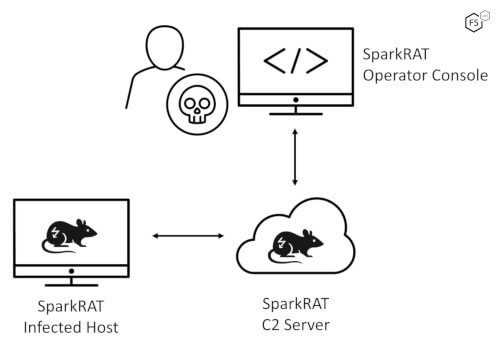
The F5 Security Incident Response Team (F5 SIRT) helps customers tackle security incidents in real time. As part of the 2021 Application Protection Report, earlier this year, we looked at the top reported security incidents to the F5 SIRT for the years 2018 through 2020. Now we’re taking a deeper dive into the reported security incidents at financial organizations, sometimes referred to as BFSI for banking, financial services, and insurance institutions.
A quick recap: in our March article, we noted that financial services organizations experienced the highest ratio of incidents attributed to password login attacks (46.2%) compared to all other sectors. They were third in the percentage of denial-of-service (DoS) incidents (36.1%). The last largest category was web-related attacks, at 6.3%. Figure 1 breaks down the categories of incidents at financial organizations.
A wide variety of organizations fall under financial services, including banks of varying sizes, credit unions, insurance companies, government-sponsored financial institutions, stock exchanges, investment funds, payment processors, consumer finance lenders, brokerages, and companies that service the financial sector. We’ll look at all of these and note the differences in the data, starting with the largest category, banks.
Cyberattack Incidents at Banks
Banks are the largest segment in the 2018-2020 financial services incident data, representing 40% of the records. Out of financial services organizations, banks saw more DoS attacks (41%), which is five points above the average of 36%. However, they also saw fewer password login attacks (41%), which was five points below the average of 46%. One possible reason for this is that banks have better antibot controls in place, which mitigate password login attacks, and thus see fewer attacks than the average financial organization. Web attacks make up 6% of the reported bank security incidents, which is on par with the average.
Of the password login attacks against banks, the majority of incidents were reported as brute force (77%), with the remainder (23%) reported as credential stuffing botnet attacks. The DoS attacks that could be classified were mostly web application, or layer 7, attacks (36%), followed by network volumetric attacks (24%) and DNS DoS (14%) attacks, with the rest uncategorized.
Cyberattack Incidents at Large and Small Banks
We had enough data to do a significant breakout by bank size, as shown in Figure 2. Using a bank asset size of USD $100 billion as a divider between large and small banks, we found that large banks reported more DoS attacks. Of all the incidents larger banks reported, 44% were DoS, while only 37% of incidents at smaller banks were noted as DoS. This is reversed for password login attacks, with smaller banks seeing a higher proportion (48%), while larger banks saw only 36%. Reported web attack incidents were nearly the same—large banks 6% and small banks 7%.
Cyberattack Incidents at Credit Unions
Some may think that credit unions are like small banks, but they are far different. For one, credit unions are owned by their customers, so they are far more focused on individual consumers than the average bank. This consumer focus shows up in the cyber-incident data as well, with 88% of incidents reported as password login attacks. This is nearly double the average and far higher than banks see. Credit unions provide a lot more customer services, which means more user-friendly logins that attackers are eager to exploit with credential stuffing and brute force attacks.
DoS attacks are also far below the average at credit unions, showing up as only 8% of reported incidents. It could be that credit unions are less of a target for DoS because they are perceived as having less money to pay ransom. Or perhaps they aren’t as unloved as banks or they’re simply not seen as a potential target. Credit unions also saw about half the average of web attacks, at 3%.
Cyberattack Incidents at Insurance Companies
Many don’t think of insurance companies as financial institutions, but they handle large amounts of money and confidential financial data. They also deal with fraud and have experienced some large cyberattacks as well as subsequent compliance investigations.1 Insurance companies reported higher-than-average DoS attacks (60%), but their password login attacks were below average, at 27%. They reported a little bit more than average for web attacks, at 7%.
Cyberattack Incidents for Government-Sponsored Financial Institutions
This category looks at large government- or public-sponsored financial organizations, usually established to promote borrowing by augmenting credit to particular industry sectors. Overall, their reported cyberincidents look pretty close to the average for password login attacks (32%). Their reports of DoS attacks are 8 points higher than average, at 44%. They saw an average number of web attacks (6%).
Cyberattack Incidents for Stock Exchanges
Over the years, stock exchanges have been the target of a few notable massive DoS attacks. Therefore, it should be no surprise that reported DoS attack incidents at stock exchanges clocked in at 80%, way above the average. Although there were no reported password login attack incidents, they did report more than three times the average in web attacks, at 20%.
Cyberattacks at Financial Institutions: The Big Picture
Figure 3 shows all of the F5 SIRT cyberattack incident data in a single graph. The average is present, so you can see what’s divergent and what’s not.
This is a lot of data, so we’re splitting it up into two articles. In part 2 of our analysis, we’ll cover the reported security incidents at other types of financial organizations. This will include data for investment funds, payment processors, consumer finance lenders, brokerages, and financial services companies. We’ll also look at how the move to open banking affects the security at these organizations. See you then!