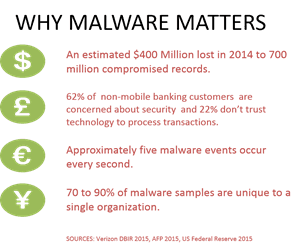
Malware. It’s come to be a significant factor in attacks against both corporate and consumer assets. It continues to result in millions of dollars in fraud while simultaneously chipping away at consumer trust in financial and banking institutions.
Research indicates that preventing and/or detecting malware threats is a top factor driving network security strategy today. Given that Google found just this year that a primary delivery mechanism for malware, phishing, still catches nearly half of its targets that’s no surprise.
It behooves us, then, as leaders and practitioners interested in addressing these issues to be aware of new and rising malware threats that may compromise both our systems and the systems of our consumer-customers.
One such rising dark star is “Slave.” First spotted in March 2015, Slave targets banking web apps with script injections designed to perform a number of functions including credential theft, account access and automatic funds transfers.
In many respects Slave is less sophisticated than some of its cousins, but that makes it no less dangerous. To help you better understand the threat – and defend against it – our security researchers have put together a detailed analysis of this pernicious piece of software and made it available on DevCentral.
Stay safe out there!

###
Editors Note: F5 and DevCentral do not condone the usage of the term ‘slave’ in the context of our technology. In this case the term ‘slave’ is a name, used to specify a particular piece of malware. We believe removing or changing the term, here, would only cause confusion and remove information necessary for effective application security.
About the Author

Lori MacVittie is a Distinguished Engineer and Chief Evangelist in F5’s Office of the CTO with deep expertise in application delivery, automation strategy, and infrastructure. She is known for turning complexity into clarity whether she’s defining guardrails for AI agents, dissecting brittle multicloud architectures, or probing the limits of scalable systems. She brings more than thirty years of industry experience across application development, IT architecture, and network and systems operations. Before joining F5, she served as an award-winning technology editor. MacVittie holds an M.S. in Computer Science and is a prolific author whose publications span security, cloud, and enterprise architecture. She is also an avid tabletop and video gamer with unapologetically strong opinions about cheese.
More blogs by Lori Mac VittieRelated Blog Posts

Secure-by-design storage for agentic AI: Why runtime visibility plus traffic control matters
Learn how F5 is collaborating with NVIDIA to help protect agentic AI with secure-by-design AI infrastructure, runtime visibility, and traffic control.

F5 joins the Dell AI Ecosystem Program to help enterprises operationalize AI
F5 joins the Dell AI Ecosystem Program to help enterprises deploy production AI with greater performance, security, and control.

Why sub-optimal application delivery architecture costs more than you think
Discover the hidden performance, security, and operational costs of sub‑optimal application delivery—and how modern architectures address them.

Architecting for AI: Secure, scalable, multicloud
Operationalize AI-era multicloud with F5 and Equinix. Explore scalable solutions for secure data flows, uniform policies, and governance across dynamic cloud environments.

AppViewX + F5: Automating and orchestrating app delivery
As an F5 ADSP Select partner, AppViewX works with F5 to deliver a centralized orchestration solution to manage app services across distributed environments.
F5 NGINX Gateway Fabric is a certified solution for Red Hat OpenShift
F5 collaborates with Red Hat to deliver a solution that combines the high-performance app delivery of F5 NGINX with Red Hat OpenShift’s enterprise Kubernetes capabilities.
