As early as 2009, when cloud was just beginning to rise ascendant as the technology most likely to disrupt, well, everything, many of us began looking at the problem of consistency at the infrastructure level. Under the moniker of “infrastructure 2.0” we looked at the role of programmability – APIs, templates, configuration models – and the issue of achieving consistent policy provisioning and enforcement in what we then called an “intercloud” world.
Today we call that hybrid or multi-cloud, and the issue still remains: how do we achieve consistency of policy in an environment that incorporates traditional infrastructure models with cloud computing?

And it is still an issue. CloudPassage, a managed cloud security provider, commissioned a survey that garnered over 1000 responses on the topic of cloud and security, finding that “consistency across IT infrastructure” and “continuous protection” were the most important factors for protecting cloud infrastructure, with 60% and 58% percent of respondents agreeing, respectively. When asked about methods for closing the cloud security gap that continues to plague organizations, the number one method cited was the “ability to enforce consistent, continuous security policies.”
This desire for policy parity between cloud and on-premises showed itself again when We (that’s the corporate We) conducted our annual State of Application Delivery survey this year, in which 48% of the more than 3000 respondents cited “security and audit parity with on-premises” as one of the top three security requirements for cloud adoption.
The problem we sought to address back in 2009 remains: how do we achieve parity of policies across infrastructure on-premises and in the cloud without stripping security down to its bare minimum so as to support the broadest set of options possible? After all, configuration models across vendors already varies widely. Adding cloud computing into the mix only increases the variety of models and methods used to manage and control security. A standard app security policy used to implement a web application firewall (WAF) policy on-premises, for example, cannot simply by reused by a cloud provider. A distinct policy must be created, which then must be maintained, managed, and audited. Achieving parity in such situations requires diligent attention to insuring both policies are enforcing the same security in both environments.
This is unsustainable. It is operationally difficult, administratively expensive, and fraught with the potential for errors. Costly errors.
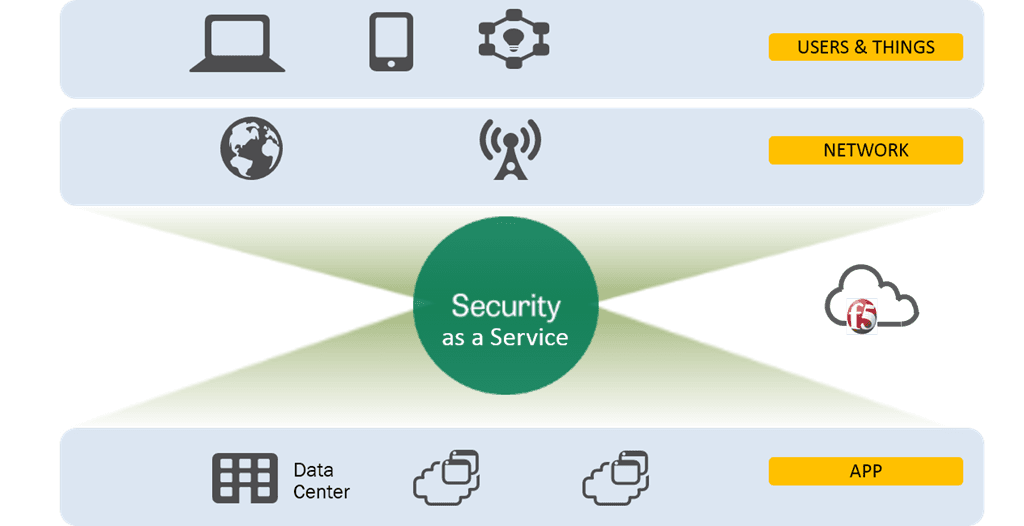
One of the ways to achieve the consistency desired is actually to look to the cloud itself, to those security services that can be offered as a service, in the cloud. Such services can generally be identified as being upstream from the application and responsible for inspection and scrubbing before application requests are allowed to reach the application. DDoS prevention, WAF services, SPAM mitigation, and malware detection are all in the category of upstream application services that can be effectively offloaded to a cloud-based service to ensure consistency of policy across all applications, regardless of whether they’re in the cloud or on-premises. Much in the same way a CDN offloads caching services, these security-as-a-service options provide consistency for multi-cloud environments because they can use the same policies or base policies across multiple applications and environments.
The need for consistent policy enforcement, particularly those policies that relate to security, is only going to grow as the Internet of Things becomes more prevalent and organizations continue to expand their presence not just in the cloud, but in many clouds. Variety may be the spice of life, but for security, too many cooks spoil the soup. And if I could find one more idiom to mix in with my metaphors, I would because it’s existentially illustrating the challenge that needs to be addressed.
Security is hard enough as it is. Adding more environments, more systems, and more and differenter policies to the mix only makes it more difficult. And in a world where there’s a shortage of security talent, it makes sense to seek out and take advantage of any solution that makes it easier to not just deploy and manage but enforce security policies in an increasingly multi-everything-under-the-sun world.
About the Author

Lori MacVittie is a Distinguished Engineer and Chief Evangelist in F5’s Office of the CTO with deep expertise in application delivery, automation strategy, and infrastructure. She is known for turning complexity into clarity whether she’s defining guardrails for AI agents, dissecting brittle multicloud architectures, or probing the limits of scalable systems. She brings more than thirty years of industry experience across application development, IT architecture, and network and systems operations. Before joining F5, she served as an award-winning technology editor. MacVittie holds an M.S. in Computer Science and is a prolific author whose publications span security, cloud, and enterprise architecture. She is also an avid tabletop and video gamer with unapologetically strong opinions about cheese.
More blogs by Lori Mac VittieRelated Blog Posts

Secure-by-design storage for agentic AI: Why runtime visibility plus traffic control matters
Learn how F5 is collaborating with NVIDIA to help protect agentic AI with secure-by-design AI infrastructure, runtime visibility, and traffic control.

F5 joins the Dell AI Ecosystem Program to help enterprises operationalize AI
F5 joins the Dell AI Ecosystem Program to help enterprises deploy production AI with greater performance, security, and control.

Why sub-optimal application delivery architecture costs more than you think
Discover the hidden performance, security, and operational costs of sub‑optimal application delivery—and how modern architectures address them.

Architecting for AI: Secure, scalable, multicloud
Operationalize AI-era multicloud with F5 and Equinix. Explore scalable solutions for secure data flows, uniform policies, and governance across dynamic cloud environments.

AppViewX + F5: Automating and orchestrating app delivery
As an F5 ADSP Select partner, AppViewX works with F5 to deliver a centralized orchestration solution to manage app services across distributed environments.
F5 NGINX Gateway Fabric is a certified solution for Red Hat OpenShift
F5 collaborates with Red Hat to deliver a solution that combines the high-performance app delivery of F5 NGINX with Red Hat OpenShift’s enterprise Kubernetes capabilities.
