Infográfico OWASP Top 10 2021
Os 10 principais da OWASP:
Uma nova onda de risco
INTRODUÇÃO
As oportunidades para invasores explodiram na economia digital de hoje, que depende de aplicativos e arquiteturas modernas, implantações multi-nuvem e integrações de terceiros, incluindo cadeias de suprimentos de software e pipelines de CI/CD. O OWASP Top 10 para 2021 aborda uma nova onda de riscos como orientação de leitura obrigatória para melhorar a segurança no design e na implementação de aplicativos.
A atualização mais significativa em 20 anos
O OWASP Top 10, lançado pela primeira vez em 2003, representa um amplo consenso sobre os riscos de segurança mais críticos para aplicativos da web. Por 20 anos, os principais riscos permaneceram praticamente inalterados, mas a atualização de 2021 faz mudanças significativas que abordam os riscos de aplicativos em três áreas temáticas:
Recategorização do risco para alinhar os sintomas às causas raiz
Novas categorias de risco abrangendo arquiteturas e desenvolvimento de aplicativos modernos
Explorações de vulnerabilidades, bem como abuso de lógica de negócios
Qual é a principal causa de violações?
Ataques de acesso
“Ataques de acesso, ou seja, ataques contra superfícies de autenticação voltadas para o usuário, foram a causa mais frequente de violações.”1
— Relatório de Proteção de Aplicativos de 2022: Na expectativa de exfiltração
O que há de novo para 2021
Aqui estão os principais fatores que influenciaram a atualização do OWASP Top 10:
2017
Foco em aplicações web tradicionais
Pequeno conjunto de dados (subconjunto prescrito de 30 CWEs)
Variedade de fatores de risco, impactos técnicos/empresariais
Injeção como o maior risco por mais de 20 anos
2021
Mudança para arquiteturas modernas
Processo baseado em dados com 400 CWEs
Recategorizado em torno de sintomas e causas raiz
Uma nova onda de risco: design e implementação inseguros
Os 10 principais riscos de segurança da OWASP de 2021
A01
Controle de acesso desfeito
A02
Falhas Criptográficas
A03
Injeção
A04
Design Inseguro
A05
Configuração incorreta de segurança
A6
Componentes Vulneráveis e Desatualizados
A7
Falhas de identificação e autenticação
A8
Falhas de software e integridade de dados
A9
Falhas de monitoramento e registro de segurança
A10
Server-Side Request Forgery (SSRF)
TEMA #1
Sintomas alinhados às causas raiz

O que mudou?
Os 10 principais riscos do OWASP são mapeados para enumerações de fraquezas comuns (CWEs), que frequentemente se tornam explorações de vulnerabilidades. Mas a coleta de dados anterior do OWASP se concentrou em um conjunto prescrito de 30 CWEs, e as listas anteriores não faziam distinção significativa entre CWEs que representavam causas raiz e fraquezas mais sintomáticas com uma variedade de causas potenciais. A lista de 2021 reflete 400 CWEs e, portanto, permitiu uma análise mais ampla.
2017: Sintoma
A3:2017
Exposição de dados sensíveis
A7:2017
Script entre sites (XSS)
A4:2017
Entidades externas XML (XXE)
A9:2017
Usando componentes com vulnerabilidades conhecidas
A8:2017
Desserialização Insegura
A10:2017
Registro e monitoramento insuficientes
2021: Causa raiz
A02:2021
Falhas Criptográficas
A03:2021
Injeção
A05:2021
Configuração incorreta de segurança
A06:2021
Componentes Vulneráveis e Desatualizados
A08:2021
Falhas de software e integridade de dados
A09:2021
Falhas de monitoramento e registro de segurança
POR QUE ISSO É IMPORTANTE?
A lista de 2021 alinha melhor os sintomas às causas raiz subjacentes para ajudar as equipes de segurança a se concentrarem na redução dos riscos na origem.
Qual é a principal causa de violações de dados na nuvem?
Configuração incorreta de segurança
“O que queremos que você faça é realmente pensar sobre essas causas raiz e o que você pode fazer sobre elas, em vez de tentar colocar curativos nos sintomas.”2
—Andrew van der Stock, Diretor Executivo, Fundação OWASP
TEMA #2
Novas categorias de risco

O que mudou?
Três novas categorias de risco enfatizam a necessidade de abordar a segurança desde o início do design do aplicativo e de tornar a segurança parte do ciclo de vida do software.
A04: 2021
Design inseguro
A08: 2021
Falhas de software e integridade de dados
A10: 2021
Falsificação de solicitação do lado do servidor
POR QUE ISSO É IMPORTANTE?
A recente publicação da vulnerabilidade log4j2 destaca a importância das explorações de software de código aberto. As fraquezas no utilitário de registro log4j2 mapeiam duas categorias de risco do OWASP Top 10, e um CVE com explorações do mundo real o tornam uma tríade: falhas de injeção, software e integridade de dados, além de componentes vulneráveis e desatualizados.
“Um design seguro ainda pode ter defeitos de implementação que levam a vulnerabilidades que podem ser exploradas.”
—OWASP Top 10 para 2021
TEMA #3
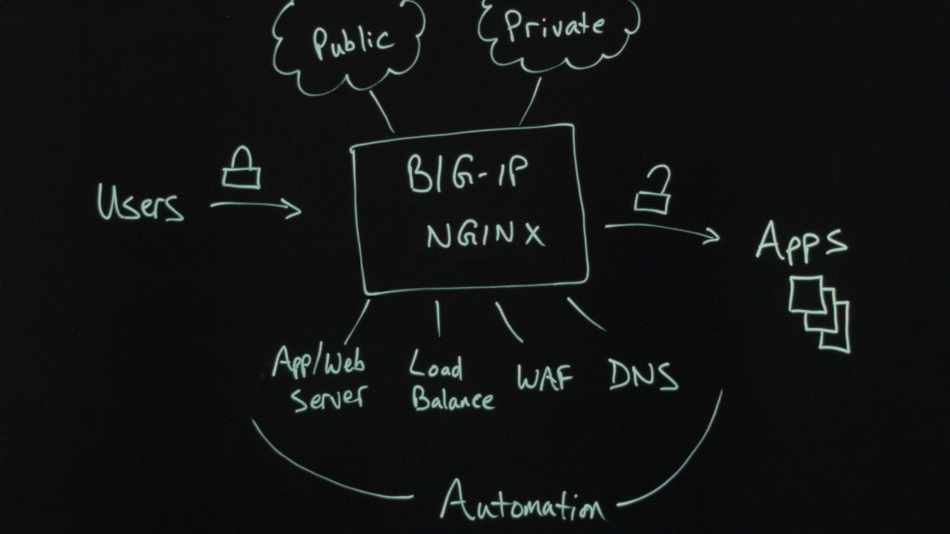
Proteção para aplicativos e arquiteturas modernas

O que mudou?
As arquiteturas de aplicativos evoluíram, com implantações em nuvem, conteinerização, aplicativos móveis e uma proliferação de APIs e integrações de terceiros. Páginas de login, carrinhos de compras e outras lógicas de negócios não são defeitos, mas são inerentemente vulneráveis a abusos. O OWASP Top 10 para 2021 oferece orientação para segurança proativa e preventiva nesta nova ordem mundial.
POR QUE ISSO É IMPORTANTE?
A segurança deve ser integrada em todo o processo de desenvolvimento de aplicativos, incluindo pipelines de CI/CD seguros, inventários de componentes, modelagem de ameaças e gerenciamento de riscos sólido. O mais recente OWASP Top 10 oferece um recurso para profissionais de segurança e AppDev/DevOps que trabalham para levar a segurança ainda mais para a esquerda, em direção aos princípios fundamentais de design.
1 Relatório de proteção de aplicativos F5 2022.
2 Van der Stock, Andrew, OWASP Top 10 , YouTube. 8 de outubro de 2021.
Descubra mais
RELATÓRIO
Relatório de proteção de aplicações F5 Labs 2022
Entenda como as ameaças evoluíram no ano passado e como as defesas de segurança podem ser ajustadas para derrotar os ataques mais recentes.
E-book
OWASP Top 10 de 2021: A Nova Onda de Risco
Aprenda a usar o OWASP Top 10 como base para um desenvolvimento mais seguro e melhor segurança de aplicações.
WEBINAR
OWASP Top 10 2021: A Nova Ordem de Risco
Veja o que mudou no OWASP Top 10 e como soluções como o F5 Distributed Cloud WAAP atenuam esses riscos.
Simulador de solução
Proteção de API e aplicativo da Web em nuvem distribuída F5 (WAAP)
Explore uma demonstração interativa de proteção holística como serviço para aplicativos, onde quer que sejam executados.
vídeo
OWASP Top 10 para 2021 — Série de vídeo de lições no Lightboard
Obtenha uma análise detalhada dos 10 principais riscos de segurança de aplicativos da Web do novo OWASP.