There are two kinds of speed that security professionals struggle with. The first is related to performance, and balancing the need to respond quickly to requests with the need to protect both users and corporate assets from exploitation. This struggle is primarily one of risk management. As we discovered last year in our annual research, a plurality of organizations are, in fact, willing to sacrifice security for some defined improvement in performance.
But there is another kind of speed that security professionals—along with the businesses they serve—struggle with. That is, the speed to address emerging threats. You know, zero-day exploits of vulnerabilities. DDoS attacks targeting networks, applications, and APIs that appear out of nowhere.
We know from other industry research that when it comes to patching vulnerabilities there is a significant gap between discovery and closure that leaves businesses vulnerable to attack. We also know that pushing the right policies to address DDoS attacks to the right systems and services can also take time that, in the world of digital business, costs real money.
So it was not really a surprise when we asked respondents to our State of Application Strategy 2023 survey about the reasons they’re adopting Security as a Service (SECaaS).
Overwhelmingly the answer was “speed.”
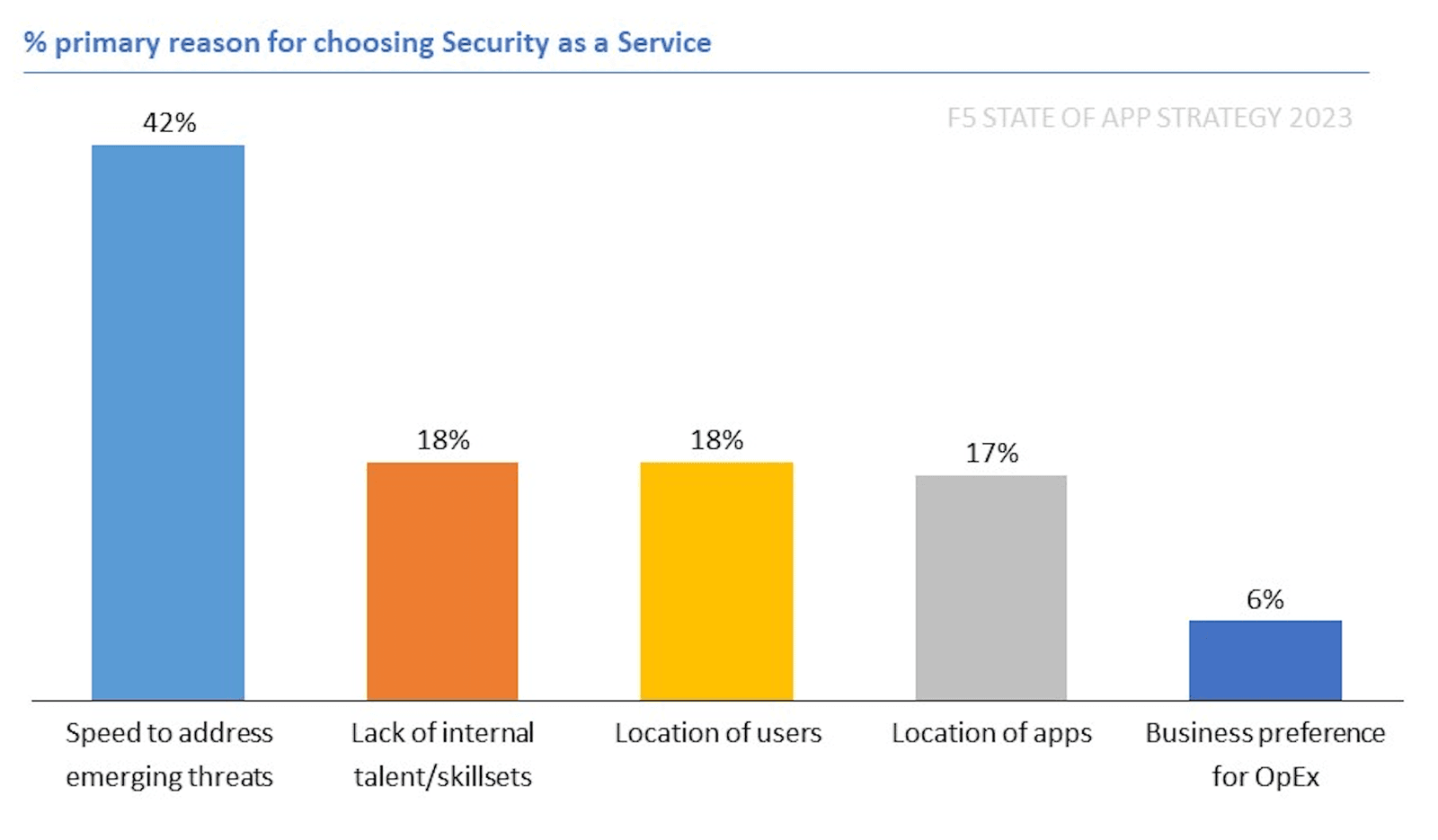
This need for speed is affecting the decisions about where to deploy workloads. For the first time in our nine-year history of conducting this research, we saw security services deployed off-premises (36%) at a slightly higher rate than on-premises (35%). No other category of app delivery services is even close to parity. But security? Security is being deployed in the public cloud and as a service in increasing numbers.
And when we looked at the types of workloads respondents planned to deploy at the edge, it is probably no surprise that those planning to deploy security service workloads tagged “speed to address emerging threats” as the top reason for adopting SECaaS.
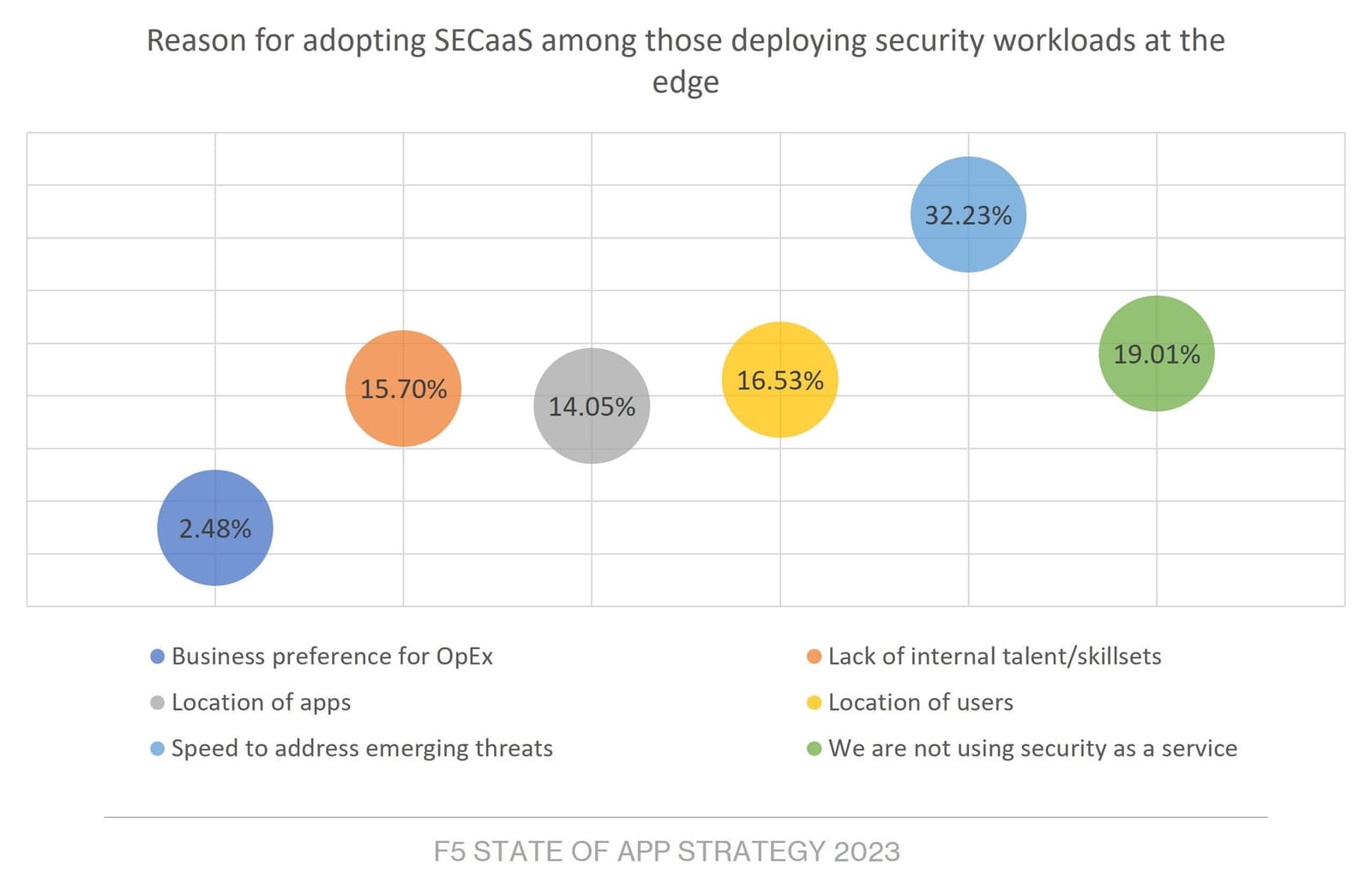
Now, none of this should be a surprise. One of the operational benefits of adopting SECaaS—whether traditional or at the edge—is the speed with which providers can address emerging threats. But it’s also good for performance. Moving security services closer to the user—which includes bad actors who pretend to be users—means detecting and neutralizing threats sooner, which prevents them from overwhelming target apps, APIs, and services.
And as readers are aware, operational axiom number two states that “as load increases performance decreases.” So, if any service or system in the critical path—between the user and the app/API—is suddenly overwhelmed by an attack, its load increases as it tries to address it. As load increases… performance decreases.
By pushing the responsibility to detect and neutralize attacks at the edge, businesses are effectively gaining both “speed” benefits—that of response time to emerging attacks and real-time performance of apps and APIs.
Now, it’s also true that not every security function is a good fit for “as a service” or at the edge. But when it comes to protections like DDoS and WAAP, it’s absolutely true that “as a service” and at the edge are good options to optimize for both kinds of speed—operational and runtime. That’s one of the reasons it’s increasingly important that the design of a digital service includes both app delivery and security considerations at design time.
One of the ways organizations are doing that is by adopting a platform approach to security. I won’t spoil our findings around that topic by diving in here, but you can read about them in our 2023 State of Application Strategy Report.
Stay safe out there.
About the Author

Lori MacVittie is a Distinguished Engineer and Chief Evangelist in F5’s Office of the CTO with deep expertise in application delivery, automation strategy, and infrastructure. She is known for turning complexity into clarity whether she’s defining guardrails for AI agents, dissecting brittle multicloud architectures, or probing the limits of scalable systems. She brings more than thirty years of industry experience across application development, IT architecture, and network and systems operations. Before joining F5, she served as an award-winning technology editor. MacVittie holds an M.S. in Computer Science and is a prolific author whose publications span security, cloud, and enterprise architecture. She is also an avid tabletop and video gamer with unapologetically strong opinions about cheese.
More blogs by Lori Mac VittieRelated Blog Posts

Multicloud chaos ends at the Equinix Edge with F5 Distributed Cloud CE
Simplify multicloud security with Equinix and F5 Distributed Cloud CE. Centralize your perimeter, reduce costs, and enhance performance with edge-driven WAAP.
At the Intersection of Operational Data and Generative AI
Help your organization understand the impact of generative AI (GenAI) on its operational data practices, and learn how to better align GenAI technology adoption timelines with existing budgets, practices, and cultures.
Using AI for IT Automation Security
Learn how artificial intelligence and machine learning aid in mitigating cybersecurity threats to your IT automation processes.
Most Exciting Tech Trend in 2022: IT/OT Convergence
The line between operation and digital systems continues to blur as homes and businesses increase their reliance on connected devices, accelerating the convergence of IT and OT. While this trend of integration brings excitement, it also presents its own challenges and concerns to be considered.
Adaptive Applications are Data-Driven
There's a big difference between knowing something's wrong and knowing what to do about it. Only after monitoring the right elements can we discern the health of a user experience, deriving from the analysis of those measurements the relationships and patterns that can be inferred. Ultimately, the automation that will give rise to truly adaptive applications is based on measurements and our understanding of them.
Inserting App Services into Shifting App Architectures
Application architectures have evolved several times since the early days of computing, and it is no longer optimal to rely solely on a single, known data path to insert application services. Furthermore, because many of the emerging data paths are not as suitable for a proxy-based platform, we must look to the other potential points of insertion possible to scale and secure modern applications.
