The rise of business applications delivered “as a Service” can be great for cost savings and operational efficiency. After all, who really wants to spend hours and hours implementing a new HR or CRM system on hardware that you will have to manage and maintain? Who wants to work over the weekend to perform yet another upgrade to an aging messaging platform which, if it fails, will stop the business dead in its tracks? And who wants to pay upfront for value that will take years to be delivered? SaaS applications let you outsource the provisioning of some of the more mundane, highly operationalized software so that the business—and IT in particular—can get on with more productive tasks.
However, SaaS apps can also add complexity if you are a user who has to remember yet another password. Or what if you are responsible for adding more steps to your onboarding and exit procedures? And it’s probably a little uncomfortable if you’re in charge of security and you notice an increasing number of colleagues retrieving credentials from under their keyboards.
As a business, while you want the benefits of SaaS applications, you need your users to keep working efficiently—and securely. It’s vital to maintain control of user identity and keep it close to you, because the data in these SaaS systems might be routine, but it can also be highly sensitive. The consequences of the theft of that data could range from a mild inconvenience to Very Bad News™ if it leaves you failing compliance audits or in breach of regulations.
Since SaaS applications take data security seriously, the weakest link is likely to be your users and their password security. Helping them follow best practices by reducing the number of identities and passwords they have to remember is a crucial step you can take to keep your data secure.
Fortunately, most SaaS offerings now allow you to federate your corporate identity into their system. Using the Security Assertion Markup Language (SAML) standard, SaaS providers can seamlessly redirect users to an identity service (known as a SAML IdP) where a user authenticates and returns with a valid token (a SAML assertion). This technology allows you to retain complete control of user identity—even when it’s being used in a third-party SaaS application.
The SAML IdP can also allow you to go beyond simple username and password authentication. Since it is in control of returning a valid assertion, it is the ideal place to add in stricter controls such as two-factor authentication or one-time passwords. It’s even better if you can insert some context-aware intelligence wherein stricter controls can be added based on context such as user location, device type, time of day, etc.
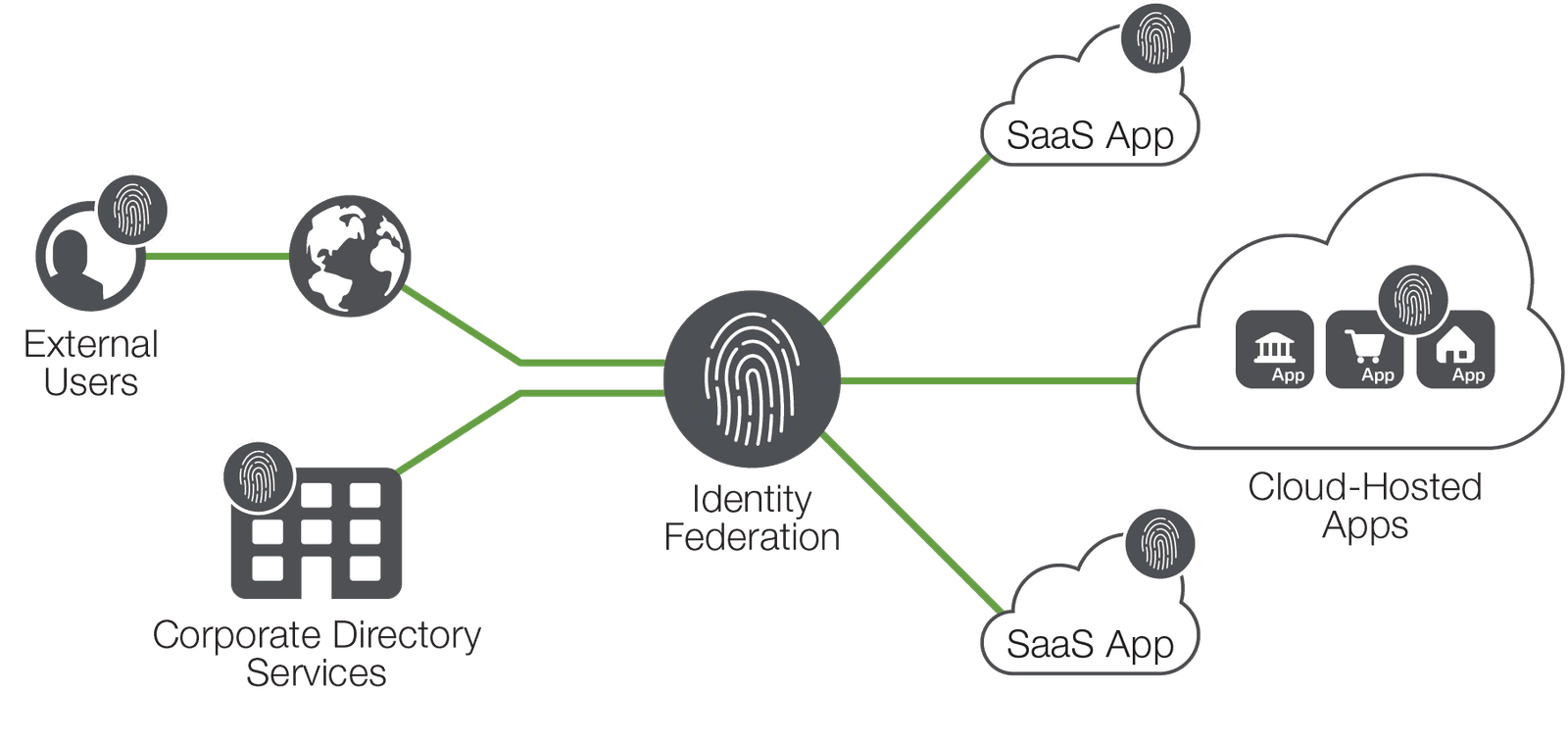
Federating identity into SaaS applications helps you maintain better control and encourages good password hygiene. Using an intelligent SAML IdP will give you more flexible access control of your outsourced business applications. With the right solutions in place, SaaS applications can deliver on the promise of greater agility and productivity, while not compromising critical security and identity management processes.
About the Author

Related Blog Posts

Build a quantum-safe backbone for AI with F5 and NetApp
By deploying F5 and NetApp solutions, enterprises can meet the demands of AI workloads, while preparing for a quantum future.
F5 ADSP Partner Program streamlines adoption of F5 platform
The new F5 ADSP Partner Program creates a dynamic ecosystem that drives growth and success for our partners and customers.

Accelerate Kubernetes and AI workloads with F5 BIG-IP and AWS EKS
The F5 BIG-IP Next for Kubernetes software will soon be available in AWS Marketplace to accelerate managed Kubernetes performance on AWS EKS.
F5 NGINX Gateway Fabric is a certified solution for Red Hat OpenShift
F5 collaborates with Red Hat to deliver a solution that combines the high-performance app delivery of F5 NGINX with Red Hat OpenShift’s enterprise Kubernetes capabilities.
F5 Silverline Mitigates Record-Breaking DDoS Attacks
Malicious attacks are increasing in scale and complexity, threatening to overwhelm and breach the internal resources of businesses globally. Often, these attacks combine high-volume traffic with stealthy, low-and-slow, application-targeted attack techniques, powered by either automated botnets or human-driven tools.
Phishing Attacks Soar 220% During COVID-19 Peak as Cybercriminal Opportunism Intensifies
David Warburton, author of the F5 Labs 2020 Phishing and Fraud Report, describes how fraudsters are adapting to the pandemic and maps out the trends ahead in this video, with summary comments.
