Web application security testing tools are now essential for modern organizations seeking to move ahead in today’s fast-paced, AI-driven world. Many organizations are building and deploying applications at unprecedented speed and scale. Their app portfolios have become increasingly complex and distributed, with services spanning on-premises, multicloud, and edge environments. This expansion has created a rapidly growing attack surface, with new vulnerabilities emerging at a much faster rate. Attackers are quick to exploit any weaknesses, rendering traditional security approaches focused solely on the OWASP Top 10 no longer sufficient.
Why organizations need help with app security
The scale of change is staggering. According to the F5 2025 State of Application Strategy Report, 94% of organizations are deploying apps across multiple environments. Also, modern apps now account for 53% of the average portfolio, surpassing traditional monolithic applications.
APIs, meanwhile, are being delivered faster than ever: 63% of organizations can move an API from concept to production in a week or less, according to Postman’s 2024 State of API Strategy Report.
And external-facing web applications remain the No. 1 attack vector, linked to 34% of all breaches in 2024, according to the Verizon 2025 Data Breach Investigations Report.
The result moving forward is an ever-growing and faster-moving attack surface. Not only are apps and APIs proliferating across diverse environments, but modern development practices mean new services and potential vulnerabilities being introduced at a frenetic pace.
Continuous testing, monitoring, detection, and protection are no longer optional. They’re critical for keeping modern application portfolios secure.
Tools and strategies for a comprehensive testing plan
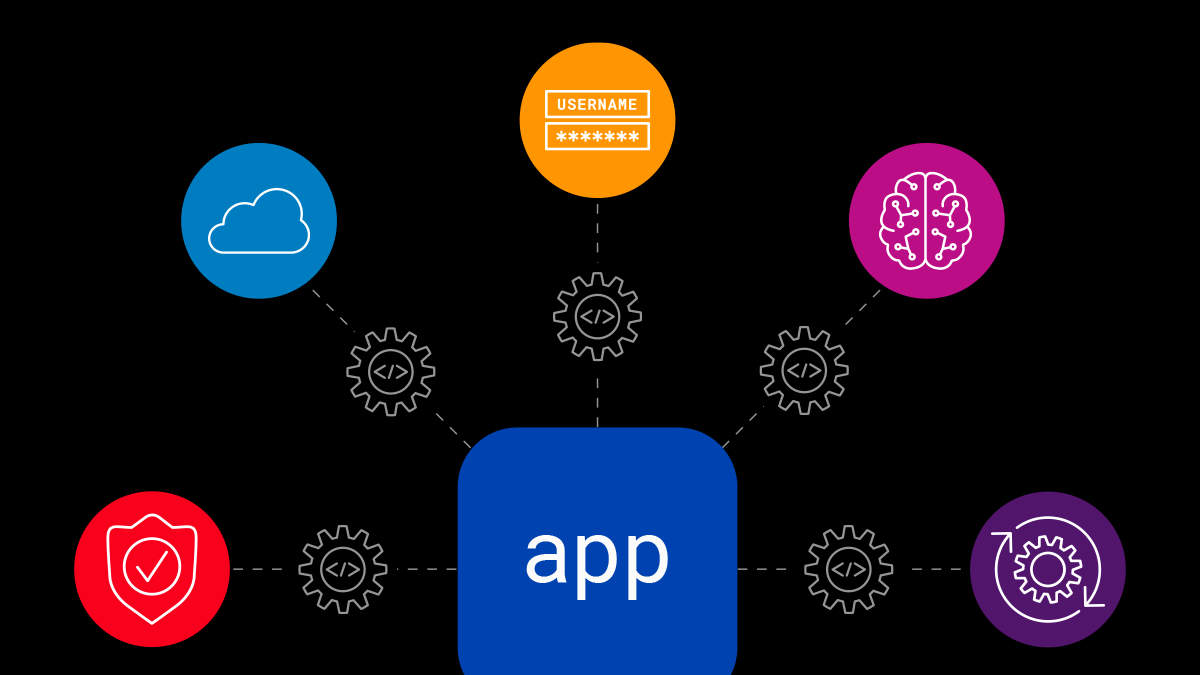
For organizations seeking to manage today’s sprawling application threat surface, visibility is everything. The challenge is not only identifying known risks but also anticipating new ones introduced by rapid development cycles, complex integrations, and modern architectures.
The solution begins with a comprehensive testing plan—one that combines multiple approaches to provide layered coverage across the software development lifecycle (SDLC). Here is what it should include:
The core testing methods
- Static application security testing (SAST): SAST analyzes application source code, bytecode, or binaries without executing the application. It is highly effective for finding coding flaws such as buffer overflows, SQL injection, or insecure data handling.
- Dynamic application security testing (DAST): DAST evaluates applications while they are running, simulating external attacks against a live environment. This “black-box” approach reveals vulnerabilities an attacker would encounter and could exploit.
- Penetration testing: Penetration testing goes beyond automation by engaging ethical hackers to simulate real-world adversaries. Using a mix of automated tools and manual expertise—such as web scanners, sniffers, proxies, and password-cracking utilities—pen testers probe for weaknesses and document vulnerabilities with remediation guidance.
Emerging techniques
Modern application landscapes demand more than the core methods. Organizations are increasingly adopting advanced and AI-driven approaches:
- Fuzz testing: Feeds invalid or random input into applications to trigger crashes or unexpected behavior.
- Interactive application security testing (IAST): Combines SAST and DAST by monitoring code execution from inside the application.
- Runtime application self-protection (RASP): Provides real-time defense by monitoring and blocking attacks as they occur in production.
- AI-augmented testing: Uses machine learning to prioritize findings, reduce false positives, and identify anomalies more efficiently.
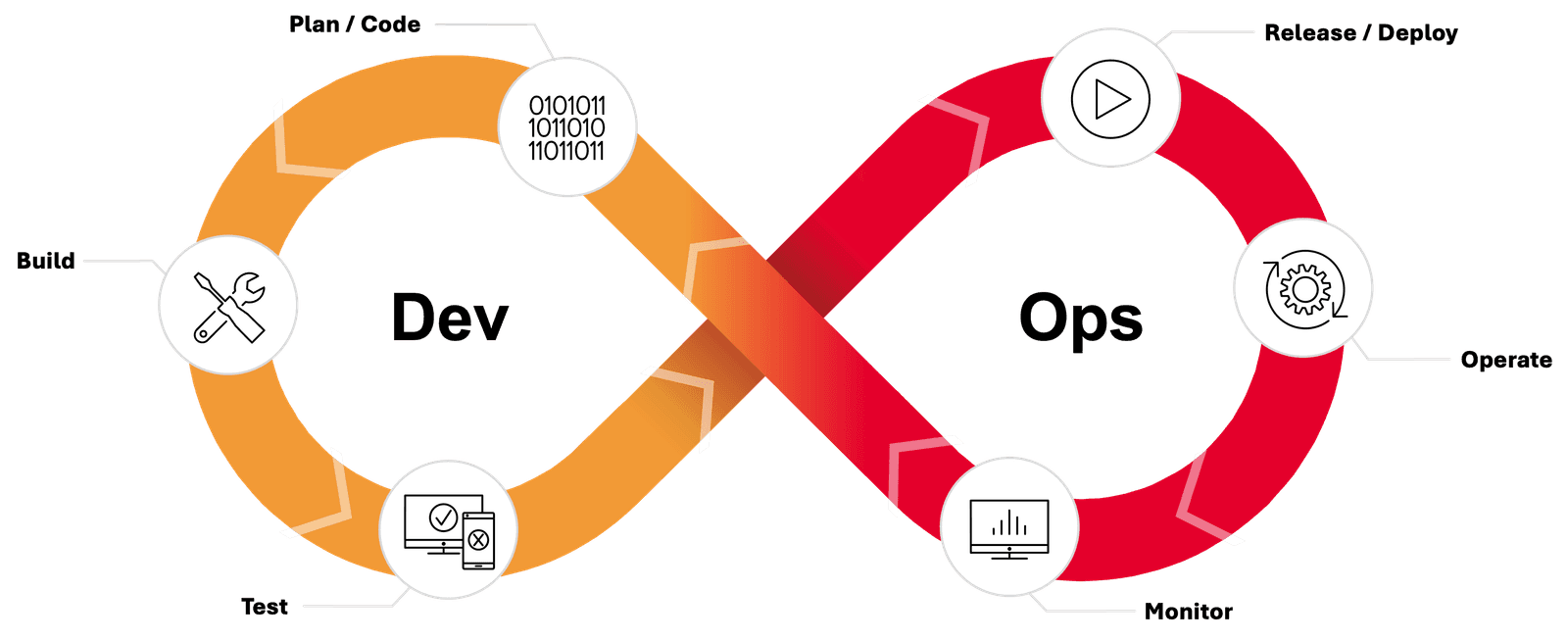
Integrating testing into the SDLC
No single method is sufficient on its own. The most resilient strategies integrate testing early and maintain it throughout the application lifecycle:
- Design phase: Perform threat modeling to anticipate risks before coding begins.
- Development phase: Apply SAST to detect insecure code early.
- Testing/QA phase: Use DAST and fuzzing to find runtime flaws.
- Release phase: Perform penetration testing and validate API security configurations.
- Post-deployment/operations: Continuously monitor production environments with DAST, RASP, and anomaly detection tools.
“The solution begins with a comprehensive testing plan—one that combines multiple approaches to provide layered coverage across the software development lifecycle.”
The benefits of continuous and integrated testing
Embedding security testing throughout the lifecycle—sometimes called “shift-left” and “shield-right” security—delivers clear business benefits:
- Faster remediation cycles: Issues are caught early and fixed quickly, or compensating controls are applied while patches are developed.
- Reduced risk of breaches: Continuous feedback loops limit the window of opportunity for attackers.
- Lower cost of fixes: Vulnerabilities found in production cost exponentially more to remediate than those caught during development.
By combining SAST, DAST, penetration testing, and emerging techniques into a continuous and integrated workflow, organizations can transform application security from a reactive exercise into a proactive enabler of innovation.
“Embedding security testing throughout the lifecycle delivers clear business benefits.”
Take the next step with F5
Discover how F5 can help strengthen your app security posture, with a complimentary web app security assessment. This includes discovery of your publicly accessible web apps across domains and IP addresses owned by your organization and in-depth penetration testing of your exposed web apps.
We help you evaluate your current web app security posture while giving you critical insights to improve the security of your web apps. Reach out to F5 today.