TLS 1.3 network and security implications
With all these benefits, what could possibly be a problem? So glad you asked! With PFS, only the endpoints (the web user and the application server), can decrypt the traffic. However, it’s likely that you have one or more solutions—such as a next-generation firewall, an intrusion detection system (IDS), or a malware sandbox—designed to spot malicious traffic egressing your network. Alternatively, you might have a web application firewall, IDS, or an analytics solution in front of an application that you host. All these solutions sit between a user and the application or website they are connected to, so they are typically blind to the encrypted traffic.
Some security inspection tools do have the ability to decrypt; however, this often comes with performance hits to the tools and adds complexity to your network architecture. Also, blindly decrypting everything may introduce privacy regulation violations.
It's worth mentioning is that some security experts are up in arms over the 0-RTT feature, because of the potential for replay attacks. And without 0-RTT enabled within the TLS configuration, you may lose most of the performance boost that motivated you to implement in the first place.
Is it time to roll out TLS 1.3 for your web applications?
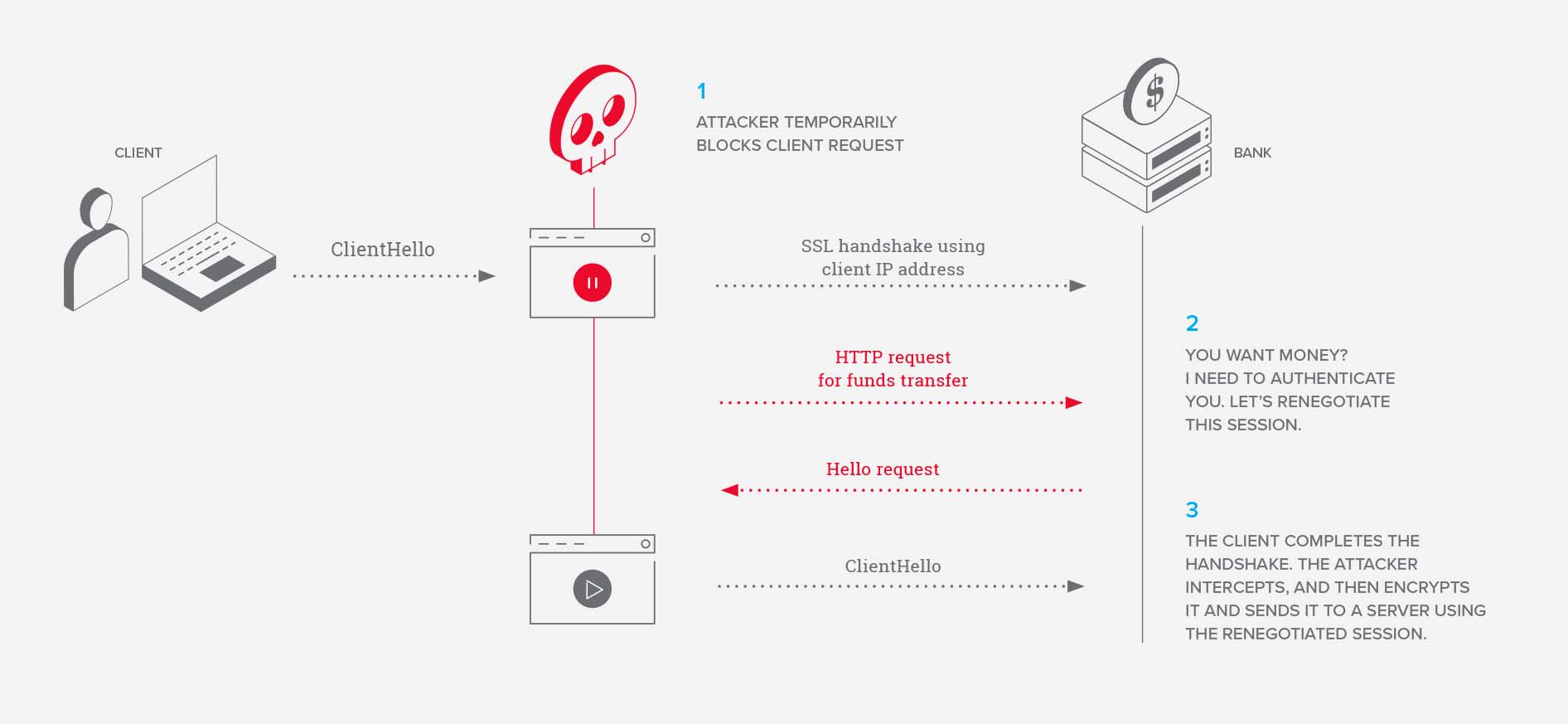
The decision to implement TLS 1.3 at this point will depend on your requirements and motivations. There are some browsers that do not support 1.3, which could result in a bad user experience. Additionally, if you take out potentially vulnerable features like renegotiation and use PFS for your applications’ TLS 1.2 configuration, you get all the same security and privacy benefits as TLS 1.3. As far as a potential performance boost, you should perform thorough testing to see if this is true for your application as it may not be worth the effort with 0-RTT disabled.
Whatever your decision, it doesn’t mean that previous versions of TLS are going away any time soon. Google has announced that they will deprecate TLS 1.0 and 1.1 by 2020, so TLS 1.2 will continue to be around for quite a while. And, with the exception of some point-to-point API connections, you will need to continue support for TLS 1.2 (and possibly 1.1) for some time to ensure you do not break users’ connections to your applications.