Many of us may have heard the term application programming interface (API), but unless we are application developers or in technical roles, we might not be entirely sure what an API actually is (or what it does). The meaning certainly is not intuitive.
An API facilitates a channel for one application to access the information and capabilities of another. However, additional context may be necessary, so let us start with a basic analogy.
APIs Explained
Suppose you get into a car accident and need to have your car repaired. You find a reputable repair shop and work with a service representative to discuss the work that needs to be done, get your questions answered, obtain an estimate, and schedule an appointment.
It is not up to you to hire a mechanic, order parts, provide the necessary shop tools and equipment, run diagnostics tests, and so on. If the windshield needs to be replaced, the body needs to be repainted, or the wheels need to be realigned, your service rep will also arrange for those outside services to be performed.
You can think of the service rep as the interface between you and the shop—the messenger and interpreter who handles your request for services and, at the same time, spares you from having to know about all the behind-the-scenes details and complexities involved in repairing your car.
The service rep works on your behalf by taking your request, interpreting, and translating it correctly, arranging for all the services required to fulfill your request, and eventually responding to you by returning your car in working condition.
The important terms and concepts to pay attention to in this scenario are the interface as messenger and interpreter/translator, the request-response process, and the notion of shielding you, the requester, from the details of how repairs are made. These concepts are all central to how APIs work.
Let us now apply some of these concepts to a typical application you may use every day, such as a typical travel application on your phone. The app likely provides up-to-date information about flights, hotels, cruises, ground transportation, tours, and more. It is unlikely that the company that makes this app has all this information stored in its own databases or all the expertise in-house. Instead, this data is delivered via an app using APIs made available to them by partner vendors such as hotels, airlines, cruise lines, etc. The APIs are just like those service reps at the repair shop, serving up what’s needed to the requesting customer (in this case, your travel app), and minimizing unnecessary complexity.
The Building Blocks of Modern Apps
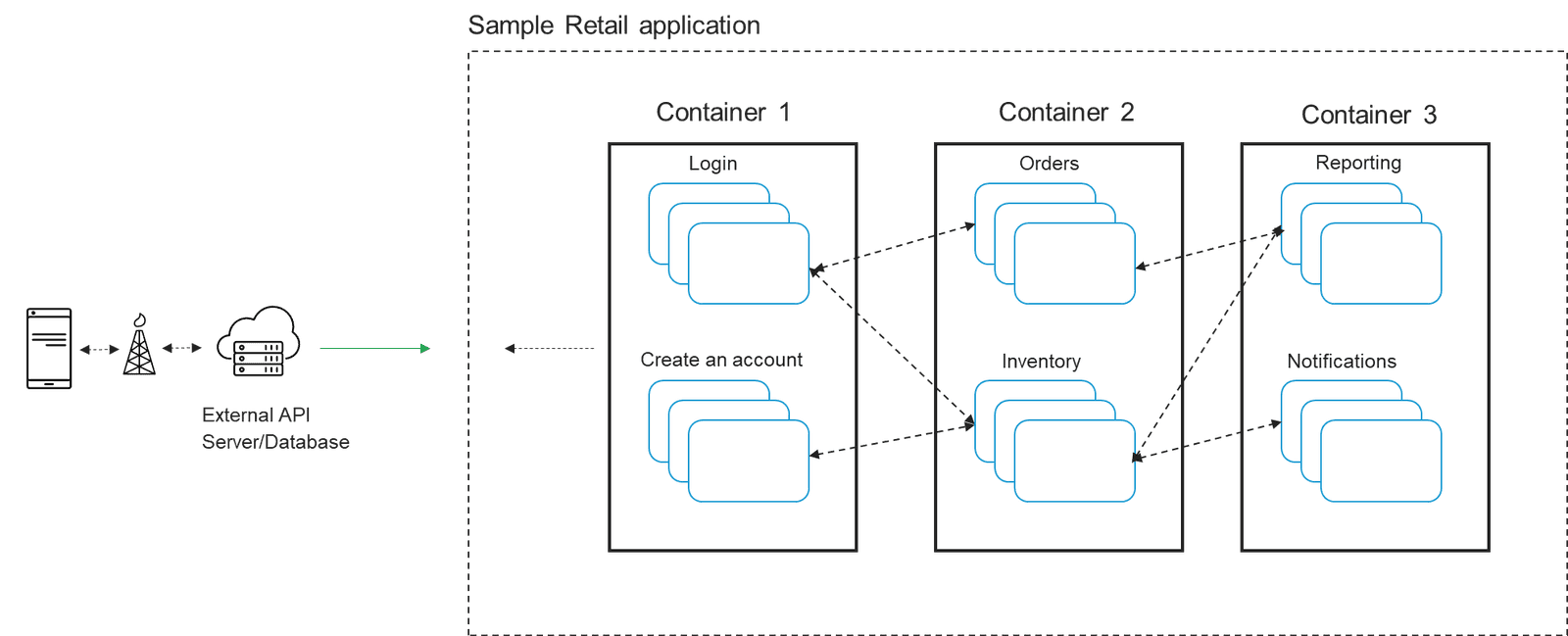
Today, APIs have become the building blocks of modern applications. And as we described in our previous blog in this series, How Modern Apps Are Built and Deployed, containers are also essential to modern applications, breaking the application down into distinct components so it is easier to manage development and future updates.
APIs are effectively the communication channels between these container clusters and the application services they share. Additionally, they facilitate data exchanges with external servers and databases. (See Figure 1 below.)
The downside is that APIs may expose data to outsiders. This makes an organization’s APIs extremely attractive to attackers, not just for access to data, but as potential entry points to other critical systems within an organization’s infrastructure. If proper precautions and security controls are not in place, APIs may pose serious risks to organizations.
APIs Expand the Attack Surface
As APIs become foundational to modern application development, the attack surface continues to expand. Unfortunately, many organizations have lagged in maintaining a proper inventory of the APIs connecting to their apps. They also need to ensure that APIs are regularly maintained and updated to avoid new vulnerabilities.
By exploiting API vulnerabilities, attackers can gain access to the network and potentially compromise an organization’s most sensitive data, including personally identifiable information (PII) or intellectual property (IP). This can damage a company’s brand and reputation, result in lost revenue, and incur significant fines.
APIs are susceptible to many of the same kinds of attacks that target web and mobile applications, including:
- Inserting malicious code into an API program, usually where an ordinary user enters their username and password—referred to as injection.
- Flooding APIs with more traffic than they can handle, making the apps they communicate with unavailable to intended users—usually referred to as a distributed denial-of-service (DDoS) attack.
- Using stolen credentials to try to gain unauthorized access to APIs—usually referred to as credential stuffing.
Understanding the Potential Risks
APIs have become the preferred method for building modern applications. And while the concept of pulling information into an application from an outside source is not a new one, constantly evolving app development methods and the pressure to innovate means organizations may not yet have grasped the potential risks involved in making their APIs publicly available before properly securing them.
The good news is that there is no great mystery involved in securing APIs. Most organizations already have measures in place to combat well-known attacks such as injection, DDoS threats, credential stuffing, and other types of attacks that also target APIs.
Watch the video below to learn How F5 is helping organizations protect the APIs that power their digital experiences.
Be sure to check out the other blog posts in our four-part series for Cybersecurity Awareness Month: How Modern Apps Are Built and Deployed, How Bad Actors Exploit Applications with Attacks, and How Online Accounts Get Taken Over by Cybercriminals.
About the Author
Related Blog Posts

Build a quantum-safe backbone for AI with F5 and NetApp
By deploying F5 and NetApp solutions, enterprises can meet the demands of AI workloads, while preparing for a quantum future.
F5 ADSP Partner Program streamlines adoption of F5 platform
The new F5 ADSP Partner Program creates a dynamic ecosystem that drives growth and success for our partners and customers.

Accelerate Kubernetes and AI workloads with F5 BIG-IP and AWS EKS
The F5 BIG-IP Next for Kubernetes software will soon be available in AWS Marketplace to accelerate managed Kubernetes performance on AWS EKS.
F5 NGINX Gateway Fabric is a certified solution for Red Hat OpenShift
F5 collaborates with Red Hat to deliver a solution that combines the high-performance app delivery of F5 NGINX with Red Hat OpenShift’s enterprise Kubernetes capabilities.
F5 Silverline Mitigates Record-Breaking DDoS Attacks
Malicious attacks are increasing in scale and complexity, threatening to overwhelm and breach the internal resources of businesses globally. Often, these attacks combine high-volume traffic with stealthy, low-and-slow, application-targeted attack techniques, powered by either automated botnets or human-driven tools.
Phishing Attacks Soar 220% During COVID-19 Peak as Cybercriminal Opportunism Intensifies
David Warburton, author of the F5 Labs 2020 Phishing and Fraud Report, describes how fraudsters are adapting to the pandemic and maps out the trends ahead in this video, with summary comments.