SSL パフォーマンス結果: F5 BIG-IP iSeries と Citrix と A10
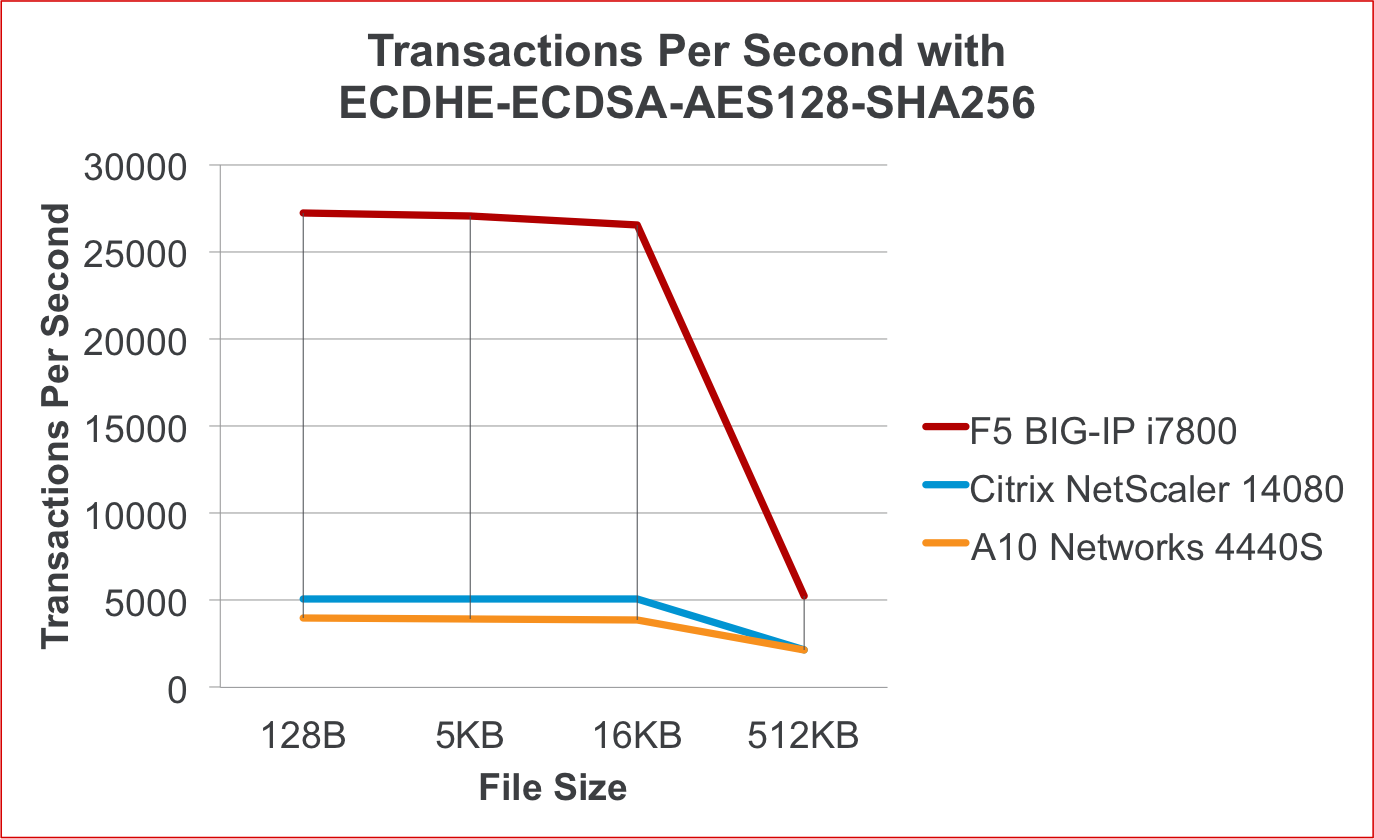
テストを実行した結果、新しい F5 BIG-IP iSeries アプリケーション配信プラットフォームは、競合他社の同等デバイスよりも 5 倍高速な SSL ECC TPS を実現しました。
世界がより広範な暗号スイートへと移行する中、F5 は SSL/TLS リーダーシップを維持できる独自の立場にあります。 旧世代の SSL ハードウェア アクセラレータを搭載した ADC は、暗号化された接続をソフトウェアで処理することで、これらの欠陥を補います。 これによりシステムに追加の負荷がかかり、アプリのパフォーマンスが低下し、容量が制限される可能性があります。 F5 の新しい iSeries には、Diffie-Hellman 楕円曲線暗号 (ECDHE) をオフロードする最新世代の暗号化アクセラレーション ハードウェアが搭載されており、高負荷の TLS 環境でも ECC および ECDHE 暗号スイートを迅速に導入できます。
iSeries のパフォーマンスが市場の他のデバイスとどのように比較されるかを判断するために、A10 Networks および Citrix の同等のデバイスと並行して、ECDH-ECDSA-AES128-SHA256 SSL 暗号を使用してプラットフォーム上で厳密なパフォーマンス テストを実行しました。
私たちのテストでは、クライアントは、ECDH-ECDSA-AES128-SHA256 SSL 暗号をサポートするクライアント側 SSL を使用して仮想サーバーに接続しました。 接続が確立されると、クライアントはファイルの単一の要求を送信し、サーバーはファイルと 200 OK で応答しました。 その後、接続はクライアントによって 4 方向に送信されました。 すべてのテストで再利用が無効になりました。
以下の数字からわかるように、当社がテストした Citrix および A10 Networks デバイスは、どちらも SSL をオフロードするために市販のシリコンを使用していましたが、F5 の iSeries 暗号化オフロード ハードウェアが提供するパフォーマンスに匹敵することはできませんでした。
1秒あたりのトランザクション数 |
|
|
|
|
ファイルサイズ |
128B |
5KB |
16KB |
512KB |
F5 BIG-IP i7800 |
27243 |
27077 |
26573 |
5251 |
Citrix NetScaler 14080 |
5103 |
5087 |
5060 |
2156 |
A10ネットワークス4440S |
3976 |
3910 |
3891 |
2135 |
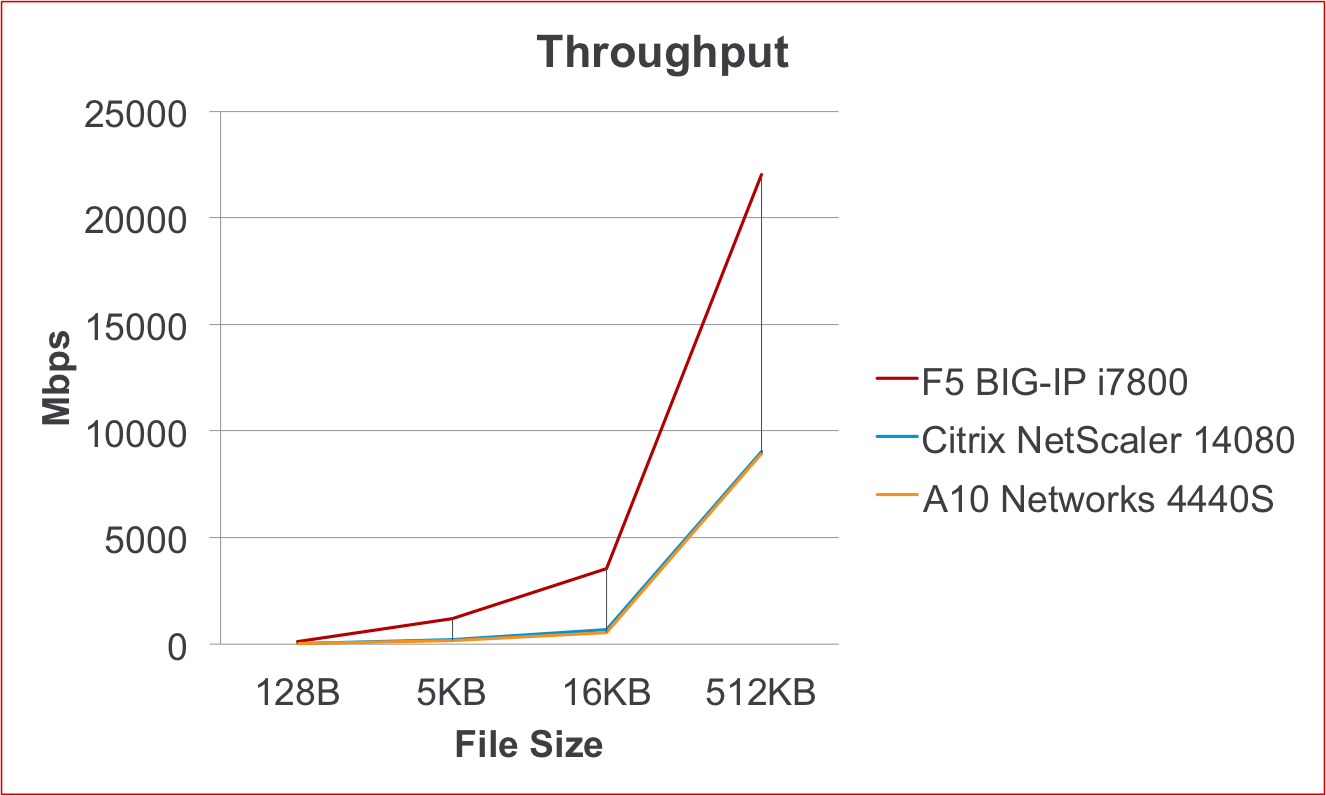
スループット(Mbps) |
||||
ファイルサイズ |
128B |
5KB |
16KB |
512KB |
F5 BIG-IP i7800 |
105 |
1185 |
3558 |
22034 |
Citrix NetScaler 14080 |
19 |
222 |
677 |
9047 |
A10ネットワークス4440S |
15 |
171 |
521 |
8955 |
テストプロセスと環境
各製品は、F5 が以前のレポートで使用したのと同じ多段階のテスト プロセスを経ています。 このプロセスは次のフェーズで構成されます。
- 予備テスト: すべての DUT がネットワーク トラフィックを同じ方法で管理できるように、各テスト対象デバイス (DUT) の構成を作成して検証します。
- 探索的テスト: これにより、各デバイスに最適なテスト設定が決定され、各タイプのテストでのパフォーマンスが明らかになります。 このフェーズで DUT の構成が確定されます。
- 最終テスト: 各タイプのテストは複数回実行されます。 少なくとも 3 回の実行で一貫して最良の結果が得られるまで、テストが繰り返されます。 この一貫性の基準に達するには、テストを何度も実行する必要がある場合があります。
- 最良の結果を決定する: 各テスト タイプについて、最も優れた 3 つのテスト実行を詳細に調べて、どのテストが全体的に最も優れたパフォーマンスを生成したかを特定します。 このレポートでは、各タイプのテストのベスト実行の結果が使用されます。
これらの結果を得るために、合計で 50 回以上のテスト実行が実施されました。
テストされた製品
私たちがテストした製品は同様の価格帯で、次のような内容でした。
- Citrix 14080 (113,069 ドル)
- A10 4440S (94,240ドル)
- F5 BIG-IP i7800(85,000ドル)
SSL処理テスト
Secure Sockets Layer (SSL) 暗号化は、ユーザーとアプリケーション間の通信を保護するために世界中で使用されています。 SSL は、すべての主要なオペレーティング システム、Web ブラウザー、スマートフォンなどで利用できる標準の暗号化プロトコルです。 SSL テクノロジーは、オンライン ショッピングの安全性を確保し、安全なリモート アクセス (SSL VPN) を実現するなど、さまざまな機能を提供します。SSL は、商用および消費者向けネットワーク セキュリティ ソリューションで広く利用されています。 SSL は、暗号鍵を共有するための公開鍵暗号と、実際にトラフィックを暗号化するための対称暗号化 (通常は RC4、3DES、または AES) の組み合わせを使用してセキュリティを提供します。 キー交換とさまざまな暗号化アルゴリズムはどちらも計算集約型であり、SSL のほぼすべての商用利用において許容できるパフォーマンスまたは大規模なスケールを実現するには、サーバー側に特殊なハードウェアが必要です。
SSL トランザクション/秒 (TPS) パフォーマンスは、主にデバイスのキー交換/ハンドシェイク容量の尺度です。 通常は小さなファイル サイズで測定され、新しい SSL セッションの開始時に発生するハンドシェイク操作を測定します。 この操作は計算負荷が高く、すべての主要な SSL オフロード ベンダーは、このタスクを高速化するために専用のハードウェアを使用しています。 サーバー応答とファイル サイズが大きい場合、ハンドシェイク操作の計算コストはそれほど重要ではありません。 操作はセッションの開始時に 1 回だけ実行されるため、オーバーヘッドは大幅に少なくなります。 パフォーマンスを比較するためのよりバランスの取れた指標は、対称暗号化またはバルク暗号化とも呼ばれる暗号化トラフィックのスループットです。 バルク暗号化は、特定の秒間に暗号化して転送できるデータの量の尺度です。
SSL トラフィックを処理するにはさまざまなアプローチがあります。 一部のデバイスでは、SSL ハンドシェイク/キー交換にのみ専用のハードウェアを使用し、進行中の「バルク」暗号化には CPU を使用します。 他のデバイスには、両方の機能に特化したハードウェアを使用できるという利点があります。 F5 iSeries は、SSL 接続のセットアップとバルク スループットを最適に処理するように独自に設計されています。 F5 iSeries プラットフォームは、高度な暗号化ハードウェアを最大限に活用することで、優れたトランザクション パフォーマンスを実現すると同時に、大量の暗号化されたバルク スループットを実現します。 これにより、顧客とシステム管理者は CPU サイクルを節約して、パフォーマンスや機能を向上させることができます。
いつものように、さまざまな状況でのパフォーマンスを実証するために、さまざまなファイル サイズ (128B、5KB、16KB、512KB) にわたってテストが実施されました。
テストは、すべての信頼できるセキュリティ機関によって推奨されている 384 ビットのキー サイズと、最も一般的な暗号アルゴリズムの 1 つである ECDH-ECDSA-AES128-SHA256 暗号を使用して実行されました。
結論
iSeries プラットフォームは、ECDHE の専用ハードウェア オフロードをサポートする最初の ADC であることを含め、お客様に包括的な SSL ソリューションを提供するという F5 のリーダーシップを継続します。 完全な前方秘匿性を実現するために ECC 暗号スイートに移行する企業が増えるにつれ、アプリのパフォーマンスを保証するソリューションの必要性は高まり続けます。 当社のパフォーマンス テストでは、F5 の iSeries プラットフォームが、今後も最も幅広い暗号スイートをサポートしながら、最高レベルのパフォーマンスを維持することが示されています。