As we continue our journey to continuous IT, there's a lot of focus on security. And well there should be. Breaches abound. Vulnerabilities are discovered on a daily basis, and the patch gap doesn't seem to be getting any smaller.
One of the often-suggested solutions to more secure code is that of scanning source code. Static and dynamic security scans have become a staple ingredient to continuous delivery processes. Our own internal pipelines include them, and I can - at any time - take a peek at a dashboard that tells me all about what those scans find.
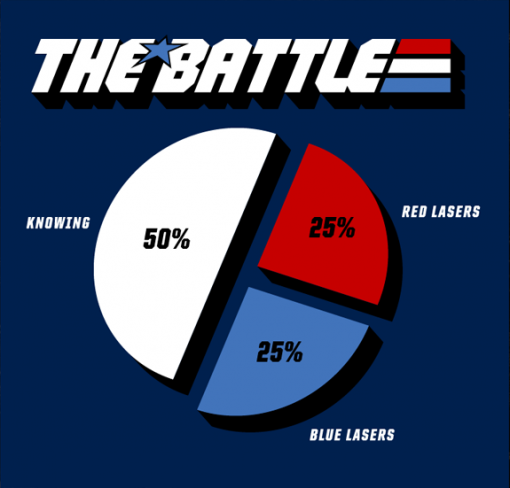 | But knowing vulnerabilities exist in source code - as G.I. Joe reminds us - is only half the battle. While it would be fascinating if the other half really was blue and red lasers, the reality of application security is that the other half is "Doing something about those vulnerabilities." Sadly, we don't see that reality becoming reality. You may recall a Tripwire report (2019 State of Container Security) in which 17% of respondents admitted to having vulnerable containers, knew what they were, and deployed them anyway. You may also recall a 2017 Arxan/IBM report on Mobile and IoT Application Security that found that 53% of respondents use static security testing and 51% use dynamic security testing for mobile apps. And despite significant concerns regarding a breach, nearly half (44%) were taking no steps to prevent it. |
The problem of not testing and not doing anything about known vulnerabilities is almost always tied to pressure to decrease time to value. Almost half (48%) of developers say they don't have enough time to spend on security (2018 DevSecOps Community Survey). Other surveys concur; there is incredible pressure on developers to churn out code faster and more frequently. It turns out that security continues to be the "thing" that's dropped when speed is on the line whether in the data or delivery path.
It's well established that people work toward what they're measured on. And as developers are people, that means they are subject to that rule, too. If they're measured on quickly getting to market, they're going to work toward that - even if it means skipping steps that compromise security. If we’re going to deliver secure applications to market, we need to embrace a cultural shift that measures and values securely getting to market as much as it does quickly getting to market.
Until it does, we're just as safe relying on red and blue lasers to deal with vulnerabilities as we are on developers.
About the Author

Lori MacVittie is a Distinguished Engineer and Chief Evangelist in F5’s Office of the CTO with deep expertise in application delivery, automation strategy, and infrastructure. She is known for turning complexity into clarity whether she’s defining guardrails for AI agents, dissecting brittle multicloud architectures, or probing the limits of scalable systems. She brings more than thirty years of industry experience across application development, IT architecture, and network and systems operations. Before joining F5, she served as an award-winning technology editor. MacVittie holds an M.S. in Computer Science and is a prolific author whose publications span security, cloud, and enterprise architecture. She is also an avid tabletop and video gamer with unapologetically strong opinions about cheese.
More blogs by Lori Mac VittieRelated Blog Posts

F5 joins the Dell AI Ecosystem Program to help enterprises operationalize AI
F5 joins the Dell AI Ecosystem Program to help enterprises deploy production AI with greater performance, security, and control.

Why sub-optimal application delivery architecture costs more than you think
Discover the hidden performance, security, and operational costs of sub‑optimal application delivery—and how modern architectures address them.

Keyfactor + F5: Integrating digital trust in the F5 platform
By integrating digital trust solutions into F5 ADSP, Keyfactor and F5 redefine how organizations protect and deliver digital services at enterprise scale.

Architecting for AI: Secure, scalable, multicloud
Operationalize AI-era multicloud with F5 and Equinix. Explore scalable solutions for secure data flows, uniform policies, and governance across dynamic cloud environments.

AppViewX + F5: Automating and orchestrating app delivery
As an F5 ADSP Select partner, AppViewX works with F5 to deliver a centralized orchestration solution to manage app services across distributed environments.
F5 NGINX Gateway Fabric is a certified solution for Red Hat OpenShift
F5 collaborates with Red Hat to deliver a solution that combines the high-performance app delivery of F5 NGINX with Red Hat OpenShift’s enterprise Kubernetes capabilities.
