAS hosts in Canada. The global view of attacks launched from OVH SAS during this time period was similar in that 78% of the attacks originated from hosts with French IP addresses, followed by 20% with Canadian IP addresses, and 1% with IP addresses in the U.K.
The second largest network source of attacks against systems in Australia was RM Engineering LLC, through only seven IP addresses in Moldova. RM Engineering’s ASN 49877, however, is registered in Russia. All seven IP addresses launched RFB/VNC port 5900 attacks and attacked systems all over the world. Prior to the global attack campaign targeting VNC port 5900, which started in June of 2019, RM Engineering was not a top attacking network globally.
The ASN in third position, GTECH S.p.a. from Italy, launched attacks against Australia as well as systems all over the world. These attacks were multi-port scans, typical reconnaissance activity looking for vulnerabilities, and were broadly distributed across lots of IP addresses. Only two IP addresses from GTECH showed up in the top attacking IP addresses list across all regions, and they only accounted for 10% of the total attacks launched from their network towards Australian systems during this time period. The other 90% of attacks launched from the GTECH network were distributed across many IP addresses with smaller accounts of attacks per IP address, which is intentional behavior by threat actors attempting to fly under the radar.
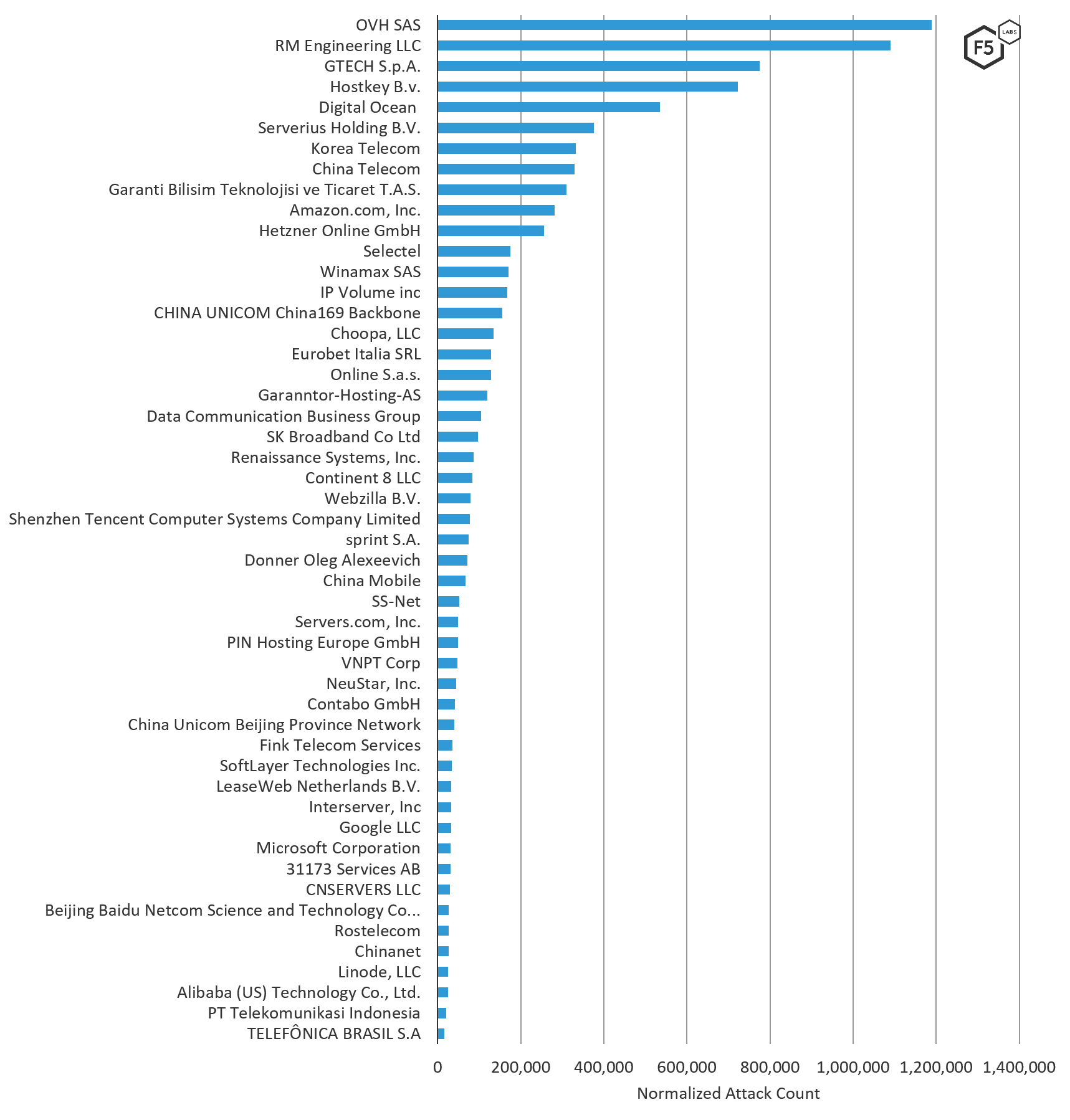
Figure 3. Source ASNs of attacks targeting systems in Australia, August through October 2019
The following table lists ASNs and their associated organizations (note that some ASNs have multiple ASNs).
| ASN Organization | ASN Number | Normalized Attack Count |
| OVH SAS | 16276 | 1,189,059 |
| RM Engineering | 49877 | 1,090,089 |
| GTECH S.p.A. | 35574 | 775,680 |
| Hostkey B.v. | 57043 | 723,013 |
| Digital Ocean | 14061 | 535,575 |
| Serverius Holding B.V. | 50673 | 375,715 |
| Korea Telecom | 4766 | 333,138 |
| China Telecom | 4134 | 329,883 |
| Garanti Bilisim Teknolojisi ve Ticaret T.A.S. | 12903 | 310,630 |
| Amazon.com | 16509 | 281,743 |
| Hetzner Online GmbH | 24940 | 256,659 |
| Selectel | 49505 | 174,205 |
| Winamax SAS | 197014 | 170,285 |
| IP Volume | 202425 | 167,712 |
| China Unicom | 4837 | 155,865 |
| Choopa, LLC | 20473 | 133,682 |
| Eurobet Italia SRL | 200944 | 128,738 |
| Online S.a.s. | 12876 | 128,451 |
| Garanntor-Hosting-AS | 328110 | 119,761 |
| Data Communication Business Group | 3462 | 104,532 |
| SK Broadband Co Ltd | 9318 | 97,053 |
| Renaissance Systems, Inc. | 16897 | 86,423 |
| Continent 8 LLC | 14537 | 83,087 |
| Webzilla B.V. | 35415 | 78,142 |
| Shenzhen Tencent Computer Systems Co Ltd | 45090 | 77,206 |
| Sprint S.A. | 197226 | 73,816 |
| Donner Oleg Alexeevich | 35606 | 71,949 |
| China Mobile | 9808 | 67,435 |
| SS-Net | 204428 | 51,415 |
| Servers.com, Inc. | 7979 | 49,282 |
| PIN Hosting Europe GmbH | 39556 | 49,120 |
| VNPT Corp | 45899 | 47,443 |
| NeuStar, Inc. | 19905 | 44,850 |
| Contabo GmbH | 51167 | 41,231 |
| China Unicom | 4808 | 39,982 |
| Fink Telecom Services | 6775 | 34,737 |
| SoftLayer Technologies Inc. | 36351 | 33,136 |
| LeaseWeb Netherlands B.V. | 60781 | 32,922 |
| Interserver, Inc | 19318 | 32,633 |
| Google LLC | 15169 | 32,373 |
| Microsoft Corporation | 8075 | 30,799 |
| Elite Services, 31173 | 39351 | 30,625 |
| CNSERVERS LLC | 40065 | 28,804 |
| Beijing Baidu Netcom Science and Technology Co... | 38365 | 26,726 |
| Rostelecom | 12389 | 25,994 |
| Chinanet | 23650 | 25,759 |
| Linode, LLC | 63949 | 24,700 |
| Alibaba (US) Technology Co., Ltd. | 45102 | 24,436 |
| PT Telekomunikasi Indonesia | 7713 | 20,747 |
| TELEFÔNICA BRASIL S.A | 27699 | 15,510 |
Table 1. ASNs and their associated organizations (some have multiple ASNs)
ASNs Attacking Australia Compared to Other Regions
We looked at the count of attacks by ASN towards systems in Australia and compared that to other regions of the world. The key difference between attack traffic launched from networks targeting Australia versus the rest of the world was that the top networks targeting Australia launched significantly more attacks against systems in the U.S., Canada, Europe, Middle East and Asia. Six ASNs exclusively targeted systems in Australia (see ASNs denoted with *** in Figure 4). These include ASNs located in China (China Mobile, China Unicom and Beijing Baidu Netcom Science and Technology Co), Switzerland (Fink Telecom), Sweden (Elite Services, 31173), and the U.S. (Interserver).
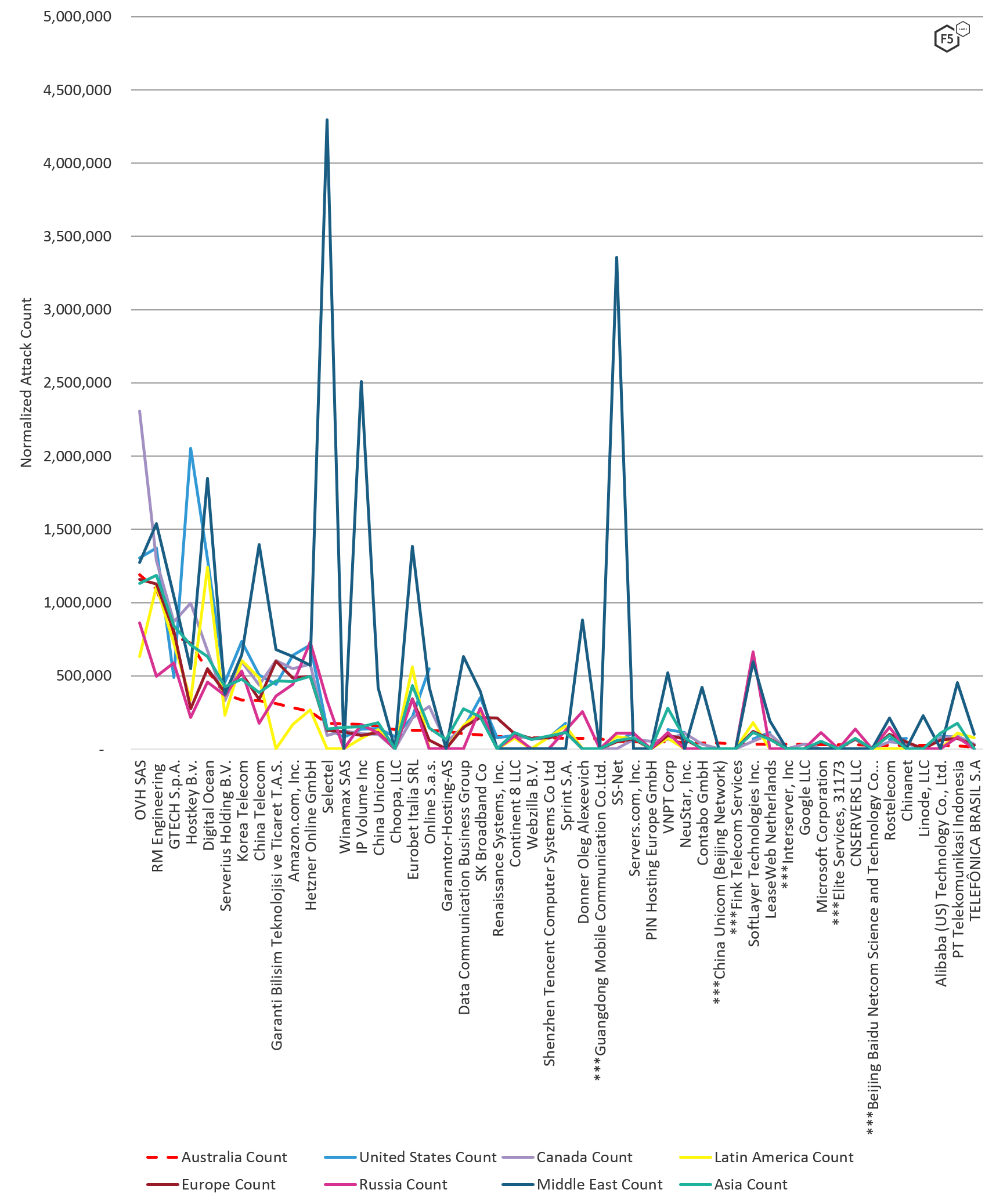
Figure 4: Normalized attack count by ASN by region, August through October 2019
Top Attacking IP Addresses
The top ten IP addresses attacking systems in Australia from August 1, 2019 through October 31, 2019 were all engaged in abusive port scanning followed by RFB/VNC port 5900 credential stuffing attacks. These attacks can from IP addresses in the networks of OVH SAS (France), RM Engineering (Moldova), Hostkey B.v. (Russia), and Serverius Holding B.v (Netherlands). Forty-eight percent of the IP addresses on the top 50 attacking IP addresses list were engaging in the same RFB/VNC port 5900 scanning and credential stuffing attacks.1 These port 5900 attacks were new activity we noticed earlier in the summer and continued through October 31, 2019. We have opened up a public threat hunting investigation on Twitter to uncover what is going on with these attacks and will be looking to share our findings and ask questions soon. For now, join the conversation on Twitter.
For a complete list of attacks by IP address, see section Attacks Types of Top Attacking IP Addresses below.
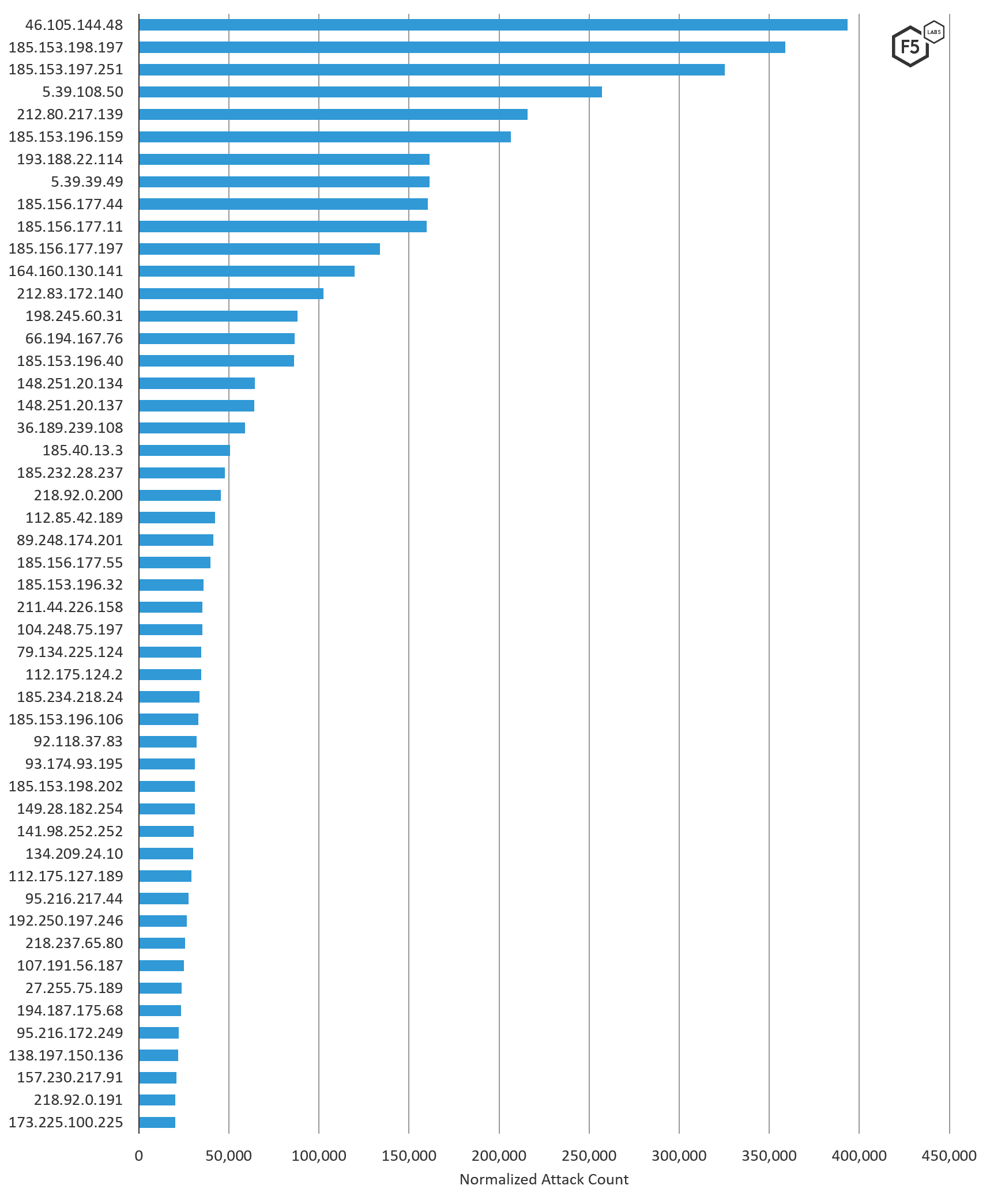
Figure 5. Top 50 IP addresses attacking Australian targets, August through October 2019.
IP Addresses Attacking Australia Compared to Other Regions
We compared the volume of attack traffic systems in Australia received per IP address to other regions of the world. The top 10 source IP addresses of attacks against Australian systems where the most overlap occurs (see Figure 6) were engaged in global attacks against RFB/VNC port 5900 (see the next section). Twenty-eight percent of the top attacking IP addresses sending malicious traffic to Australia were exclusively targeting the Australian region (see IP addresses denoted with *** in Figure 6).
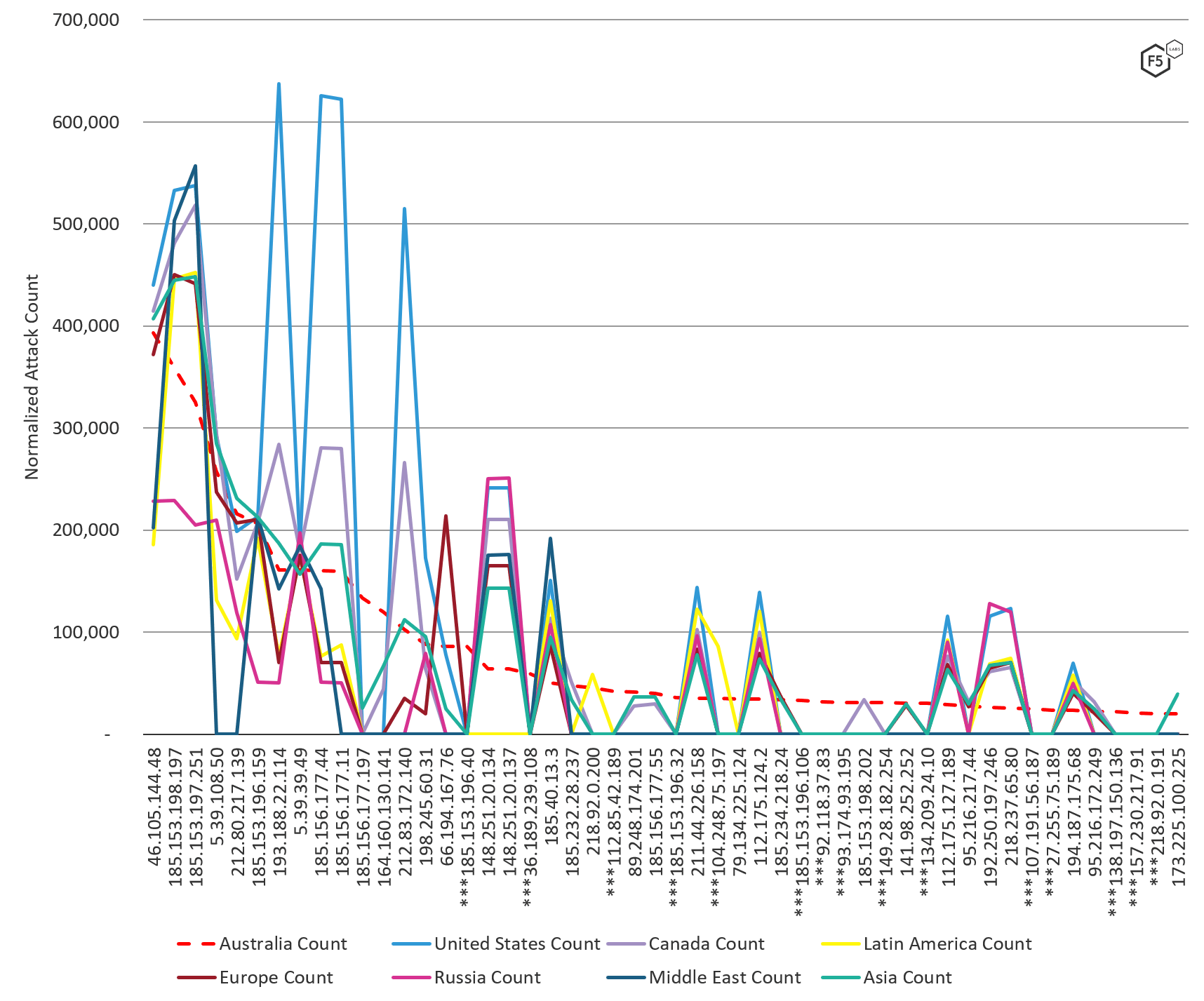
Figure 6: Normalized attack count by IP by region, August through October 2019
Attacks Types of Top Attacking IP Addresses
Outside of the global RFB/VNC port 5900 attacks (48% of top 50 IP addresses), a lot of general reconnaissance and vulnerability probing occurred against systems in Australia in the fall of 2019. Forty-two percent of the top 50 IP addresses on the top attacking list launch generic reconnaissance scans looking for vulnerabilities by probing multiple, if not all 65,000 ports. These IP addresses were from all over the world (10 countries), inside 13 different ASNs. Eight IP addresses were engaged in targeting SSH port 22 with credential stuffing attacks, behavior that’s typical of IoT bot building or targeting vendor default SSH credentials. The remaining IP addresses were scanning for systems with the Microsoft RDP port 3389 open, HTTP port 80 and HTTPS port 443, MySQL port 3306 and SMTP email port 25. When scanning for SMTP email port 25, we also saw credential stuffing on POP3 port 110, and spamming from port 25.
The following table is in descending order starting with top attacking IP addresses and includes the attack types each IP address launched.
| Source IP | Normalized Attack Count | Attack Type |
| 46.105.144.48 | 393,400.4 | Port Scanning: RFB/VNC port 5900 Credential Stuffing: RFB/VNC port 5900 |
| 185.153.198.197 | 359,027.0 | Port Scanning: 29 unique ports Credential Stuffing: RFB/VNC port 5900 |
| 185.153.197.251 | 325,416.7 | Port Scanning: 36 unique ports Credential Stuffing: RFB/VNC port 5900 |
| 5.39.108.50 | 257,020.8 | Port Scanning: RFB/VNC port 5900 Credential Stuffing: RFB/VNC port 5900 |
| 212.80.217.139 | 215,865.7 | Port Scanning: 6 unique ports Credential Stuffing: RFB/VNC port 5900 |
| 185.153.196.159 | 206,620.0 | Port Scanning: 23 unique ports Credential Stuffing: RFB/VNC port 5900 |
| 193.188.22.114 | 161,258.8 | Port Scanning: RFB/VNC port 5900 Credential Stuffing: SSH port 22, RFB/VNC port 5900 |
| 5.39.39.49 | 161,253.0 | Port Scanning: RFB/VNC port 5900 Credential Stuffing: RFB/VNC port 5900 |
| 185.156.177.44 | 160,319.6 | Port Scanning: RFB/VNC port 5900 Credential Stuffing: RFB/VNC port 5900 |
| 185.156.177.11 | 159,949.8 | Port Scanning: RFB/VNC port 5900 Credential Stuffing: RFB/VNC port 5900 |
| 185.156.177.197 | 133,845.9 | Port Scanning: 43 unique ports Credential Stuffing: RFB/VNC port 5900, SSH port 22 |
| 164.160.130.141 | 119,760.9 | Port Scanning: RDP port 3389, and port 33899 |
| 212.83.172.140 | 102,388.8 | Port Scanning: RFB/VNC port 5900 Credential Stuffing: RFB/VNC port 5900 |
| 198.245.60.31 | 88,096.9 | Port Scanning: RFB/VNC port 5900 Credential Stuffing: RFB/VNC port 5900 |
| 66.194.167.76 | 86,422.6 | Port Scanning: RFB/VNC port 5900 |
| 185.153.196.40 | 86,068.9 | Port Scanning: 18 unique ports |
| 148.251.20.134 | 64,368.2 | Port Scanning: SMTP port 25, HTTPS port 443, SSH port 22, HTTP port 80 |
| 148.251.20.137 | 64,237.7 | Port Scanning: HTTPS port 443, SMTP port 25, HTTP port 80, SSH port 22 |
| 36.189.239.108 | 59,082.4 | Port Scanning: 14995 unique ports |
| 185.40.13.3 | 50,495.5 | Port Scanning: 51 unique ports |
| 185.232.28.237 | 47,635.0 | Port Scanning: 11 unique ports |
| 218.92.0.200 | 45,382.3 | Port Scanning: SSH port 22 Credential Stuffing: SSH port 22 |
| 112.85.42.189 | 42,419.4 | Port Scanning: SSH port 22 Credential Stuffing: SSH port 22 |
| 89.248.174.201 | 41,438.2 | Port Scanning: 64502 unique ports |
| 185.156.177.55 | 39,905.6 | Port Scanning: 111 unique ports Credential Stuffing: RFB/VNC port 5900 |
| 185.153.196.32 | 35,940.5 | Port Scanning: 11 unique ports |
| 211.44.226.158 | 35,442.5 | Port Scanning: 48 unique ports |
| 104.248.75.197 | 35,334.9 | Port Scanning: RFB/VNC port 5900 |
| 79.134.225.124 | 34,725.6 | Port Scanning: 30 unique ports Credential Stuffing: RFB/VNC port 5900 |
| 112.175.124.2 | 34,567.9 | Port Scanning: 61 unique ports |
| 185.234.218.24 | 33,674.4 | Port Scanning: port 3389, RFB/VNC port 5900, port 3396 Credential Stuffing: RFB/VNC port 5900 |
| 185.153.196.106 | 32,943.7 | Port Scanning: RFB/VNC port 5900, RDP port 3389 |
| 92.118.37.83 | 32,084.4 | Port Scanning: 21935 unique ports |
| 93.174.93.195 | 31,144.2 | Port Scanning: 32973 unique ports |
| 185.153.198.202 | 31,029.5 | Port Scanning: 9 unique ports |
| 149.28.182.254 | 30,974.7 | Port Scanning: ports 47720 & 22001 |
| 141.98.252.252 | 30,611.9 | Port Scanning: MySQL port 3306 |
| 134.209.24.10 | 30,310.7 | Port Scanning: RFB/VNC port 5900 |
| 112.175.127.189 | 29,283.3 | Port Scanning: 48 unique ports |
| 95.216.217.44 | 27,686.2 | Port Scanning: RFB/VNC port 5900 Credential Stuffing: RFB/VNC port 5900 |
| 192.250.197.246 | 26,505.8 | Port Scanning: 20 unique ports Credential Stuffing: SSH port 22 |
| 218.237.65.80 | 25,537.2 | Port Scanning: HTTP port 80, SSH port 22, HTTPS port 443, DNS port 53 |
| 107.191.56.187 | 24,894.6 | Port Scanning: ports 22001 & 47720 |
| 27.255.75.189 | 23,680.1 | Port Scanning: SMTP port 25 Credential Stuffing: POP3 port 110 Spam: SMTP port 25 |
| 194.187.175.68 | 23,361.7 | Port Scanning: 45 unique ports |
| 95.216.172.249 | 22,166.1 | Port Scanning: RFB/VNC port 5900 Credential Stuffing: RFB/VNC port 5900 |
| 138.197.150.136 | 21,966.2 | Port Scanning: RFB/VNC port 5900 |
| 157.230.217.91 | 20,804.5 | Port Scanning: RFB/VNC port 5900 |
| 218.92.0.191 | 20,164.2 | Port Scanning: SSH port 22 Credential Stuffing: SSH port 22 |
| 173.225.100.225 | 20,119.0 | Port Scanning: SMTP port 25 |
Top Targeted Ports
It’s not surprising that RFB/VNC port 5900, what was attacked all over the world during this time period, was the number one attacked port in Australia by a large margin. This activity is not typical, hence the investigative threat hunting we are doing on Twitter mentioned previously.
In a distant second was SSH port 22, followed by HTTP ports 80 and 443, and Telnet port 23 rounding out the top 5 attacked ports. Given the port probing and credential stuffing attacks seen, it is clear attackers were targeting applications (over VNC, HTTP, HTTPS, SMB, RDP), remote administration of applications over SSH and Telnet, and email over SMTP in Australia.
One port was uniquely targeted in Australia during this time period: port 47720.
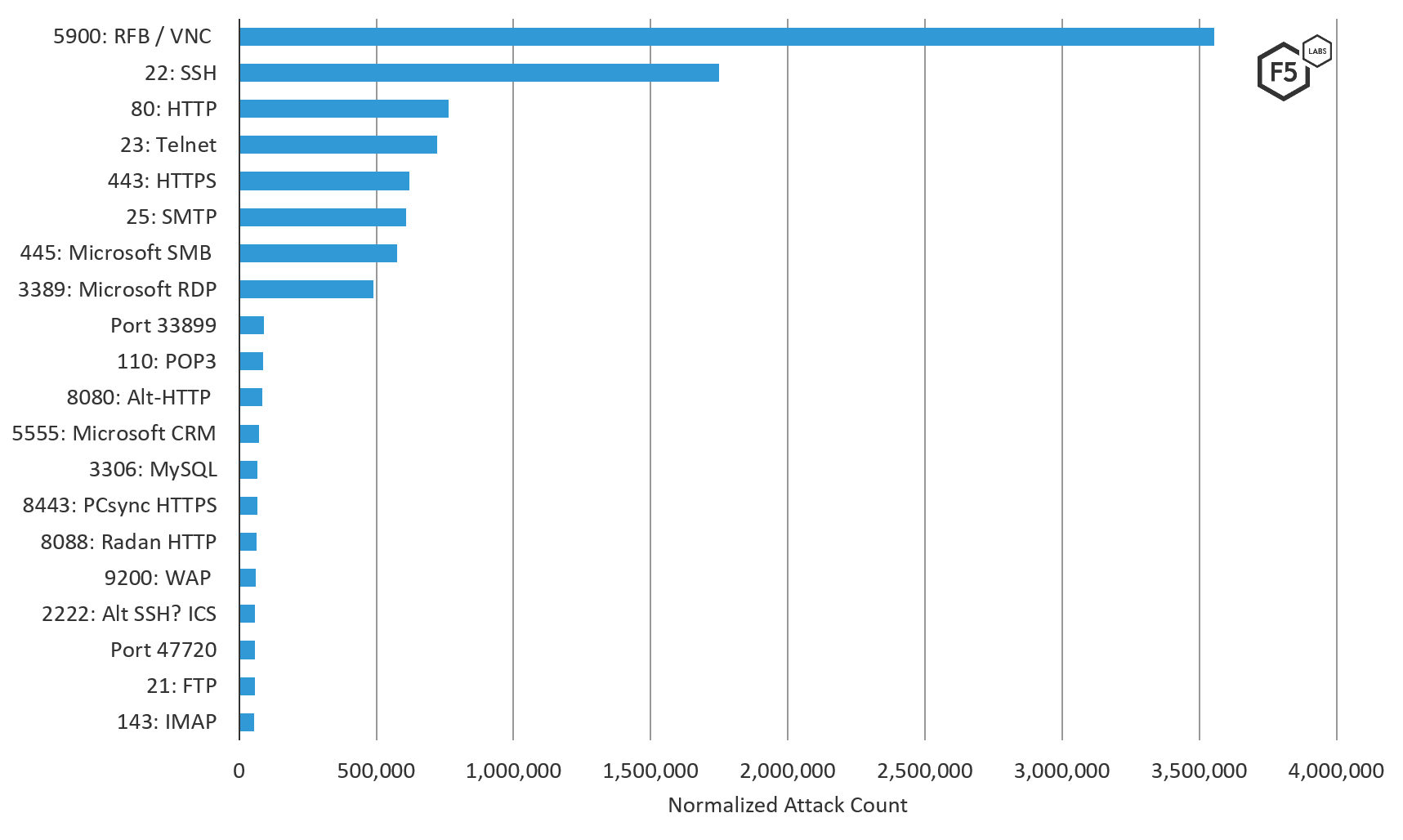
Figure 7. Top 20 ports attacked in Australia, August through October 2019
Conclusion
In general, the best approach a security team can take as defenders in this modern threat landscape is one of “assume breach.” This is not a FUD (fear, uncertainty, and doubt) position, this is a realistic position backed up by the volume of attack traffic all systems touching the Internet receive, the likelihood of vulnerabilities existing, and the amount of compromised credentials available to attackers. When you take an “assume breach” defensive position, you are collecting attack traffic and monitoring your logs. You can use this high-level attack data to compare against the attack traffic directly hitting your own network. This will help you rule out run-of-the-mill attack traffic, or help you determine whether or not you are being targeted, in which case, investigating the attack sources and patterns is a worthwhile activity.
Additionally, you should lock down as soon as possible any of the top targeted ports that do not absolutely require unfettered Internet access. And because default vendor credentials are commonly left in place, and the volume of breached credentials in 2017 was so large that many usernames and passwords are now considered “public,” all organizations should have credential stuffing protection in place. Particularly for any system with remote authentication, and especially administrative remote access. See F5 Labs report Lessons Learned from a Decade of Data Breaches for more data on these breached passwords.
Security Controls
To mitigate the types of attacks discussed here, we recommend the following security controls be put in place:
Recommendations
- Use firewalls to restrict all unnecessary access to commonly attacked ports that must be exposed publicly.
- Never expose internal databases publicly, and restrict access to internal data on a need-to-know basis.
- Prioritize risk mitigation for commonly attacked ports that require external access (like HTTP and SSH) for vulnerability management.
- Use SSH vs Telnet for secure remote access and protect against brute force attacks.
- Implement MFA on applications with remote administration.
- Disable all vendor default credentials (commonly used in SSH and Telnet brute force attacks) on all systems before deploying them publicly.
- Implement geo IP address blocking of commonly attacking countries that your organization does not need to communicate with.


