This week, the bright lights of Las Vegas will illuminate the future of application delivery and security as we host our annual customer and partner event, AppWorld. Those attending can expect plenty of updates spanning our F5 Application Delivery and Security Platform (ADSP), products, and partner ecosystem, each aimed at tackling the most pressing app delivery and security challenges.
At the heart of those announcements is, of course, F5 BIG-IP, a core component of F5 ADSP and today, I’m excited to share a sneak peek into BIG-IP’s upcoming software release, v21.1. Expected to launch in the next few months, BIG-IP v21.1 will continue our journey of BIG-IP TMOS modernization, introduce new capabilities to protect and deliver AI workloads, enhance post-quantum cryptography (PQC) readiness, provide advanced protections for modern protocols and APIs, and much, much more. So, let’s dive in and take a look at the most significant changes coming with BIG-IP v21.1.
BIG-IP TMOS software modernization
When we discontinued BIG-IP Next last year, we pledged to modernize our BIG-IP TMOS software by integrating many of the enhancements originally envisioned for BIG-IP Next. The BIG-IP v21.0 release was the first step towards this goal, as it delivered major advancements in control plane scalability and performance. With v21.1, we’re continuing this modernization journey with two further updates:
Introducing the new BIG-IP Declarative API: BIG-IP has long supported declarative automation through Application Services 3 Extension (AS3), enabling teams to streamline and accelerate application configuration changes. While AS3 revolutionized BIG-IP automation and continues to effectively serve the needs of most deployments, modern environments are evolving at an extraordinary pace. The increasing demand for near-instant configuration changes at unprecedented scale has highlighted the need for a new, next-generation API.
I’m pleased to reveal that BIG-IP v21.1 will introduce—albeit in an Alpha state at first—the new BIG-IP Declarative API. Unlike AS3, the API will be fully integrated into BIG-IP’s codebase, meaning there’s no need for separate lifecycle management. It also moves to a more scalable per-app model, shifting away from AS3’s per tenant design, making it possible to break up those large, complex AS3 configurations into smaller, reusable modules that are simpler to manage and help reduce risk. What’s more, the new API offers much broader automation coverage than AS3, letting you automate most BIG-IP workflows and use cases. And it’s fast: Significant performance improvements mean configurations can be deployed in near real-time, aligning BIG-IP to modern application operating conditions. We’ll be sharing more about the BIG-IP Declarative API in the months ahead, so stay tuned.
Continued control plane enhancements: We began modernizing the BIG-IP control plane in v21.0 (more info available here), which will be a recurring theme in v21.1 and throughout subsequent releases. This latest update delivers significant improvements across three key areas—MCPd, iControl REST, and the BigD daemon—aimed at boosting control plane reliability and performance, while optimizing resource utilization.
The iControl REST API will implement requests faster, cutting end-to-end configuration times by up to 10%. Its enhanced efficiency reduces CPU and memory consumption, freeing up resources for other vital control plane functions. MCPd, the central process responsible for managing BIG-IP configurations, has been upgraded for greater resilience under low-memory conditions and to accelerate system boot-up and configuration-load tasks. Finally, BigD, BIG-IPs application heath monitoring daemon, now utilizes multi-threading to improve monitoring scalability and reduce its total resource consumption.
Upgrading the control plane remains one of our top priorities, so expect further enhancements in BIG-IP v22.x and beyond.
PQC readiness
Depending on who you ask, “Q-Day” is just around the corner, or it’s still a number of years out. Either way, the threat of “harvest now, decrypt later”—where encrypted data is being stored today with the intention of decrypting it once quantum computers become capable in the future—makes the need for PQC critical today.
BIG-IP delivered its first steps toward PQC readiness in v17.5.0 with support for hybrid key exchange X25519_ML-KEM-768 in TLS 1.3. But that was just the beginning. With each release, BIG-IP continues to expand its PQC capabilities and BIG-IP v21.1 delivers two major updates:
Support for additional NIST-compliant PQC ciphers: As quantum computers edge closer to mainstream viability, existing cryptographic algorithms like RSA and ECC are at risk of becoming obsolete. Recognizing this, the U.S. National Institute of Standards and Technology (NIST) led a global effort to standardize PQC algorithms that could withstand quantum-powered attacks. The result? The SecP+ML-KEM cipher groups, which align to FIPS 203 standards, were chosen for their ability to provide hybrid cryptography. These ciphers combine traditional cryptographic methods (SecP) with quantum resistant algorithms (ML-KEM), helping ensure security today and into the future.
For customers required to comply with NIST guidelines and FIPS standards, particularly those in government and other regulated industries, adopting SecP + ML-KEM ciphers is critical to securing their infrastructure. To meet these requirements, BIG-IP will support two new NIST-compliant PQC cipher groups in v21.1:
- SecP256r1ML-KEM-768
- SecP384r1ML-KEM-1024
The ciphers will be supported for both client-, and server-side connections at release, while also enabling SSL Forward Proxy use cases. (You can find more information about BIG-IP v21.1s PQC enhancements in this blog by F5’s Rachael Shah.)
Quantum-resistant TLS/SSL VPN Tunneling: VPN tunneling was first introduced in the late 1990s as a way to secure data transmission over public or private networks by creating an encrypted tunnel between a client and a server. For nearly three decades, VPN tunnels have successfully kept sensitive information out of the wrong hands; however, the rise of quantum computing will grant adversaries the computational power needed to break traditional encryption methods and access that data.
To counteract this, BIG-IP Zero Trust Access (formerly BIG-IP APM) v21.1 will introduce quantum-resistant TLS/SSL VPN tunneling with support for the X25519 + ML-KEM-768 cipher. As above, this cipher will support end-to-end client-side and server-side connections, providing comprehensive protection for modern VPN tunnels while maintaining compliance with NIST guidelines and FIPS 203 standards. For organizations that prefer to use IPSec VPNs over TLS/SSL VPNs, BIG-IP Zero Trust Access is expected to add similar quantum-secure IPSec tunneling support in the not-too-distant future.
AI workload delivery, security, and access enhancements
At their core, the requirements for AI workloads are much like those of other applications; they need to be fast, available, and above all, secure. But as these workloads grow in scale and sophistication, the infrastructure supporting them, including application delivery controllers (ADCs), must also evolve to meet new demands. With v21.0, BIG-IP took an important first step by providing an initial set of capabilities to support the Model Context Protocol (MCP). Now, with v21.1, we’re building on that work with additional MCP functionality and by empowering agentic AI systems with fast and secure access to resources.
Expanded security and delivery capabilities for the Model Context Protocol: As AI apps increasingly rely on MCP as a fast, standardized way for agents to interact with applications, having consistent and secure traffic flows is critical. BIG-IP v21.1 introduces two significant improvements for MCP traffic:
- MCP Protocol Protection with F5 BIG-IP Advanced WAF: AI apps leveraging MCP traffic are often vulnerable to emerging attack types such as tool poisoning, secret exposure, injection attacks, and other threats as described by the OWASP MCP Top-10. BIG-IP v21.1 adds WAF-enabled MCP inspection, enabling proactive detection and mitigation of these threats, keeping AI traffic secure without impacting performance or latency.
- MCP Session Persistence with F5 BIG-IP Local Traffic Manager (LTM): MCP workflows often require requests to route consistently to the same server to ensure proper processing, which wasn’t previously possible. With BIG-IP v21.1 we’re introducing session persistence for MCP, which behaves in many ways like cookie persistence. This ultimately means that when an MCP server issues a session ID to a client, subsequent traffic carrying that session ID will be routed to the same pool member, helping to ensure a smoother and more reliable connection.
Seamless, secure access for AI agents: Agentic AI systems—those comprised of autonomous agents operating in real time—require dynamic and fluid access to backend resources like databases, cloud services and internal systems. Yet traditional methods for managing credentials and authenticating new agents can be cumbersome, often leaving developers to rely on access team admins to authorize and manually configure new clients, which isn’t always time efficient. Fortunately, that’s where the new Dynamic Client Registration (DCR) capability of BIG-IP Zero Trust Access in v21.1 comes in.
With DCR, agentic AI systems (or any other app for that matter), can securely and effortlessly register themselves with BIG-IP Zero Trust Access as the central authorization server when new tasks or agents are created. Rather than waiting for manual configuration, an agent can send an API request to the BIG-IP Zero Trust Access DCR endpoint, including basic details like the agent’s name and required access permissions. BIG-IP Zero Trust Access automatically validates the request, registers the agent, and issues secure credentials on the fly, significantly shortening and simplifying the process. You can find a visual representation of this process below.
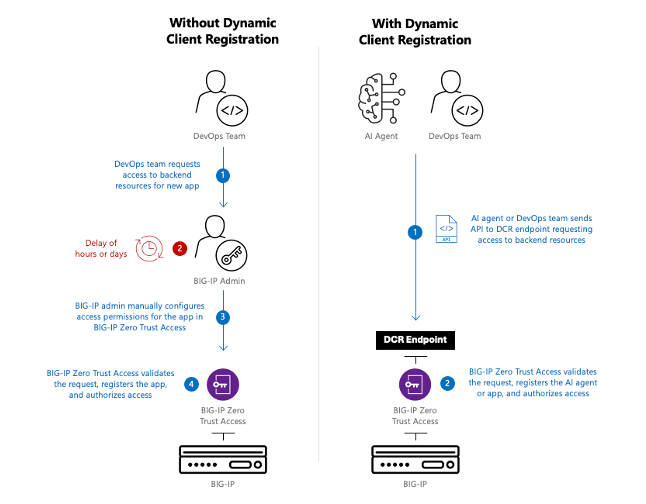
As noted earlier, the DCR endpoint can be used to register and approve any type of app—not just AI systems— for secure access to resources. DevOps teams can utilize their existing CI/CD pipelines to send an access request to the DCR endpoint automatically, helping to shorten app deployment times and lessen the daily workloads of BIG-IP admins. (You can learn more about BIG-IP Zero Trust Access in this blog by Jay Kelley.)
Modern API and protocol protection
As applications evolve over time, so do the protocols and APIs that underpin them, bringing better performance, scale, and flexibility. However, these advancements also introduce new challenges, as attackers shift their focus to exploit weaknesses and vulnerabilities in these emerging technologies. To help our customers stay ahead in this relentless cycle, BIG-IP Advanced WAF is adding protection for both HTTP/3 protocol traffic and APIs defined by the OpenAPI 3.1 specification in v21.1. Let’s take a closer look:
Advanced security for HTTP/3 protocol traffic: Adoption of HTTP/3 has been rapidly accelerating since its introduction in 2022, with an estimated 38% of websites using the protocol today. While HTTP/2 remains dominant, HTTP/3’s superior performance, reliability, and efficiency are widely expected to drive its adoption past HTTP/2 in the coming years. And as organizations gradually migrate to HTTP/3, the need to protect that traffic from web-based threats doesn’t diminish, emphasizing the continued need for robust WAF protection.
Beginning in BIG-IP v21.1, BIG-IP Advanced WAF protects traffic no matter which HTTP protocol variant you’re using. WAF policies can now inspect HTTP/3 traffic with the same fidelity and security as HTTP/2 or HTTP1/1, identifying and blocking sophisticated attacks like cross-site scripting (XSS) or SQL injection. Initially this support applies to client-side traffic only in BIG-IP v21.1. However, server-side protection is expected to be a fast follow in future versions.
WAF protection for APIs built on OpenAPI 3.1 specifications: APIs are the backbone of modern applications, enabling seamless connectivity and compatibility between systems, and keeping them secure is critical. The OpenAPI standard plays a vital role in this ecosystem by providing a structured framework for defining and documenting APIs, ensuring consistency and interoperability across different platforms. You can think of the OpenAPI spec as a rulebook that defines exactly how an API should work—what endpoints it exposes, what data it expects, and how it should behave. BIG-IP Advanced WAF uses this rulebook to protect your APIs by identifying any unusual behavior and enforcing strict security policies based on the way your APIs are designed.
With v21.1, BIG-IP Advanced WAF now protects APIs based on the OpenAPI 3.1 specification. It learns the allowed endpoints, methods, parameters, data types, and security requirements defined in the OpenAPI 3.1 spec, then blocks any requests that don’t match those rules. This stops malformed requests, abuse of undocumented endpoints, and common API attacks before they reach your application, ensuring only expected and properly structured API traffic is allowed. Previous versions of the OpenAPI specification including 2.0 and 3.0 will, of course, continue to be supported and protected.
And that’s not all…
The enhancements covered in this blog really are just the tip of the iceberg when it comes to the new capabilities planned for BIG-IP v21.1. In addition to everything outlined here, you can expect improved HTTP/2 performance, native IPSec VPN tunneling, policy-based egress routing, multi-factor authentication for the BIG-IP management plane, and so much more.
Once released, checkout the BIG-IP v21.1 release notes on MyF5 for more information. In the meantime, be sure to register for our upcoming webinar for an in-depth look at the BIG-IP v21.1 release.
About the Author

Related Blog Posts
F5 Distributed Cloud Services: Security innovation built for operational scale
Learn how the latest upgrade to F5 Distributed Cloud Services advances AI driven security while strengthening the operational foundations teams need to run at scale.
From dashboard fatigue to operational excellence: Why XOps needs F5 Insight for ADSP
Learn how F5 Insight for ADSP lays the visibility foundation for XOps—turning fragmented signals across applications and infrastructure into actionable intelligence.
The hidden cost of unmanaged AI infrastructure
AI platforms don’t lose value because of models. They lose value because of instability. See how intelligent traffic management improves token throughput while protecting expensive GPU infrastructure.
Govern your AI present and anticipate your AI future
Learn from our field CISO, Chuck Herrin, how to prepare for the new challenge of securing AI models and agents.

F5 recognized as one of the Emerging Visionaries in the Emerging Market Quadrant of the 2025 Gartner® Innovation Guide for Generative AI Engineering
We’re excited to share that F5 has been recognized in 2025 Gartner Emerging Market Quadrant(eMQ) for Generative AI Engineering.
Self-Hosting vs. Models-as-a-Service: The Runtime Security Tradeoff
As GenAI systems continue to move from experimental pilots to enterprise-wide deployments, one architectural choice carries significant weight: how will your organization deploy runtime-based capabilities?
