Many organizations are considering the best methods for building and managing their private cloud deployments. According to the 2016 State of the Cloud Survey, private cloud adoption rose from 63 percent to 77 percent over the last year, with 31 percent of enterprises running more than 1,000 virtual machines in their private clouds—an increase of 9 percent over the preceding year.1
Building out a dedicated infrastructure with the agility, scalability, and efficiency of a public cloud—while enjoying increased levels of control and security—can help enterprises boost agility and improve operational efficiency. However, while most private cloud networking services provide basic load balancing functionality, they lack important application delivery features, putting the performance, availability, and security of applications at risk.
As private clouds increasingly host mission-critical production applications, advanced application delivery services for layers 4 through 7 are becoming essential. End-to-end integration, orchestration, and automation of the needed application delivery networking and security services are also critical to improve application time-to-market and operational efficiency.
Once an enterprise settles on a platform for its private cloud, it must turn its attention to ensuring that IT can continue to deliver the consistent level of application delivery services that users expect and that the business demands. Key application delivery concepts fall into four general areas: security, availability, performance, and visibility. By examining each area, enterprises can identify the required services and then begin to make a plan to ensure their mission-critical applications remain secure, highly available, optimized, and visible when deployed in a private cloud.
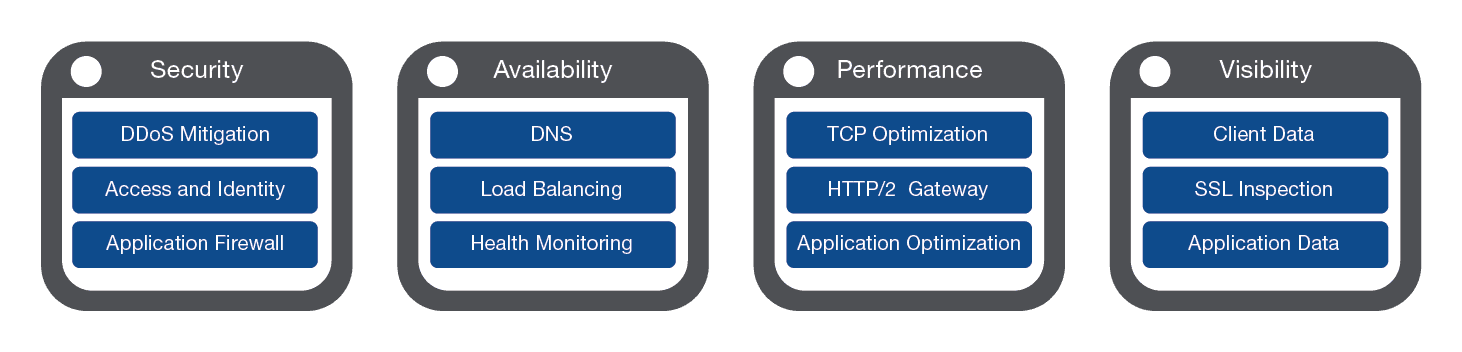
Network and application security concerns in a private cloud are largely the same as those faced by enterprises in traditional data centers and in the public cloud. Organizations confront web application threats, issues of identity and access management, mitigation of distributed denial-of-service (DDoS) attacks, and SSL and encryption concerns in their efforts to secure their applications and ensure that private data remains private.
WAF—When considering implementing a private cloud architecture, organizations must deploy advanced network firewall services, including a solution that can control traffic using basic criteria such as IP address, port, and protocol, as well as advanced principles such as HTTP protocol validation, geographical location, or endpoint reputation. In addition, a robust web application firewall (WAF) can provide comprehensive tools to identify web application threats, block malicious traffic, and offer outbound data loss prevention services.
IAM—Managing identity and access in a cloud computing environment with an increasingly distributed mobile workforce becomes more complex every day. Enterprises require a solution that provides advanced authentication services, such as two-factor tokens, CAPTCHA, or geographical restrictions, as well as client certificate checking and endpoint inspection. In addition, many organizations consider deploying SAML identity provider services to provide an architecturally sound single sign-on (SSO) solution throughout the enterprise.
DoS and DDoS—With more and more sites facing multiple denial-of-service (DoS) attacks each year, DoS mitigation services are a necessity for most enterprises running private clouds. A strong solution provides proactive bot defense as well as application-layer DoS detection and mitigation.
SSL—Finally, in the contemporary business world, SSL is everywhere. Analysts predict that encrypted traffic will jump to nearly 64 percent of all North American online traffic in 2016, up from just 29 percent in 2015.2 Enterprises must ensure security with a strong SSL solution that provides decryption, traffic inspection, and re-encryption, as well as optimize performance by offloading of computationally intensive SSL workloads from compute node resources.
One of the main benefits of the private cloud is the ability to exercise granular control over virtual resources, allowing organizations to optimize the availability of their critical applications. While most private cloud networking platforms offer basic load balancing services, business-critical applications require more advanced services.
To complicate matters, enterprises with private clouds most often operate in a hybrid cloud environment with a heterogeneous mix of private and public clouds as well as one or more traditional data centers. According to the 2016 State of the Cloud Survey, cloud users are running applications in an average of 1.5 public clouds and 1.7 private clouds.3 In these hybrid environments, global availability of applications is key. Enterprises should ensure that they have a solution that can ensure availability across a mix of environments, intelligently directing users to the closest or best-performing physical, virtual, or cloud environment.
A robust solution uses advanced algorithms to distribute traffic to the servers performing best. In addition, a multiple-step monitor enables multi-level application health checks and non-HTTP health checks on services such as SIP, Microsoft Windows SQL Server, and FTP. With the flexibility to function in virtual and hybrid-cloud environments, organizations can extend DNS services and global app availability while maintaining centralized control within the data center.
The next piece of the puzzle of extending robust application services to a private cloud is ensuring that applications perform at the level users have come to expect, regardless of the environment in which they are deployed. Organizations look for a configurable TCP stack that can be optimized to deliver across WAN and cellular networks, as well as an HTTP/2 gateway that brings the advantages of additional compression and request multiplexing without altering the back-end infrastructure.
Additional features that can optimize applications and data include on-the-fly compression dependent upon network or client characteristics as well as WAN acceleration over SSL-encrypted tunnels with adaptive compression.
With the imperative to deliver applications faster and more efficiently—with lead times of hours or days—enterprises require proactive monitoring and troubleshooting of their applications. To facilitate this, they must have the ability to see and make use of application-related data.
A strong visibility solution can automatically consolidate data from a variety of sources and provide a single interface from which the data can be interpreted. Optimally, this solution would also serve that data to existing analysis and visualization tools, as well as management interfaces, to enable automated orchestration based on the consolidated data.
Once enterprises have identified the application delivery services they want to deploy in their private clouds, they turn their attention to the question of integration. The ability to cut deployment times from weeks to minutes or to deploy hundreds of services per day is often the driving force behind the move to a cloud platform. Instead of producing a service ticket, waiting for IT, getting a purchase order, having it approved, and then waiting again, application owners or DevOps can spin up new environments in minutes.
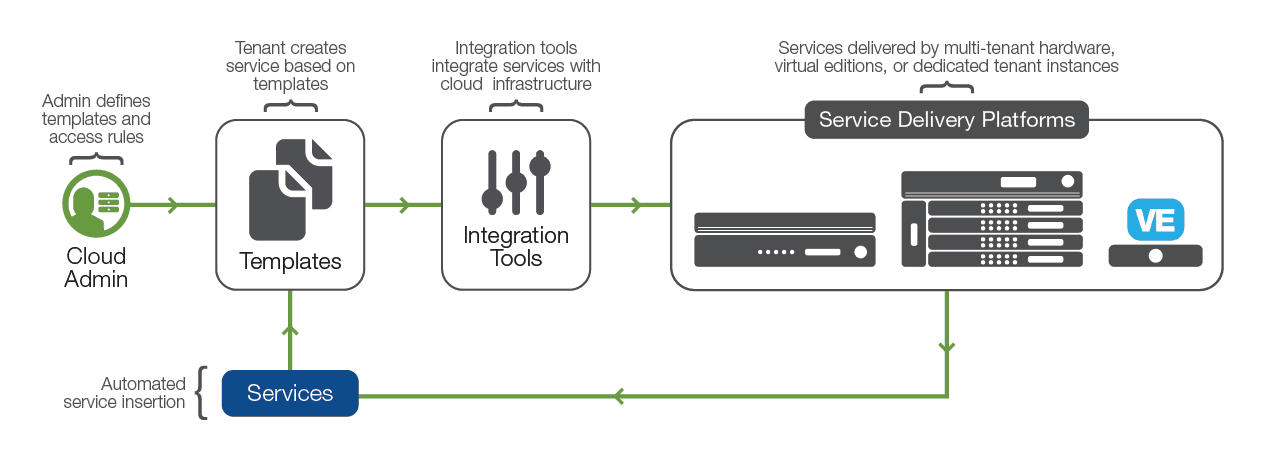
However, for this to be effective, all components of the infrastructure must be part of the automation framework. Many applications will require advanced application delivery services (such as application security or access control) to be truly production-ready, so it's vital that application delivery services integrate with the orchestration and provisioning tools of the private cloud networking platform.
In addition, with the rise of container technology, application delivery services should become tightly integrated with the container management services. When a container is provisioned, application delivery services will be provisioned concurrently.
To maximize the value of the private cloud, application delivery services must be on demand. They must be automated and orchestrated. And the whole process must be streamlined. So what's the best way to do that?
In private cloud designs, organizations can utilize a multi-tier architecture to enhance the capacity, scalability, and flexibility of their critical applications.
At the edge of the network, high-capacity, multi-tenant hardware deals with network firewalling, SSL decryption, access control, and network optimization. These general services are shared by all tenants and controlled centrally.
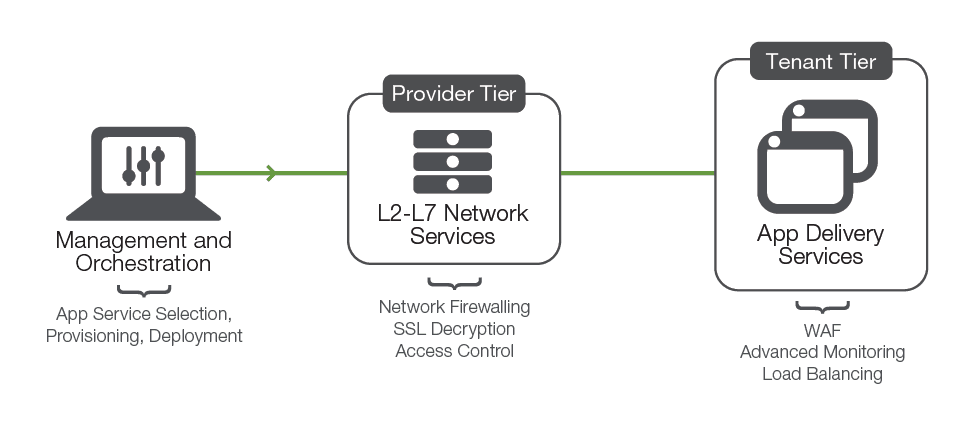
Close to the application, specific tasks such as web application firewalling, advanced application monitoring, load balancing, and content routing can be fulfilled by software-only platforms that service a single or a low number of applications tied to an organizational unit.
Once this structure is in place, attention can turn to the efficient deployment of applications. Service templates save time, ensure consistent deployments, and reduce the operational risk of manual deployments by codifying standard configuration elements for a particular service, exposing only a limited number of site or application-specific options at the time of deployment.
It only takes a relatively small number of templates to build a catalog capable of deploying the majority of an organization's applications. Each time an application delivery service is deployed from a template, key configurations are set to the organization's best practices. This can be particularly useful for activities such as identifying SSL cipher suites and logging traffic.
Service templates also allow complex application delivery services to be deployed simply and with a small number of API calls. When templates are used, the orchestration engine or configuration management tool simply requests an instance of that application type and then supplies the values required by the template. Even deploying a complex configuration—including load balancing, web application firewall services, and advanced logging—can be accomplished with a single API call, thus maximizing efficiency, reducing the possibility of errors, and speeding deployment.
However, while deploying from a template has obvious benefits, there may be occasions when, for example, a DevOps teams wants to simply spin up a server and try something out. With full, end-to-end integration with the private cloud networking platform, teams can skip the templating process and simply deploy an instance with a few clicks on a GUI.
The key here again is flexibility. When the private cloud platform is fully integrated with the means of delivering application services, enterprise teams have the flexibility to work the way they prefer without sacrificing the security, availability, performance, and visibility required.
Private clouds can deliver great benefits to enterprises that want to maximize their resources while maintaining granular control over their network operations. While most private cloud networking platforms offer a basic battery of application delivery services, enterprises that host mission-critical applications in their private clouds need more.
Organizations can map out a strategic list of required application delivery services in the areas of security, availability, performance, and visibility. The benefits of a private cloud deployment are maximized when the networking platform integrates seamlessly with the selected application delivery services. Enterprises that move proactively to ensure efficient and reliable delivery of their key applications—regardless of where they are deployed—take an essential step toward optimizing user productivity and customer satisfaction.
1 Right Scale Cloud Management Blog, 2016 State of the Cloud Survey, February 9, 2016
2Sandvine, Global Internet Phenomena Spotlight: Internet Traffic Encryption, 2015
PUBLISHED SEPTEMBER 30, 2016