As organizations migrate and extend their applications to cloud-native infrastructures, they are introducing risk. According to F5’s State of Application Strategy Report, 88% of organizations continue to manage a mix of modern and legacy applications. The reality is that many enterprises have an application catalog that spans generations of architectures.To secure these legacy and modern apps across hybrid and multi-cloud environments, organizations constantly deploy and tune numerous security controls. Since applications are only as secure as the infrastructure on which they run, security needs to be extended across the entire architectural stack, from apps and APIs to the underlying cloud-native infrastructure.
Traditional security controls are not designed to protect dynamic and highly distributed architectures. Organizations lack the visibility and control to identify a variety of security threats that may surface from a single coordinated attack campaign. Businesses look to their cloud infrastructure providers to close the gap, but different cloud providers have varying responsibility models, security postures, and cloud-native tools. Furthermore, moving apps to the cloud does not remove risks and may not even reduce complexity. In reality, the risk surface for a heterogenous environment that spans the data center and multiple cloud providers will most likely expand as cloud-native infrastructure often lacks sufficient observability and security—creating significant blind spots and opportunities for attackers that can lead to downtime, outage, and security incidents due to inconsistent security postures.
As Businesses Innovate, So Do Attackers
Inevitably, vulnerability exploits will continue as bad actors innovate their attack arsenals and playbooks. The expansive threat surface cannot be completely mitigated with a single tool, even a web application firewall (WAF). Complex software supply chains, open-source software proliferation, and automation via CI/CD pipelines will introduce unforeseen risk, making early detection and remediation critical for effectively protecting web apps and APIs.
For example, the infamous log4j2 vulnerability can be exploited in a variety of ways, making remediation difficult, especially when potential exposure spans components across multiple clouds. In order to improve speed to remediation, indicators of vulnerability and integration between the front door (apps), windows (APIs), and foundation (infrastructure) of the digital house is required. Expanding web app and API protection (WAAP) to secure cloud-native infrastructure and workloads helps to contain threats by detecting vulnerable components and potentially malicious behavior in real time—delivering critical insights to security controls such as a WAF—where policy can be updated to protect critical application services. The log4j2 vulnerability serves as a warning to security leaders about the risk of untenable complexity and the devastating exploits yet to come, but it is also an opportunity for organizations to revisit their security postures and employ a comprehensive security strategy that includes robust infrastructure protection.
Securing Your Entire Digital Fabric
Successfully operating and securing applications as they are modernized requires comprehensive observability across the entire architecture, which is increasingly decentralized and distributed, for a comprehensive view of threats at both the application level and infrastructure level.
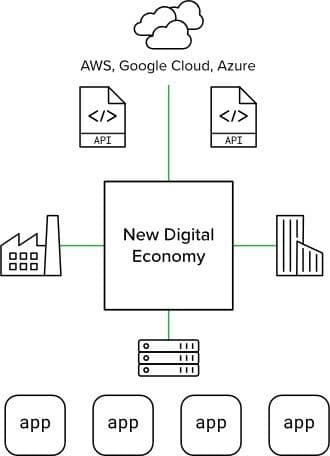
As organizations embrace toolsets from different cloud providers and build out multi-cloud architectures for redundancy, observability will manifest as a critical challenge that jeopardizes governance efforts to maintain a consistent security posture. Cloud security models vary, and inconsistency introduces risk by increasing the threat surface—something attackers know and exploit.
F5 ensures comprehensive defense of all the architectural components apps and APIs depend on, providing resilience and agility so organizations can modernize their apps and embrace the efficiencies of cloud-native infrastructure while proactively protecting the critical services that underpin their business in the new digital economy.
Securing the Entire Digital House
We recently introduced F5 Distributed Cloud App Infrastructure Protection (AIP), a cloud workload protection service that delivers comprehensive telemetry and high-efficacy intrusion detection for cloud-native workloads, running on the F5 Distributed Cloud (F5 XC) Platform to improve detection and remediation of increasingly complex attack campaigns. F5 XC AIP combines telemetry, rules, and machine learning to detect threats in real time across the entire infrastructure stack.
A comprehensive solution that secures apps, APIs, and underlying infrastructure has several benefits:
- Increased Visibility – Multi-cloud observability through deep telemetry analysis from cloud workloads wherever they are deployed.
- Effective Detection – Real-time protection with retrospective analysis across billions of data points collected daily, with context and workflows that help speed remediation.
- Automated Protection – Streamlined insights-to-policy protection loop that neutralizes threats wherever they start and however they spread.
- Ecosystem Integration – Interoperability with existingsecurity tools, SIEMs, and cloud provider platforms to share actionable insights and rich context.
F5 is excited to deliver app infrastructure protection to our customers to help them continue modernizing their applications while effectively managing risk. When combined with WAAP, customers have a detection-in-depth approach that helps remediate security threats to applications, APIs, and the cloud-native infrastructure on which they run.
To learn more, go to: www.f5.com/solutions/protect-app-infrastructure
About the Author
Related Blog Posts

F5 joins the Dell AI Ecosystem Program to help enterprises operationalize AI
F5 joins the Dell AI Ecosystem Program to help enterprises deploy production AI with greater performance, security, and control.

Why sub-optimal application delivery architecture costs more than you think
Discover the hidden performance, security, and operational costs of sub‑optimal application delivery—and how modern architectures address them.

Keyfactor + F5: Integrating digital trust in the F5 platform
By integrating digital trust solutions into F5 ADSP, Keyfactor and F5 redefine how organizations protect and deliver digital services at enterprise scale.

Architecting for AI: Secure, scalable, multicloud
Operationalize AI-era multicloud with F5 and Equinix. Explore scalable solutions for secure data flows, uniform policies, and governance across dynamic cloud environments.

AppViewX + F5: Automating and orchestrating app delivery
As an F5 ADSP Select partner, AppViewX works with F5 to deliver a centralized orchestration solution to manage app services across distributed environments.
F5 NGINX Gateway Fabric is a certified solution for Red Hat OpenShift
F5 collaborates with Red Hat to deliver a solution that combines the high-performance app delivery of F5 NGINX with Red Hat OpenShift’s enterprise Kubernetes capabilities.