The Challenge: Supporting Performant & Secure Containerized Apps
Much of what makes containers so attractive—portability, scaling, increased development and deployment efficiency, etc.—can also be risk factors because they introduce more points of exposure. While there are some native services available within container platforms like Kubernetes and OpenShift, they lack critical features such as web application firewalls and protocol gateways that can protect you from hacks, bots, and data exfiltration that can put your customer data at risk.
You need a platform that understands the transient nature of events within the cluster and can provision application services appropriately in response.
Here's What You Can Do
With a microservices-based solution, you need security and networking solutions that are aligned with that highly dynamic and transient architecture. These application services should include enterprise-grade front door security and comprehensive end-to-end visibility. F5 makes it easy to integrate app services directly into the cluster management system, regardless of where it’s hosted, allowing the security and network teams to keep services up to date without slowing down development.
How F5 Can Help
F5 provides your organization with a powerful application services platform, Container Ingress Services, that integrates with your container management solution to deliver tighter application security and optimized performance of containerized applications.
F5 does this via two key components:
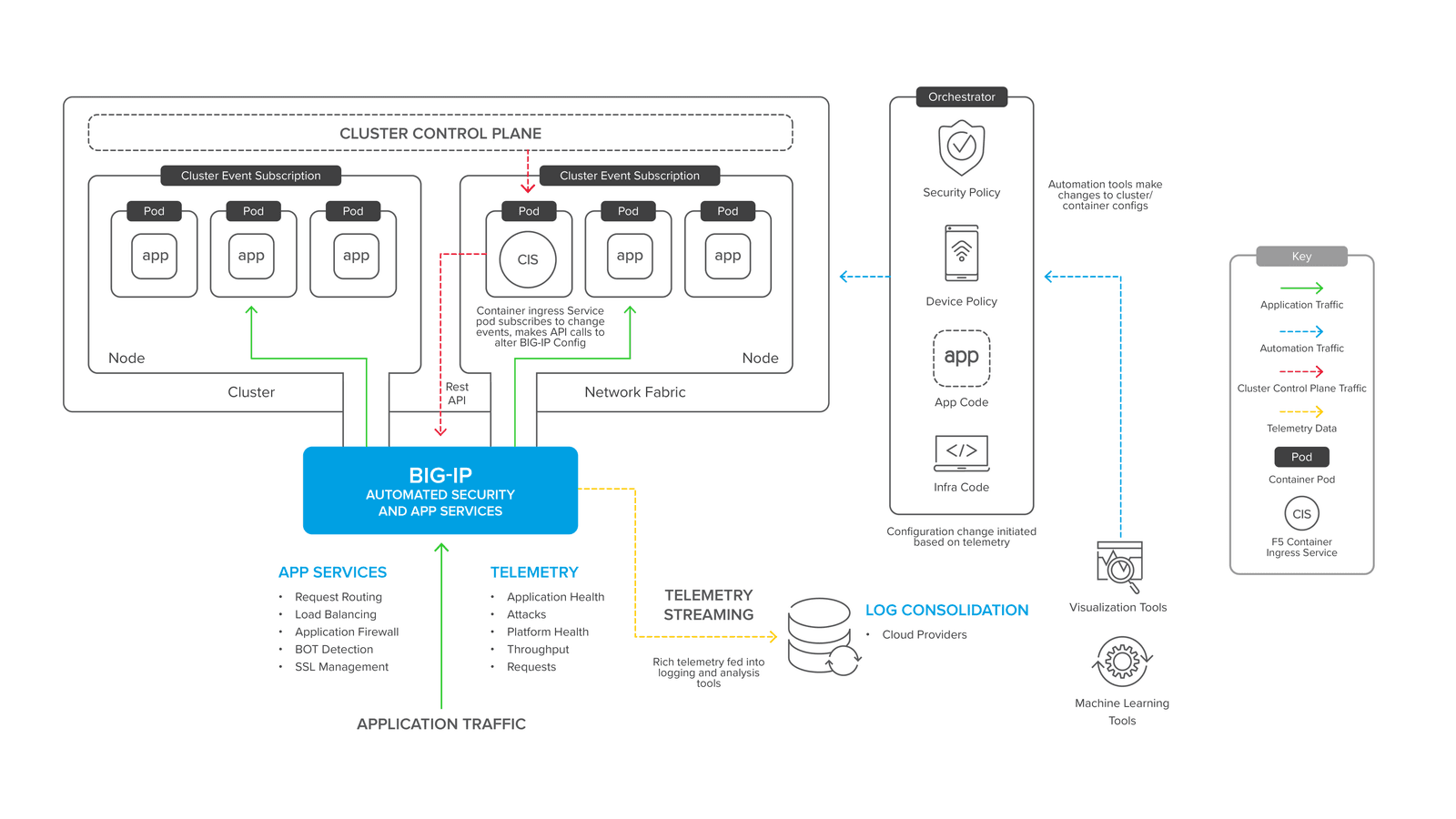
- Platform – F5’s powerful platform manages traffic, defends apps from attacks, and provides detailed telemetry for application and network teams. This is the front door to container apps, protecting and optimizing at the edge.
- Orchestration – Orchestration between the container management solution and the app services solution enables you to listen for events in the container cluster and automate configurations on the traffic management platform.
In the F5 Container Ingress Services architecture below, the container connector component (labelled CIS) listens for container management events, like new clusters or pods being created, and makes configuration changes on BIG-IP to manage traffic to new container resources. Meanwhile, BIG-IP, as well as protecting and accelerating application traffic, is supplying rich telemetry to management and visualizations services, which can then propagate changes in the container management system, closing the circle of observation to action.
Solution Guides
Challenge
Container platforms such as Kubernetes or Red Hat OpenShift combine with agile development methodologies to speed up application development and deployment. Containerized apps are no less vulnerable to application-layer vulnerabilities, denial-of-service attacks, and the impacts of client-side network latency—which means they still need app delivery and security services such as web application firewalls, TCP optimization, and protocol gateways.
But a traditional solution with a static configuration changed only by an IT operator conflicts with the agile container paradigm where new microservice containers might be created dynamically for just a few minutes to service a spike in demand or roll out an upgrade by simply replacing old containers with new ones.
How do you ensure that your app services deployments keep up with your rapid release cycles in containerized environments?
Solution
You need powerful application security and optimization services integrated with the container platform management plane.
Integration allows your app services to automatically respond in real time to container events (such as the creation of a new container, or a whole new service)—without an application developer or container platform manager needing a lot of domain-specific knowledge.
You can provide robust protection and advanced traffic management for container applications by combining the market-leading BIG-IP application delivery platform, an extended container network fabric, and a management container that integrates into the container management plane.
Components
To deliver consistent and powerful multi-cloud application services in containerized environments, organizations can leverage a few F5 components.
- BIG-IP Plateform
The BIG-IP platform is a powerful application proxy available as a software appliance for a wide range of public and private clouds—plus dedicated hardware options for on-premises deployments that require the largest scale in the smallest compute footprint. Whether deployed as hardware or software, BIG-IP provides a range of functionality to secure applications, direct incoming requests, and optimize client connections.
Although this robust set of capabilities might imply complexity, the platform supports a powerful templating system that allows security and operations experts to create standardized templates, which can be implemented by application teams with a few simple inputs and no advanced security or traffic management expertise.
Of course, you also have to be able to get application traffic in and out of your container environment—so VXLAN support is essential to extend a cluster fabric into a gateway device such as a BIG-IP. Both hardware and software BIG-IP platforms offer full VXLAN integration (as well as a number of other network overlays).
Learn more about the BIG-IP platform ›
- Container Ingress Services
The power and network integration of a BIG-IP needs to be deployed and updated in coordination with container events. To do this, F5 provides a free container integration solution—the Container Ingress Services (CIS) component, which runs as a container and subscribes to cluster management events. CIS combines event awareness with native container platform tools like config maps and annotations to configure Ingress services via the BIG-IP REST API.
Telemetry and instrumentation of your container apps is essential to their continuous improvement. As the BIG-IP platform has deep insight into application traffic, it’s an obvious point to stream stats and event data into the collection and visualization tool of your choice.
Learn more about Container Ingress Services ›
Partners
F5 works closely with its technology partners to help you optimize your apps in containerized environments.
Download the solution guide to get all the details ›
- Container Management Plateforms
Container Ingress Services are available for the following container management platforms:- Kubernetes
- OpenShift
- Cloud Foundry
- Mesos Marathon
Learn more about container management platforms ›
- Virtual Environments
The BIG-IP platform can run in the following virtual environments:
Public:
- AWS
- Microsoft Azure
- Google Cloud Platform
- Alibaba Cloud
Private:
- VMware (ESX, ESXi, vCloud Director)
- Microsoft HyperV
- Linux KVM, Xen Project, OpenStack
See all the BIG-IP Virtual Edition supported platforms ›