CISOs don’t buy web application firewalls (WAFs) for features—they buy them to reduce business risk without slowing the organization down. Yet for many enterprises, WAF solutions stall in a familiar place: the WAF is deployed, alerts are flowing, but blocking mode is delayed because tuning is expensive, cross-functional, and risky.
Meanwhile, attackers don’t wait. They probe APIs, automate credential abuse, and use evasion techniques that bypass rule sets designed for yesterday’s traffic. WAFs have evolved in response to this reality. Understanding that evolution helps explain why AI-powered WAFs are becoming a practical inflection point: they reduce time-to-protection, lower operational drag, and improve security outcomes without increasing customer friction.
“CISOs should evaluate WAF solutions based on business outcomes—how quickly the organization can reach and sustain blocking mode, how effectively threats are stopped across apps and APIs, and how little legitimate customer traffic is disrupted—rather than the breadth of individual features.”
Generation 1: Control-rich, signature-driven protection
First-generation WAFs established the baseline for web security: strong coverage for known threats through signatures and protocol enforcement. They excelled at blocking common exploits (e.g., SQLi, XSS), mapping to CVEs via large signature engines, enforcing HTTP compliance, and applying consistent policy and observability across apps. They also added important operational safeguards—masking sensitive data in logs, customizing block pages, managing allowed response codes, using IP reputation feeds, and protecting sensitive data in responses.
The challenge emerged as applications became more dynamic and the attack surface shifted toward APIs, bots, and automation. Signature-based models create a fundamental operational tradeoff:
- Tightening rules to catch more attacks leads to higher false positives and business disruption.
- Loosening rules to reduce disruption leads to higher false negatives and increased breach risk.
In practice, this becomes a tuning tax: security teams triage alerts, developers validate whether traffic is legitimate, and platform teams implement exceptions. That cycle repeats per application, per release, and often per environment. The result is delayed blocking mode, inconsistent protection, and a growing gap between what the WAF could stop and what it actually stops in production.
Generation 2: From “request inspection” to “user and session behavior”
Second-generation WAF capabilities expanded beyond payload inspection to identify and track user sessions using multiple signals—client IP, TLS fingerprinting, cookies, HTTP headers, and other identifiers. This shift matters because many modern attacks don’t look like a single “bad request.” They look like behavior over time: reconnaissance, automation, abuse patterns, or low-and-slow probing.
By tracking sessions and assigning user risk based on behavior, second-generation WAFs improved detection of bots and abusive clients and enabled mitigations such as challenge or temporary blocks. This reduced reliance on static signatures alone.
But even with better behavioral visibility, many CISOs still see the same adoption barrier: enforcement confidence. Knowing something is “suspicious” doesn’t automatically translate into a decision that won’t break legitimate traffic. Teams still end up debating thresholds, exceptions, and rule interactions—especially when applications and APIs change weekly.
Generation 3: AI-powered WAFs and outcome-based enforcement
Third-generation WAFs introduce a different operating model: risk-based decisions driven by AI-powered WAF risk scoring. Instead of forcing teams to interpret a maze of signature matches, violations, and tuning tradeoffs, the WAF evaluates multiple signals per request and assigns a risk level. That risk level becomes the enforcement primitive.
This changes the CISO conversation from “How do we tune the WAF?” to “What level of risk are we willing to accept for this app, endpoint, or business function?”
The practical outcomes are significant:
- Faster time-to-protection: Customers can move into blocking mode sooner because decisions rely on layered analysis rather than brittle single-rule triggers.
- Less operational drag: Fewer manual exceptions and less case-by-case tuning reduces cross-team friction between SecOps, AppSec, developers, and platform teams.
- Improved detection with low false positives: Multi-signal correlation helps catch more attacks while reducing disruption to legitimate users.
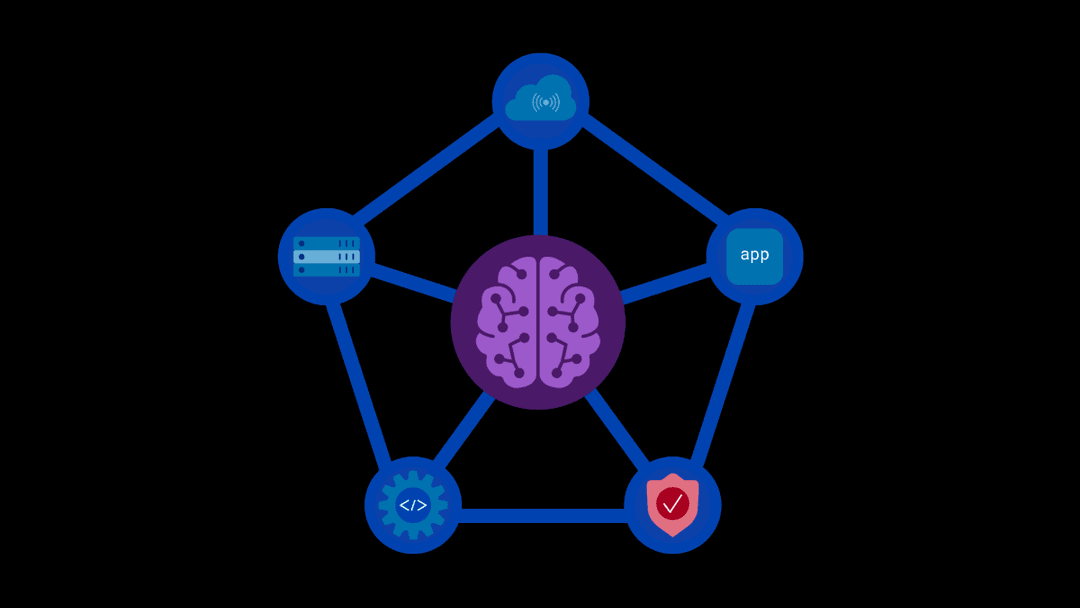
Taking a layered approach
Best outcomes come from layering Gen 1, Gen 2, and Gen 3 WAF capabilities, not treating them as substitutes.
Gen 1 controls—signatures, protocol compliance, threat campaign protections, sensitive data safeguards, and strong observability—provide high-efficacy coverage for known vulnerabilities and common exploitation techniques, and they remain essential baseline hygiene.
Gen 2 adds session awareness and behavioral tracking to connect requests into user journeys, enabling the platform to distinguish abusive automation from normal usage patterns and reduce reliance on brittle, per-URL exceptions.
Gen 3 AI-enabled risk scoring then ties these signals together into a consistent, outcome-driven decision engine—correlating signature hits, behavioral anomalies, and contextual indicators into a single risk posture per request/session—so teams can confidently enable blocking faster while minimizing both false negatives and false positives.
In combination, this layered approach delivers the highest protection with the least operational tuning: deterministic controls for what’s known, behavioral detection for what’s evolving, and risk-based enforcement to make accurate decisions at scale.
Evaluating WAFs based on business outcomes
As noted earlier, CISOs should evaluate WAF solutions based on business outcomes—how quickly the organization can reach and sustain blocking mode, how effectively threats are stopped across apps and APIs, and how little legitimate customer traffic is disrupted—rather than the breadth of individual features.
Done well, this shifts operations away from debating individual signatures and exceptions toward setting risk thresholds aligned with business tolerance—improving protection while keeping false positives low across distributed environments.
To learn more, about F5 Distributed Cloud WAF and its AI-based capabilities, visit our product page or contact our team to schedule a demo.
About the Author
Related Blog Posts
F5 Distributed Cloud Services: Security innovation built for operational scale
Learn how the latest upgrade to F5 Distributed Cloud Services advances AI driven security while strengthening the operational foundations teams need to run at scale.
From dashboard fatigue to operational excellence: Why XOps needs F5 Insight for ADSP
Learn how F5 Insight for ADSP lays the visibility foundation for XOps—turning fragmented signals across applications and infrastructure into actionable intelligence.
The hidden cost of unmanaged AI infrastructure
AI platforms don’t lose value because of models. They lose value because of instability. See how intelligent traffic management improves token throughput while protecting expensive GPU infrastructure.
Govern your AI present and anticipate your AI future
Learn from our field CISO, Chuck Herrin, how to prepare for the new challenge of securing AI models and agents.

F5 recognized as one of the Emerging Visionaries in the Emerging Market Quadrant of the 2025 Gartner® Innovation Guide for Generative AI Engineering
We’re excited to share that F5 has been recognized in 2025 Gartner Emerging Market Quadrant(eMQ) for Generative AI Engineering.
Self-Hosting vs. Models-as-a-Service: The Runtime Security Tradeoff
As GenAI systems continue to move from experimental pilots to enterprise-wide deployments, one architectural choice carries significant weight: how will your organization deploy runtime-based capabilities?