Get a Free Application Security Threat Assessment
F5 Distributed Cloud Offers Real-Time Protection
F5 Distributed Cloud platform safeguards the world’s largest brands, protecting billions of accounts and transactions every day.
F5 Distributed Cloud makes it possible to stop malicious automated attacks, identify fraudulent human activity, and reward legitimate users—all in real time. Interested in seeing Distributed Cloud's defense in action? Reach out for a complimentary application security threat assessment. Our automation and fraud experts will study your web and mobile applications and provide you with a summary of how attackers can target them. You will also receive a set of recommended next steps. |
Prevent Attacks That Start with Bots and Evolve into Fraud
Prevent sophisticated, human-emulating automation and retooling
Securely reduce friction to improve customer experience
Monitor every transaction for signs of fraud or risky behavior
F5 Distributed Cloud fits into your existing infrastructure
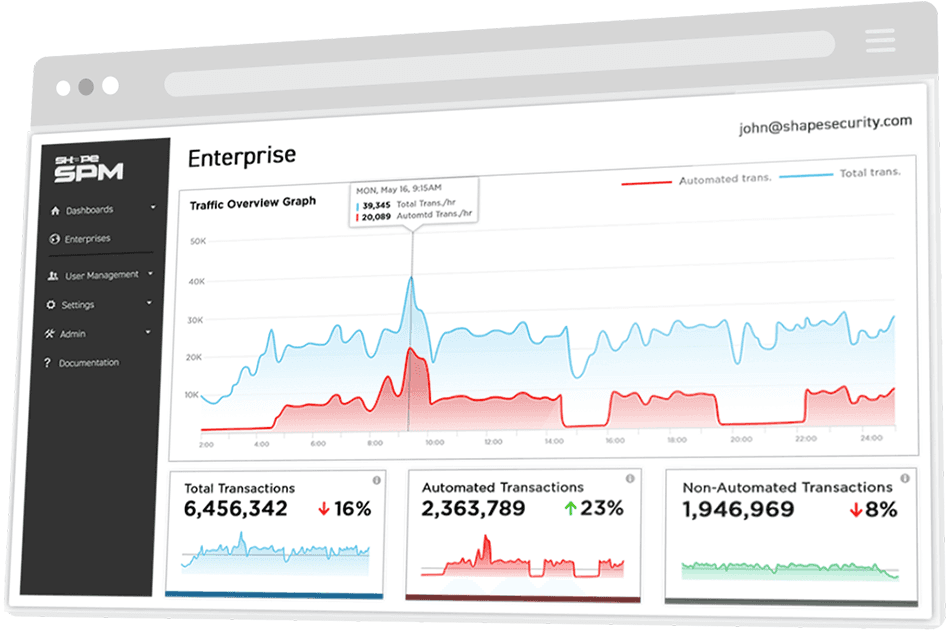
F5 Distributed Cloud in Action
Learn how F5 Distributed Cloud has defeated account hijackers and saved tens of millions of dollars for customers.
CASE STUDY
F5 Distributed Cloud Helps a Digital Bank Detect 177% More Fraud Than Existing Fraud Solutions


