Data moving between clients (computers, tablets, phones, and so on) and servers is predominantly encrypted with Secure Sockets Layer (SSL) or the more modern, more secure Transport Layer Security (TLS). (For reference, see the 2019 TLS Telemetry Report Summary from F5 Labs). Today’s pervasive encryption means threats are hidden and invisible to security inspection unless traffic is decrypted.
The decryption and encryption of data by different security devices, like Palo Alto Networks Next-Gen Firewall (NGFW), can potentially increase overhead and latency. In addition to SSL/TLS visibility challenges and the fragmented nature of the security stack, enterprises are finding it challenging to design a comprehensive security strategy with any longevity.
This system reference architecture covers the different ways of structuring F5® SSL Orchestrator® and Palo Alto Networks Next-Gen Firewall (NGFW) across network topologies while also addressing visibility, privacy, and regulatory compliance challenges.
F5 SSL Orchestrator sits between the IT infrastructure and the Internet, creating a decryption zone which you can use for inspection. Within the decryption zone, security devices like Palo Alto Networks NGFW can access the data to detect and mitigate hidden threats like malware.
F5’s advanced SSL/TLS decryption technology, strong cipher support, and flexible architectures help you optimize the use of resources, remove latency, and add resilience to your security inspection infrastructure. Because all communication is funneled through SSL Orchestrator, it also serves as a strategic point of control where policies addressing operational risk (performance, availability, and security) are enforced.
SSL Orchestrator provides high-performance decryption of both inbound (from Internet users to web applications) and outbound (from corporate users to the Internet) SSL/TLS traffic. As shown in Figure 1, outbound traffic is decrypted and sent to Palo Alto Networks NGFW for inspection and detection.

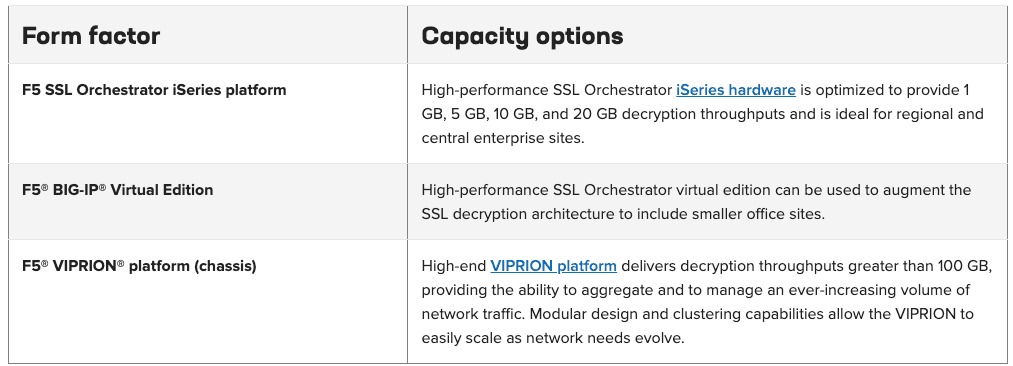
Different environments call for different architectures. SSL Orchestrator is offered in various form factors and sizes to address diverse architectural requirements.
A typical security stack often consists of multiple systems such as a NGFW, intrusion detection or prevention systems (IDS/IPS), data loss prevention, and malware analysis tools. All these systems require access to decrypted data for inspection. SSL Orchestrator easily integrates with existing security architectures and centralizes SSL/TLS decryption across multiple inspection devices in the security stack. This “decrypt once and steer to many inspecting devices” design addresses latency, complexity, and risk issues that can occur if every single security device performs decryption. You can also create multiple service chains for different traffic flows using the context engine.

“Services in SSL Orchestrator A service in the SSL Orchestrator system is defined as a pool of identical security devices. For example, a Cisco WSA service would include one or more WSA devices. By default, SSL Orchestrator will load balance the traffic to all the devices in a service. Health Monitoring SSL Orchestrator provides various health monitors to check the health of the security devices in a service and handles any device failures instantly. For example, in a Cisco WSA service, should a device fail, the SSL Orchestrator will automatically shift the load to the active WSA devices. Should all the devices in the service fail, SSL Orchestrator will bypass the service to maintain network continuity and maximize uptime.”
SSL Orchestrator’s context engine provides the ability to intelligently steer traffic based on policy decisions made using classification criteria, URL category, IP reputation, and flow information. You can also use the context engine to bypass decryption to applications and websites like financials, government services, health care, and others like them for legal or privacy purposes.

SSL Orchestrator supports an active-standby HA architecture: one system actively processes traffic while the other remains in standby mode until needed. The goal is to decrease any downtime and eliminate single points of failure. Configuration and user connection information are synchronized automatically between the systems.
“Bypass Protection SSL Orchestrator can be integrated with a bypass switch to give fail-to-wire protection. If the SSL Orchestrator system loses power, the traffic will be bypassed without endangering network performance.”
SSL Orchestrator is deployed inline in either L2 or L3 mode and can be configured as an explicit forward proxy, transparent forward proxy, or a reverse proxy. When integrated with Palo Alto Network NGFW, SSL Orchestrator can be connected via inline L2, inline L3, or receive-only TAP mode to steer the decrypted traffic as shown in Figure 4.
“User Authentication When both SSL Orchestrator and Cisco WSA are configured as transparent forward proxy, user authentication can be performed on Cisco WSA using a captive portal via SSL Orchestrator. When Cisco WSA is configured as an explicit forward proxy, user authentication should be performed by SSL Orchestrator. The same is true when Cisco WSA is deployed as upstream proxy to SSL Orchestrator.”

Figure 5 shows how SSL Orchestrator integrates into an enterprise architecture to centralize decryption for both inbound and outbound traffic across the inspection infrastructure.

As shown in Figure 6 below, SSL Orchestrator supports link aggregation using IEEE 802.1q VLAN tagging protocol to provide link redundancy for increased fault tolerance.

SSL and its successor TLS are becoming more prevalent to secure IP communications on the Internet. This can be good or bad. Good, because all communications are scrambled from prying eyes. But potentially bad, because attackers can hide malware inside encrypted traffic. If encrypted traffic is simply passed through, security systems are can’t intercept it. And that defeats the entire defense-in-depth strategy of layering security functions.
SSL Orchestrator, when combined with an advanced threat protection system like Palo Alto Networks NGFW, can solve these SSL/TLS challenges by centralizing decryption within enterprise boundaries. It can orchestrate the decrypted traffic through the entire security stack for inspection to identify and block zero-day exploits. As a result, this solution lets you maximize existing security services investments for malware protection and next-generation firewalls.
F5 (NASDAQ: FFIV) gives the world’s largest businesses, service providers, governments, and consumer brands the freedom to securely deliver every app, anywhere—with confidence. F5 delivers cloud and security application services that enable organizations to embrace the infrastructure they choose without sacrificing speed and control. For more information, go to f5.com. You can also follow @f5networks on Twitter or visit us on LinkedIn and Facebook for more information about F5, its partners, and technologies.