Avatar: The Last Airbender was a popular animated series back in the 2000s. For the uninitiated, Aang, who is the Avatar, needs to master all four elements—air, water, earth, and fire—to maintain harmony in the world. While he can wield the powers of each element separately, he’s at his most powerful when he masters all of them together.
Funnily enough, the show reminded me of the current app architecture landscape, where apps are becoming more fragmented and distributed as they are hosted in different environments. Managing API security thus becomes a lot more complex, and you’ll need a comprehensive API security strategy to mitigate API risks.
Just like mastering the four elements, what if you could have a more resilient and manageable app architecture? Here’s where a centralized application platform would certainly simplify the management of distributed app and API security.
Below are four primary tiers that serve as a foundational structure for app and API security best practices. These tiers are strategic ways to start thinking of how to simplify architectural complexity, and to better consolidate services and be more efficient—or a master of your environment like the Avatar.
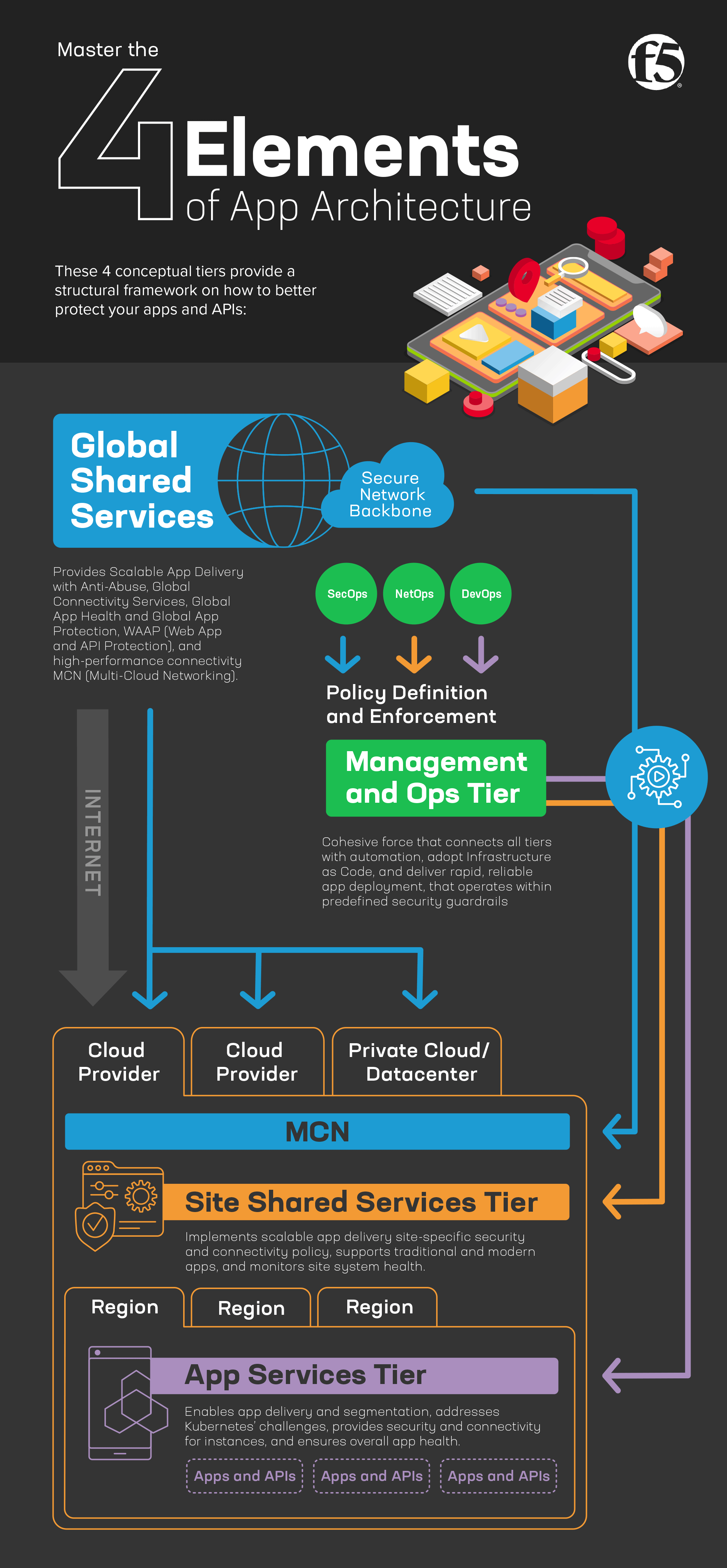
1) Global Site Shared Services Tier
Whether you are utilizing a public or private cloud infrastructure, it is crucial to ensure the security of your web applications and APIs.
For starters, think about how to secure web apps and APIs deployed in multi-cloud and distributed environments. Here’s where you implement Domain Name Server (DNS), Content Distribution Network (CDN), WAAP (Web App and API Protection) and Anti-Abuse to fortify defenses with safeguards against web/API attacks, threat campaigns, bots, and advanced fraud to ensure robust protection.
Doing so helps deliver innovation; high-performance, reliable, and secure connectivity; and zero trust security for distributed apps and APIs through a consistent configuration and operational model across heterogeneous multi-cloud environments. This is how an Environment-as-a-Service (EaaS) platform is realized, allowing both the application and the environment to run together and undergo version control. EaaS gives IT the flexibility to choose the most cost-efficient environment to test and run their apps and APIs.
Find out more on how to connect, protect, and deploy apps across the distributed cloud.
2) Site Shared Services Tier
At the site level, you can specify policies that deviate from your global policy. These site-wide policies should only contain exceptions that apply at the given locale.
The site shared services tier also plays a pivotal role in supporting both traditional and modern apps, bridging the gap between legacy systems and newer, cloud-native applications. Simultaneously, this tier serves a critical function in ensuring site security, monitoring overall system health, and continuously assessing the health of individual applications at the site. By centralizing these functions, it fosters resiliency, robust security measures, and a proactive approach to app and system maintenance at the site.
Explore how BIG-IP application services can be used to scale app traffic and secure your infrastructure.
3) App Services Tier
The app services tier delves deeper into safeguarding app segments. This layer can ignore global-level and site-level policies, and focus on app-specific protection policies.
The challenge arises when organizations transition from traditional virtual machines (VMs) to more agile Kubernetes-based environments, making it difficult to seamlessly integrate modern DevSecOps and CI/CD practices with traditional VMs and traditional API gateways.
For modern apps, lightweight and DevSecOps-friendly microgateways and dedicated API gateways as with NGINX are deployed at service endpoints that are containerized or in traditional VMs. Their primary function is to provide specialized support to specific segments of an enterprise infrastructure, strengthening security for app segmentations in Kubernetes environments and fortifying the overall security within Kubernetes clusters.
4) Management & Ops Tier
The management and ops tier represents the master level, serving as the cohesive force that integrates all other tiers through automated delivery, operational observability, insightful analytics, and a seamlessly integrated business workflow.
This is the tier where you embrace an infrastructure as code (IaC) approach to automate your app landscape’s infrastructure. This approach simplifies the management and deployment of your app architecture to comply with pre-defined security guardrails, fostering collaboration among teams (NetOps, SecOps, and DevOps) through a unified set of practices and tools. This, in turn, enables the rapid and reliable delivery of applications and their supporting infrastructure at scale.
Achieving a Harmonious State
Like how Aang eventually reaches the end of his journey, becomes a master of the four elements, and maintains harmony in the world—this structured approach through the four tiers can help you allocate and manage computing resources to ultimately achieve a more harmonious app architecture.
By adopting the various tiers, the architecture can provide more flexibility and adaptability to organizations, where they can decide where workload segments can be deployed, and enjoy lower total cost of ownership and higher development speed.
You stand to gain a unified perspective of all your workloads and applications through a centralized app/API management platform. This also simplifies real-time performance monitoring, enabling your team to promptly identify any under-performing clusters and enact automated processes and scripts to address performance issues proactively.
A well-structured SaaS-based framework not only facilitates easier scalability but also enables dynamic allocation of additional resources as required. For instance, you can deploy more compute power during periods of high user activity, and conversely, optimize cost-efficiency by removing unnecessary resources during periods of low demand.
Most importantly, this ensures that every role, from NetOps and SecOps to DevOps and architects, maintains the necessary level of access and permissions within the application, promoting security, compliance, and role-based access management for system administration.
While not everyone can be an Airbender, you can definitely be the master of your app architecture when these four considerations are met.

About the Author
Related Blog Posts

Secure-by-design storage for agentic AI: Why runtime visibility plus traffic control matters
Learn how F5 is collaborating with NVIDIA to help protect agentic AI with secure-by-design AI infrastructure, runtime visibility, and traffic control.

F5 joins the Dell AI Ecosystem Program to help enterprises operationalize AI
F5 joins the Dell AI Ecosystem Program to help enterprises deploy production AI with greater performance, security, and control.

Why sub-optimal application delivery architecture costs more than you think
Discover the hidden performance, security, and operational costs of sub‑optimal application delivery—and how modern architectures address them.

Architecting for AI: Secure, scalable, multicloud
Operationalize AI-era multicloud with F5 and Equinix. Explore scalable solutions for secure data flows, uniform policies, and governance across dynamic cloud environments.

AppViewX + F5: Automating and orchestrating app delivery
As an F5 ADSP Select partner, AppViewX works with F5 to deliver a centralized orchestration solution to manage app services across distributed environments.
F5 NGINX Gateway Fabric is a certified solution for Red Hat OpenShift
F5 collaborates with Red Hat to deliver a solution that combines the high-performance app delivery of F5 NGINX with Red Hat OpenShift’s enterprise Kubernetes capabilities.