The theme of this year’s AppWorld conference was meeting the moment—a moment characterized by swift technological change. Over the past year, the technology landscape has become increasingly dominated by AI and the challenge of managing application delivery and security across an increasingly complex hybrid multicloud environment.
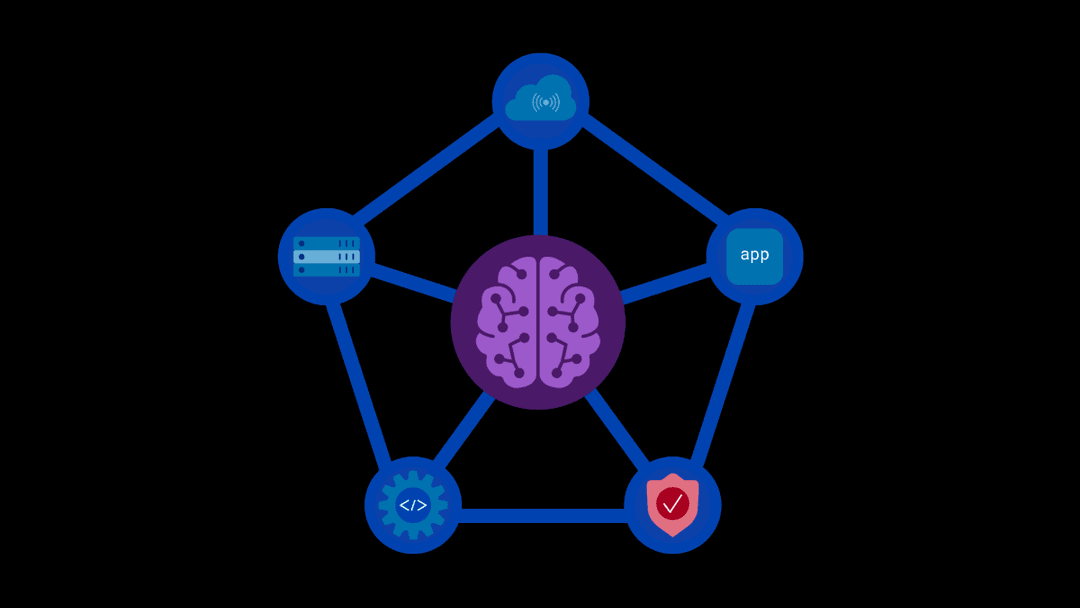
As enterprise AI adoption accelerates, the need to secure AI data and models without stalling innovation is an expanding concern for many organizations. To help organizations meet this challenge, F5 announced several new technologies and enhancements designed to close the AI security gap and to simplify delivery and visibility across diverse environments. F5 leaders also discussed evolving cyberthreats and changing attack tactics, demonstrating how F5 helps customers to stay ahead of criminals rather than responding reactively, incident by incident.
Operational resilience was an important topic at AppWorld, and speakers addressed the need to architect systems for maximized application availability and rapid recovery, regardless of the underlying physical, digital, or cloud infrastructure.
F5 also recognized its strong partner ecosystem, built on collaboration with some of the world’s leading technology companies. In addition, we announced two joint solutions with Red Hat and saluted its channel partners, who help customers with deployment and integration services to gain and maintain a competitive edge in today’s fast-evolving technology landscape.
AppWorld sets the stage for organizations to thrive in the age of AI and hybrid multicloud complexity. In case you missed it, here are four highlights from F5’s flagship customer and partner event:
1. We’re beefing up the security required to operate safely in an AI-powered world.
As AI adoption rapidly expands, ensuring the security of AI models and systems is increasingly critical. While security teams are becoming more effective at identifying vulnerabilities in AI applications, translating these findings into coordinated, enforceable controls often lags behind, limited by manual and fragmented processes. F5 AI Remediate closes the gap between AI threat discovery and threat mitigation by converting detection into enforceable AI security policies, helping organizations move beyond identifying weaknesses and toward measurable AI risk reduction.
F5 also offered a sneak preview of the upcoming F5 BIG-IP software release v21.1, which includes modernization of F5 BIG-IP TMOS software. The forthcoming release will introduce new capabilities to protect AI workloads, enhance post-quantum cryptography (PQC) readiness, and provide advanced protections for modern protocols and APIs.
In addition, F5 announced the renaming of F5 BIG-IP Access Policy Manager, first introduced in 2008, to F5 BIG-IP Zero Trust Access. The newly renamed product will continue to support existing BIG-IP APM use cases, with exciting new features and innovations to be introduced over the coming months.
2. We’re giving customers a practical path to quantum-ready encryption.
F5 has added support for two hybrid PQC ciphers in the latest F5 BIG-IP release to help organizations protect both apps and network traffic without needing to rearchitect or disrupt their systems. F5’s NIST-approved PQC ciphers are considered hybrid because they combine proven, traditional cryptography with a new quantum-resistant algorithm to deliver security for both today’s threats and tomorrow’s quantum-enabled ones.
3. We’re supplying cross-functional teams with the visibility they need.
Addressing the visibility gap typical of hybrid multicloud environments, F5 announced F5 Insight for ADSP, a unified visibility solution that enables teams to view important telemetry and query data, and get clear recommendations on what actions to take to optimize resource allocation, reduce operational costs, and improve outcomes. Now generally available, F5 Insight helps teams unlock practical intelligence about application health, security posture, and the state of underlying infrastructure in a single, unified view.
API discovery is a foundational first step toward building an effective API security strategy, yet finding, mapping, and cataloging all the APIs in an organization’s digital ecosystem isn’t straightforward, and often involves tradeoffs with performance, security, and reliability. As we continue to enhance F5 ADSP, we have expanded the platform’s API discovery capabilities, providing specialized API discovery options for F5 BIG-IP, multi-proxy and gateway architectures, and air-gapped environments.
4. Our partnerships are a key part of the F5 equation.
F5 has a dynamic partner ecosystem, and close collaborations with key technology partners extend F5 capabilities across multiple environments and platforms. Red Hat and F5 have announced two new jointly developed technologies to help organizations accelerate secure, enterprise-level AI adoption. The Red Hat OpenShift Operator is a validated integration that simplifies the deployment and lifecycle management of F5 AI security tools within Red Hat OpenShift AI environments. Jointly developed AI quickstarts from Red Hat and F5 are virtual AI deployment blueprints delivered in a lab-type environment, allowing customers to simulate F5 use cases and better understand the value that both partners bring to AI data factory deployments.
F5 channel partners deliver the expertise to help customers thrive in the era of AI and hybrid multicloud adoption, with custom deployment and integration services that enable customers to drive innovation and solve business challenges across diverse markets and industries. Together, F5 and its channel partners provide the technology and know-how to develop and deploy robust AI-powered applications, modernize legacy infrastructures, and strengthen security postures in complex environments.
In the coming months, we’re taking AppWorld on the road to other cities around the world. Next up is the AppWorld Public Sector Symposium from April 8-10 in Washington, D.C. We hope to see you there. You can find the full list of AppWorld events here.
Also, be sure to check out the F5 Application Delivery and Security Platform (ADSP) webpage.
About the Author
John Maddison is F5’s Chief Marketing Officer. John has more than 30 years of experience leading product teams and corporate marketing functions in cybersecurity, cloud, and telecommunications. Prior to F5, John spent 12 years at Fortinet, most recently as Chief Marketing Officer and EVP of Product Strategy. He previously held leadership positions at Trend Micro, Vina Communications, and Octel Communications. John holds a B.S. in Engineering degree from Plymouth University in Devon, England.
More blogs by John MaddisonRelated Blog Posts
F5 Distributed Cloud Services: Security innovation built for operational scale
Learn how the latest upgrade to F5 Distributed Cloud Services advances AI driven security while strengthening the operational foundations teams need to run at scale.
From dashboard fatigue to operational excellence: Why XOps needs F5 Insight for ADSP
Learn how F5 Insight for ADSP lays the visibility foundation for XOps—turning fragmented signals across applications and infrastructure into actionable intelligence.
The hidden cost of unmanaged AI infrastructure
AI platforms don’t lose value because of models. They lose value because of instability. See how intelligent traffic management improves token throughput while protecting expensive GPU infrastructure.
Govern your AI present and anticipate your AI future
Learn from our field CISO, Chuck Herrin, how to prepare for the new challenge of securing AI models and agents.

F5 recognized as one of the Emerging Visionaries in the Emerging Market Quadrant of the 2025 Gartner® Innovation Guide for Generative AI Engineering
We’re excited to share that F5 has been recognized in 2025 Gartner Emerging Market Quadrant(eMQ) for Generative AI Engineering.
Self-Hosting vs. Models-as-a-Service: The Runtime Security Tradeoff
As GenAI systems continue to move from experimental pilots to enterprise-wide deployments, one architectural choice carries significant weight: how will your organization deploy runtime-based capabilities?