Last week, F5 threat researchers spotted a Monero (XMR) crypto-mining campaign that was taking advantage of a user configuration vulnerability in the rTorrent client, specifically misconfigured XML-RPC functionality. This misconfiguration vulnerability in rTorrent allows an unauthenticated user to execute methods in the rTorrent client using HTTP requests.
After deeper analysis of the attack logs, F5 threat researchers discovered another campaign targeting the same rTorrent configuration error, this time to disguise threat actors’ activities with user-agents that appear to be legitimate.
- The campaign (running in January) appears to have spoofed the Recording Industry Association of America (RIAA) and New York University (NYU) user-agents.
- F5 researchers do not believe either of these user-agents are legitimately from RIAA or NYU because of the origin of returning IP addresses and other attacks seen from those addresses as well.
- The sending server for the RIAA user-agent is a proxy server in the Netherlands set up with the hosting company Hostkey B.V. Activity from the same IP address includes scans of ports commonly used by Torrent software, and scans for Intel AMT ports.
- The sending servers for the NYU user-agent resolve to various hosting companies around the world from which malicious activity has been seen previously, including SSH brute force scans.
Why the RIAA?
Better known as the Recording Industry Association of America, the RIAA (among other things) helps members protect copyrighted works from piracy. It’s also widely known that BitTorrent is a file sharing protocol that is primarily used to illegally share software, movies, music, and other protected works—the very same materials RIAA exists to protect. In 2001, the RIAA tried to fight piracy of copyrighted works by filing lawsuits against offenders.1 It even drafted an amendment to proposed legislation (the USA Act of 20012) that would have allowed the RIAA to hack distributors’ computers to delete stolen content from their file systems and indemnified them from any responsibility for damage caused to distributors’ computers.3
We reference this historical proposed legislation (which, by the way, was never signed into law) because the RIAA user-agent “RIAALABS” appears in the configuration snapshot of the January campaign, shown in Figure 1.
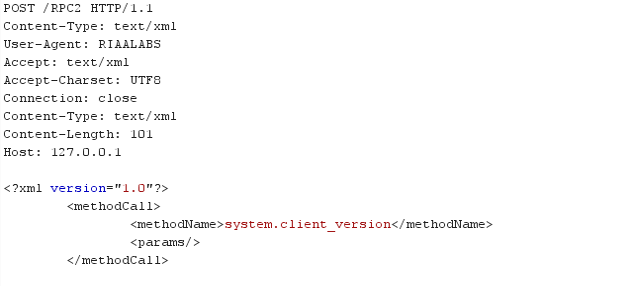
Figure 1: RIAA Labs user agent
Figure 1: RIAA Labs user agent
The HTTP POST request targets rTorrent’s XML-RPC interface and tries to invoke a “system.client_version” method on the frequently used path “/RPC2”. Upon successful execution of this method, it returns the rTorrent version number as shown in Figure 2.
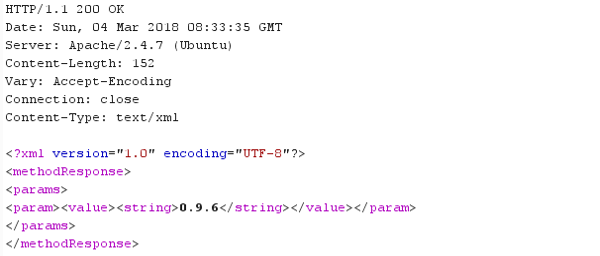
Figure 2: Campaign collects torrent client version
Figure 2: Campaign collects torrent client version
New York University?
The NYU campaign was spotted just one day after the RIAA campaign. As with the RIAA campaign, we cannot be sure who is behind this campaign. NYU started a Torrent tracking project in 2015, so this spoofed user-agent could be trying to disguise itself as that project.4 Again, this campaign tries to query the XML-RPC interface to get the Torrent client version, as shown in Figure 3.
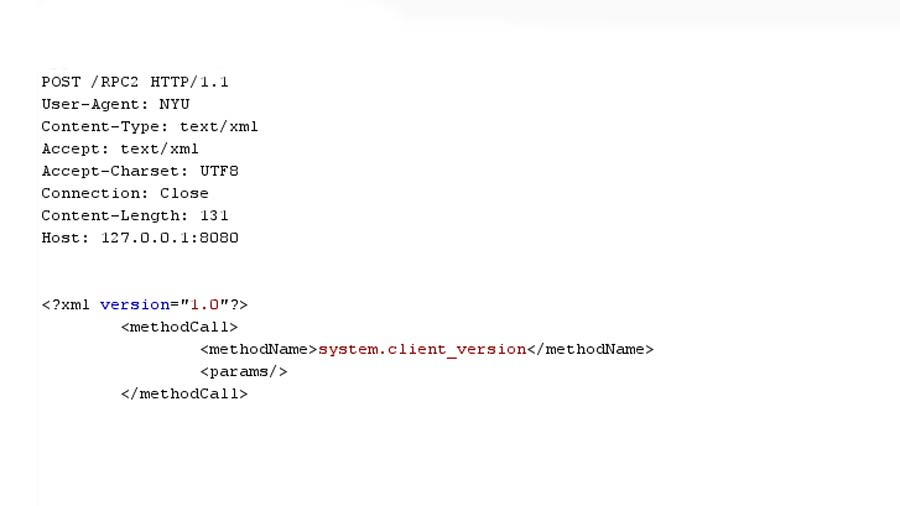
Figure 3: NYU user-agent
Figure 3: NYU user-agent
Origins of these Campaigns
There is no obvious connection between the source of these two campaigns except the timeframe. The RIAA campaign originates from a single IP address: 5.39.223.136. The NYU campaign uses three different IP addresses: 185.130.104.198, 62.210.152.47, and 203.24.188.242. All of the IP addresses are owned by hosting companies.
| IP | Campaign | Owner | ASN | Country | Industry |
| 5.39.223.136 | RIAA | HOSTKEY B.V. | ASN57043 | Netherlands | Hosting |
| 185.130.104.198 | NYU | Hosting Solution Ltd. | ASN14576 | Russia | Hosting |
| 62.210.152.47 | NYU | ONLINE S.A.S. | ASN12876 | France | Hosting |
| 203.24.188.242 | NYU | Host Sailor Ltd | ASN60117 | China | Hosting |
RIAA Campaign
F5 and our data partner Loryka checked our systems to see if the originating IP address (5.39.223.136) for the RIAA campaign had shown up as malicious over the past five years. The first time we saw it engaging in malicious activity was June 1, 2017. Other scanning activity from this IP address includes destination ports 16992, likely looking for Intel AMT-vulnerable systems, and various TCP ports commonly used by torrent software (see torrent invite site5). Because of this additional malicious traffic, we do not believe this is the actual RIAA, rather a spoofed user agent.

Figure 4: RIAA campaign originating from 5.39.223.136
Figure 4: RIAA campaign originating from 5.39.223.136
NYU Campaign
All of the originating IP addresses for the NYU campaign (185.130.104.198, 62.210.152.47, and 203.24.188.242) are also launching SSH brute force attacks. Because of these additional attacks, we assume these are threat actors spoofing an NYU user agent.
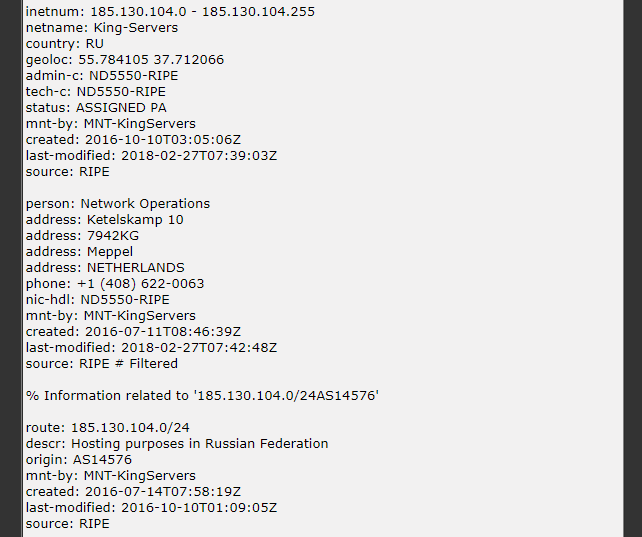
Figure 5: NYU originating IP address 185.130.104.198
Figure 5: NYU originating IP address 185.130.104.198
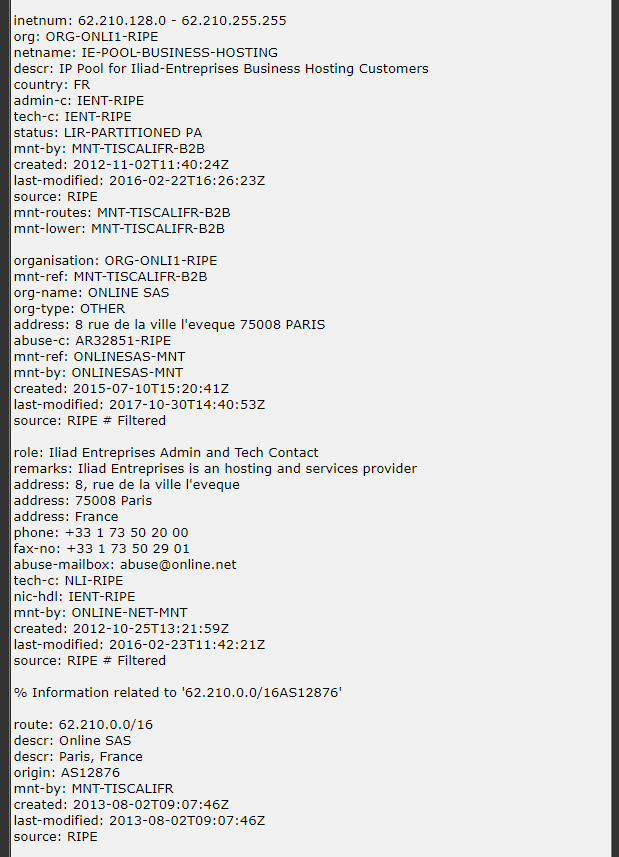
Figure 6: NYU originating IP address 62.210.152.47
Figure 6: NYU originating IP address 62.210.152.47
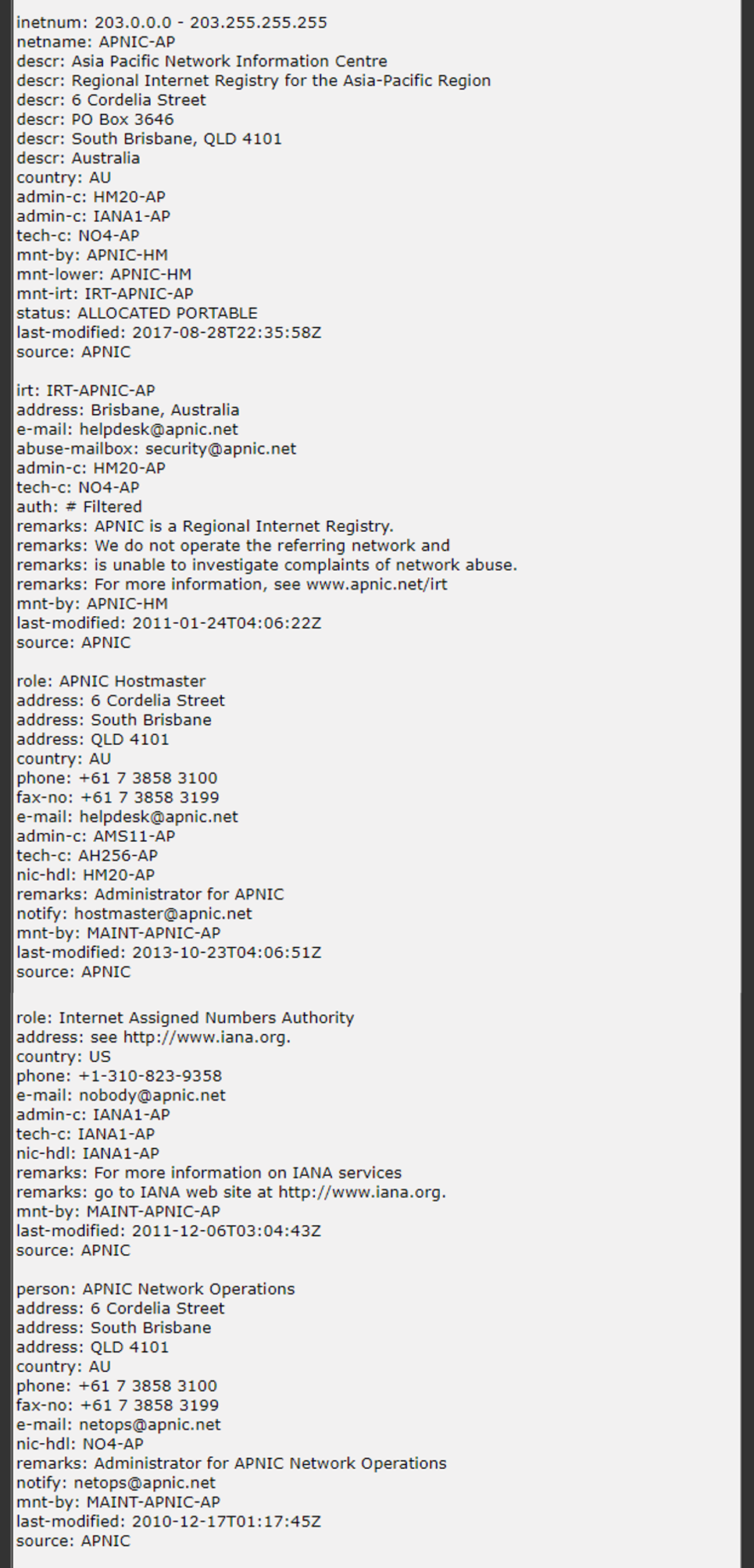
Figure 7. NYU originating IP address 203.24.188.242
Figure 7. NYU originating IP address 203.24.188.242
Summary
For now, it’s unclear what happens once a vulnerable host is found. The misconfiguration vulnerability enables attackers to invoke methods on a victim’s machine that can provide a great deal of information about the shared materials on the host (if, for example, the goal was to delete stolen, copyrighted material), or execute their own code and use the system to mine crypto-currency like we found in the February Monero campaign. Since rTorrent is the defacto standard for threat actors attacking seedboxes, which could be great crypto-miners, we are not surprised to see attacks leveraging this rTorrent misconfiguration vulnerability to compromise hosts.
Since the IP address related to the RIAA user-agent has been engaging in other malicious activity, it’s highly unlikely this is the work of the RIAA. Rather, a threat actor is pretending to be the RIAA as a deceptive tactic, or perhaps just for their own amusement. Because this campaign was seen at least a month before the Monero crypto-mining campaign, it could have been the inspiration for cyber-criminals.
Of course, it’s never okay to steal and share copyrighted works, but if you are using rTorrent for legitimate purposes, please see the misconfiguration remediation actions in our previous post: https://f5.com/labs/articles/threat-intelligence/malware/rtorrent-client-exploited-in-the-wild-to-deploy-monero-crypto-miner.


