Visibility is an often-cited challenge typically referring to the ability to inspect traffic, transactions, and errors that occur during an application's execution. But there's another, perhaps more critical, meaning to visibility at the business layer: a complete inventory of the corporate application portfolio.
In the first years of our State of Application Services (then called State of Application Delivery) research, we used to ask how many apps a respondent could shut down without anyone noticing.
Our intent was to discover just how many apps were really "critical" to the business, either for profit or productivity.
We don't ask anymore, because it turns out that most folks have absolutely no idea how many apps are in their portfolio let alone what percentage is critical.
Consider the answers to the question in 2017, in which 2104 respondents took to the time to give us a response.
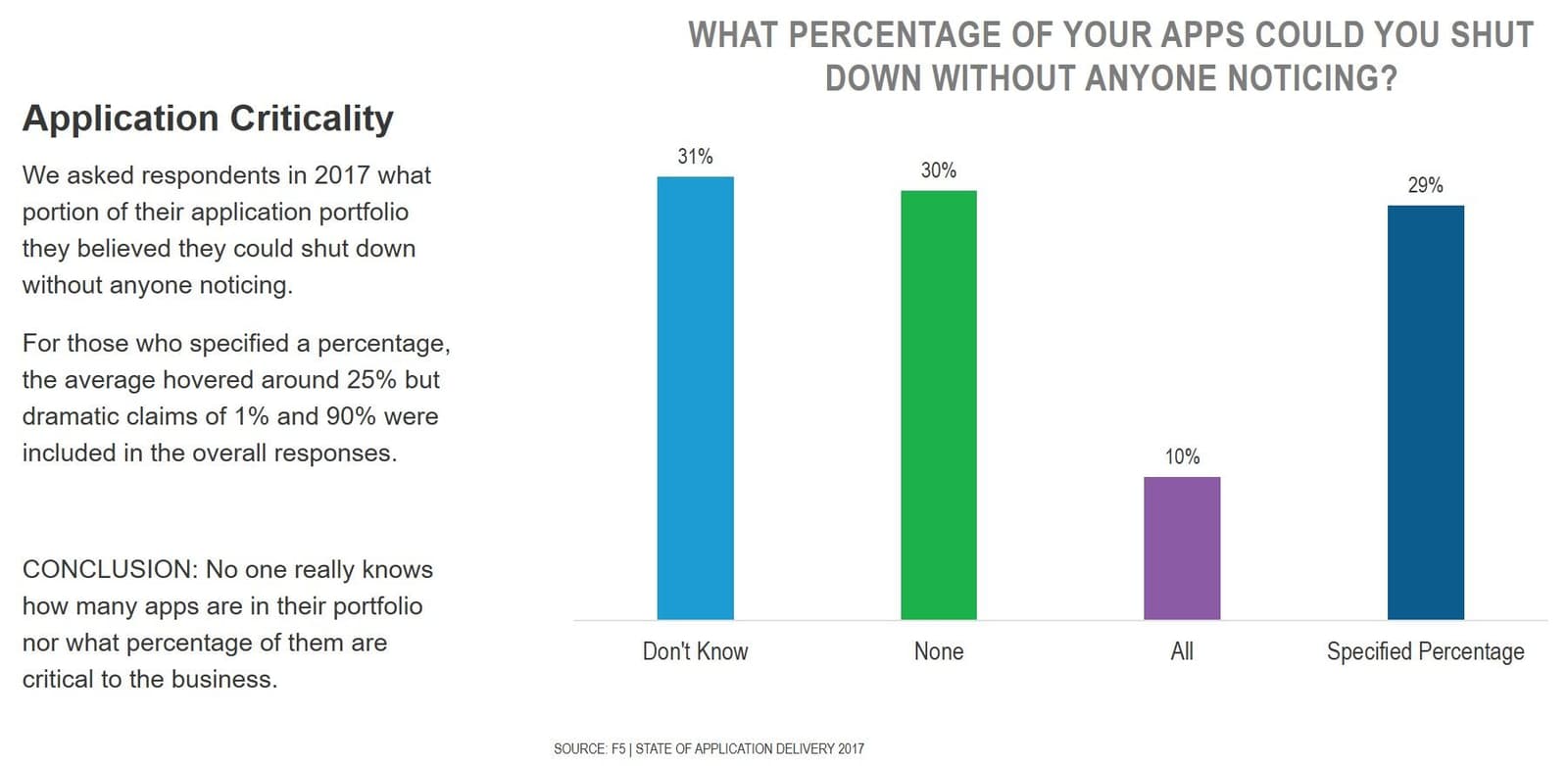
This exercise seems to validate the observation of our own Kara Sprague, who has noted that "0% of customers can report with confidence the number of applications in their portfolio."
To be fair to customers - and the market at large - a significant portion of businesses today are multi-generational. The CIO, who probably should have a good idea, likely didn't exist as a position until the late 1990s. And those who sit in the CIO chair today are likely not the same person who sat in it just a decade earlier. Cataloging and inventorying application portfolios was not something we even talked about until well after the turn of the century.
And let's not discount the impact of acquisitions and mergers on application portfolios. Even if you did know the exact number of apps in your portfolio, what about the companies you've acquired - or the one that acquired you?
The reality is that only in the last few years has the market come to recognize just how important - how critical - applications are to their respective businesses. They are the capital in which we invest today with the hopes and expectation it will pay off in the future.
Which means we really ought to protect them better, because they are under attack. Constantly.
That task is made more difficult by the ability to find them, in the first place.
But find them we must. Because while we may be protecting our most "critical" applications, we aren't protecting them all. But we should be.
About the Author

Lori MacVittie is a Distinguished Engineer and Chief Evangelist in F5’s Office of the CTO with deep expertise in application delivery, automation strategy, and infrastructure. She is known for turning complexity into clarity whether she’s defining guardrails for AI agents, dissecting brittle multicloud architectures, or probing the limits of scalable systems. She brings more than thirty years of industry experience across application development, IT architecture, and network and systems operations. Before joining F5, she served as an award-winning technology editor. MacVittie holds an M.S. in Computer Science and is a prolific author whose publications span security, cloud, and enterprise architecture. She is also an avid tabletop and video gamer with unapologetically strong opinions about cheese.
More blogs by Lori Mac VittieRelated Blog Posts

Secure-by-design storage for agentic AI: Why runtime visibility plus traffic control matters
Learn how F5 is collaborating with NVIDIA to help protect agentic AI with secure-by-design AI infrastructure, runtime visibility, and traffic control.

F5 joins the Dell AI Ecosystem Program to help enterprises operationalize AI
F5 joins the Dell AI Ecosystem Program to help enterprises deploy production AI with greater performance, security, and control.

Why sub-optimal application delivery architecture costs more than you think
Discover the hidden performance, security, and operational costs of sub‑optimal application delivery—and how modern architectures address them.

Architecting for AI: Secure, scalable, multicloud
Operationalize AI-era multicloud with F5 and Equinix. Explore scalable solutions for secure data flows, uniform policies, and governance across dynamic cloud environments.

AppViewX + F5: Automating and orchestrating app delivery
As an F5 ADSP Select partner, AppViewX works with F5 to deliver a centralized orchestration solution to manage app services across distributed environments.
F5 NGINX Gateway Fabric is a certified solution for Red Hat OpenShift
F5 collaborates with Red Hat to deliver a solution that combines the high-performance app delivery of F5 NGINX with Red Hat OpenShift’s enterprise Kubernetes capabilities.
