Modern 5G networks are designed for ultra-low latency, massive scale, and cloud-native service-based architectures that span the radio access network (RAN), core, and edge.
While this architecture enables unprecedented agility and scalability, it also introduces new operational challenges. The 5G core is no longer a set of centralized network elements: it’s a dynamic mesh of containerized services, often deployed across multiple vendors, each with its own implementation, security model, and visibility tooling.
As a result, traditional monitoring approaches struggle to provide a coherent view of what is happening inside the control and user plane. Encryption obscures critical signaling data, vendor-specific instrumentation creates silos, and legacy packet-based tools introduce cost, complexity, and performance overhead, leaving operators with significant blind spots just as networks become more critical to business outcomes.
The 5G core is a distributed mesh of microservices communicating over encrypted HTTP/2-based SBIs (service-based interfaces). With each vendor implementing its own stack and security model, it’s difficult to understand what is happening inside the control and user planes.
The 5G observability challenge
Traditional monitoring tools were designed for static networks and unencrypted packet flows. In today’s containerized 5G architectures, those assumptions no longer hold because:
- Workloads are dynamic. Network functions (NFs) scale up and down continuously, creating gaps in visibility and correlation across the control and user planes.
- Traffic is encrypted end-to-end. Transport Layer Security (TLS) 1.3 and HTTP/2-based SBI messaging conceal metadata that legacy monitoring and security systems depend on.
- Multi-vendor integration creates friction. Each vendor provides its own virtual tap (VTAP) or packet-capture mechanism, limited to its own NFs, formats, and operational boundaries.
- Fragmented visibility weakens security. Without a unified view of subscriber, session, and network-function behavior, zero-trust enforcement and anomaly detection become extremely difficult to implement consistently and at scale
These challenges are amplified by the distinct characteristics of 5G networks, such as:
- Unique and legacy protocols and protocol stacks, spanning both SBI and non-SBI (PFCP, NAS, NGAP, F1-AP)
- Legacy generations of physical infrastructure
- Need for monitoring across multiple domains, including infrastructure, application (network function), security, operating system, and orchestration
- Geographic coverage and user experience demands that require vast, scalable, high-connectivity networks
To protect these environments, operators need real-time visibility into every message, session, and subscriber event, without introducing additional overhead or operational complexity. Policies must be able to adapt instantly to risk, while also meeting evolving regulatory and compliance mandates.
Subscriber awareness is critical for advanced security use cases. It’s also fundamental for compliance, auditing, and lawful intercept requirements that depend on accurate, consistent subscriber identification across network logs and domains.
Cloud-native visibility challenges
Cloud-native visibility in distributed environments is inherently challenging. Workloads are dynamic, short-lived, and often hidden behind orchestration layers, making traditional, packet-centric monitoring models increasingly ineffective.
Traditional methods of establishing visibility were designed for static infrastructure and centralized traffic flows. In cloud-native 5G environments, these approaches introduce blind spots, operational overhead, and scaling limits.
F5 BIG-IP eBPF Observability enables
streamlined and optimized 5G
Modern 5G environments demand a consistent, high-performance observability layer that can spans vendors, understands both 5G-specific SBI and non-SBI protocols, and provides the contextual intelligence required to support security, operations, and compliance workflows.
F5 BIG-IP eBPF Observability (EOB) delivers this capability by capturing rich metadata from lightweight, containerized agents deployed across the 5G core, edge, and multi-access edge computing environments. Built on eBPF technology, each agent observes traffic directly at the kernel level, covering both control-plane (SBI, NGAP, PFCP) and user-plane traffic without relying on sidecar, packet brokers, or vendor-specific TAPs.
Unlike traditional approaches, EOB uses a single agent per node to provide complete visibility across all pods and containers on that node, minimizing operational overhead while eliminating blind spots introduced by encryption and dynamic scaling.
Telemetry from these agents is streamed in real time through a secure message bus to downstream analytics, service assurance, and security platforms. This enables a continuous operational loop, observing network behavior, analyzing context, enforcing policy, and adapting dynamically as conditions change.
How it works
BIG-IP EOB provides a unified, node-level observability layer across cloud-native 5G environments, spanning the core, edge/MEC, and distributed infrastructure.
BIG-IP EOB consists of lightweight, containerized agents that can be deployed anywhere Kubernetes runs. Using eBPF technology, each agent observes network activity directly at the kernel level, enabling deep visibility into both control-plane signaling and user-plane traffic without relying on sidecars, packet brokers, or vendor-specific taps.
EOB agents capture and generate multiple types of telemetry from network traffic and internal container communications, including:
- Raw packets (for targeted troubleshooting)
- Dynamic topology and service relationships
- Metadata extracted from encrypted traffic (including TLS 1.3)
- Protocol-specific context (for example, F1-AP, SBI, DNS, HTTP)
- Advanced cloud-native flow records (CNFlow)
Analytics platforms and third-party tools can programmatically request only the specific data required for a given use case—reducing overhead while preserving full-fidelity visibility when needed.
All BIG-IP EOB telemetry is streamed continuously in real time through a secure message bus for immediate consumption, supporting both synchronous and asynchronous workflows. This architecture enables a continuous operational loop across service assurance, security, infrastructure analytics, and open-source tools—without introducing blind spots or performance penalties.
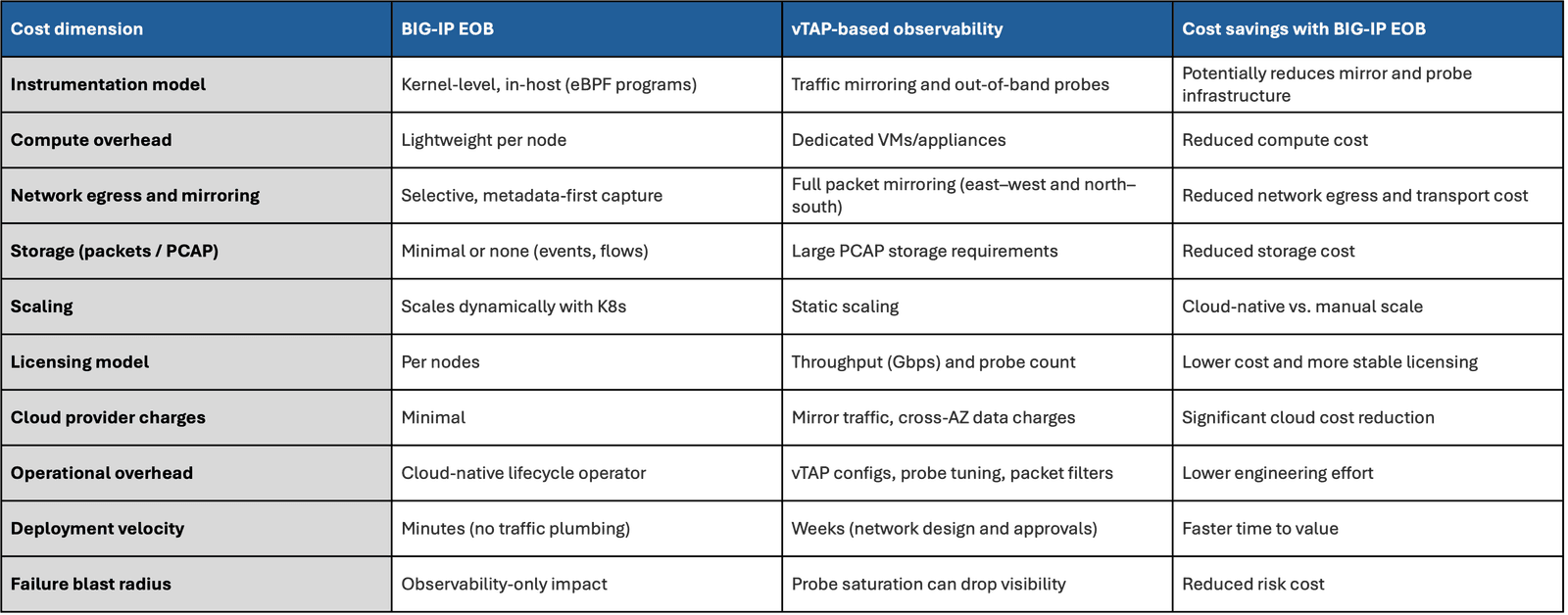
BIG-IP EOB vs. vTAP-based observability
Integrating BIG-IP EOB delivers clear advantages vs. traditional methods:
Real-world impact
At a large tier-1 service provider, BIG-IP EOB was deployed across a multi-vendor 5G core that previously relied on multiple vendor-specific vTAPs. The operator faced inconsistent telemetry, visibility gaps across network functions, and excessive resource consumption driven by third-party probes.
By deploying a single BIG-IP EOB agent per node, the operator established unified, vendor-agnostic visibility across the 5G core. Telemetry was streamed in real time into the cloud-native analytics and security platforms, including F5 BIG-IP Advanced Firewall Manager (AFM) running as a CNF, enabling faster insight and more consistent policy enforcement.
Measurable improvements included:
- Unified visibility across network functions without vendor dependence
- Reduced resource utilization compared to legacy vTAP-based approaches
- Faster response times for troubleshooting and policy-driven enforcement
Because BIG-IP EOB is built on open standards and a containerized architecture, it integrates seamlessly with both F5 solutions and third-party analytics platforms. Telemetry can be streamed to security information and event management (SIEM) systems, artificial intelligence and machine learning pipelines, or service-assurance platforms such as NETSCOUT or EXFO, enabling broader operational insight without duplicating data collection.
Conclusion
By combining deep, kernel-level visibility with a lightweight, cloud-native deployment model, BIG-IP EOB enables operators to eliminate blind spots across modern 5G and cloud-native workloads.
BIG-IP EOB provides real-time, vendor-agnostic observability that spans 5G core, edge, and distributed infrastructure, extracting critical content from encrypted, dynamic environments without introducing additional overhead. By streaming high-fidelity telemetry to existing analytics, service assurance, and security platforms, EOB helps operators move from reactive troubleshooting to faster insight, stronger policy enforcement, and more resilient network operations at scale.
Find additional product information at f5.com. To connect with a sales specialist, contact F5 Sales.