Policy enforcement is the process of managing network and application connectivity, access, and use according to one or more policies defining the conditions under which access is allowed.
In a computing context, policy enforcement typically refers to the creation, categorization, management, monitoring, and automated execution of a specific set of requirements for use of a computer or communications network—that is, not only the enforcement of policies but policy definition, application, and management more generally.
Policies may address virtually any “who, what, where, when, how, or why” parameters, including who can access resources, when, from where, using what devices or software, what the user can and cannot do once access is granted, for how long, and with what auditing or monitoring. Policies may also address more technical interactions or requirements such as protocols to accept, ports to use, or connection timeouts.
Organizations create policies to control, manage, and sometimes monetize their assets and services. Network policy enforcement helps to automate data and asset security measures, including BYOD requirements. It can enable a service provider, for instance, to create differential rates for specific services or times of use. It also can be used to help enforce enterprise ethical standards (such as use of company equipment and time for personal ends) and to better understand and manage network use.
Policy enforcement is typically handled by software or hardware serving as a gateway, proxy, firewall, or other centralized point of control in the network. Policies must first be defined, along with one or more actions that will be taken if a violation occurs. Once policies are defined, the software or hardware becomes a policy enforcement point in the network—a nexus where policy enforcement occurs in three parts:
For instance, a policy may identify known malicious IP addresses and specify that any and all traffic from those addresses be rejected. More complex policies may allow a specific user to connect to some applications but not others, or to perform some actions once connected that will incur a higher fee than others (such as using a streaming service on a high-resolution device). In this way, authentication, authorization, and accounting (AAA) systems are a form of policy enforcement.
Network policy enforcement may require compliance with more sophisticated and granular parameters such as the presence of unexpired certificates, the type or version of a device or browser being used to connect, or an absence of patterns of behavior associated with attacks.
Monitoring or documentation of the entire enforcement process, particularly incidents of noncompliance, is often part of a policy enforcement solution.
Multiple F5 products can serve as gateways or full proxies that enable granular control over policy creation and enforcement from a single, centralized point of control. In particular, BIG-IP Policy Enforcement Manager (PEM) provides sophisticated controls for service providers looking to monetize services and improve network performance. For enterprises, BIG-IP Access Policy Manager (APM) delivers context-based management of access to applications with a graphical user interface called Visual Policy Editor (VPE) that makes it easy to create, edit, and manage identity aware, context-based policies.
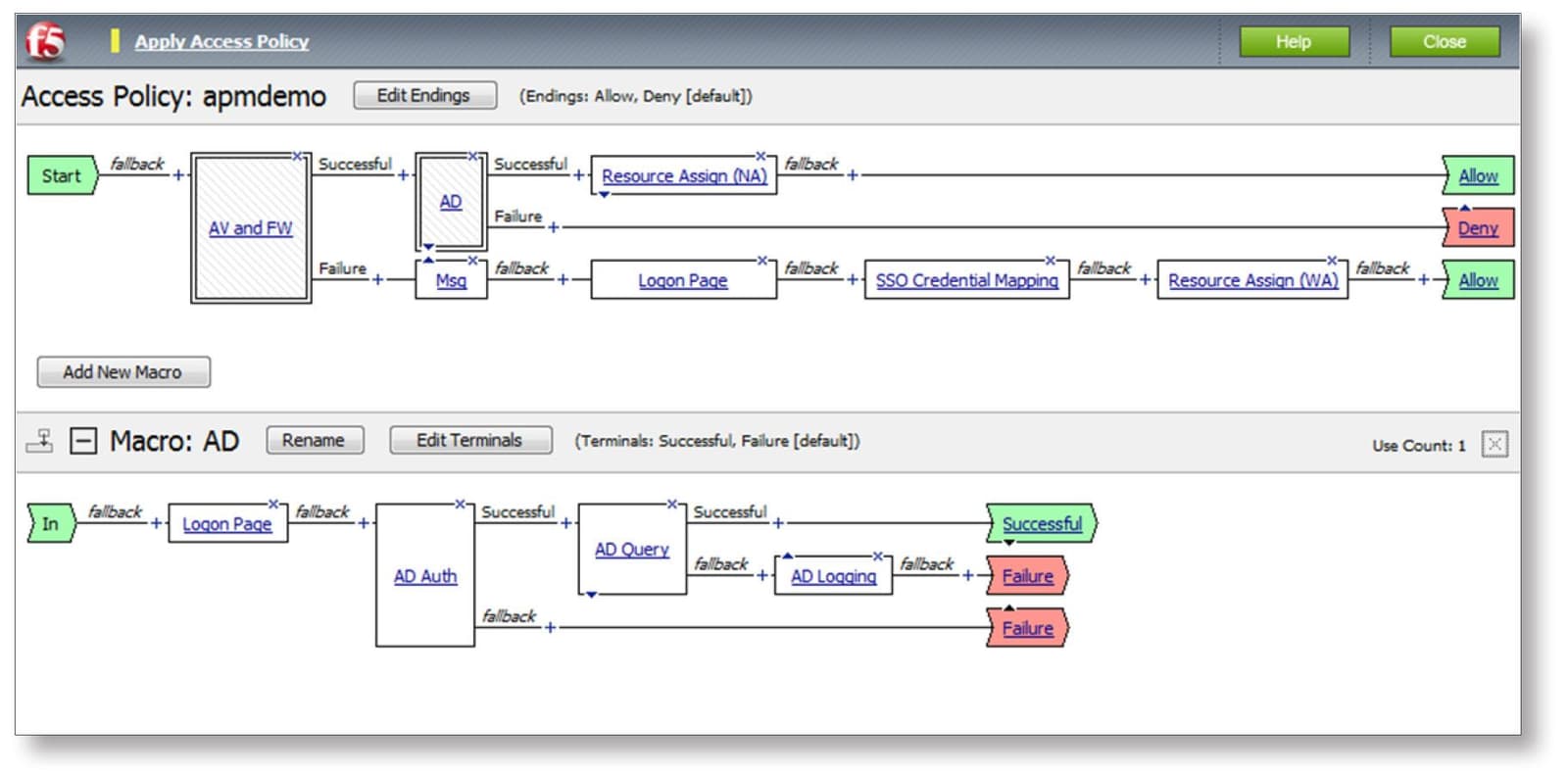
Figure 1: The BIG-IP APM Visual Policy Editor