In just two short years, the number of devices in the average home has more than doubled, growing from just ten in 2019 to a whopping 25 in 2021 according to a Deloitte survey.
I confess contributing to this explosive growth, given the broad definition of “connected devices” that include gaming consoles. Guilty as charged.
This includes a growing constituency that relies on a variety of “smart” devices designed to bolster home security such as: motion sensors, door locks, security cameras, and hazard prevention devices like water or smoke sensors. About 12.17% of homes worldwide were “smart” in 2021. That is predicted to rise to 21.09% by 2025 according to a Statista forecast on the topic.
This convergence of physical and digital security is indicative of the broader technology trend of IT/OT convergence. While we generally tend to think of OT (operational technology) as being industrial machines associated with manufacturing or critical power generators in the energy industry, the reality is that digital control systems for physical devices are something every company is likely to employ.
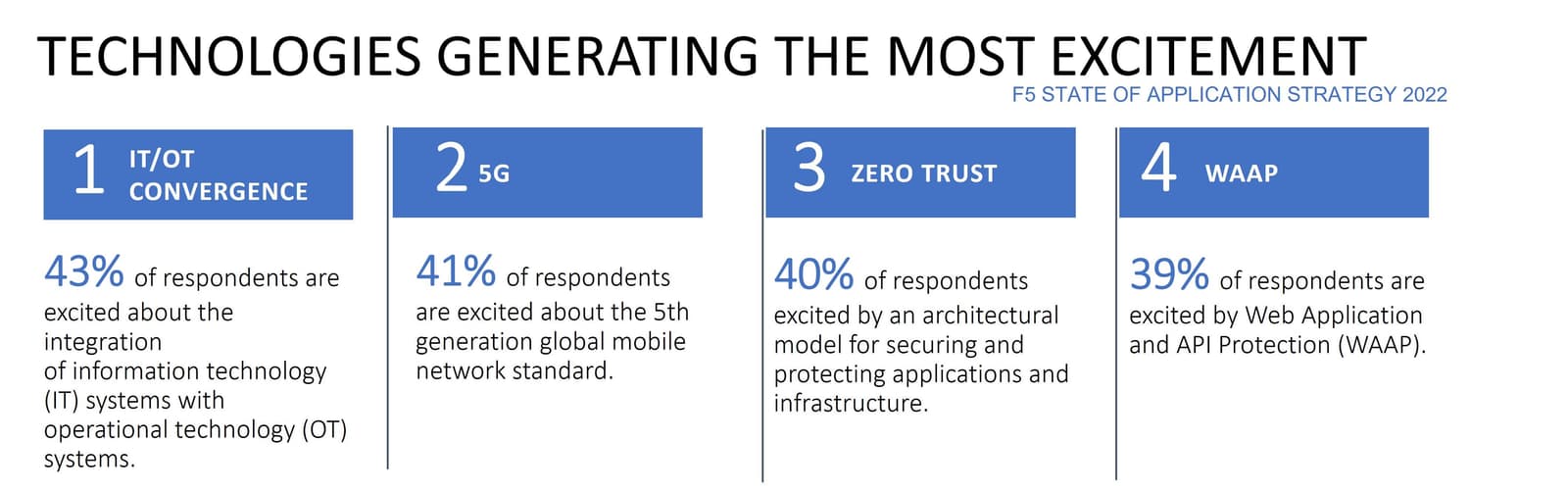
When we asked the market what technology trend excited them the most in 2021, the answer was somewhat surprisingly, IT/OT Convergence.
What might not be surprising are the industries that are most excited about this convergence of IT and OT. Energy and utilities, of course, along with manufacturing both indicated high levels of excitement for IT/OT convergence. But so did healthcare and, interestingly, technology firms.
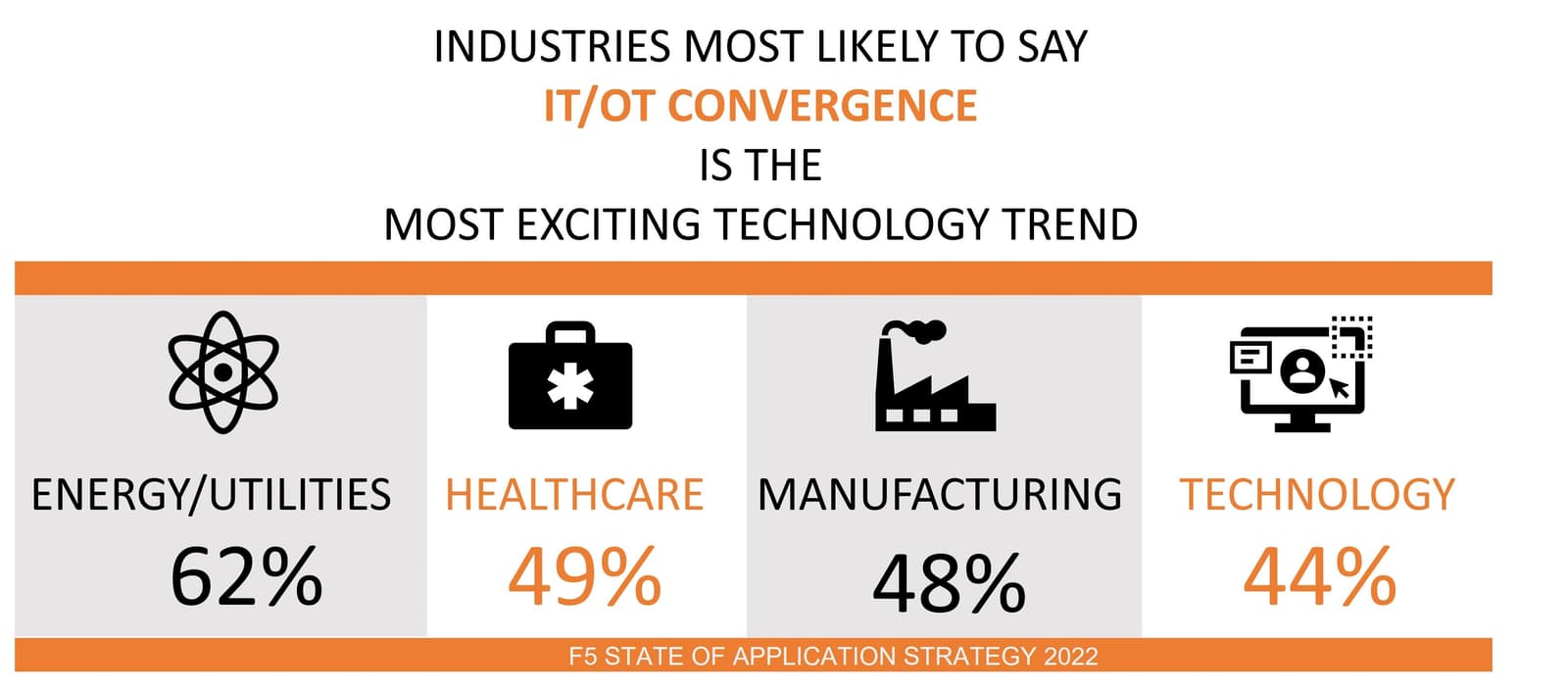
Given that IT/OT convergence is a merging of systems that manage and control the physical with those that manage and control the digital, these results should not be as surprising as they were. After all, most organizations have a robust portfolio of both types of assets, whether we immediately recognize it or not.
HVAC systems, for example, are OT. So are digital door locks and the elevators at F5 corporate headquarters. When I head to the office, there are no buttons to push. The system is wholly controlled by digital mechanisms that are closely tied to the same policies that govern my access to digital resources. Convergence brings the two worlds together, for better and for worse.
Consider reports that, during the widely covered Facebook outage in 2021, employees were unable to access conference rooms and buildings. This is certainly not beyond belief. Most technology firms would confirm that, in a highly integrated IT/OT environment, systems that control access to everything from elevators to doors could be negatively impacted by network and system outages.
Those professionals that live within the OT world already recognize the sensitive nature of operational technology and the heightened need for security for many of the systems and devices under their purview. It is no surprise that those in the security industry are at the forefront of understanding the long-term implications of IT/OT convergence on the overall security of not just IT and the business, but on consumers and customers as well. Remember, it was through a connected HVAC system that attackers were able to breach Target’s systems back in 2014.
That’s why the excitement over Zero Trust, too, is a good sign. As IT and OT converge and their systems and data become inseparable, our ability to control access to both physical and digital resources will be increasingly important.
The consequences of increasing IT/OT convergence are noticeable in our annual research in the rise of identity-centric security and the increasing value placed on access control for everything, but especially APIs. Which makes the excitement over Web Application and API Protection (WAAP) a predictable result.
As IT/OT convergence brings the two sides of IT together, there will be a need for a more comprehensive—and likely unified—means of securing access, whether by console or CLI, through app or API. And that ultimately means securing applications against attack, abuse, and misuse—no matter what side of the IT/OT fence they once sat on.
About the Author

Lori MacVittie is a Distinguished Engineer and Chief Evangelist in F5’s Office of the CTO with deep expertise in application delivery, automation strategy, and infrastructure. She is known for turning complexity into clarity whether she’s defining guardrails for AI agents, dissecting brittle multicloud architectures, or probing the limits of scalable systems. She brings more than thirty years of industry experience across application development, IT architecture, and network and systems operations. Before joining F5, she served as an award-winning technology editor. MacVittie holds an M.S. in Computer Science and is a prolific author whose publications span security, cloud, and enterprise architecture. She is also an avid tabletop and video gamer with unapologetically strong opinions about cheese.
More blogs by Lori Mac VittieRelated Blog Posts

Multicloud chaos ends at the Equinix Edge with F5 Distributed Cloud CE
Simplify multicloud security with Equinix and F5 Distributed Cloud CE. Centralize your perimeter, reduce costs, and enhance performance with edge-driven WAAP.
At the Intersection of Operational Data and Generative AI
Help your organization understand the impact of generative AI (GenAI) on its operational data practices, and learn how to better align GenAI technology adoption timelines with existing budgets, practices, and cultures.
Using AI for IT Automation Security
Learn how artificial intelligence and machine learning aid in mitigating cybersecurity threats to your IT automation processes.
Most Exciting Tech Trend in 2022: IT/OT Convergence
The line between operation and digital systems continues to blur as homes and businesses increase their reliance on connected devices, accelerating the convergence of IT and OT. While this trend of integration brings excitement, it also presents its own challenges and concerns to be considered.
Adaptive Applications are Data-Driven
There's a big difference between knowing something's wrong and knowing what to do about it. Only after monitoring the right elements can we discern the health of a user experience, deriving from the analysis of those measurements the relationships and patterns that can be inferred. Ultimately, the automation that will give rise to truly adaptive applications is based on measurements and our understanding of them.
Inserting App Services into Shifting App Architectures
Application architectures have evolved several times since the early days of computing, and it is no longer optimal to rely solely on a single, known data path to insert application services. Furthermore, because many of the emerging data paths are not as suitable for a proxy-based platform, we must look to the other potential points of insertion possible to scale and secure modern applications.
