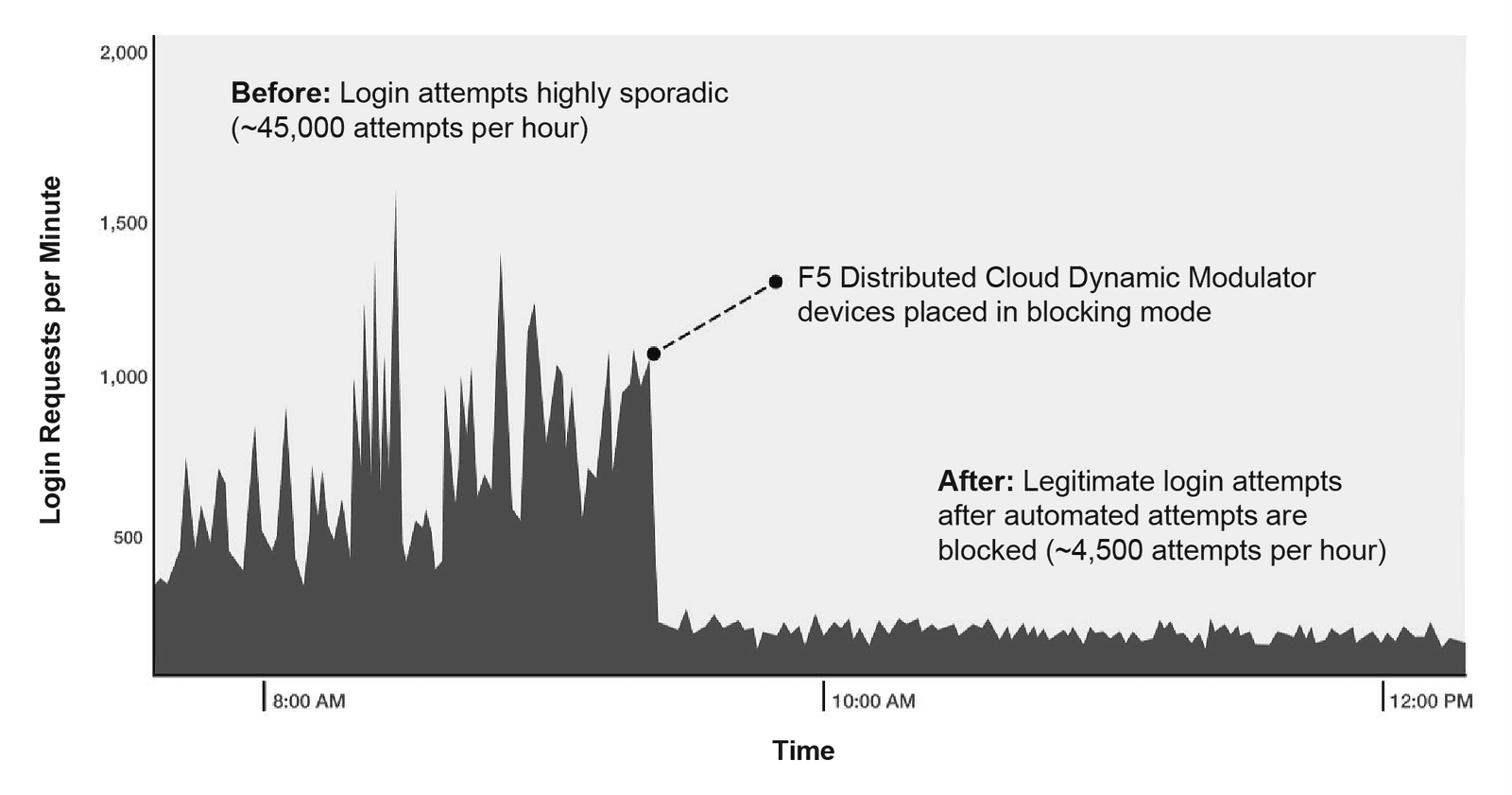
A Fortune 500 retailer manages a gift card program with a stored value of over $5B. Cybercriminals targeted the program, stealing tens of millions of dollars from the company and its customers. Attackers used credentials spilled from other website breaches to hijack customer accounts and steal funds from gift cards. Fraudulent login attempts exceeded a million per day and made up over 90% of the traffic to the login URL. Traditional defenses, like web application firewalls, intrusion detection and prevention services, and fraud analytics, failed to prevent these ongoing automated attacks. The Fortune 500 retailer deployed the F5 Distributed Cloud Bot Defense and completely eliminated account hijackings.
“The problem was with other websites. Our customers reuse the same passwords across multiple sites. When other sites get breached, fraudsters use those spilled credentials to hijack my customers’ accounts. ”
CISO of retailer
A Fortune 500 retailer sought out F5 after its WAF, IP reputation feeds, rate limits, and other defensive measures failed to stop credential stuffing attacks. Attackers used botnets, automated account checkers, and web proxies to defeat security measures. At peak, the attacks on the retailer web application involved over 100,000 new IPs that were used once, and never again. Some of the attackers also mimicked browser or browser agent behavior to simulate human visitor behavior.
“The F5 team worked with my team to go live in two weeks from start to finish. Unlike traditional security solutions, we don’t need more training or headcount to get value out of F5’s solution. They’ve completely blocked the attackers without inconveniencing my users or imposing on my team. ”
CISO of retailer
Following a successful initial deployment, the Fortune 500 retailer is rolling out Distributed Cloud Bot Defense to protect additional web applications and API services used by mobile applications. The retailer has eliminated tens of millions of dollars in fraudulent transactions and chargeback fees. The retailer also benefits on an ongoing basis from threat intelligence (collected and correlated across all F5 deployments) and consultation provided by F5’s anti-automation experts to stay ahead of cybercriminals.
