In today’s digital landscape, enterprises are increasingly looking to deliver applications closer to end users or client devices in IoT use cases, aiming to minimize latency, reduce the backhaul of high-fidelity edge data, and enhance overall customer experience. This shift is driving migration of front-end (customer-facing) applications from traditional datacenters and public clouds to the edge, where client requests can be processed locally.
Additionally, enterprises in verticals like retail and manufacturing are increasingly deploying AI/ML applications at edge sites to help with supply chain optimization, worker safety, and preventive maintenance. Meanwhile, core applications and non-real-time apps remain in the cloud. This change is driven by modern containerized apps. These apps demand the deployment of Kubernetes at the edge to provide an app hosting platform. Other primary concerns, in addition to hosting, include ensuring client-side security and establishing secure connectivity back to the cloud or datacenter.
Enterprises require a centralized solution that addresses these challenges, streamlining day-to-day operations while ensuring affordability and robust security. A comprehensive edge computing platform empowers businesses to focus their investments on building and enhancing their applications, confident in the seamless, secure, and cost-effective operation of their edge infrastructure.
F5 Distributed Cloud Services are the ideal solution for enterprises who need seamless edge deployments and need help overcoming the challenges of modern application delivery. Distributed Cloud Services offer a suite of SaaS-managed products and services designed to simplify edge deployment, accelerate application delivery, and fortify deployments with enterprise-grade security.
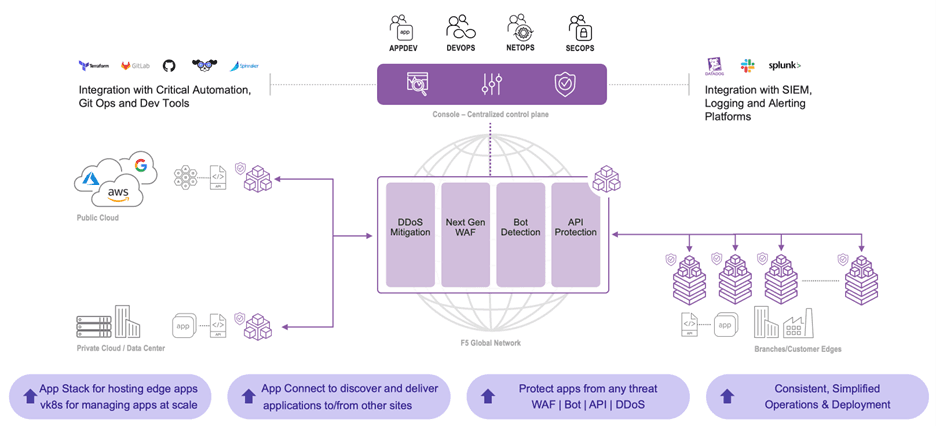
At the core of Distributed Cloud Services lies Distributed Cloud App Stack, a powerful solution enabling managed Kubernetes for application hosting and mesh networking services. This advanced platform simplifies the complexities of edge computing, providing enterprises with:
Managed Kubernetes: Distributed Cloud App Stack manages the Kubernetes platform, offering a central console for monitoring, upgrading, and conducting various day-to-day operations across clusters. This streamlined management ensures optimal performance across diverse edge environments.
AI Workload Support: Distributed Cloud App Stack offers GPU support for running AI workloads requiring parallel processing, empowering businesses to leverage cutting-edge technologies without limitations.
Offline Survivability: Distributed Cloud App Stack clusters operate seamlessly even in the face of intermittent network connectivity issues, ensuring zero downtime and uninterrupted service delivery.
Virtual Kubernetes (vK8s) is a revolutionary approach to managing clusters. It allows enterprises to group application namespaces across numerous Distributed Cloud App Stack clusters into a virtual Kubernetes cluster. This consolidation simplifies deployment complexities:
Unified API Endpoint: RBAC policies empower platform administrators to provide the required application teams access to the vK8s cluster through a single API endpoint. This unified interface streamlines deployment procedures and enhances collaboration.
Effortless Scalability: App developers can deploy applications across thousands of edge clusters with ease, mirroring the simplicity of deploying to a single cluster. The vK8s endpoint seamlessly replicates applications to all clusters, ensuring consistent application performance and health.
Distributed Cloud App Connect enables seamless service discovery and application delivery within the Distributed Cloud ecosystem. Distributed Cloud App Connect creates a cross-cluster service mesh, allowing edge applications to securely access remote services as if they were local resources. This enables seamless connectivity while reducing the attack surface of the application.
F5’s global network backbone and Regional Edge (RE) Points of Presence (PoPs) ensure:
Low Latency Private Transport: The F5 global network backbone, coupled with RE PoPs, provides a low-latency private transport system for inter-site traffic.
Integrated Security Services: REs offer integrated application security services such as WAF, DDoS and Bot protection, API protection, and encryption. This comprehensive security suite safeguards edge applications and data from potential threats, ensuring robust protection against cyber risks.
Simplified Deployment: REs can be grouped into vK8s, enabling users to deploy applications on F5’s PoPs without the need to establish their own edge sites. This accelerates deployment timelines and reduces the operational burden on enterprises.
Distributed Cloud Services empower enterprises to overcome the challenges of modern edge deployments, ensuring agility, security, and unparalleled efficiency in the rapidly evolving digital landscape. With Distributed Cloud Services, businesses can confidently embrace edge computing, concentrating their efforts on innovation while Distributed Cloud Services handle the complexities of managing edge infrastructure, application hosting, networking, and security.